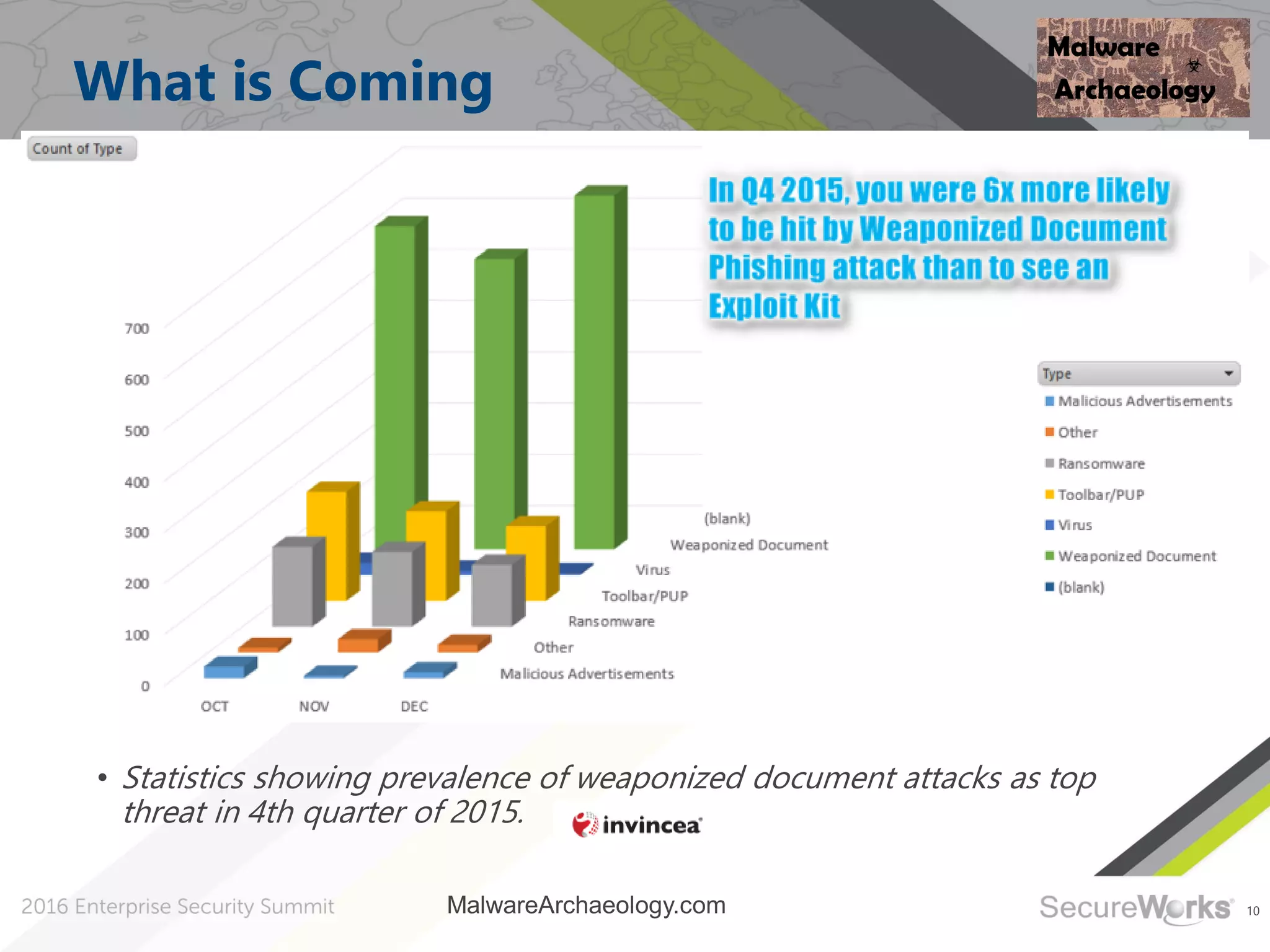
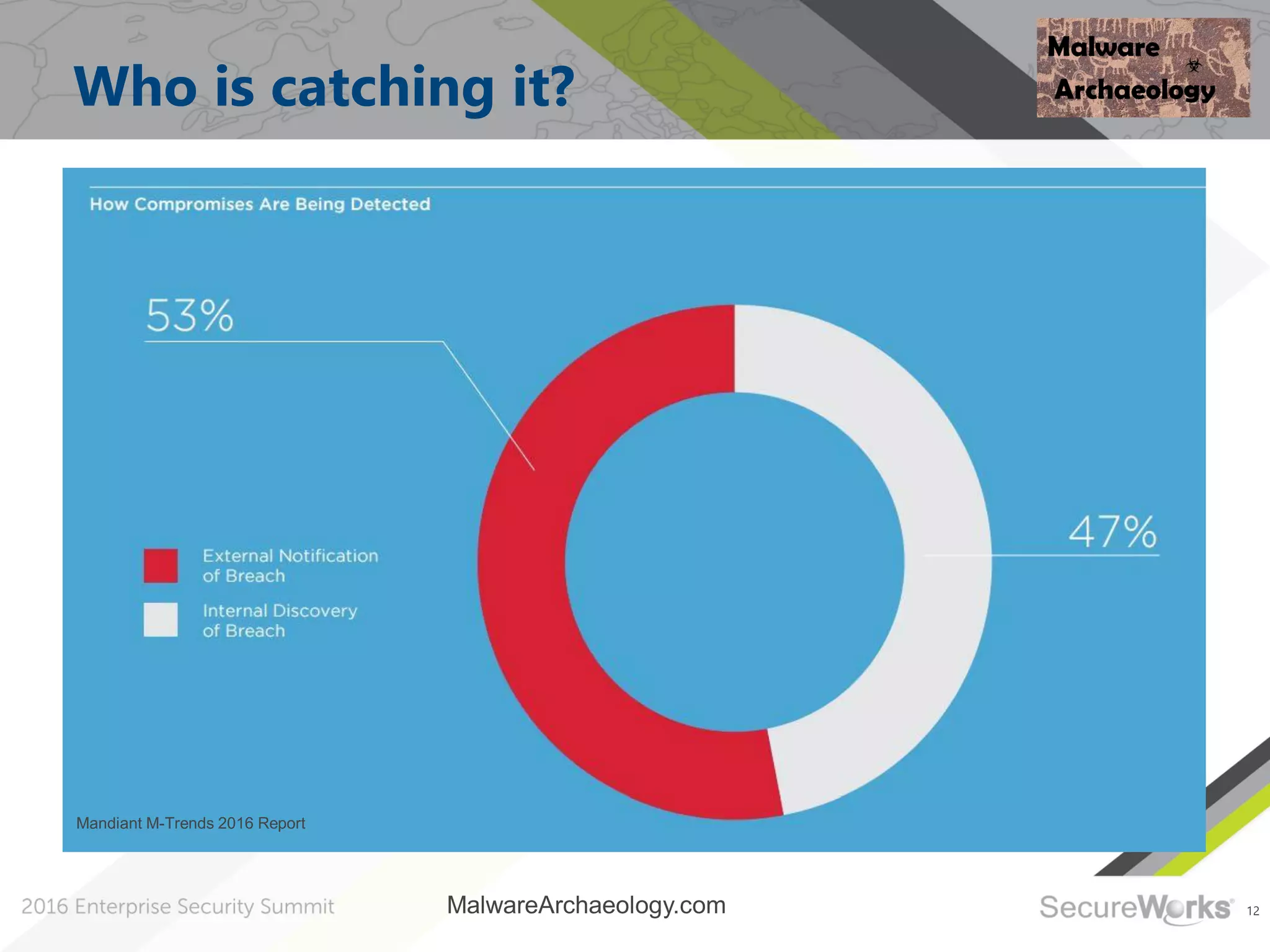
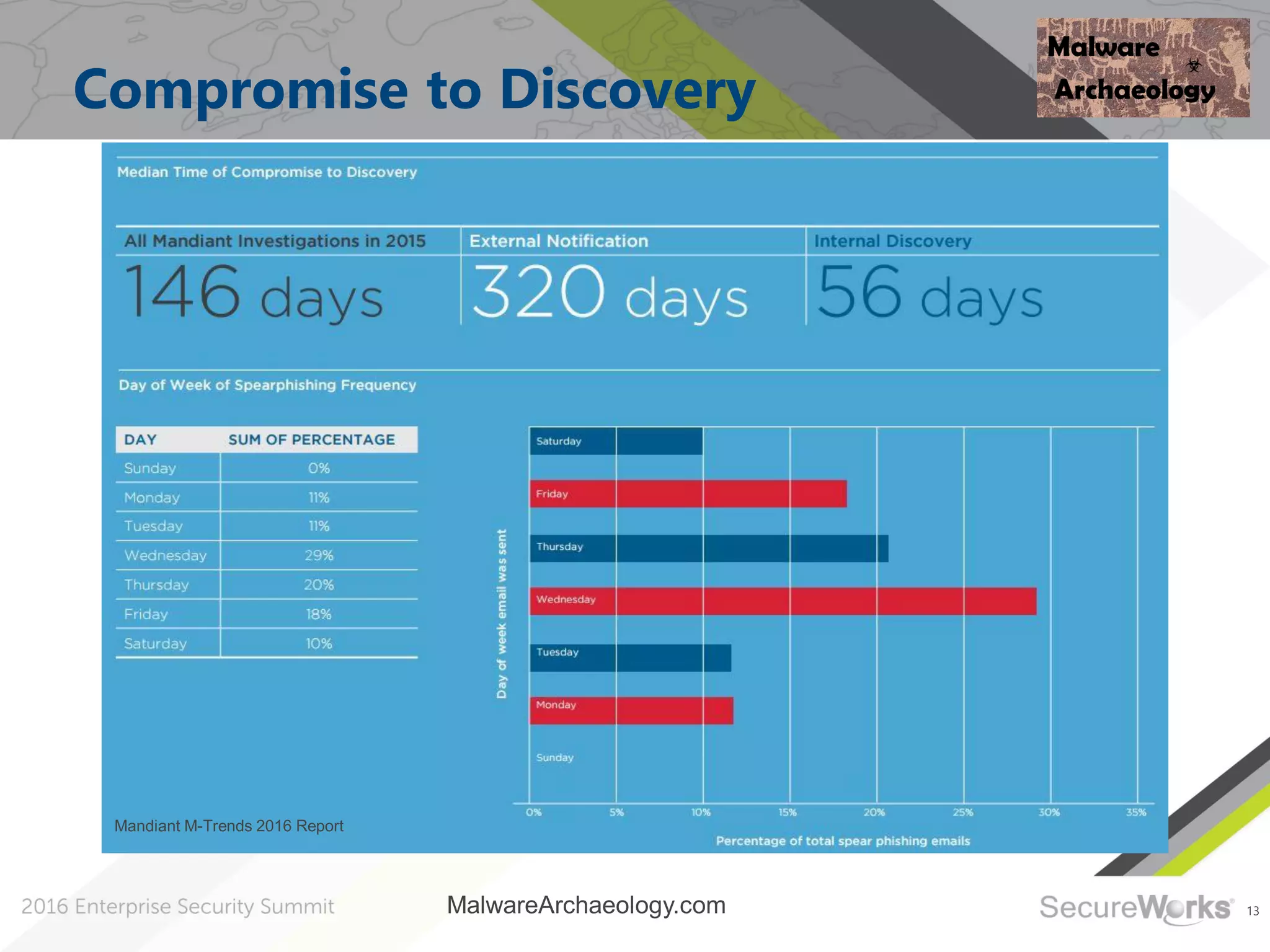
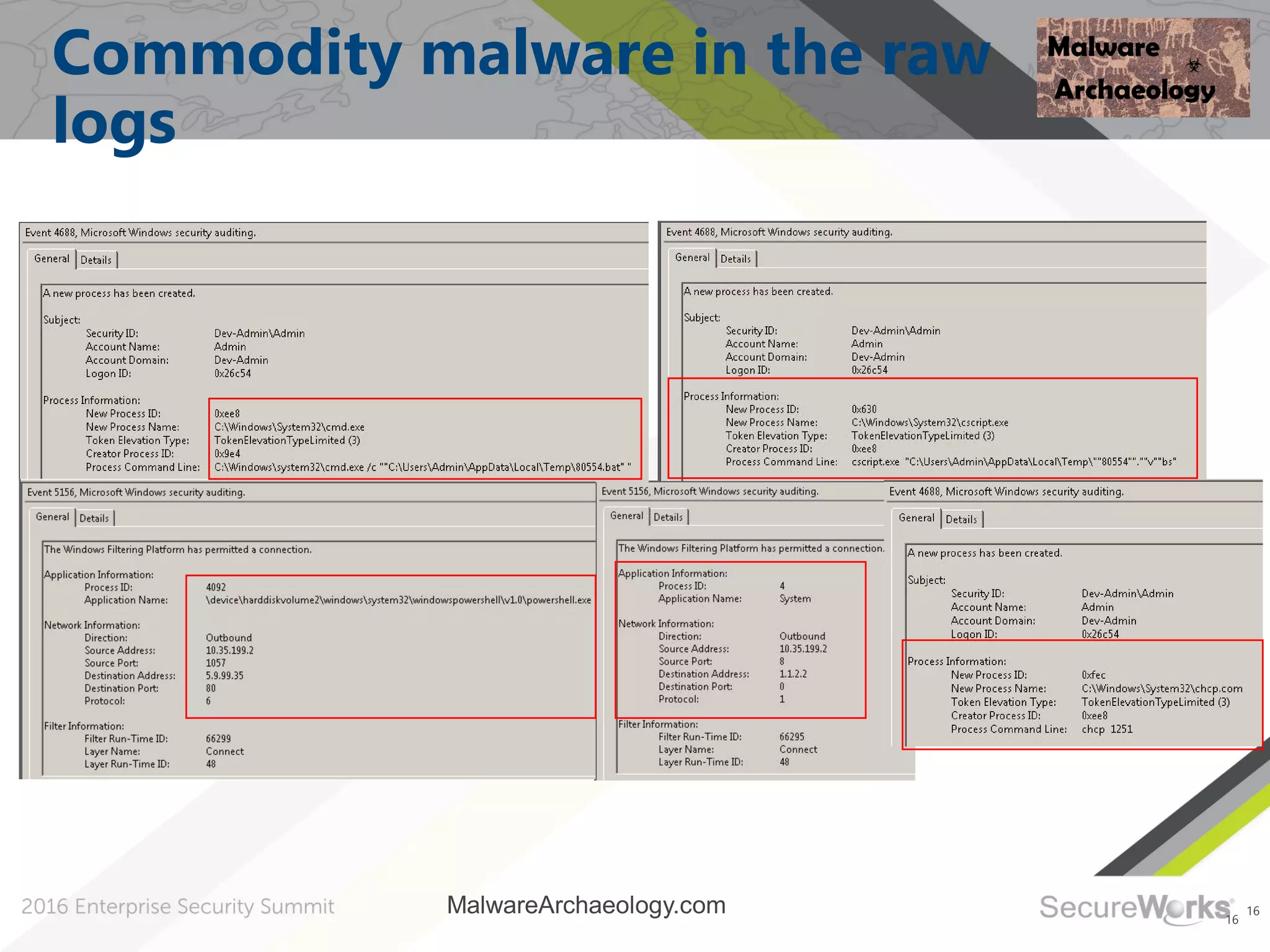
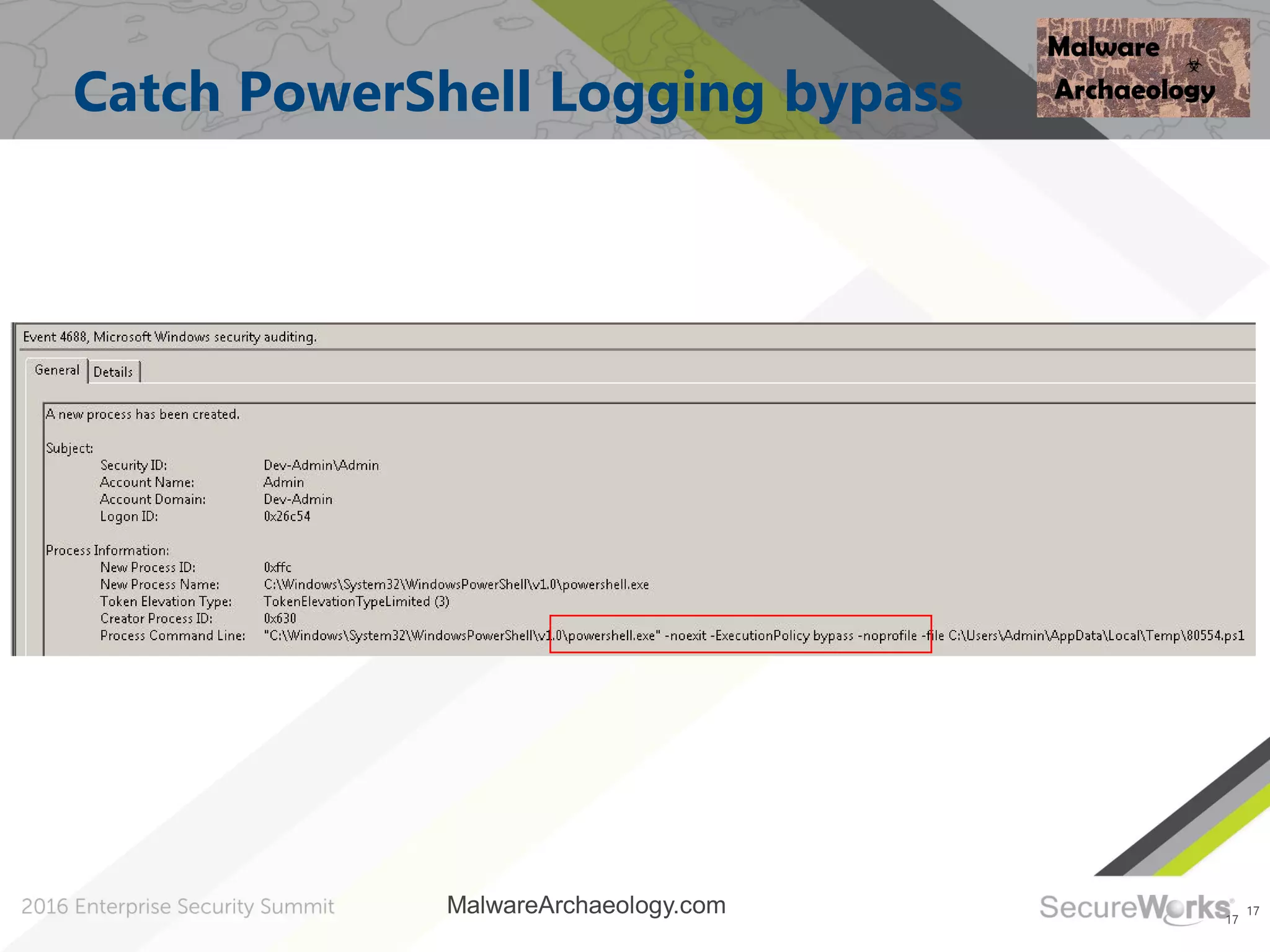
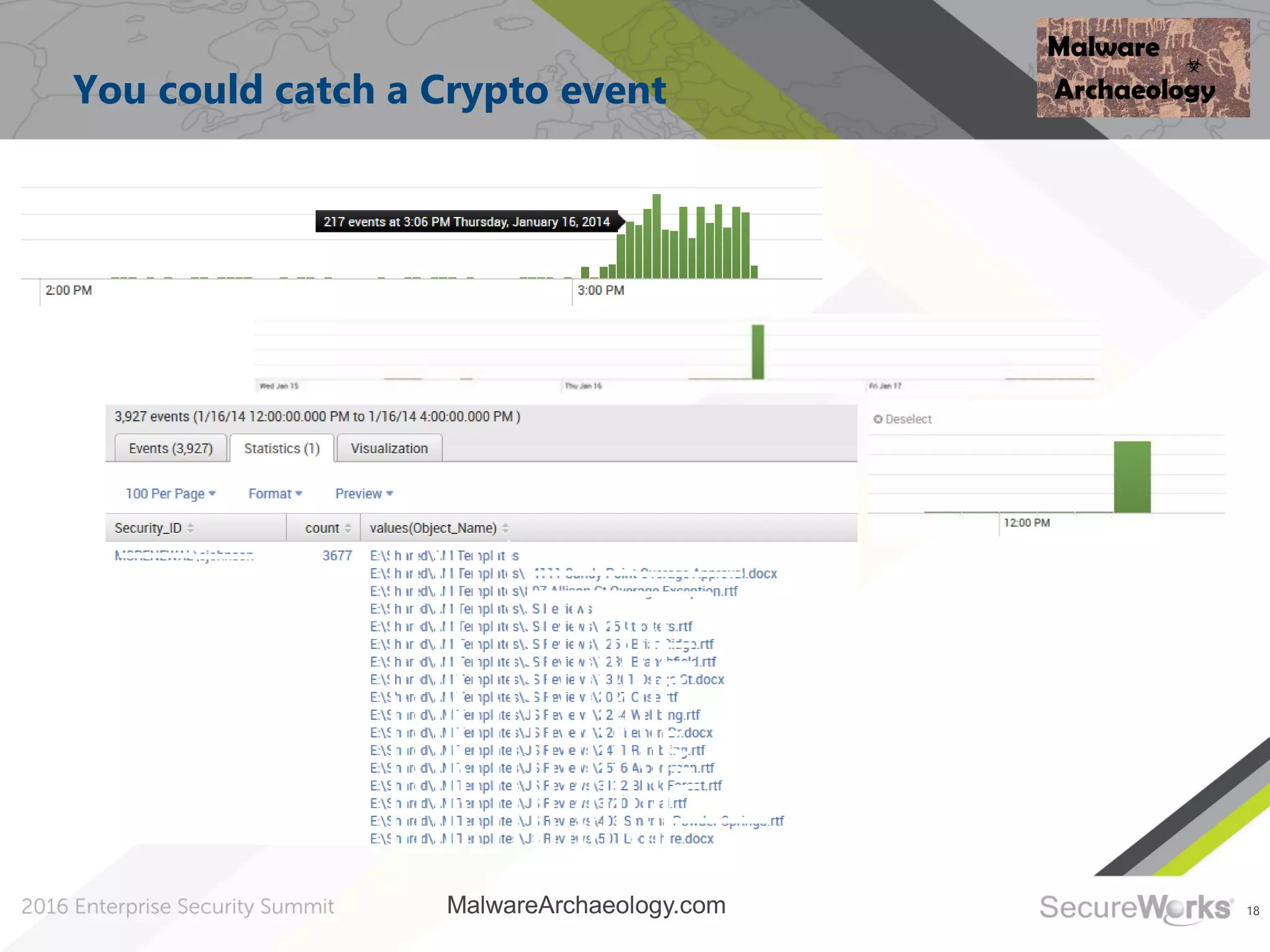
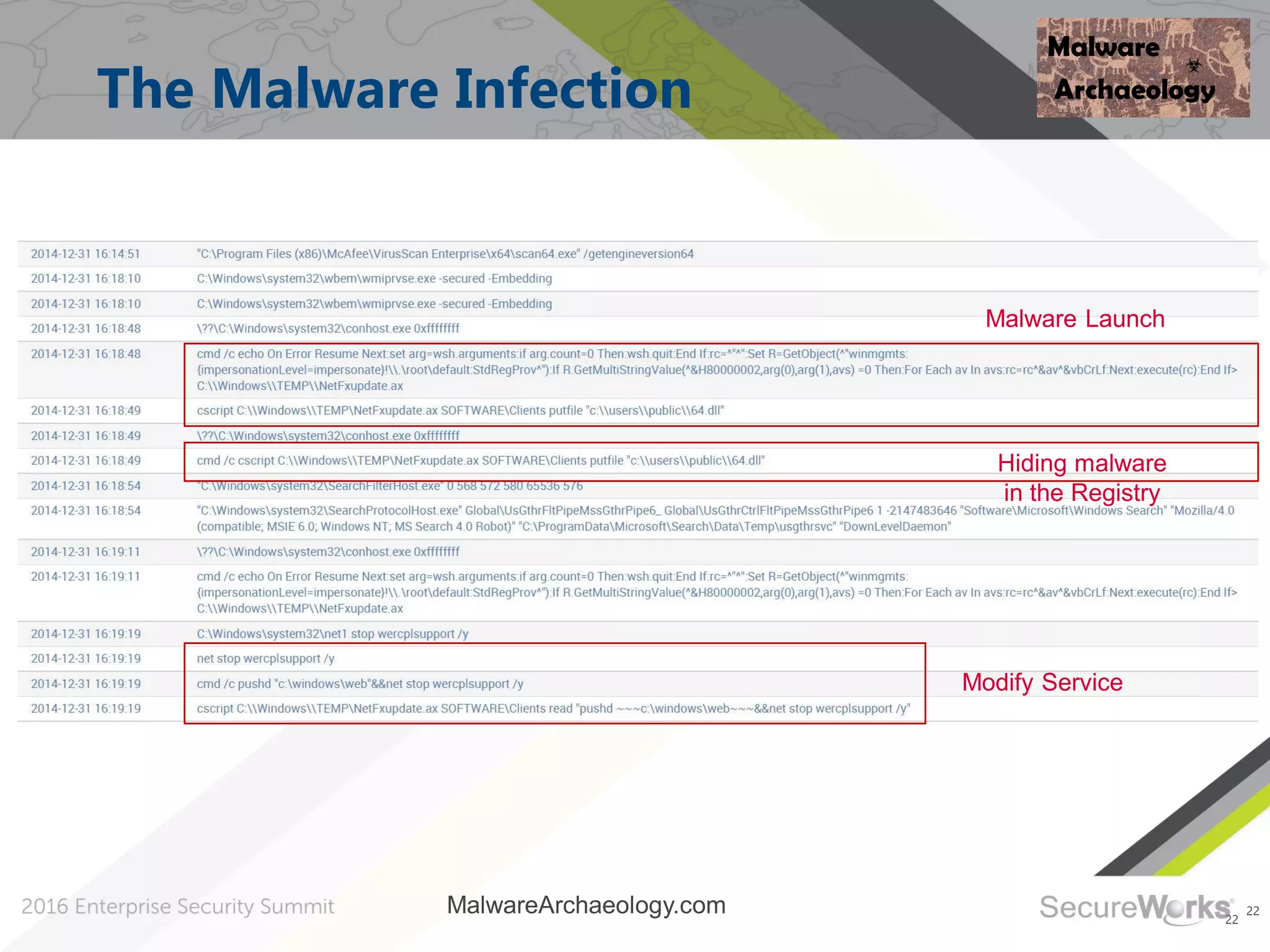
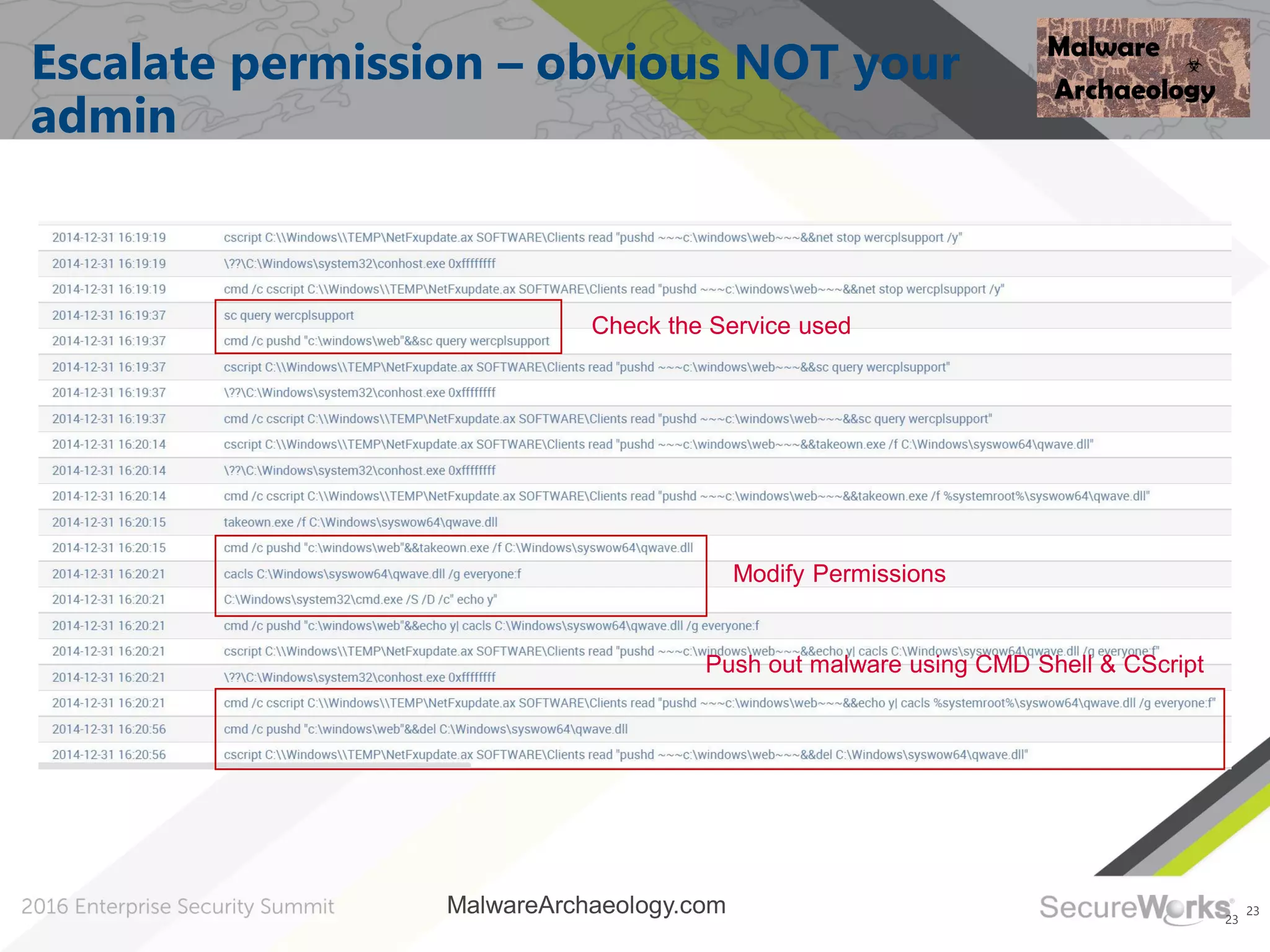
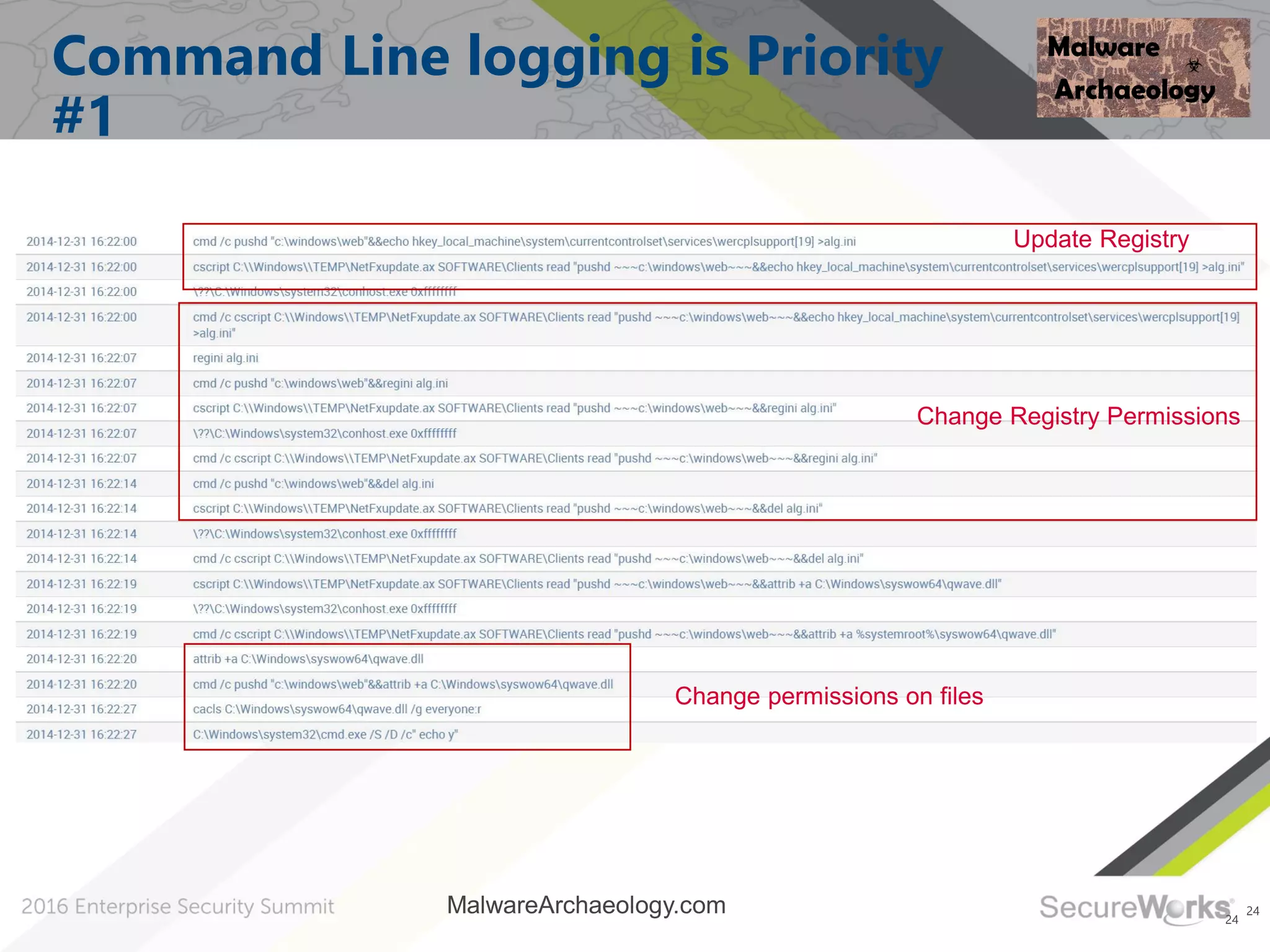
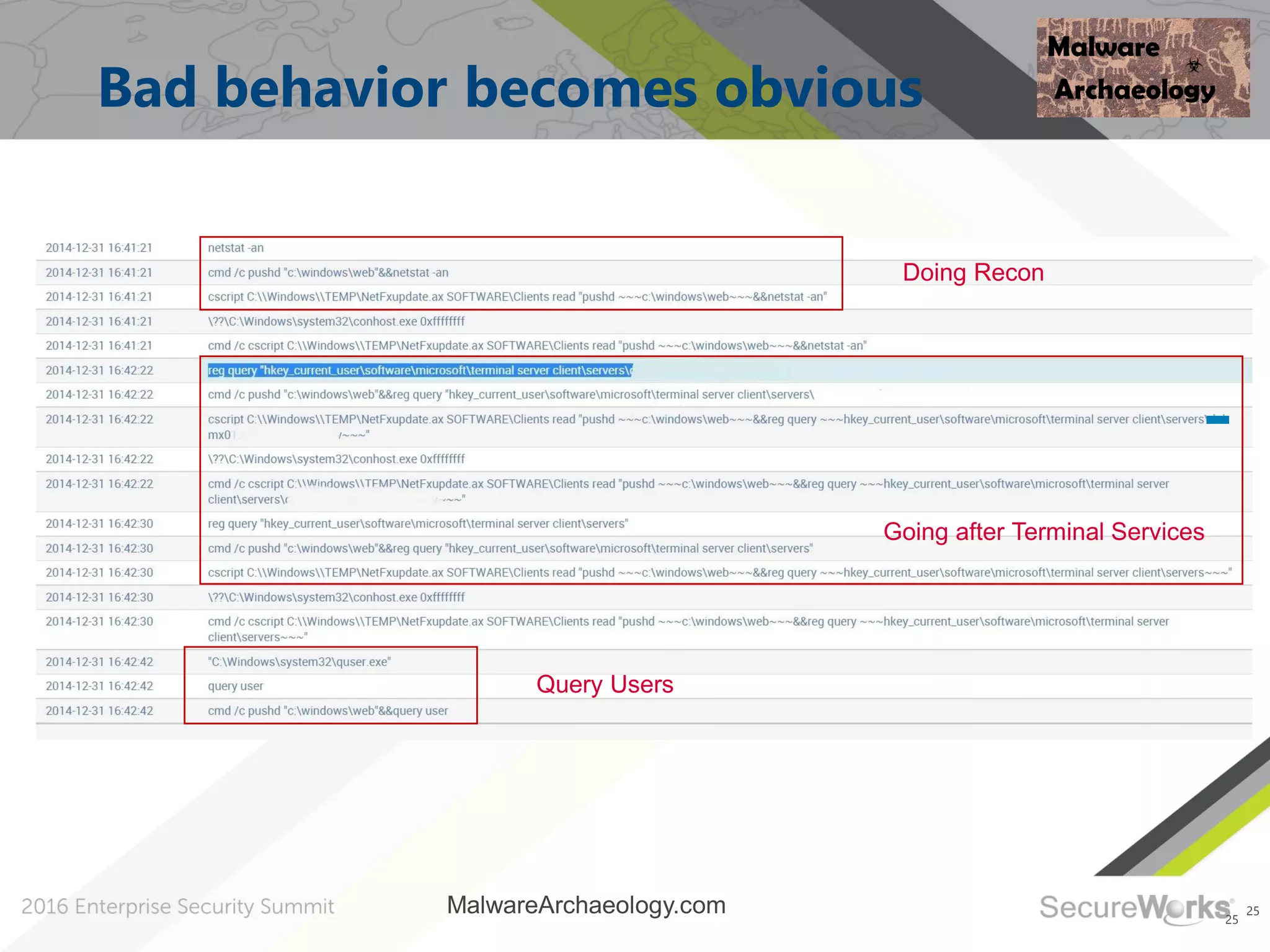
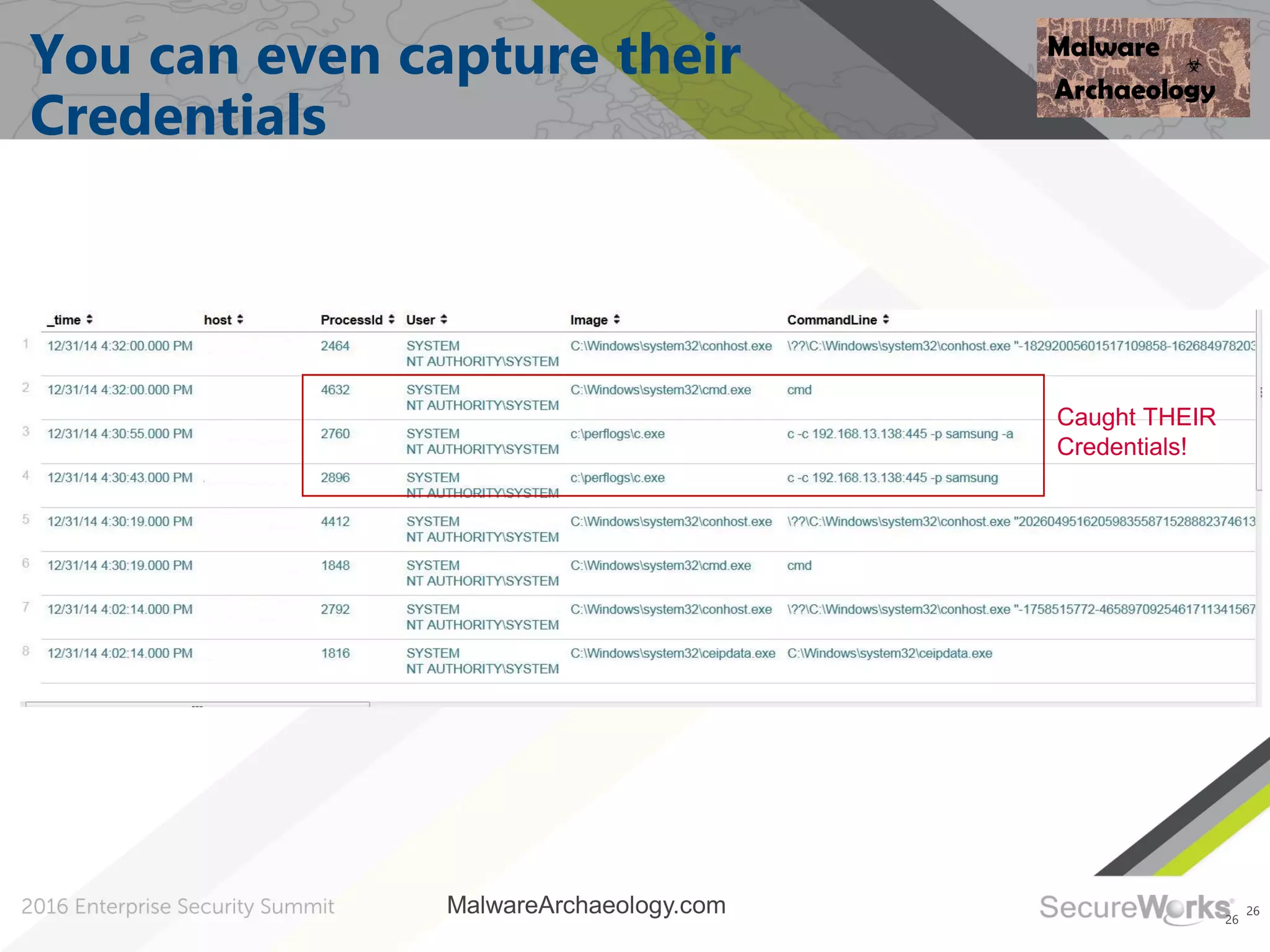
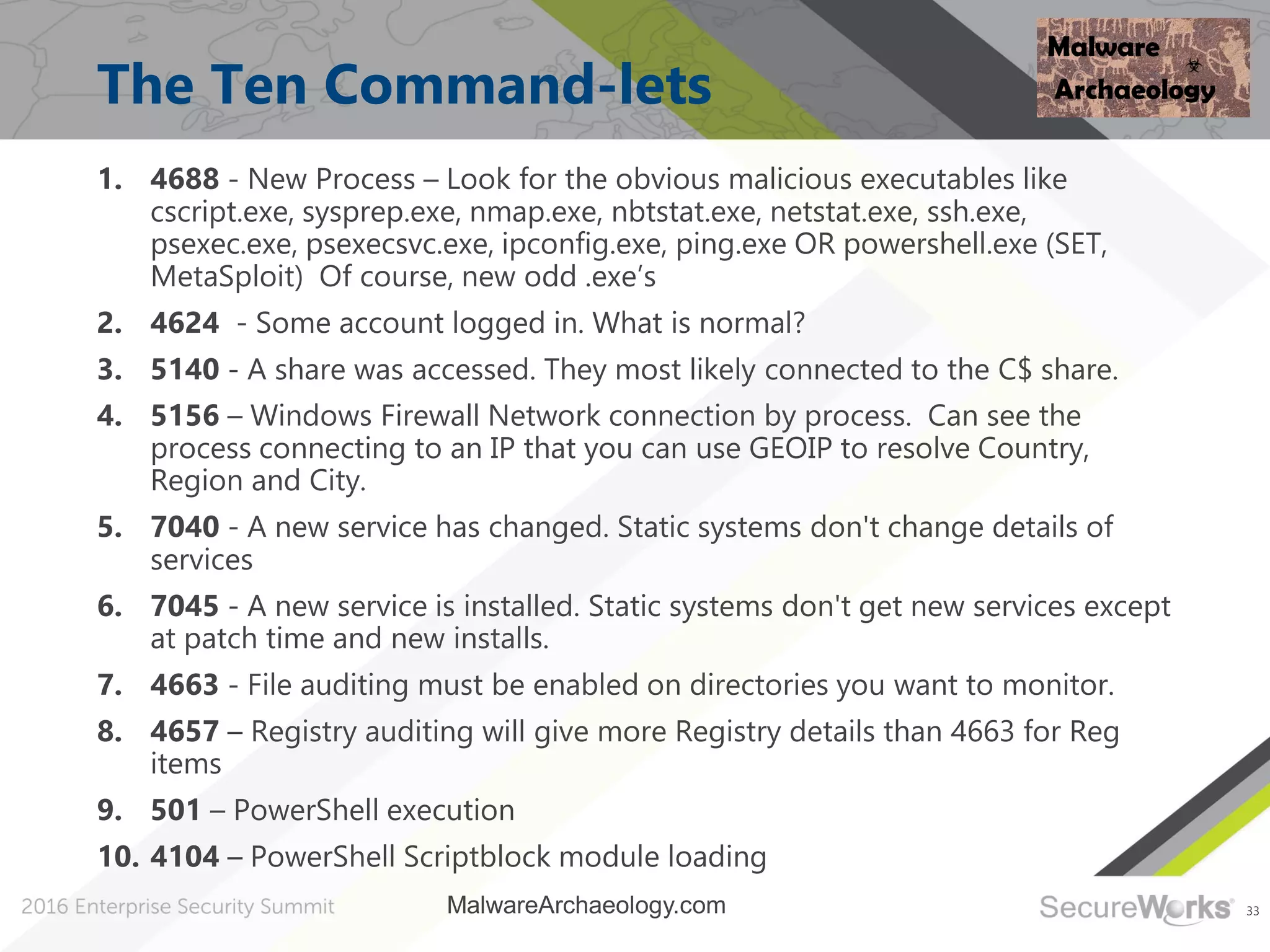
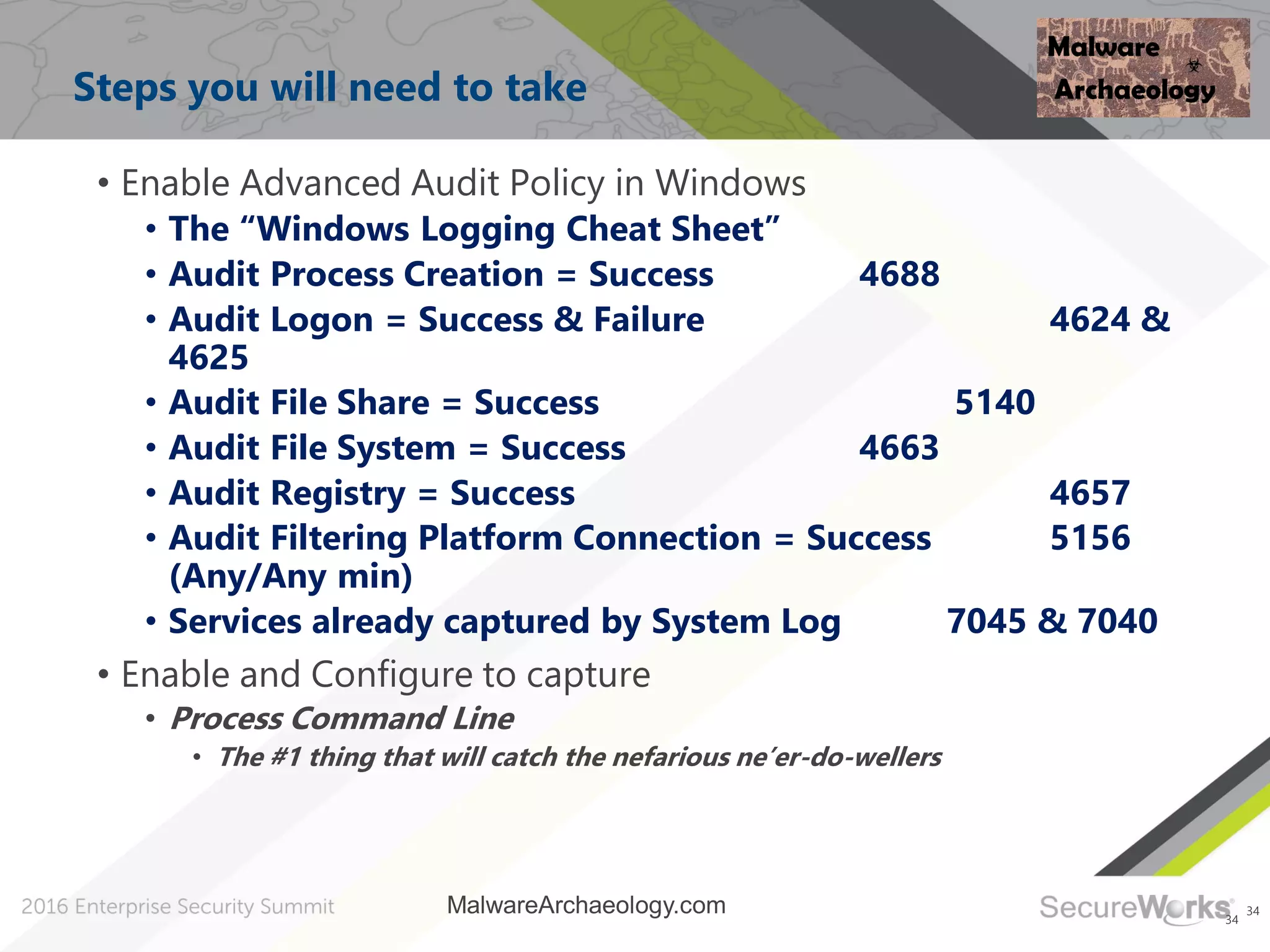
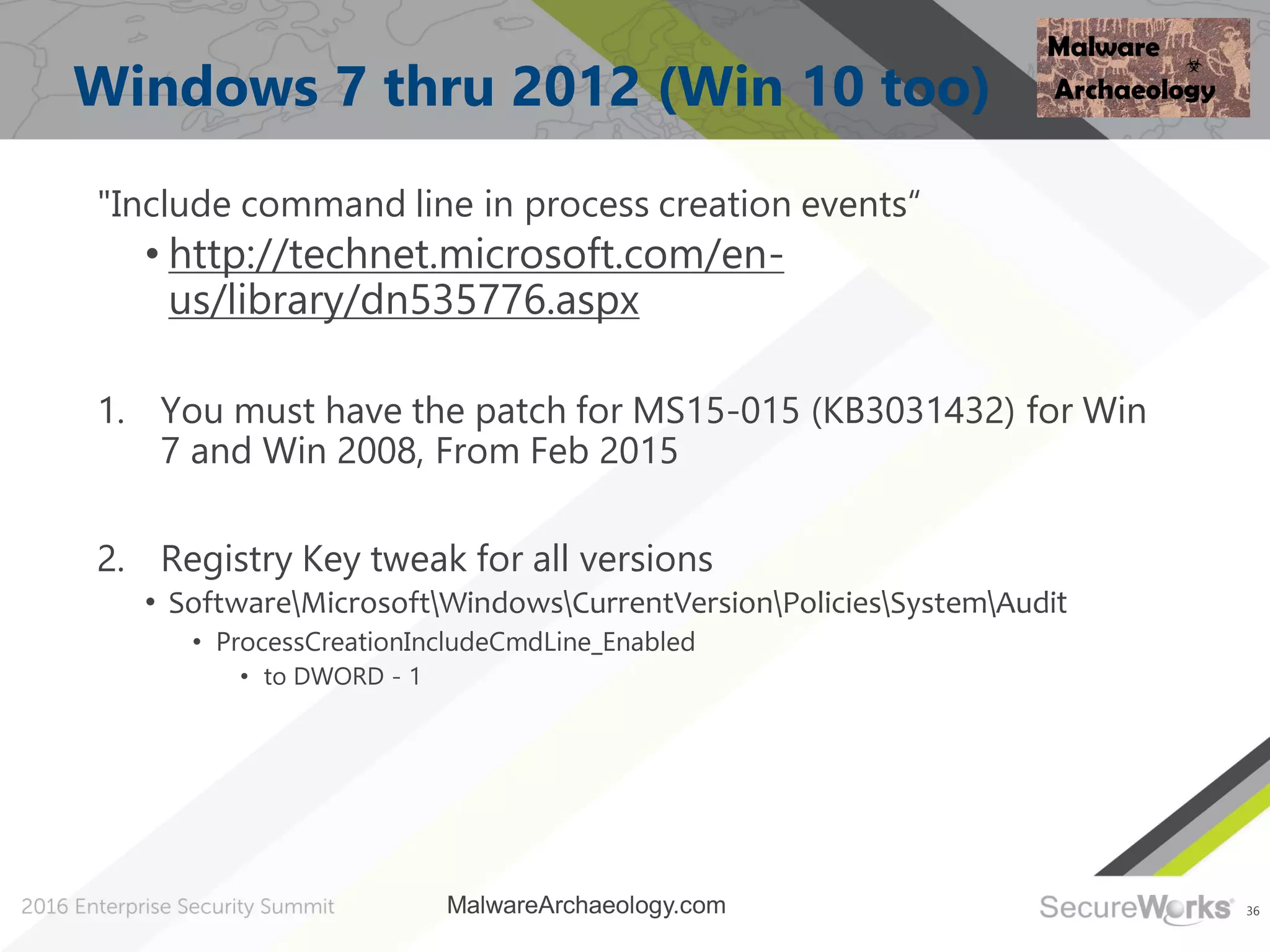
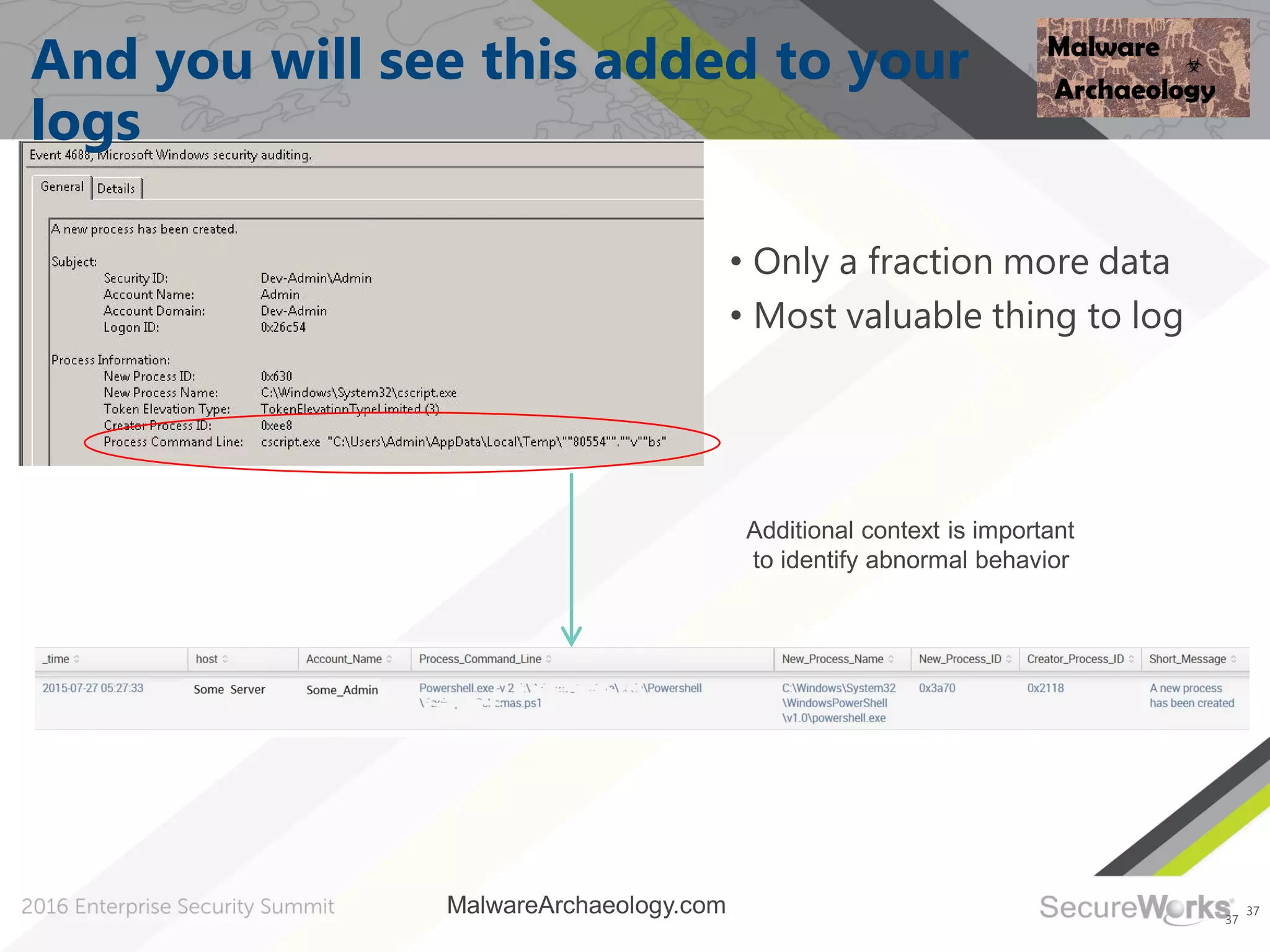
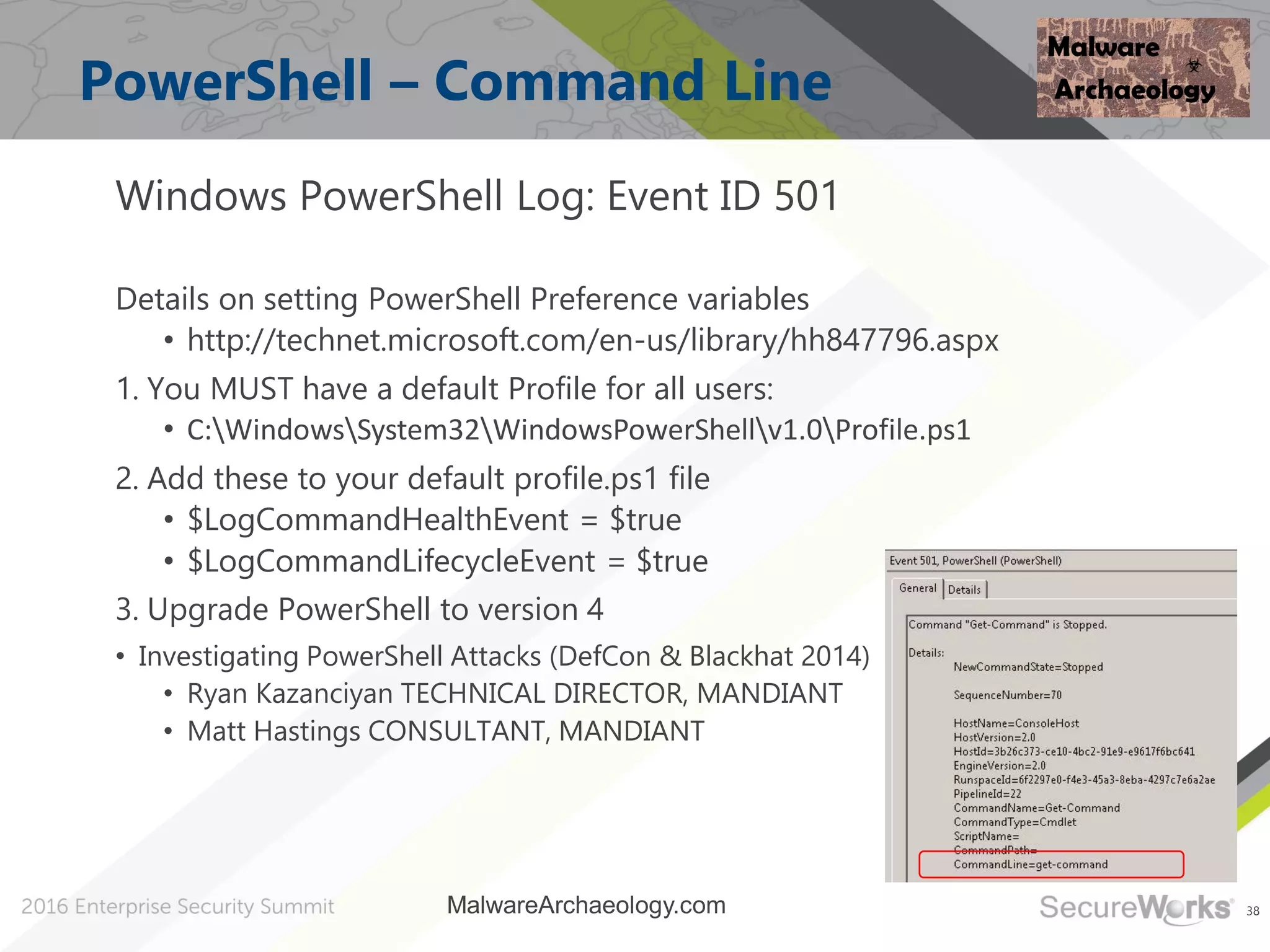
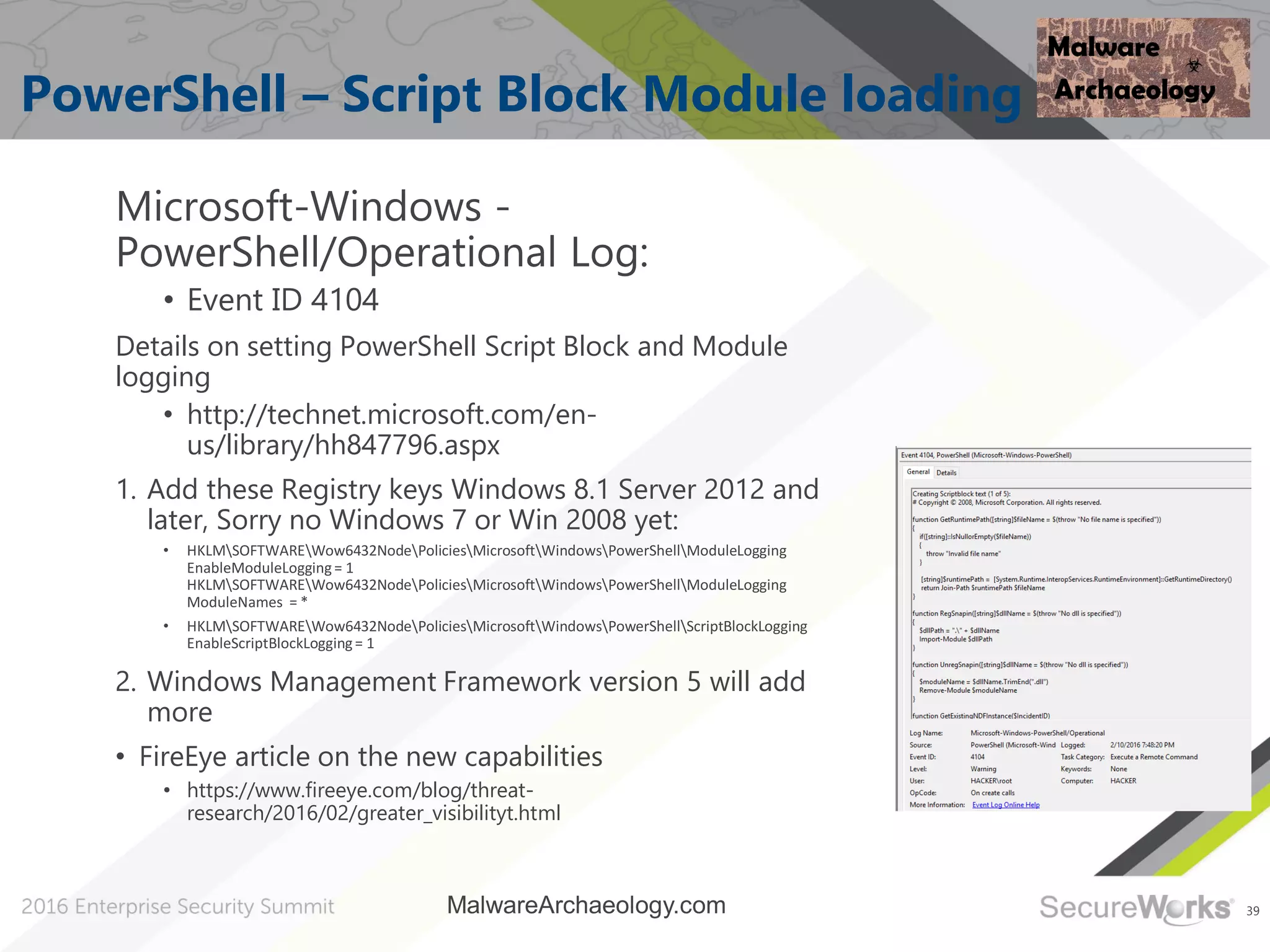
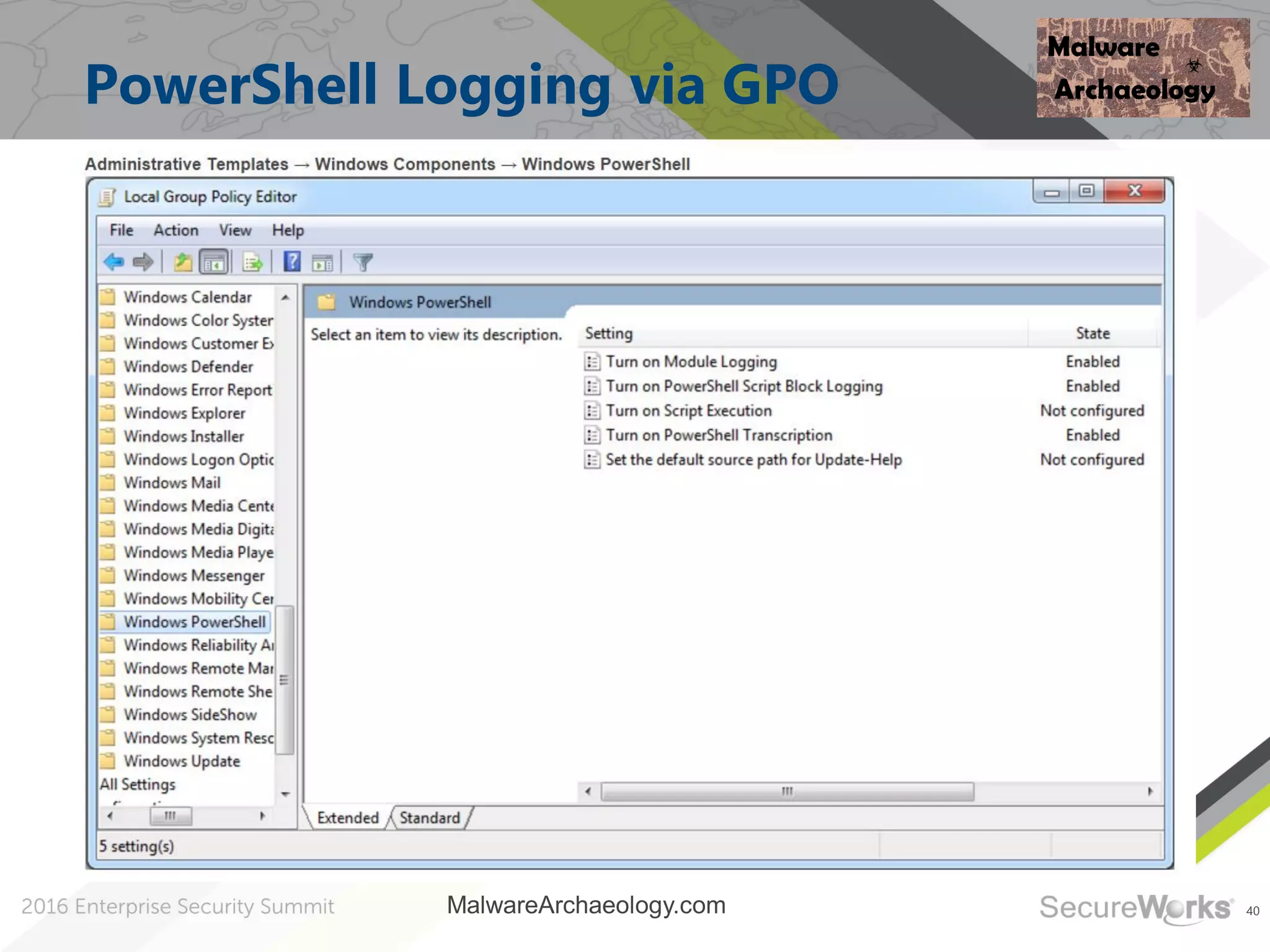
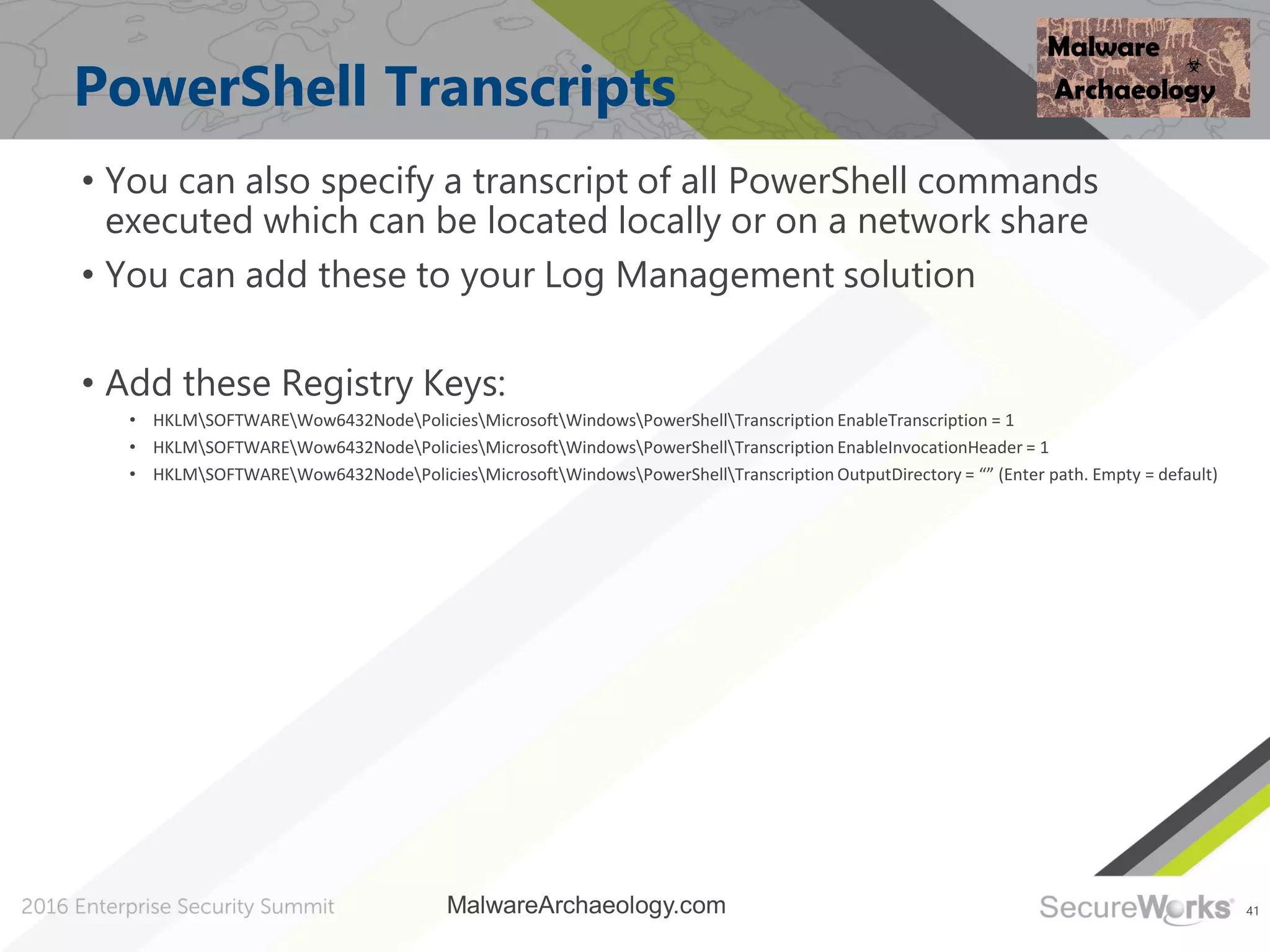
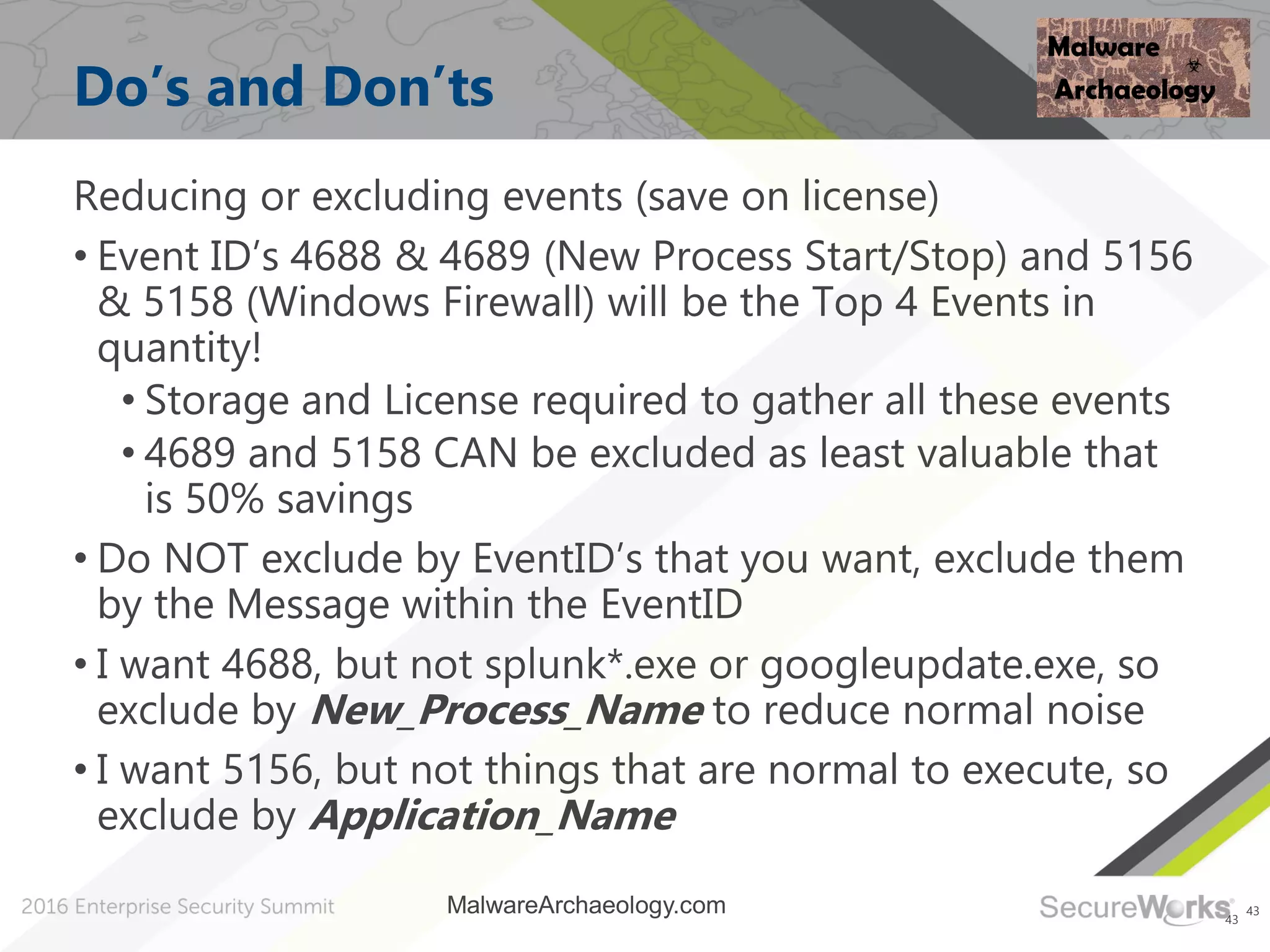
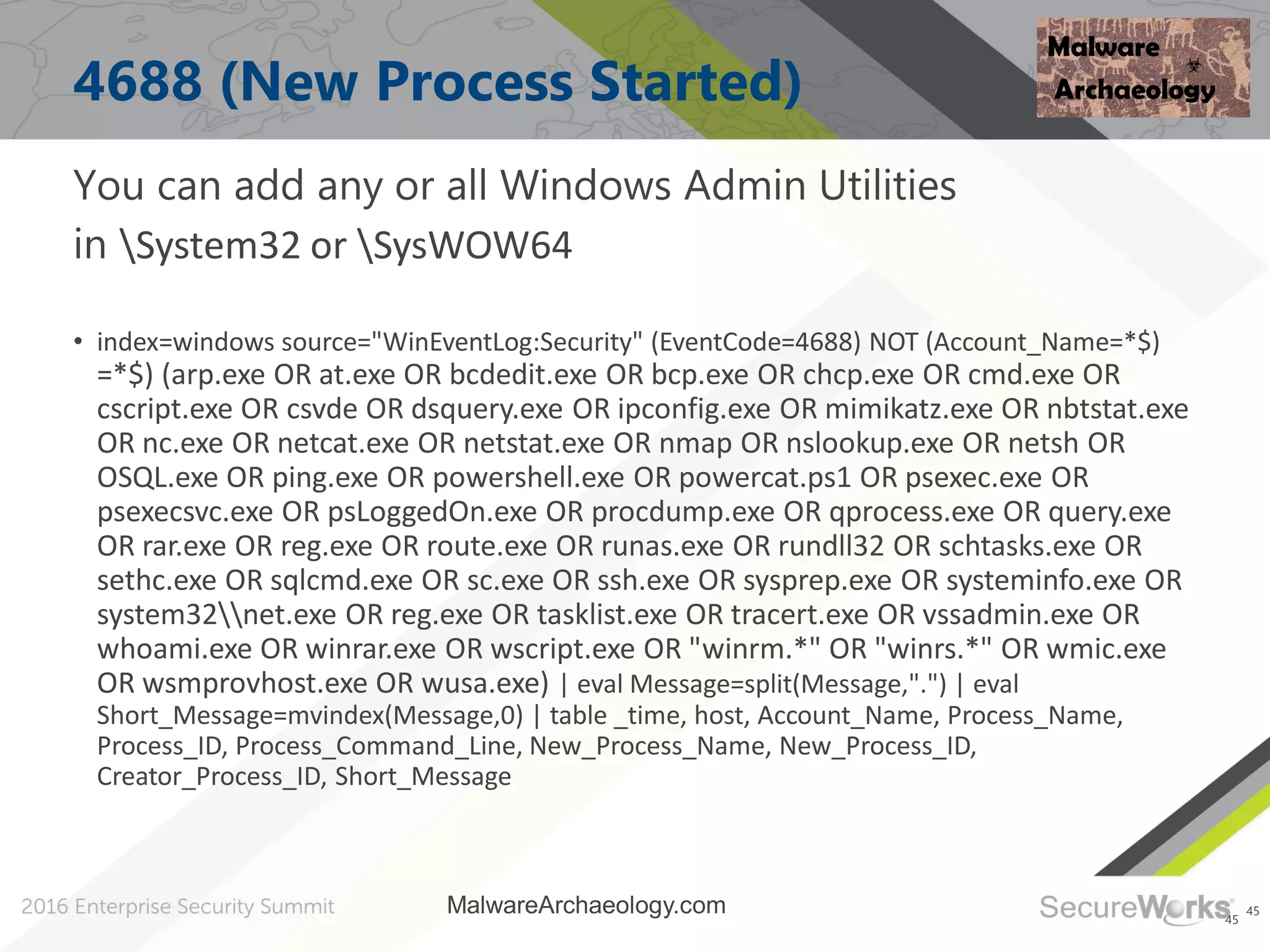
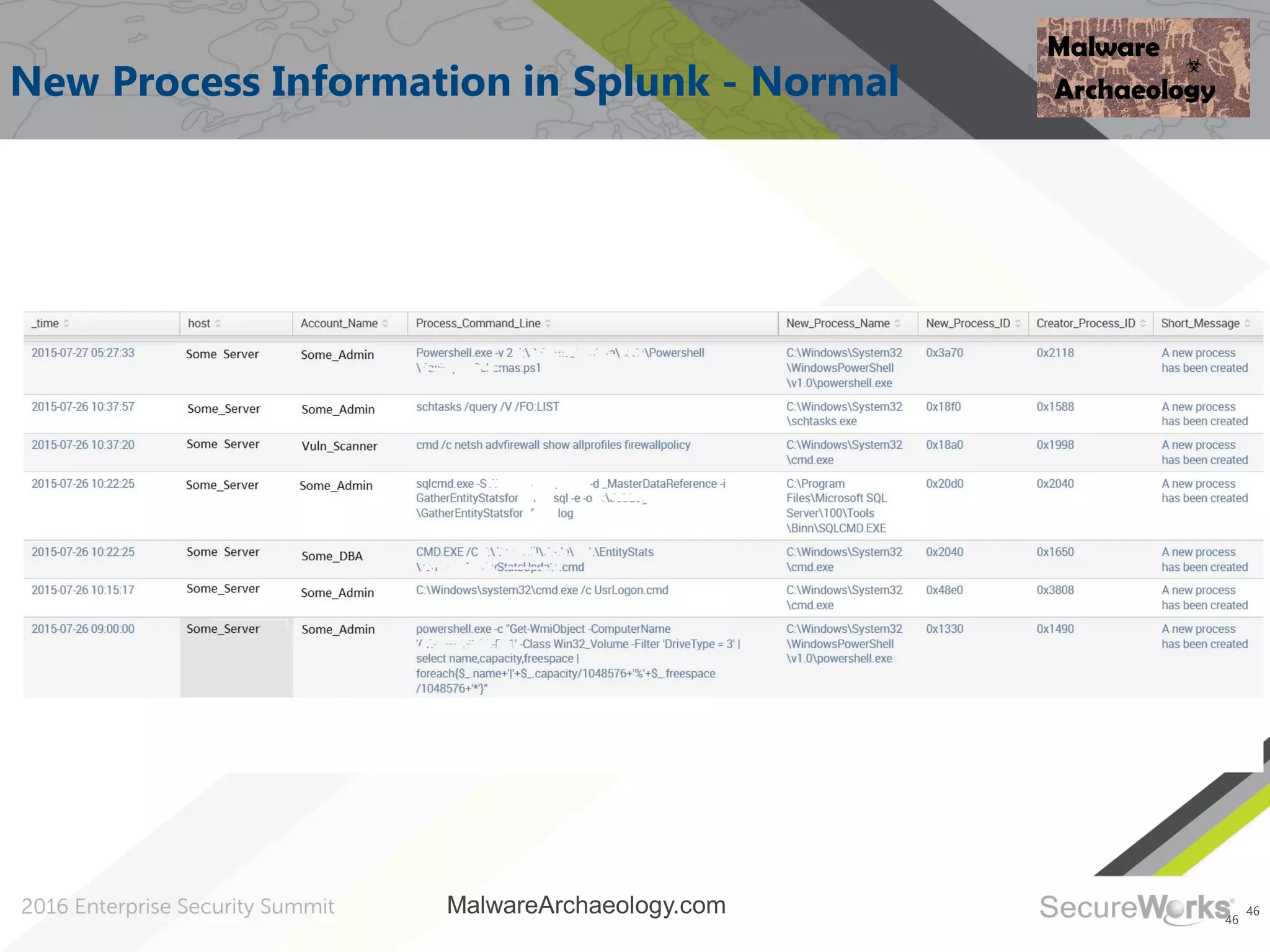
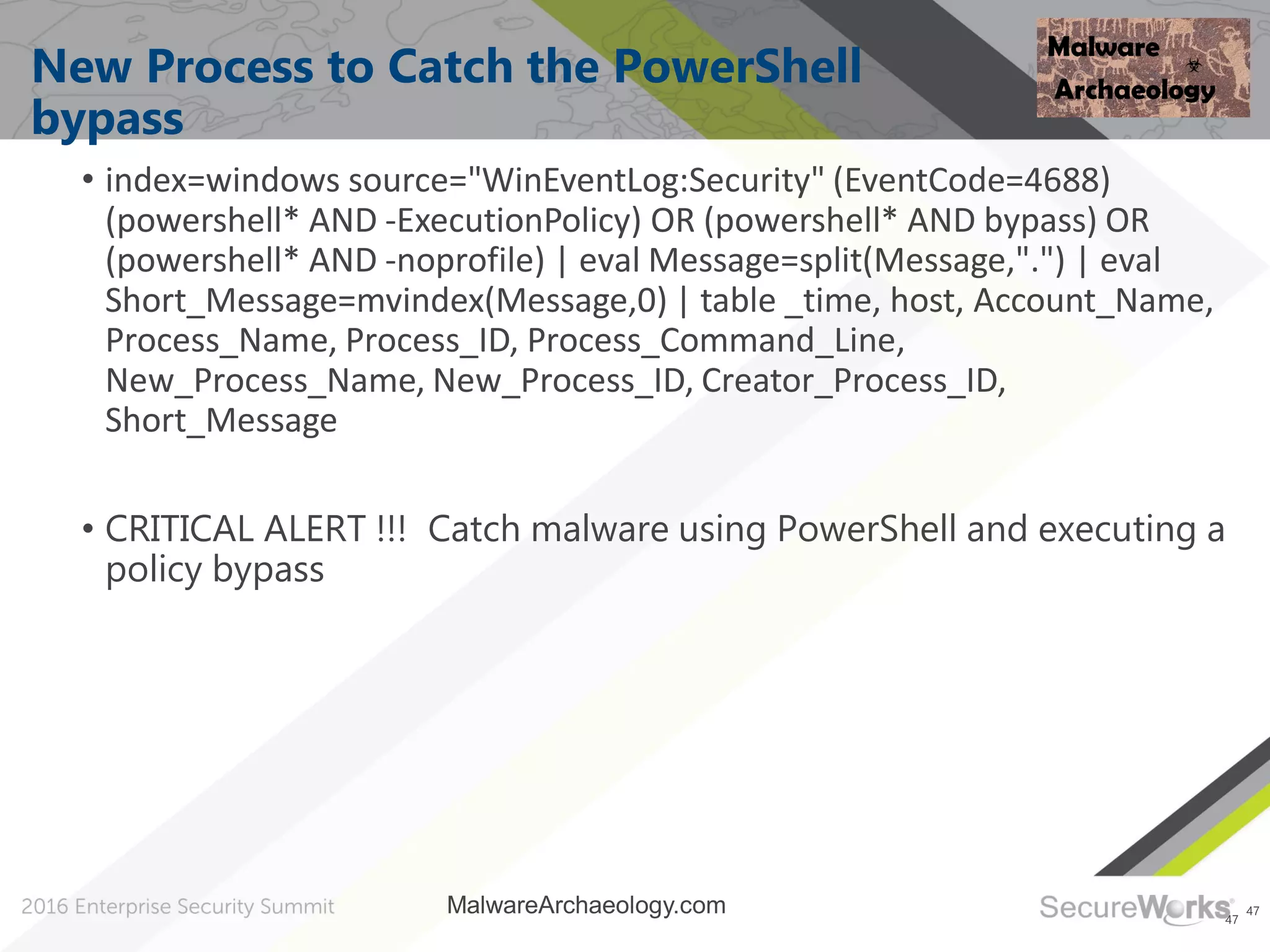
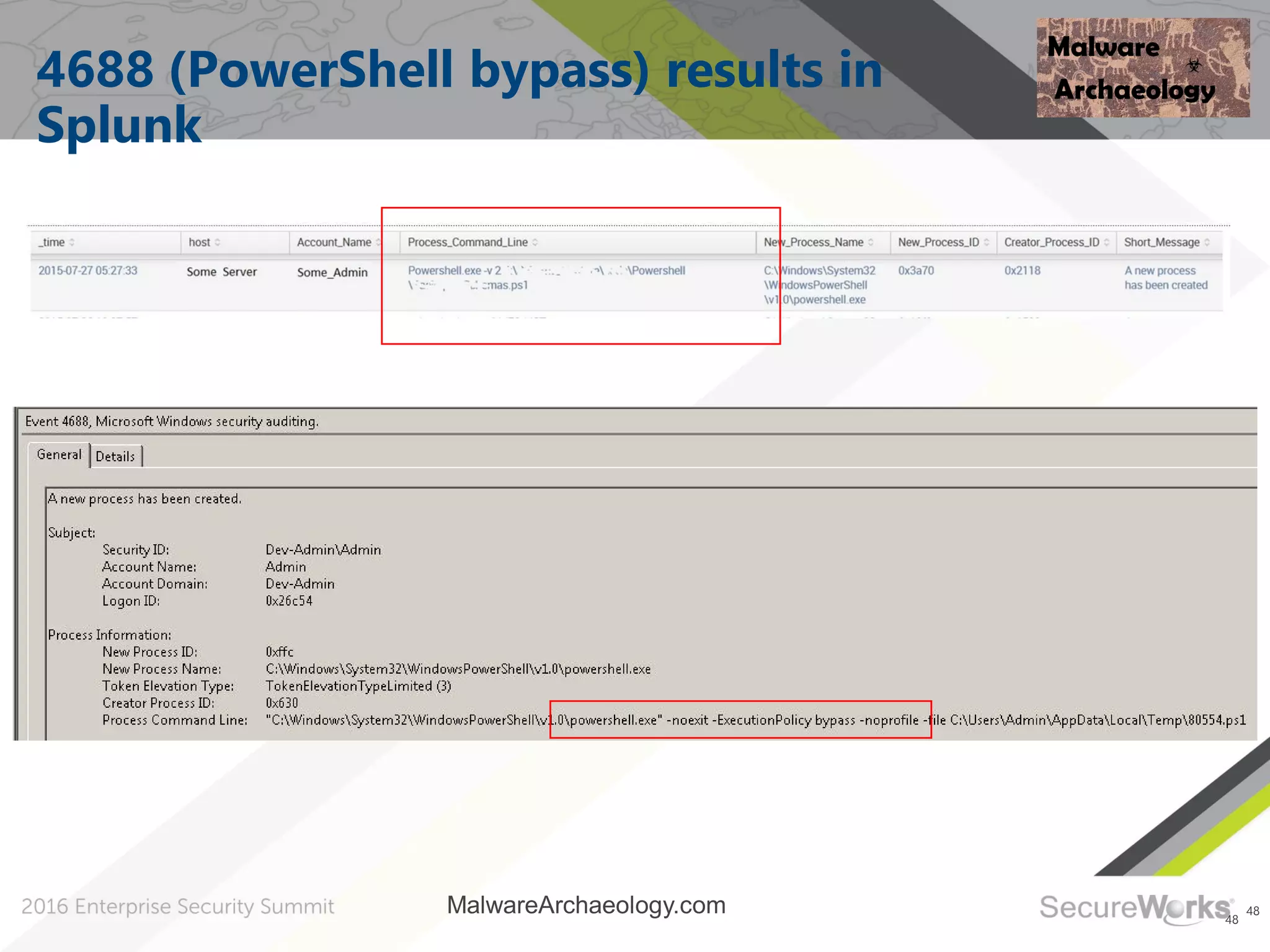
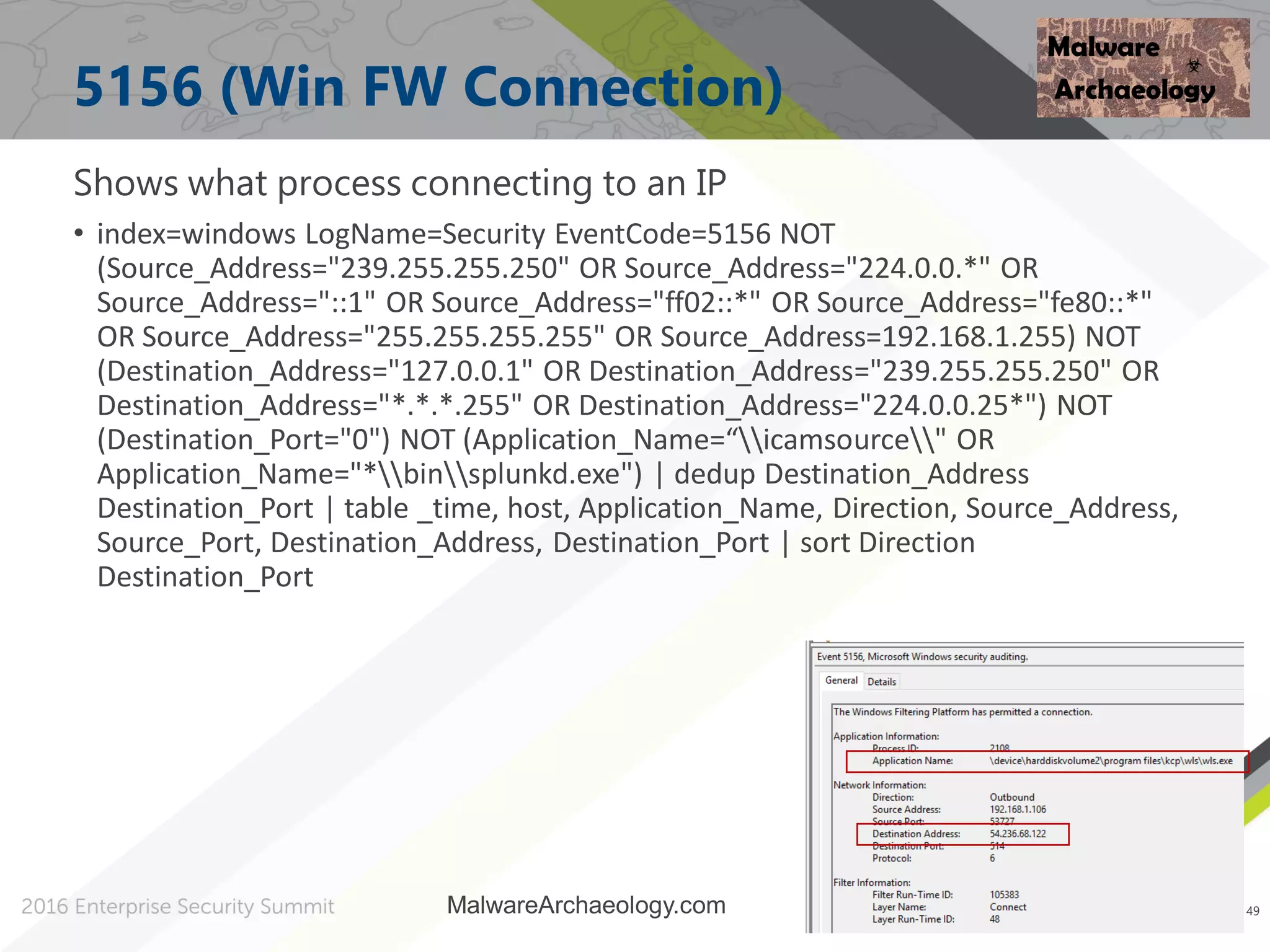
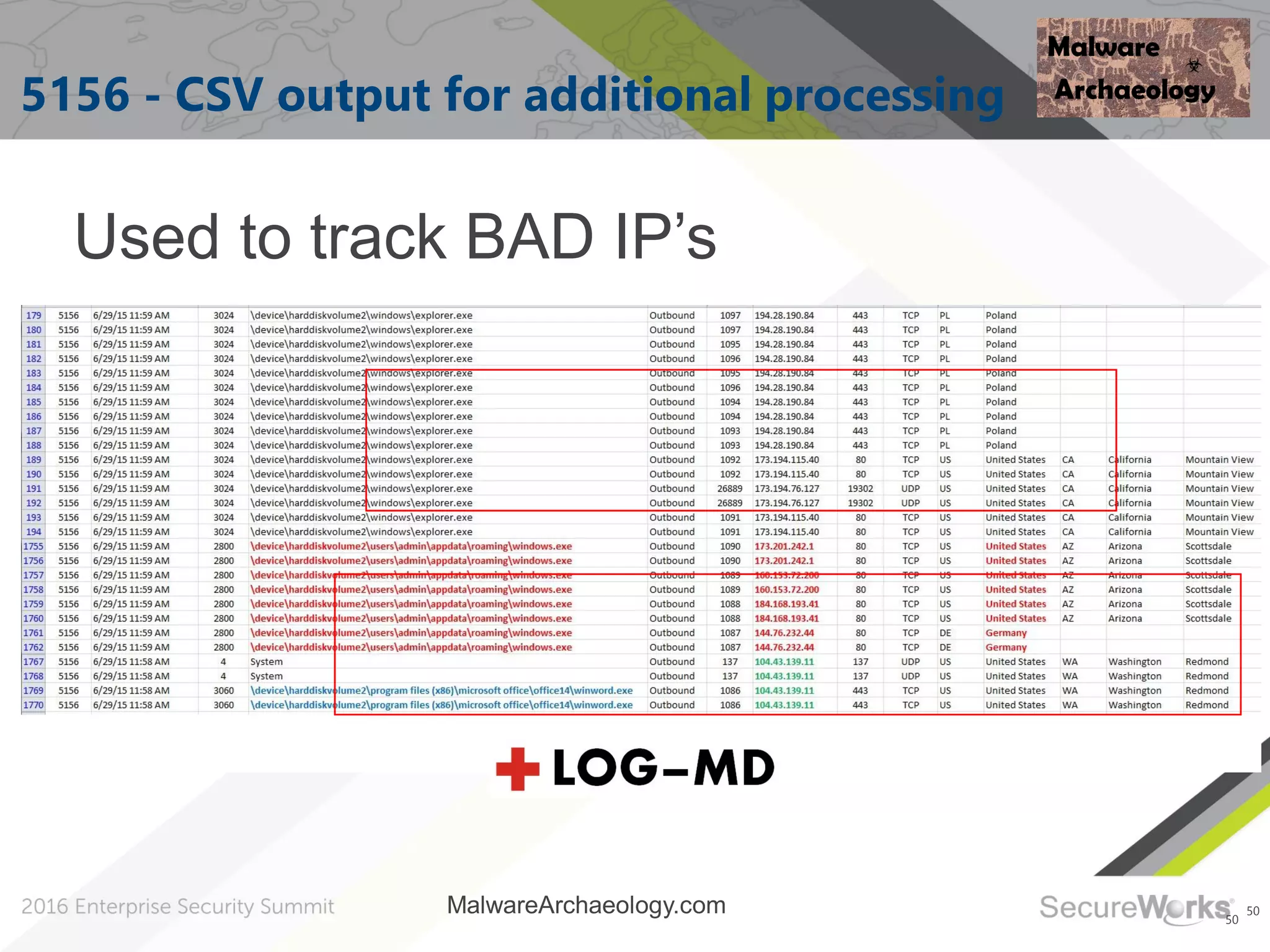
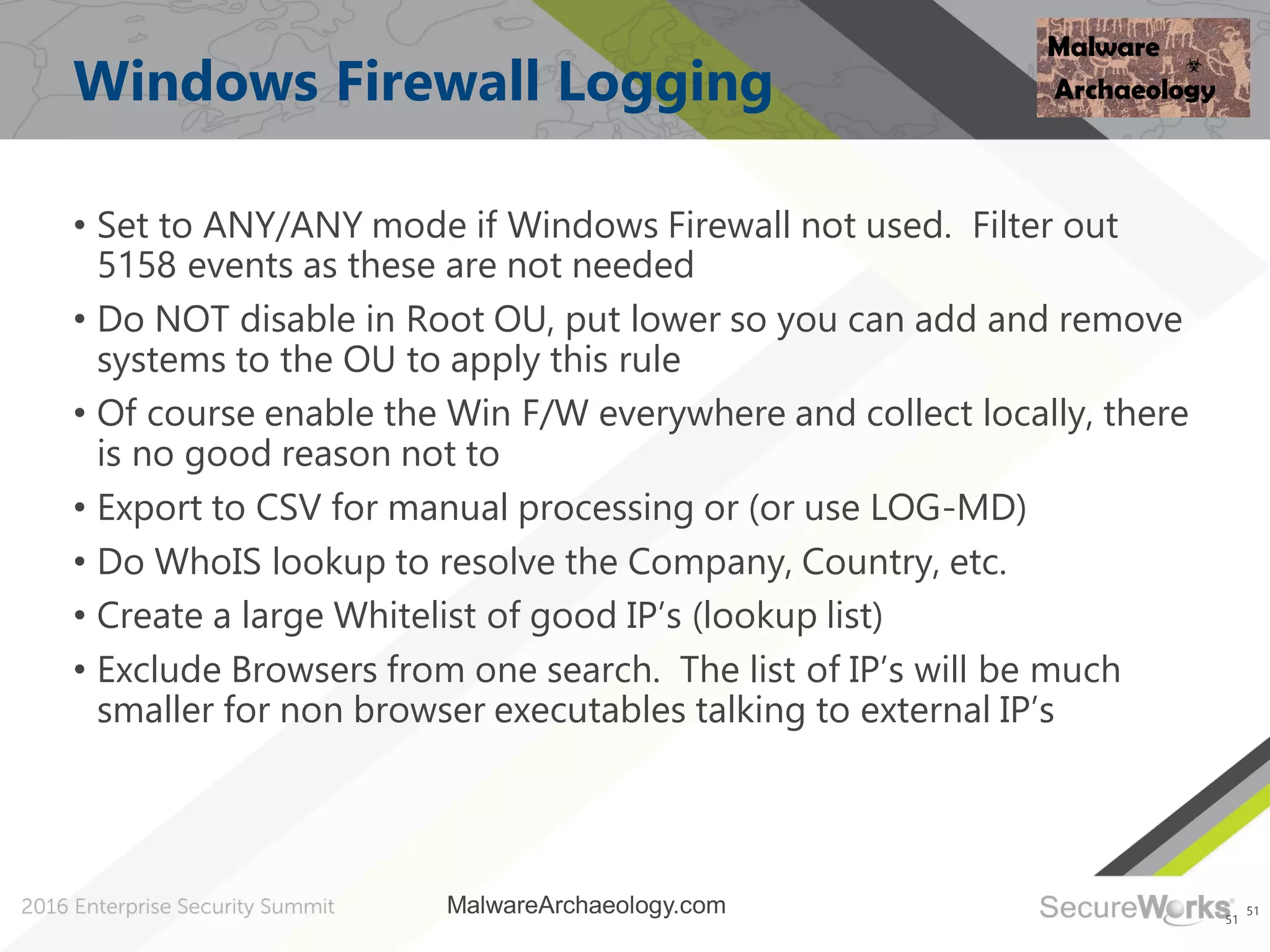
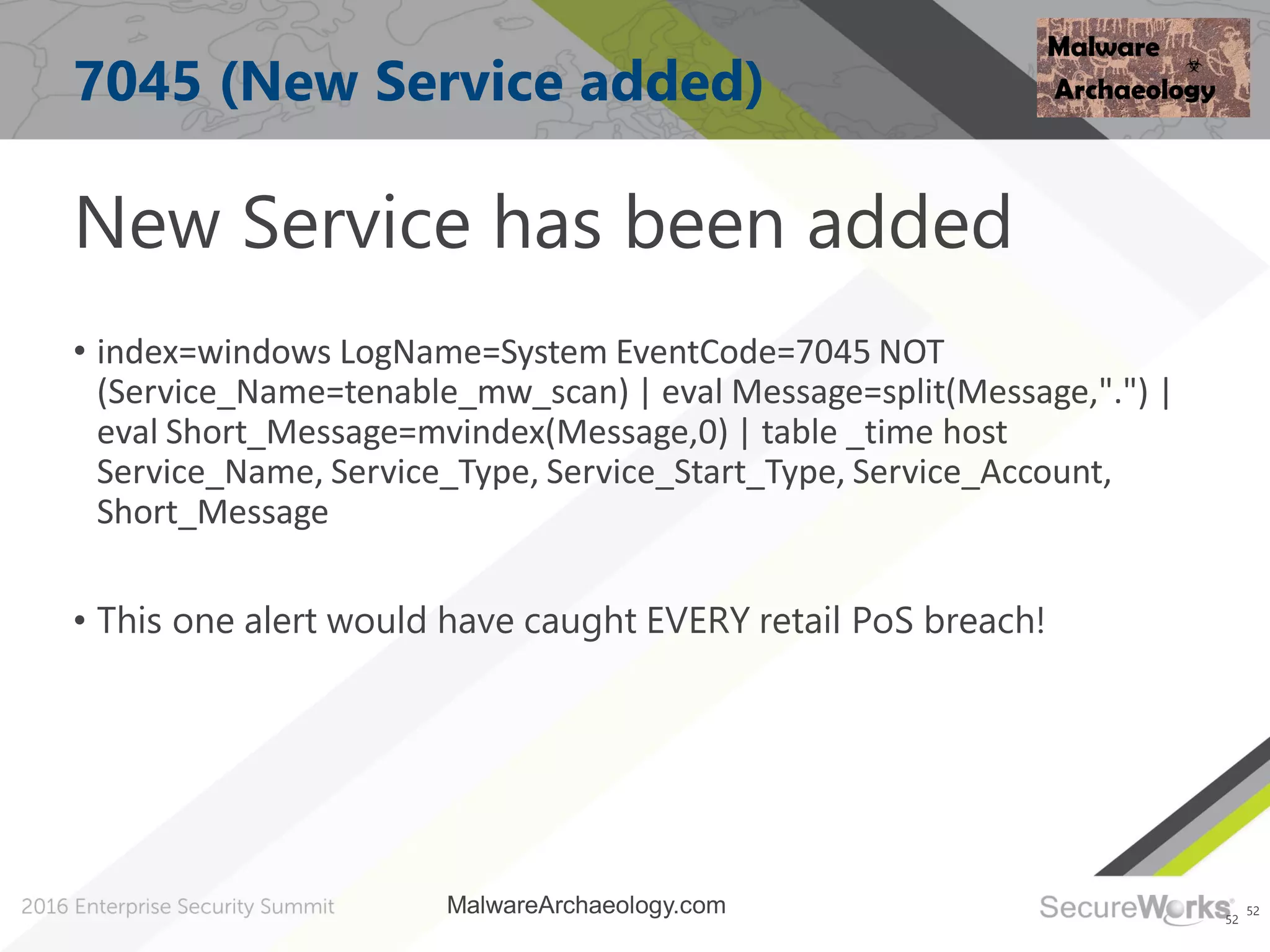
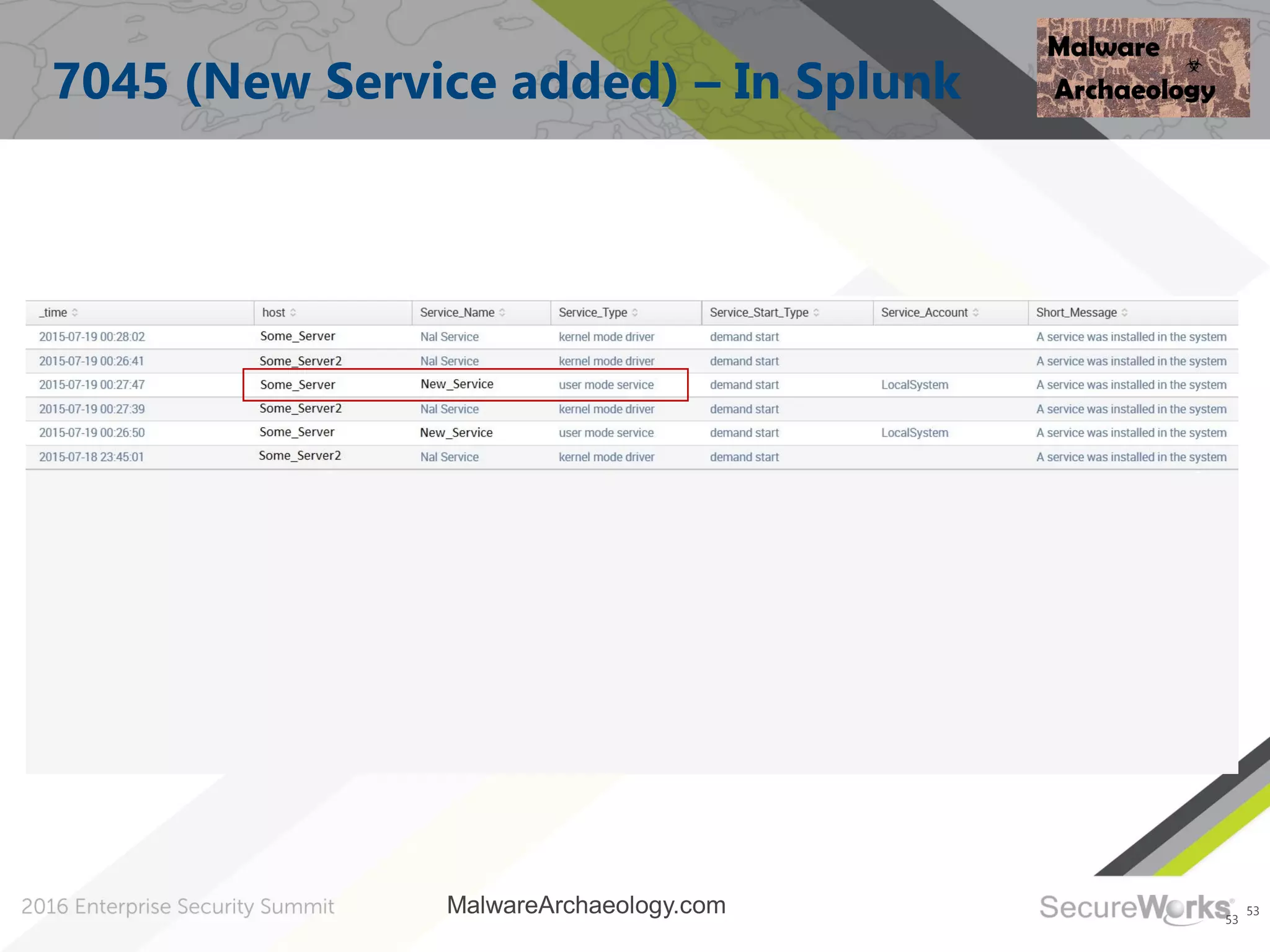
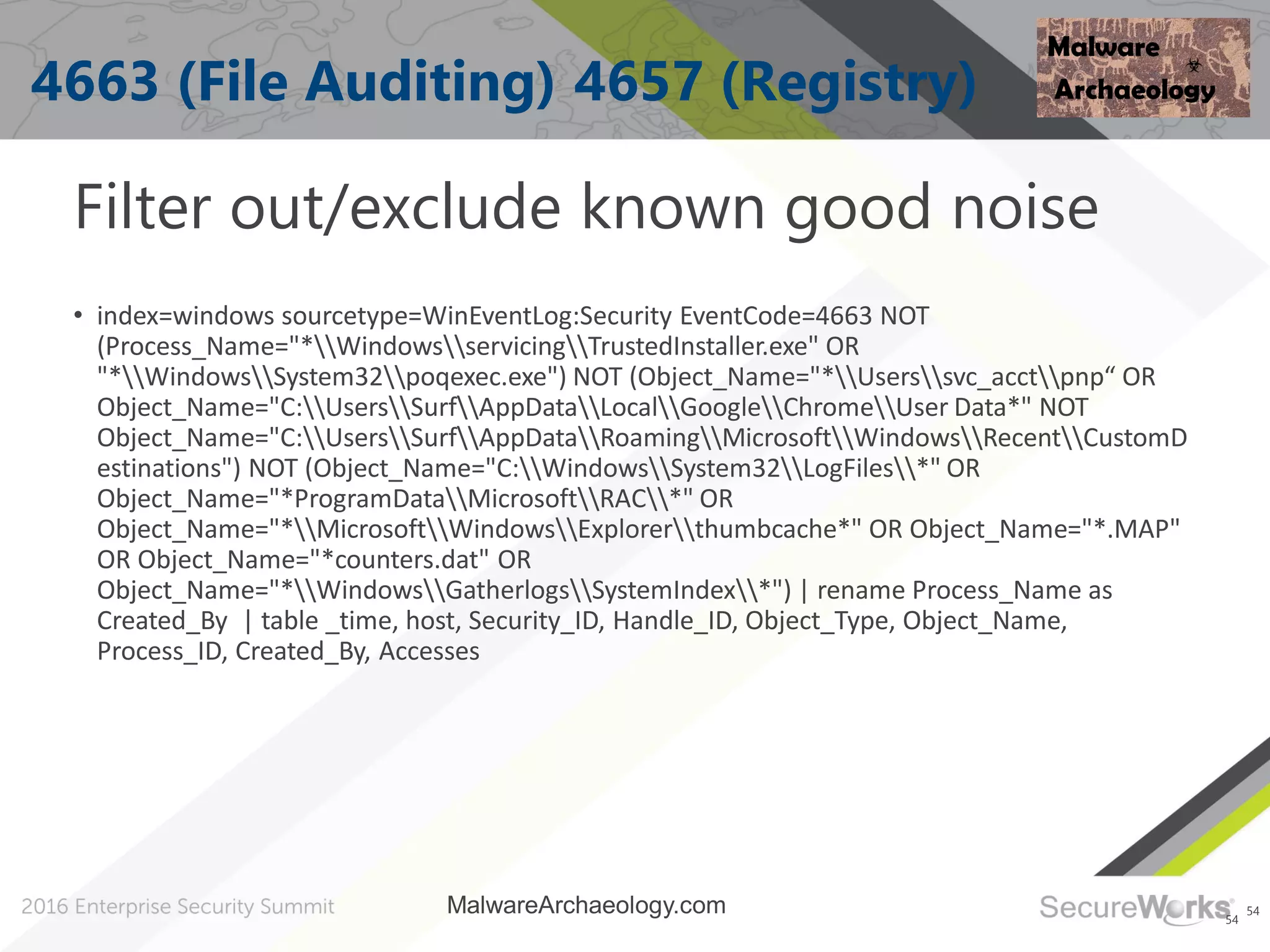
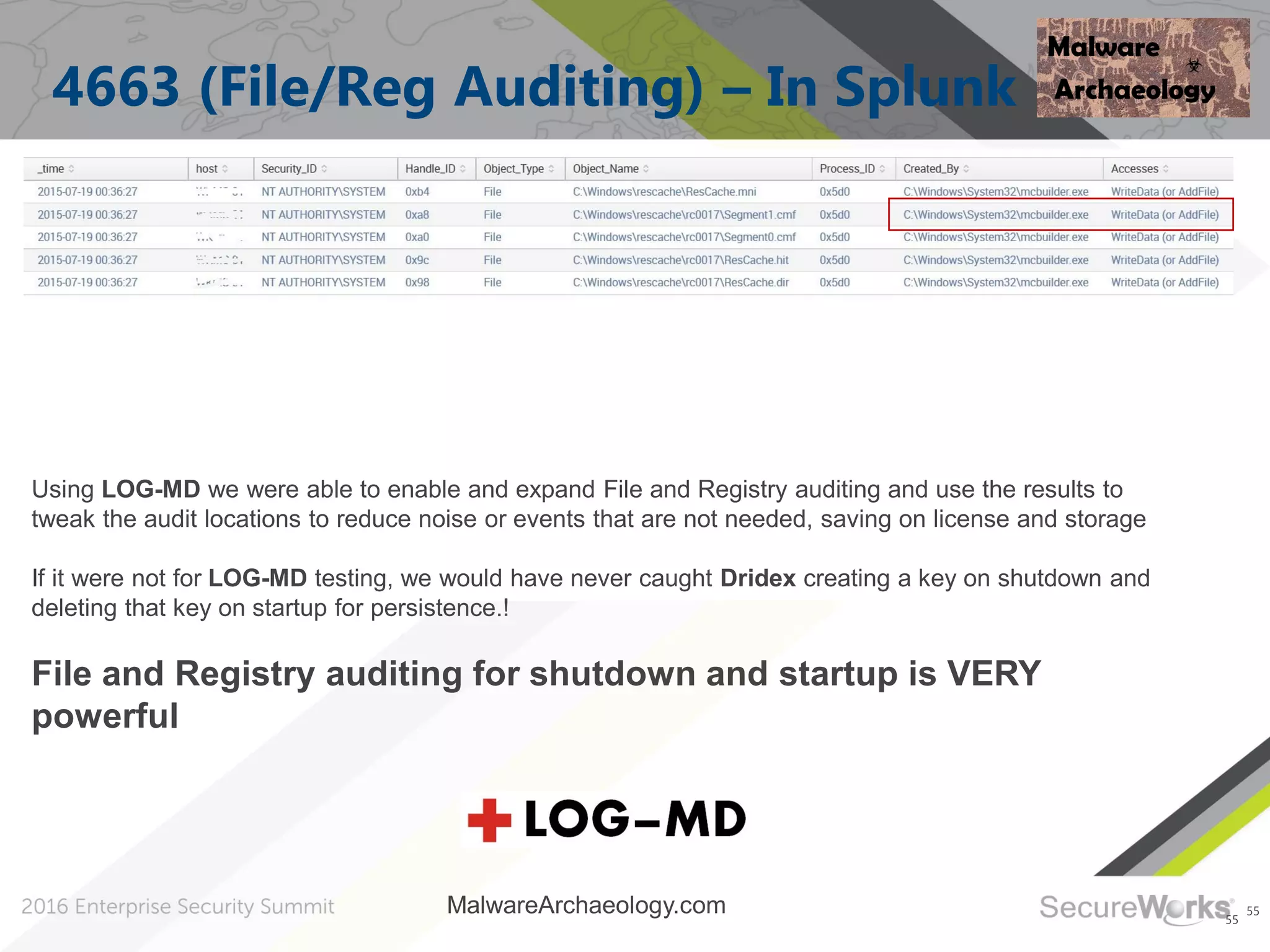
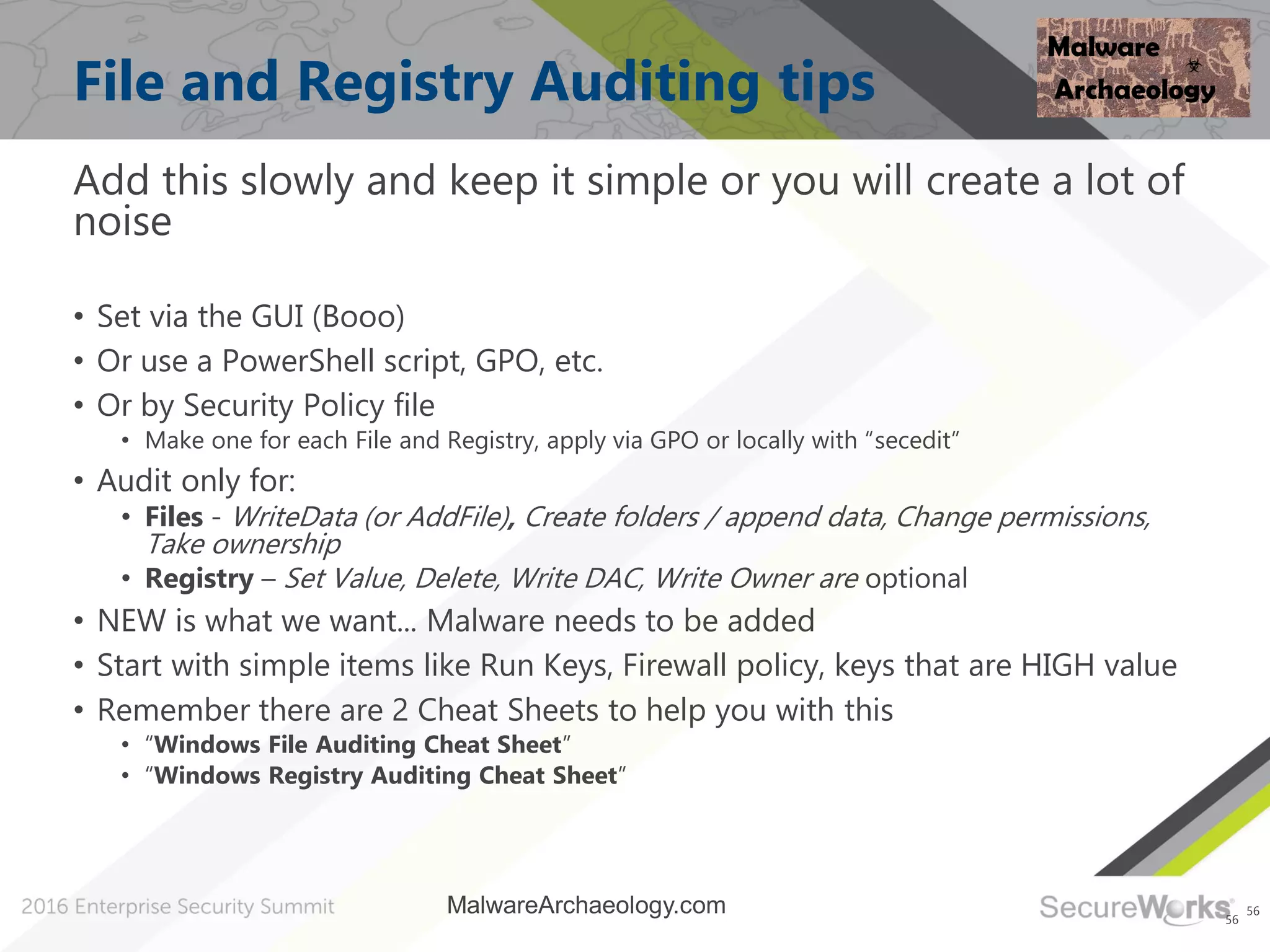
Michael Gough's presentation focuses on utilizing Windows logs to detect and respond to cyberattacks by highlighting the top 10 Windows Event IDs crucial for incident response. He discusses the importance of proper log configuration to uncover malware activities, detailing strategies and methods to improve detection capabilities. The talk emphasizes the significance of continuous monitoring and adapting defenses against evolving malware threats.