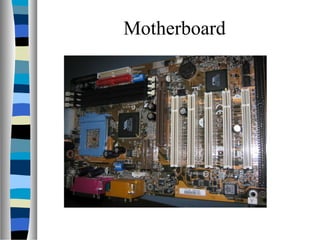
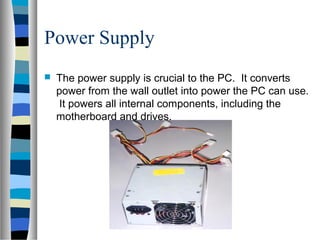
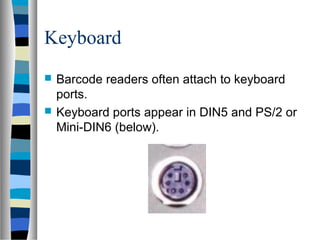
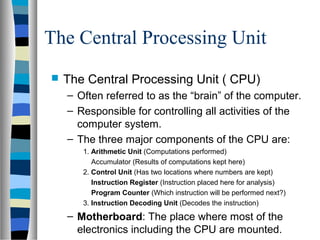
The document discusses the key internal and external components of a personal computer (PC). It identifies external components like the case, monitor, keyboard, and mouse. It then describes important internal components such as the motherboard, central processing unit (CPU), drives, expansion cards, memory, and power supply. The document provides details on how these components work and their functions within the PC.