NOTES Nov 14, 2011
•Download as PPT, PDF•
1 like•929 views
This chapter introduces basic computer concepts including defining a computer, its components, advantages and disadvantages of use, networks and the internet, types of software, categories of computers, and examples of computer applications in society. It discusses how computers process data into information, the input and output devices, storage, and main components including the processor and memory. Networks and servers are described as well as system and application software. Personal computers, mobile devices, game consoles, and different types of servers and computers are outlined. Common computer users and their needs are identified.
Report
Share
Report
Share
Recommended
Lecture-1: Introduction to Computer - Basic Definitions & Concepts- Computer ...

Lecture-1: Introduction to Computer - Basic Definitions & Concepts- Computer Types & Hierarchy
Recommended
Lecture-1: Introduction to Computer - Basic Definitions & Concepts- Computer ...

Lecture-1: Introduction to Computer - Basic Definitions & Concepts- Computer Types & Hierarchy
DTCC Chapter 1 - Introduction to Computers

Shelly Cashman Series - Discovering Computers & Microsoft Office 2010.
Introduction to computer_system (for MBM first semester, BBA first semester, ...

This slide is related to the course of MBM first semester, BBA first semester, BBS first semester, MBA first semester, MBS first semester...
Introduction to computer system.
Prepared by Raj Chand
INTRODUCTION TO INFORMATION TECHNOLOGY SARASWATHI RAMALINGAM

COMPUTER BASIC MCQ,MCQ,Data Representation ,Programming Languages /Computer Languages ,Software: System Software , Application Software,SIMPLE MCQ,INTRODUCTION TO INFORMATION TECHNOLOGY,COMPUTER BASICS
Introduction to computers pdf

"An Introduction to Computers" http://serverpartdeals.com -
The best place to buy server parts online, computer hardware supplies and computer networking products. We want to be your main computer parts supplier. Providing a reliable computer parts source to buy computer parts wholesale & server parts direct, online.
- See more at: http://serverpartdeals.com/#sthash.T7Moe4fN.dpuf
More Related Content
What's hot
DTCC Chapter 1 - Introduction to Computers

Shelly Cashman Series - Discovering Computers & Microsoft Office 2010.
Introduction to computer_system (for MBM first semester, BBA first semester, ...

This slide is related to the course of MBM first semester, BBA first semester, BBS first semester, MBA first semester, MBS first semester...
Introduction to computer system.
Prepared by Raj Chand
INTRODUCTION TO INFORMATION TECHNOLOGY SARASWATHI RAMALINGAM

COMPUTER BASIC MCQ,MCQ,Data Representation ,Programming Languages /Computer Languages ,Software: System Software , Application Software,SIMPLE MCQ,INTRODUCTION TO INFORMATION TECHNOLOGY,COMPUTER BASICS
Introduction to computers pdf

"An Introduction to Computers" http://serverpartdeals.com -
The best place to buy server parts online, computer hardware supplies and computer networking products. We want to be your main computer parts supplier. Providing a reliable computer parts source to buy computer parts wholesale & server parts direct, online.
- See more at: http://serverpartdeals.com/#sthash.T7Moe4fN.dpuf
What's hot (20)
Introduction to computer_system (for MBM first semester, BBA first semester, ...

Introduction to computer_system (for MBM first semester, BBA first semester, ...
INTRODUCTION TO INFORMATION TECHNOLOGY SARASWATHI RAMALINGAM

INTRODUCTION TO INFORMATION TECHNOLOGY SARASWATHI RAMALINGAM
Viewers also liked
Digestive System Notes

This slideshow is intended for students in Mr. Hildebrandt's anatomy & physiology classes.
Liver anatomy, physiology and imporatance to anesthesia 

Liver anatomy and physiology imporatnat considerations from anesthesia point of view
Viewers also liked (15)
Liver anatomy, physiology and imporatance to anesthesia 

Liver anatomy, physiology and imporatance to anesthesia
Similar to NOTES Nov 14, 2011
Introduction to computer Powerpoint Presentation

Introduction to computer Powerpoint Presentation for plus one Accountancy 11 chapter.
information tecnology

INFORMATION TECHNOLOGY,
INTERNET AND YOU
Topics to be covered:
Information Systems
People
Software
Hardware
Data
Connectivity and the Mobile Internet
Information System
An information system has several parts:
People
Procedure
Software
Hardware
Data
Internet
(continued…)
People: It is easy to overlook people as one of the parts of an
information system. Yet this is what personal computers are all about—
making people, end users like you, more productive.
(continued…)
Procedures: The rules or guidelines
for people to follow when using
software, hardware, and data are
procedures. These procedures are
typically documented in manuals
written by computer specialists.
Software and hardware
manufacturers provide manuals with
their products. These manuals are
provided in either printed or electronic
form.
(continued…)
Software: A program consists of the step-by-step instructions that tell
the computer how to do its work. Software is another name for a
program or programs. The purpose of software is to convert data
(unprocessed facts) into information (processed facts).
(continued…)
Hardware: The equipment that processes the data to create information
is called hardware. It includes smartphones, tablets, keyboards, mice,
displays, system units, and other devices. Hardware is controlled by
software.
(continued…)
Data: The raw, unprocessed facts, including text, numbers, images,
and sounds, are called data. Processed data yields information.
(continued…)
Internet: Almost all information systems provide a way to connect to
other people and computers, typically using the Internet. This
connectivity greatly expands the capability and usefulness of
information systems.
Stop: Let us check our progress
People
People are surely the most important part of any information system.
Our lives are touched every day by computers and information systems.
Many times the contact is direct and obvious, such as when we create
documents using a word processing program or when we connect to the
Internet.
Other times, the contact is not as obvious.
Software
There are two major kinds of software: system software and
application software.
The user interacts primarily with application software. System software
enables the application software to interact with the computer hardware.
System software is “background” software that helps the computer
manage its own internal resources.
(continued…)
System software is not a single program. Rather, it is a collection of
programs, including the following:
Operating Systems
Utilities
(continued…)
Operating systems are programs that coordinate computer resources,
provide an interface between users and the computer, and run
applications. Smartphones, tablets, and many other mobile devices use
embedded operating systems, also known as real-time operating
systems (RTOS).
Similar to NOTES Nov 14, 2011 (20)
Recently uploaded
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
ODC, Data Fabric and Architecture User Group

Let's dive deeper into the world of ODC! Ricardo Alves (OutSystems) will join us to tell all about the new Data Fabric. After that, Sezen de Bruijn (OutSystems) will get into the details on how to best design a sturdy architecture within ODC.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Recently uploaded (20)
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
NOTES Nov 14, 2011
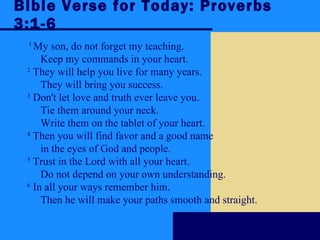
- 1. Bible Verse for Today: Proverbs 3:1-6 1 My son, do not forget my teaching. Keep my commands in your heart. 2 They will help you live for many years. They will bring you success. 3 Don't let love and truth ever leave you. Tie them around your neck. Write them on the tablet of your heart. 4 Then you will find favor and a good name in the eyes of God and people. 5 Trust in the Lord with all your heart. Do not depend on your own understanding. 6 In all your ways remember him. Then he will make your paths smooth and straight.
- 3. Chapter 1 Objectives Recognize the importance of computer literacy Define the term, computer Identify the components of a computer Discuss the advantages and disadvantages of using computers Recognize the purpose of a network Discuss the uses of the Internet and World Wide Web Distinguish between system software and application software Describe the categories of computers Identify the elements of an information system Describe the various types of computer users Discuss various computer applications in society Next
- 14. The Components of a Computer Video: Speed Up Your Hard Drive Next CLICK TO START
- 30. Categories of Computers p. 19 What are the categories of computers? Personal Computers (desktop) Mobile Computers and Mobile Devices Game Consoles Servers Mainframes Supercomputers Embedded Computers Next
- 49. Summary of Introduction to Computers Basic computer concepts The term, computer The components of a computer The advantages and disadvantages of using computers The purpose of a network The uses of the Internet Computer software Categories of computers Types of computer users Computer applications in society Chapter 1 Complete
