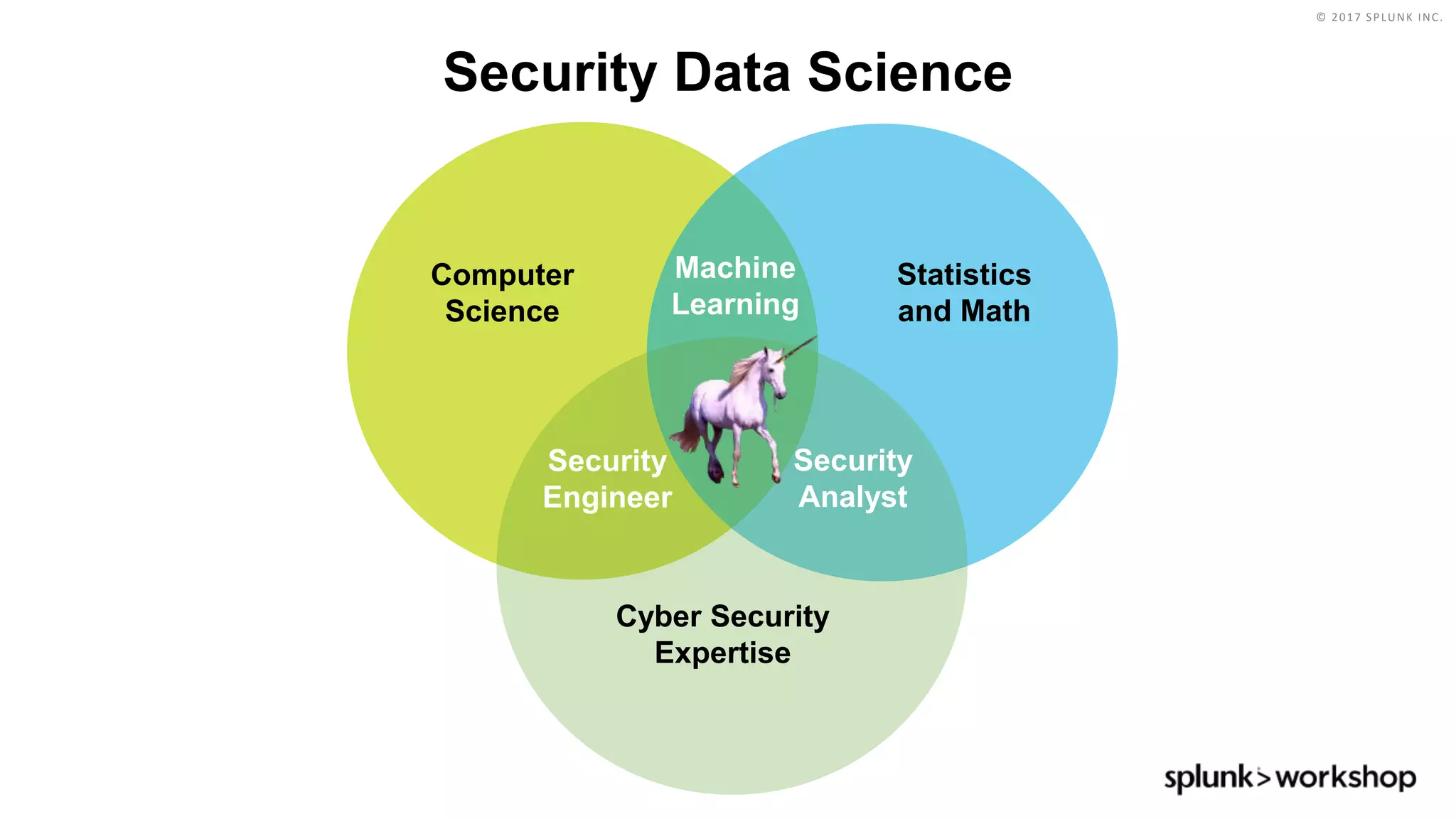
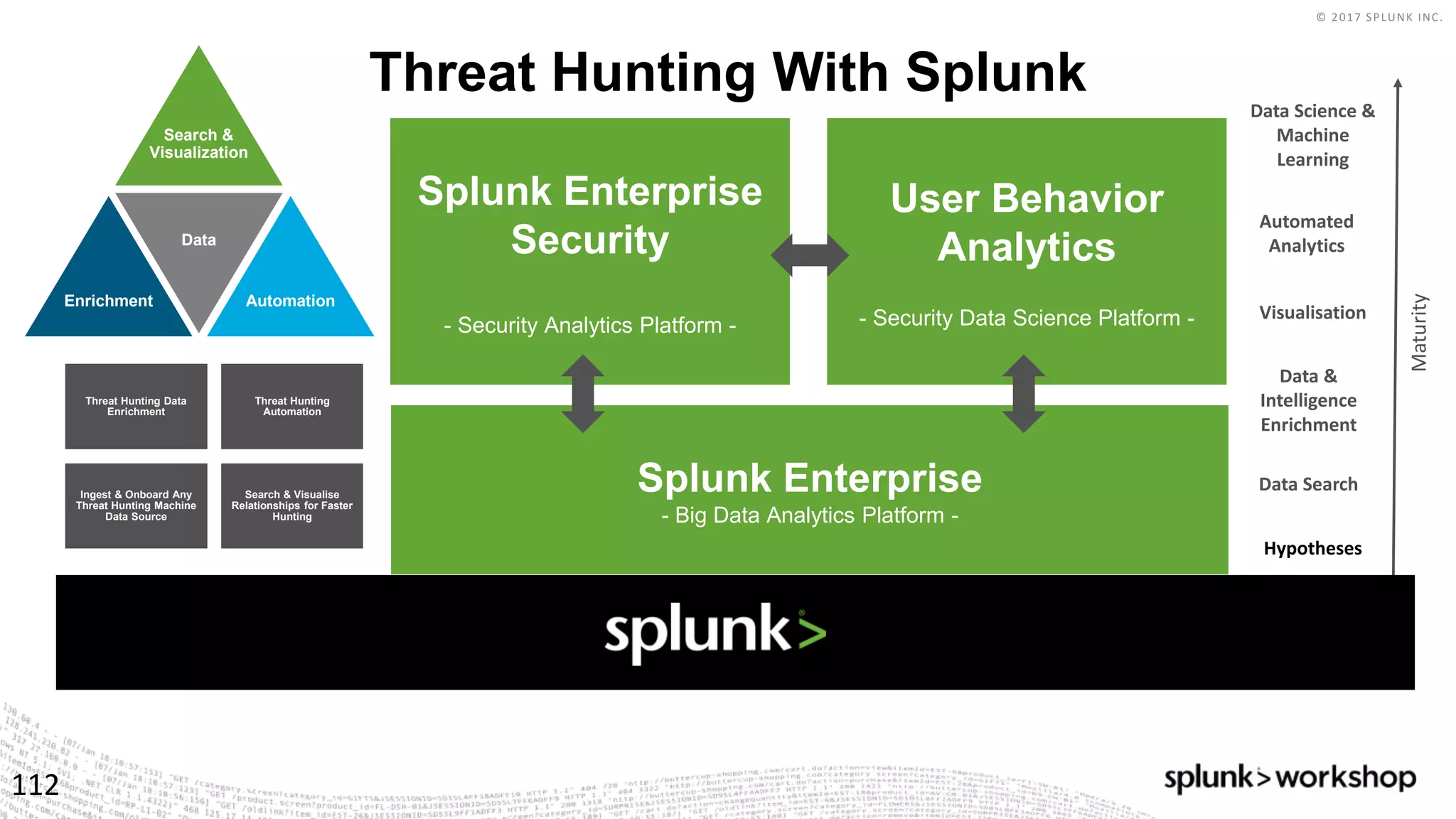
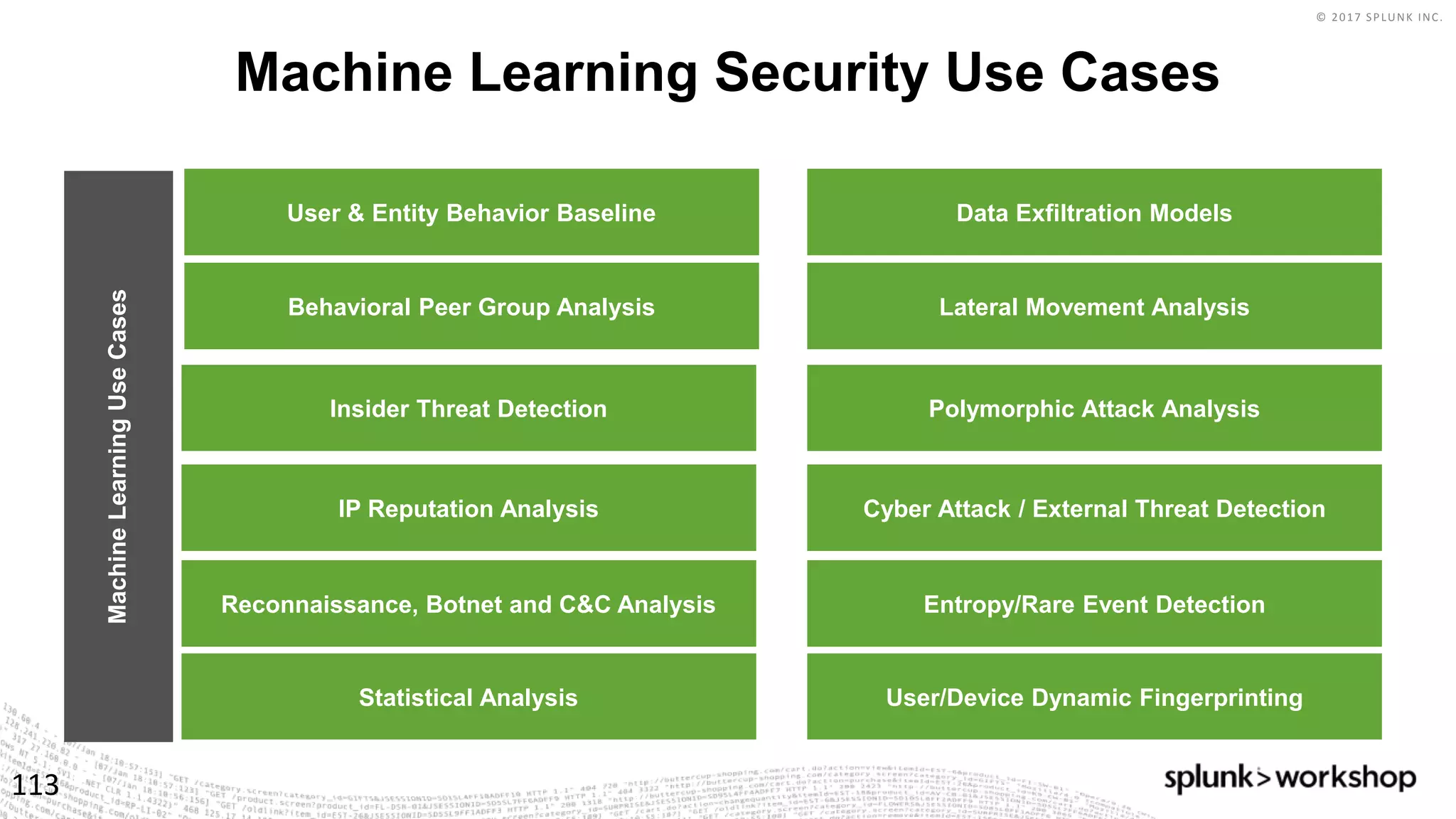
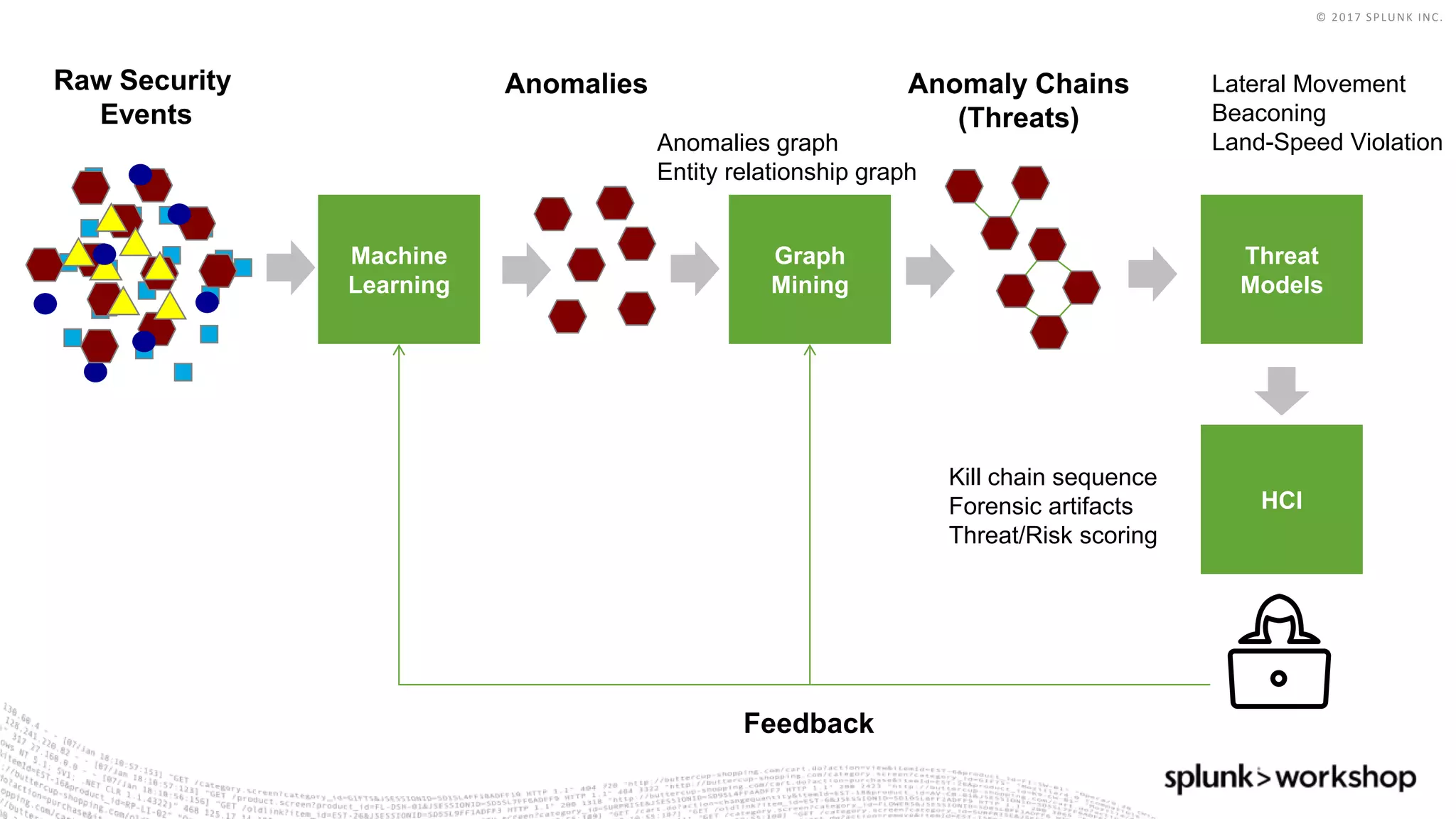
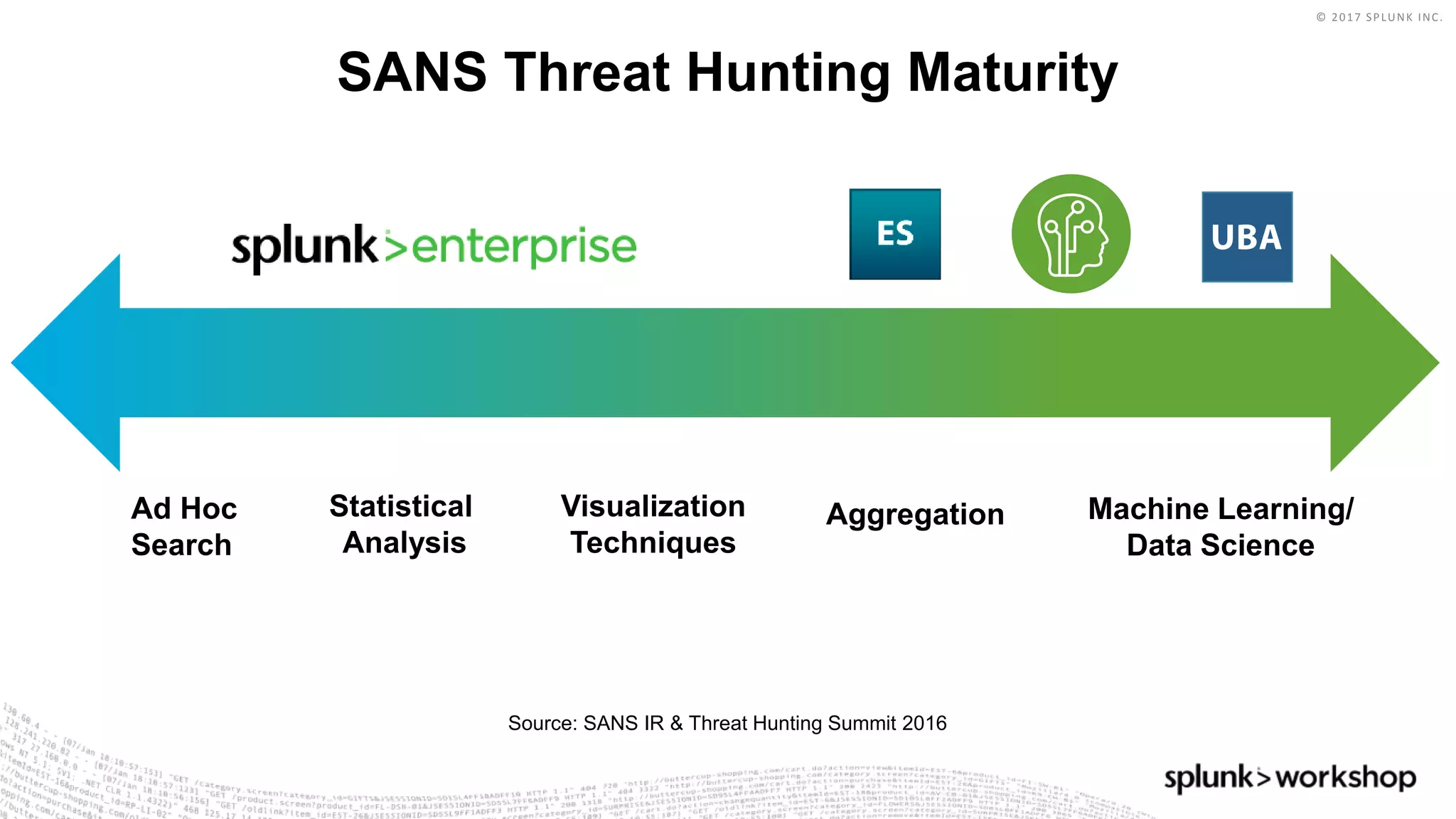
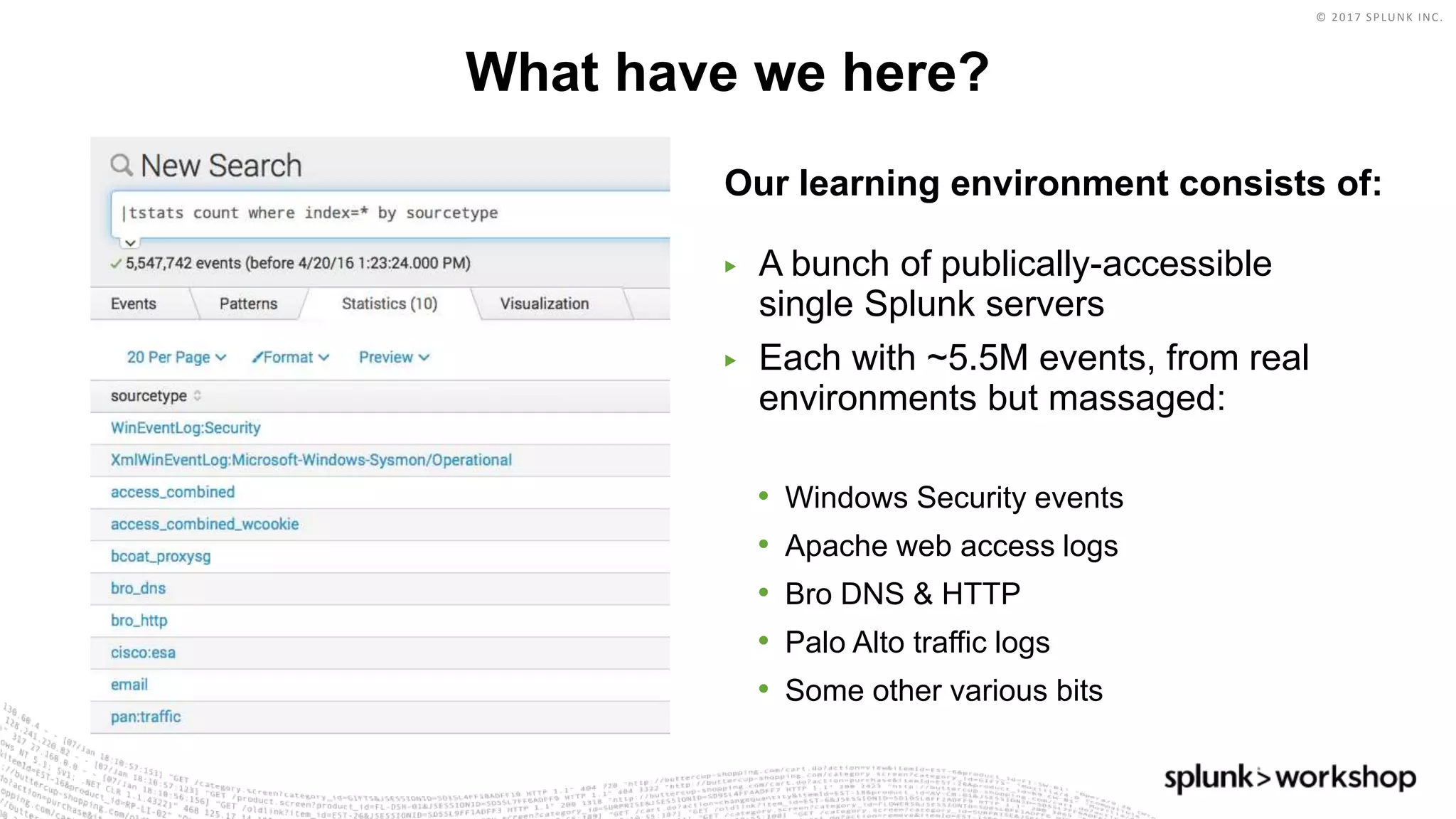
This document outlines a presentation on threat hunting with Splunk. It discusses threat hunting basics, data sources for threat hunting, understanding endpoints, and the cyber kill chain model. The agenda includes a hands-on walkthrough of attacking scenario detection using Splunk. Advanced threat hunting techniques, enterprise security investigations, and applying machine learning to security are also covered.



![© 2017 SPLUNK INC.
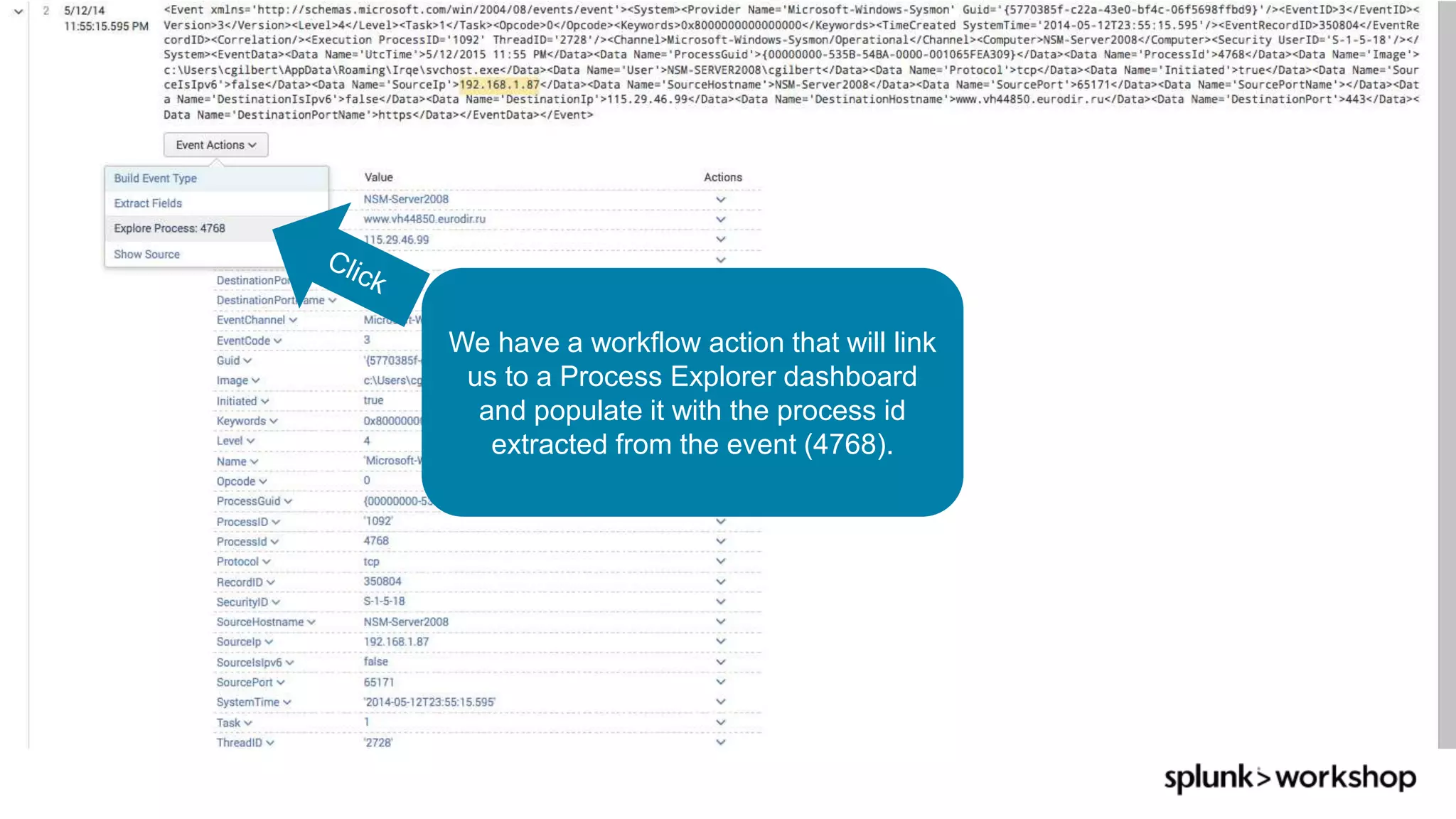
What is Threat Hunting, Why do You Need it?
1 The Who, What, Where, When, Why and How of Effective Threat Hunting, SANS Feb 2016
2 Cyber Threat Hunting - Samuel Alonso blog, Jan 2016
“Threat Hunting is not new, it’s
just evolving!”
Threat hunting - the act of
aggressively intercepting,
tracking and eliminating cyber
adversaries as early as possible
in the Cyber Kill Chain2
What?
Threats are human. Focused and
funded adversaries will not be
countered by security boxes on
the network alone. Threat
hunters are actively searching for
threats to prevent or minimize
damage [before it happens] 1
Why?](https://image.slidesharecdn.com/threathunting-170816192606/75/Threat-Hunting-5-2048.jpg)








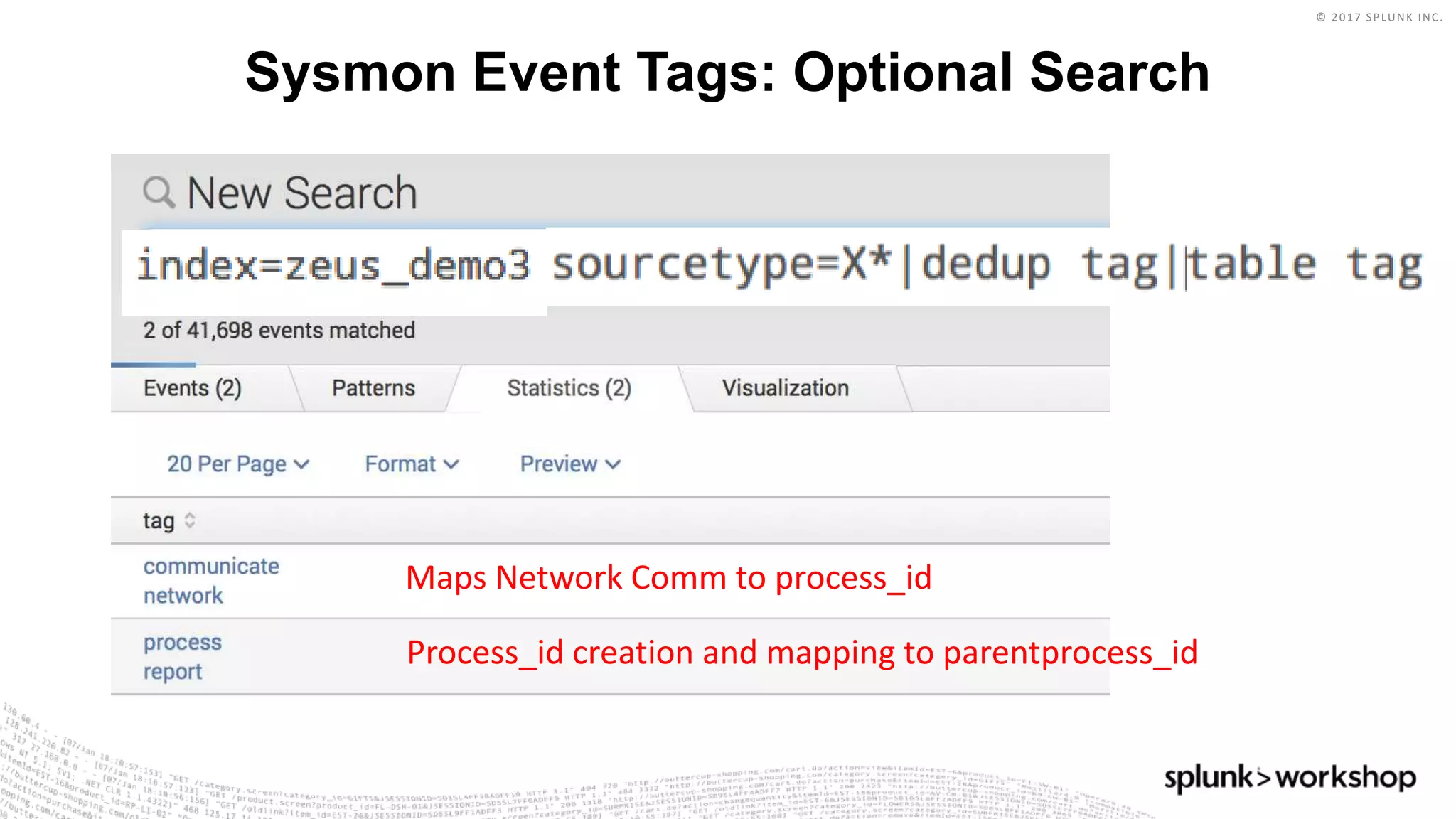



























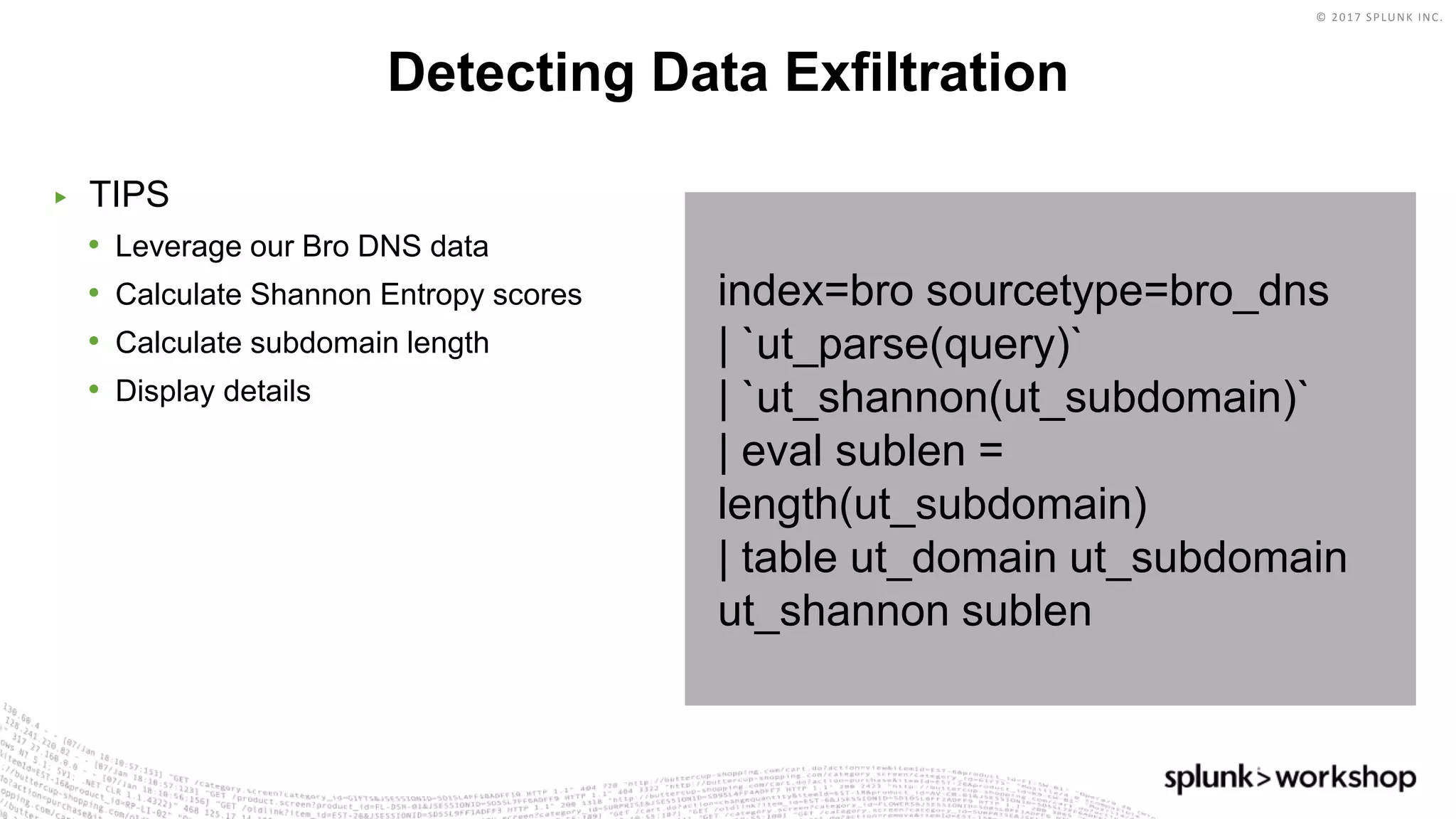
*=(%20)*[%27|'])|w*[%27|']or)
Which means: In the string we are given, look for ANY of the following matches and put that into the
“injection” field.
• Anything containing SELECT followed by FROM
• Anything containing UNION followed by SELECT
• Anything with a ‘ at the end
• Anything containing DELETE followed by FROM
• Anything containing UPDATE followed by SET
• Anything containing ALTER followed by TABLE
• A %27 OR a ‘ and then a %20 and any amount of characters then a %20 and then a %27 OR a ‘
• Note: %27 is encoded “’” and %20 is encoded <space>
• Any amount of word characters followed by a %27 OR a ‘ and then “or”](https://image.slidesharecdn.com/threathunting-170816192606/75/Threat-Hunting-58-2048.jpg)