Embed presentation
Download as PDF, PPTX
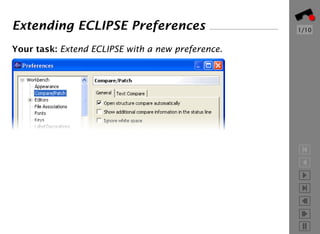
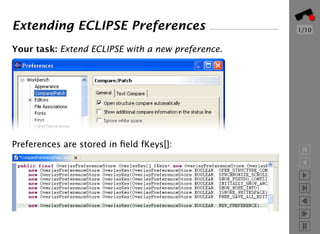
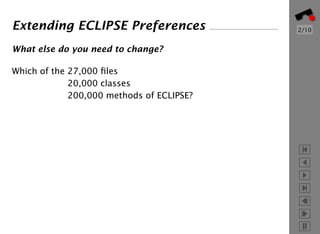
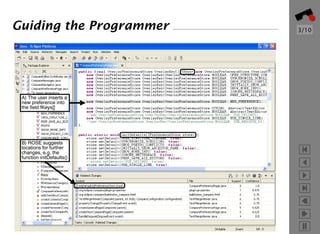
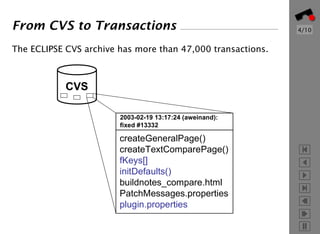
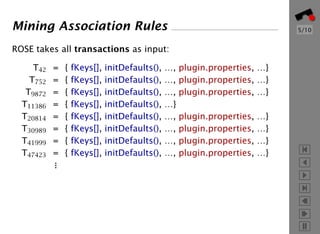
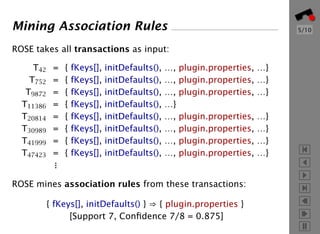
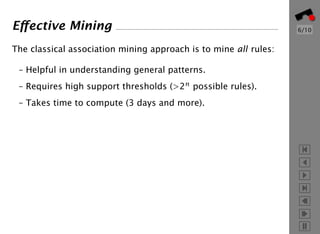
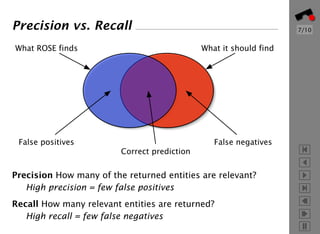
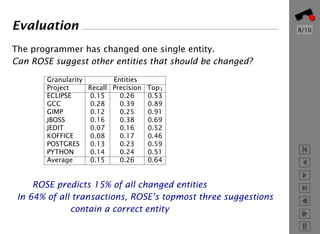
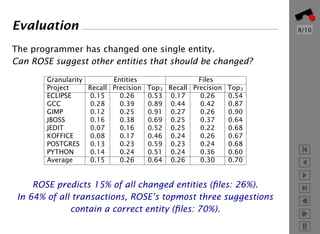
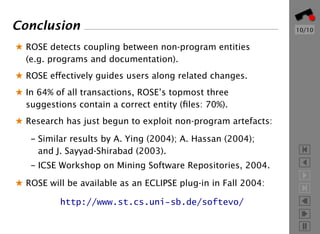

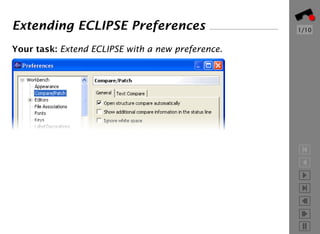
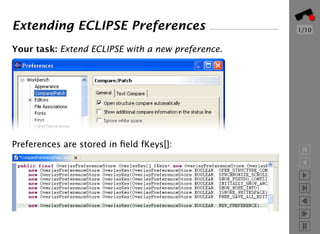
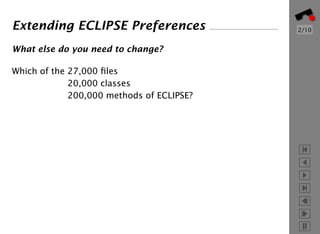
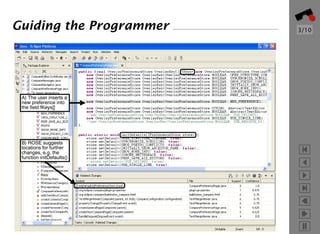
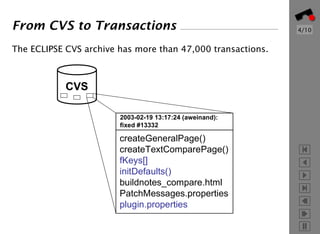
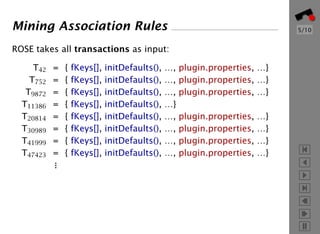
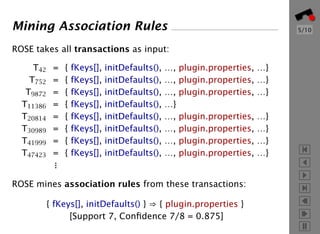
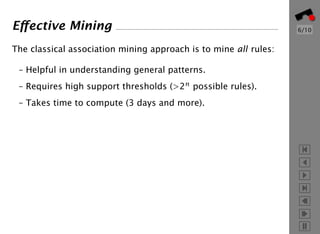
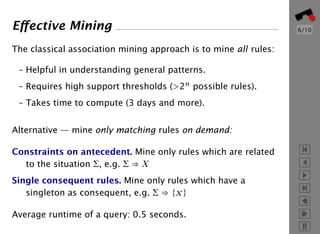
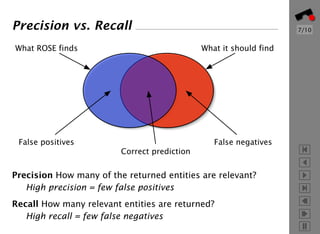
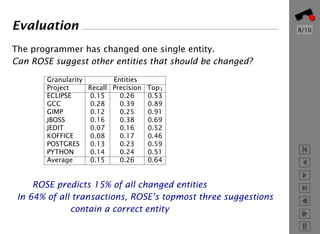
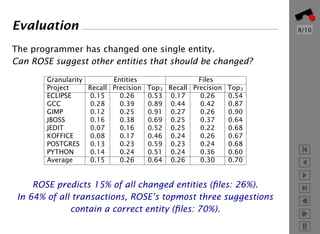
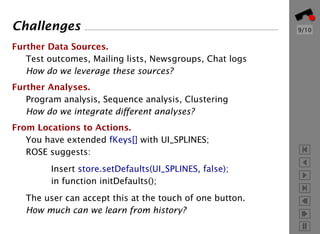
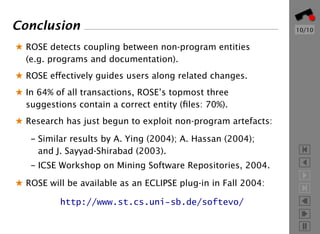
The document discusses a tool called ROSE that mines version histories to suggest related changes when a programmer modifies code. ROSE analyzes past transactions from version control systems to determine associations between code changes and uses these to recommend additional locations that may need to be updated. An evaluation shows that ROSE is able to predict the correct changed entities 15% of the time on average across various projects and its top 3 suggestions are correct 64% of the time.