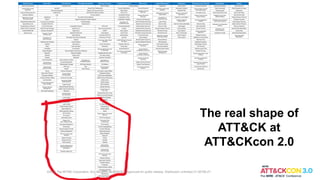
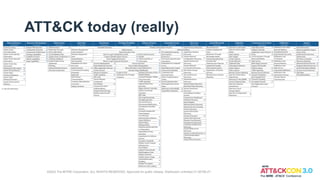
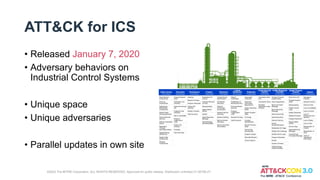
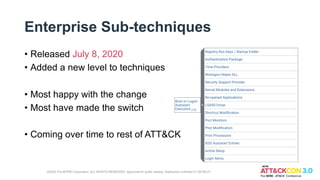
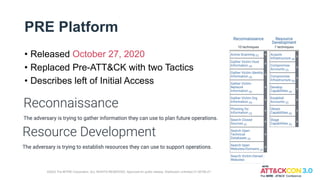
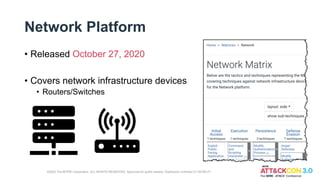
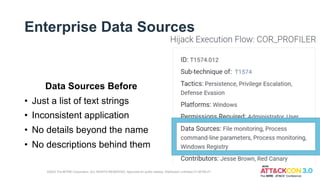
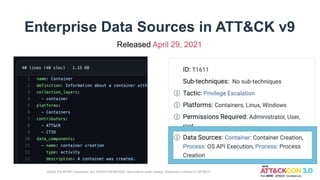
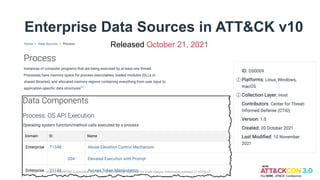
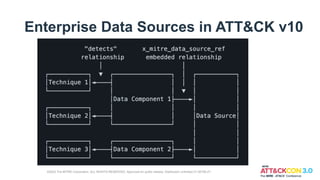
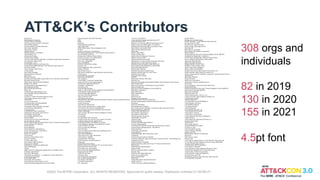
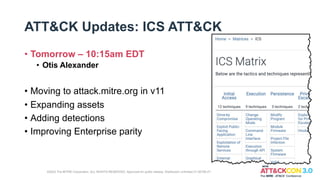
The document discusses updates to the MITRE ATT&CK framework since ATT&CKcon 2.0 in 2020. Major updates include the addition of ATT&CK for ICS focusing on industrial control systems, enterprise sub-techniques providing more granular technique details, new platforms covering pre-attack behaviors, network infrastructure, cloud, and containers, and enhanced enterprise data sources. The ATT&CK framework continues to grow and improve based on contributions from a large community of cybersecurity professionals and organizations.