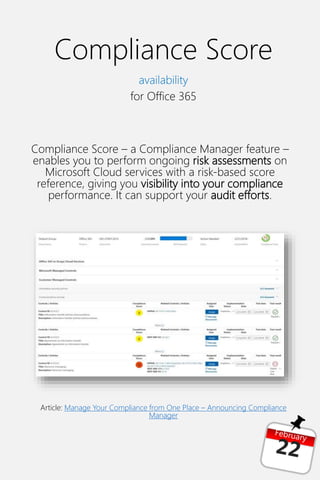
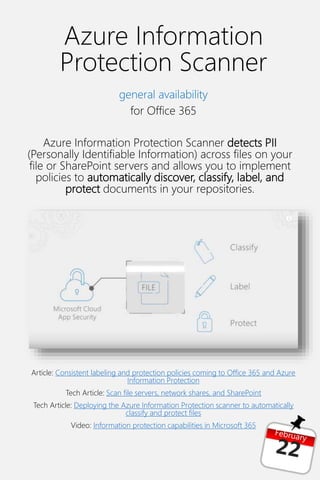
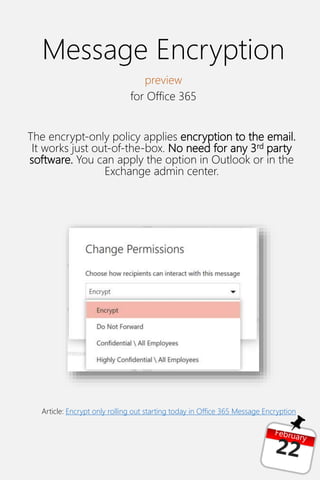
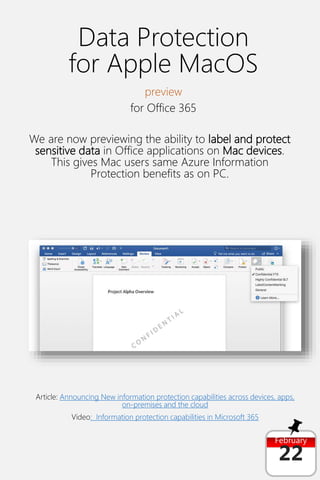
Microsoft 365 provides tools to help with GDPR compliance, including Compliance Manager, Compliance Score, and Azure Information Protection Scanner. Updates include the general availability of Compliance Manager, availability of Compliance Score for Office 365, and general availability of Azure Information Protection Scanner for Office 365. Message Encryption preview for Office 365 and data protection preview for Apple MacOS in Office 365 were also announced.