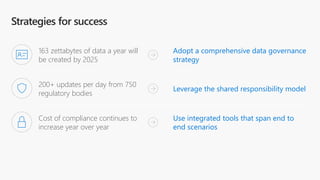
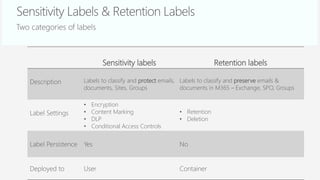
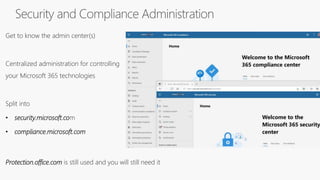
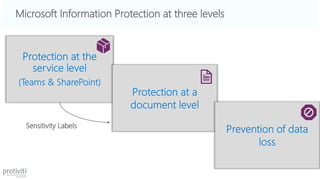
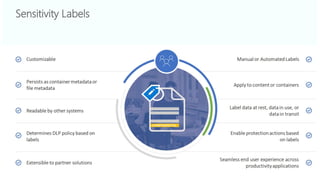
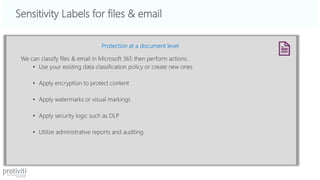
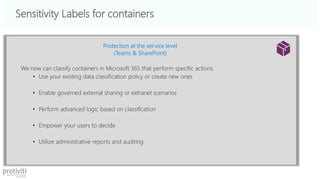
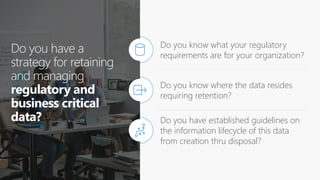
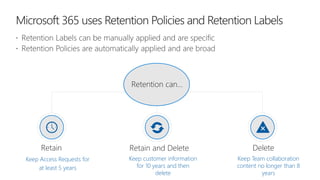
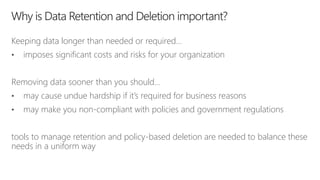
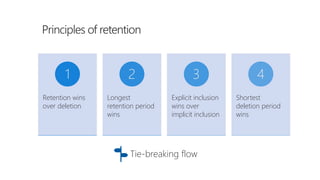
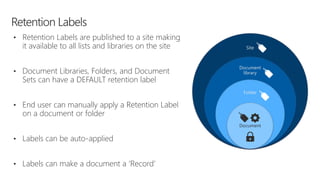
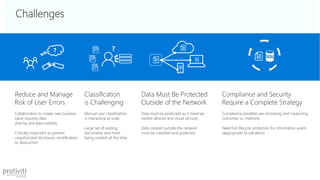
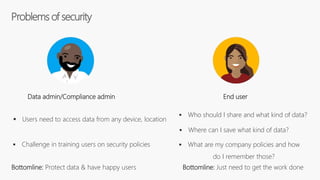
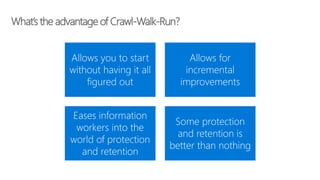
The document discusses data classification, retention, and sensitivity labeling within Microsoft 365, emphasizing the importance of a comprehensive data governance strategy amidst increasing compliance costs and regulatory updates. It highlights tools and policies for effectively managing data protection and retention while addressing challenges faced by users and organizations in a fragmented data landscape. Key features include sensitivity labels, retention strategies, and automated processes to classify and manage data throughout its lifecycle.