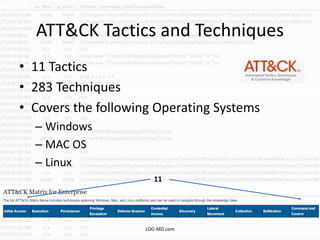
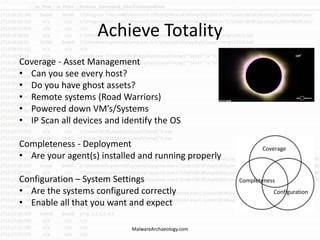
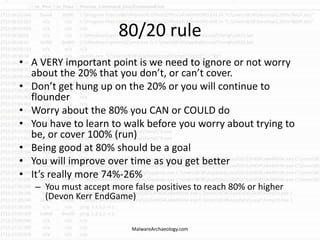
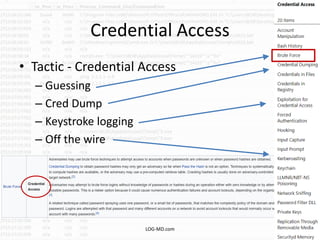
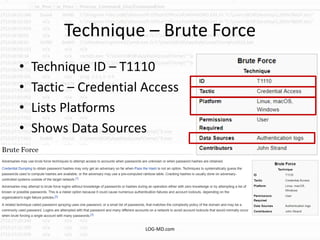
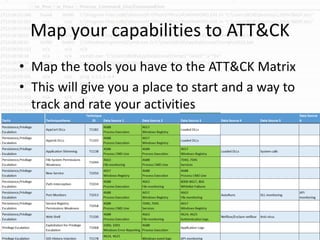
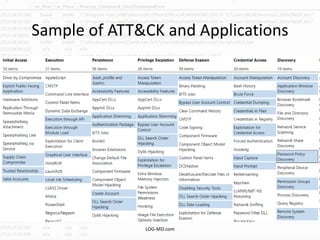
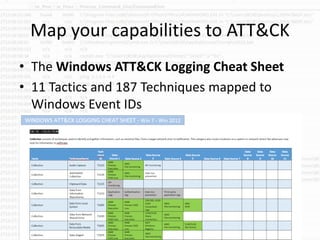
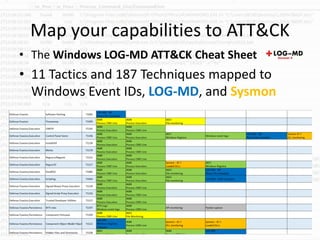
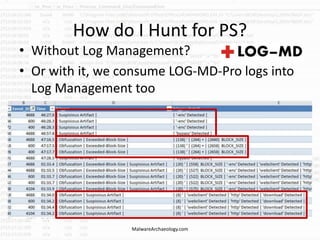
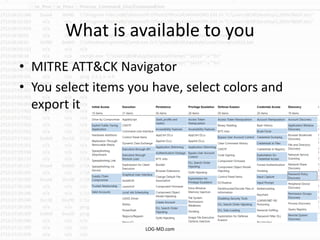
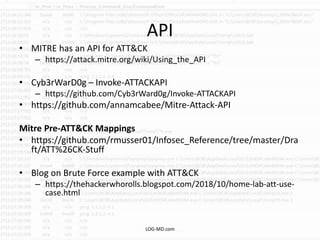
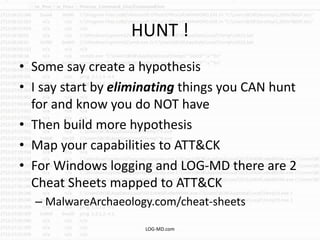
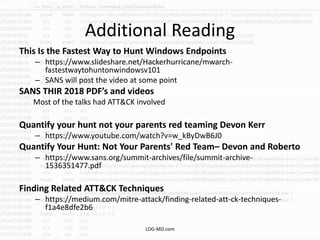
The document discusses the importance of the MITRE ATT&CK framework in enhancing cybersecurity practices, emphasizing its role in identifying security gaps and improving defense mechanisms based on actual adversary behaviors. It outlines how ATT&CK acts as a baseline for security improvements, allowing organizations to map their tools and capabilities against known tactics and techniques. Additionally, resources such as cheat sheets and tools for mapping and hunting within the ATT&CK framework are provided to assist security professionals in their efforts to fortify defenses.