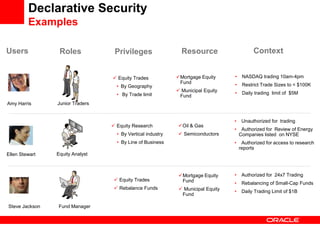
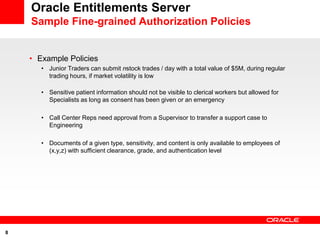
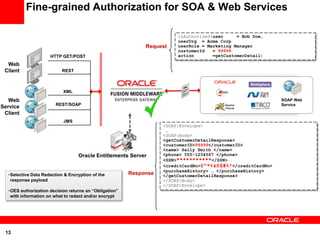
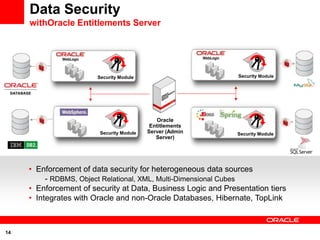
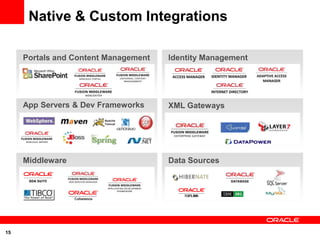
Oracle Entitlements Server 11g provides real-time, fine-grained authorization for applications, web services, and data. It scales to support large numbers of users, roles, and resources, and enforces authorization decisions with low latency. It integrates with applications through open standards and supports selective data redaction and encryption.