Embed presentation




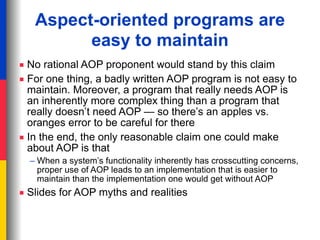
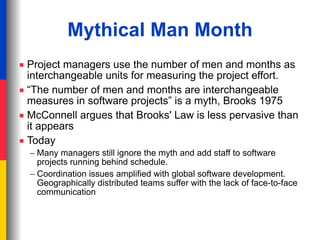
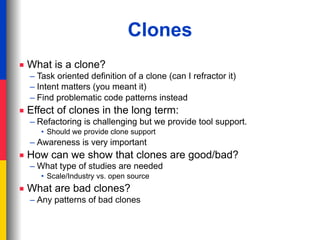
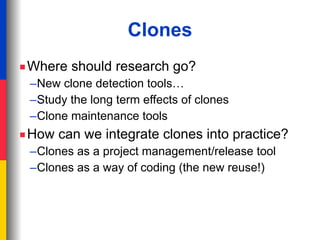
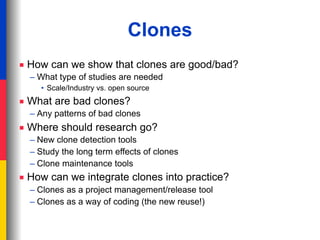
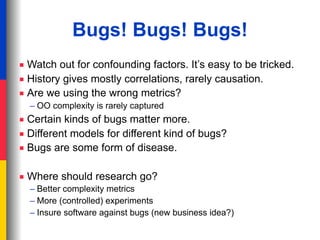

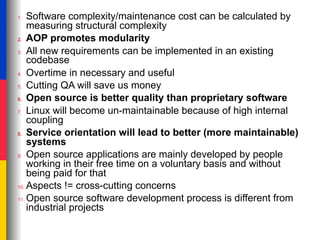




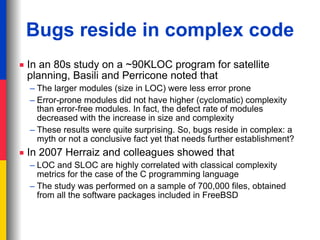
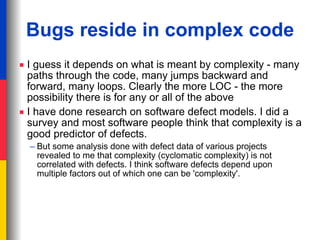
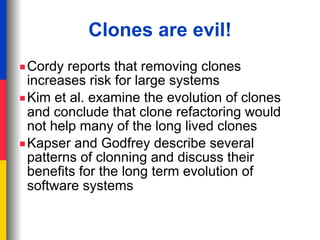
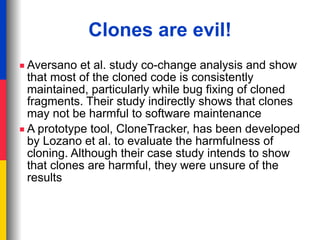
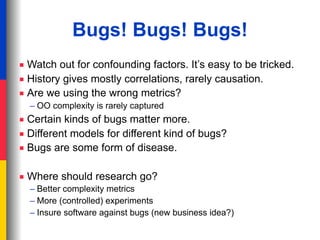
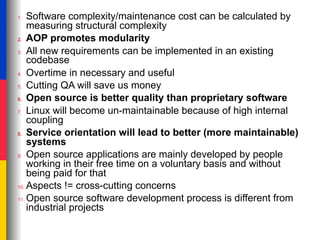
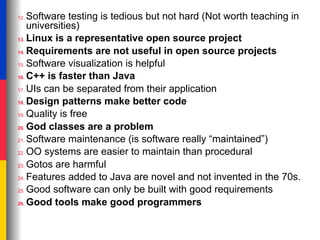
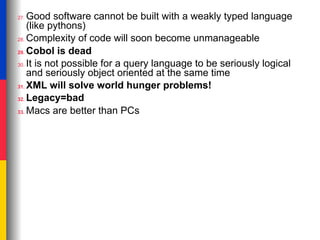
The document summarizes a working session on software engineering myths held on October 4, 2007 in Paris. The session included discussions of common myths in areas such as complexity, bugs, clones, aspect-oriented programming, and project management. Participants shared and debated myths in small group discussions. Some examples of myths discussed include the ideas that complexity leads to more bugs, clones are always bad, and aspect-oriented programs are inherently easier to maintain. The session aimed to evaluate whether such perceptions are truly myths or if aspects of them have been found to hold true in various studies.