The document is a guide on using OWASP ZAP for security scanning within a CI pipeline, outlining its purpose, features, and various use cases. It is aimed at developers, QA, and security professionals to integrate security scanning early in the development process and offers options for automated security tests. Key topics include installation options, baseline scans, API usage, and the new Jenkins plugin for enhanced integration.

![Baseline scan – usage
14
Usage: zap-baseline.py -t <target> [options]
-t target target URL including the protocol, eg https://www
Options:
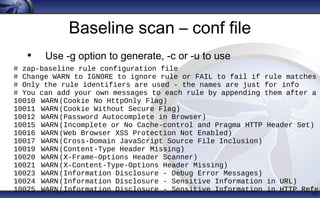
-c config_file config file to use to INFO, IGNORE or FAIL warnin
-u config_url URL of config file to use to INFO, IGNORE or FAIL
-g gen_file generate default config file (all rules set to WA
-m mins the number of minutes to spider for (default 1)
-r report_html file to write the full ZAP HTML report
-w report_md file to write the full ZAP Wiki (Markdown) report
-x report_xml file to write the full ZAP XML report
-a include the alpha passive scan rules as well
-d show debug messages
-i default rules not in the config file to INFO
-j use the Ajax spider in addition to the traditiona
-l level minimum level to show: PASS, IGNORE, INFO, WARN o
-s short output format - dont show PASSes or example
-z zap_options ZAP command line options e.g. -z "-config aaa=bbb](https://image.slidesharecdn.com/owasp201611alldaydevopszapautomationinci-161115143252/85/AllDayDevOps-ZAP-automation-in-CI-14-320.jpg)
![Baseline scan – output
16
./zap-baseline.py -t https://www.example.com
3 URLs
PASS: Cookie No HttpOnly Flag [10010]
PASS: Cookie Without Secure Flag [10011]
PASS: Password Autocomplete in Browser [10012]
<snip>
WARN: Incomplete or No Cache-control and Pragma HTTP Header Set [10015]
https://www.example.com
WARN: Web Browser XSS Protection Not Enabled [10016] x 3
https://www.example.com
https://www.example.com/robots.txt
https://www.example.com/sitemap.xml
WARN: X-Frame-Options Header Not Set [10020] x 1
https://www.example.com
WARN: X-Content-Type-Options Header Missing [10021] x 1
https://www.example.com
FAIL: 0 WARN: 4 INFO: 0 IGNORE: 0 PASS: 22](https://image.slidesharecdn.com/owasp201611alldaydevopszapautomationinci-161115143252/85/AllDayDevOps-ZAP-automation-in-CI-15-320.jpg)
![Cmdline Quick Scan
21
./zap.sh -cmd -quickurl
http://example.com/ -quickprogress
• Spidering
• Active scanning
• [====================] 100%
• Attack complete
• <?xml version="1.0"?><OWASPZAPReport
version="2.5.0" generated="Tue, 4 Oct 2016
09:31:53">
• <site name="http://example.com" ...](https://image.slidesharecdn.com/owasp201611alldaydevopszapautomationinci-161115143252/85/AllDayDevOps-ZAP-automation-in-CI-20-320.jpg)
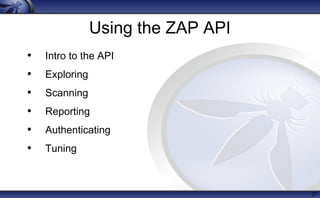
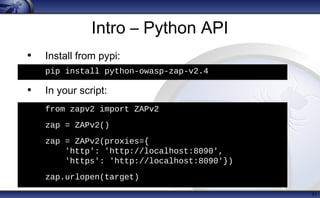
![Intro to the API
• RESTish – ok, only uses GET requests
http(s)://zap/<format>/<component>/
<operation>/<op name>[/?<params>]
• Maps closely to the UI / code
• Theres a v basic (but complete) web UI for it
• And clients in various langs:
Java, Python, Node JS, .Net, PHP, Go …
• Clients are generated from the code
28](https://image.slidesharecdn.com/owasp201611alldaydevopszapautomationinci-161115143252/85/AllDayDevOps-ZAP-automation-in-CI-27-320.jpg)