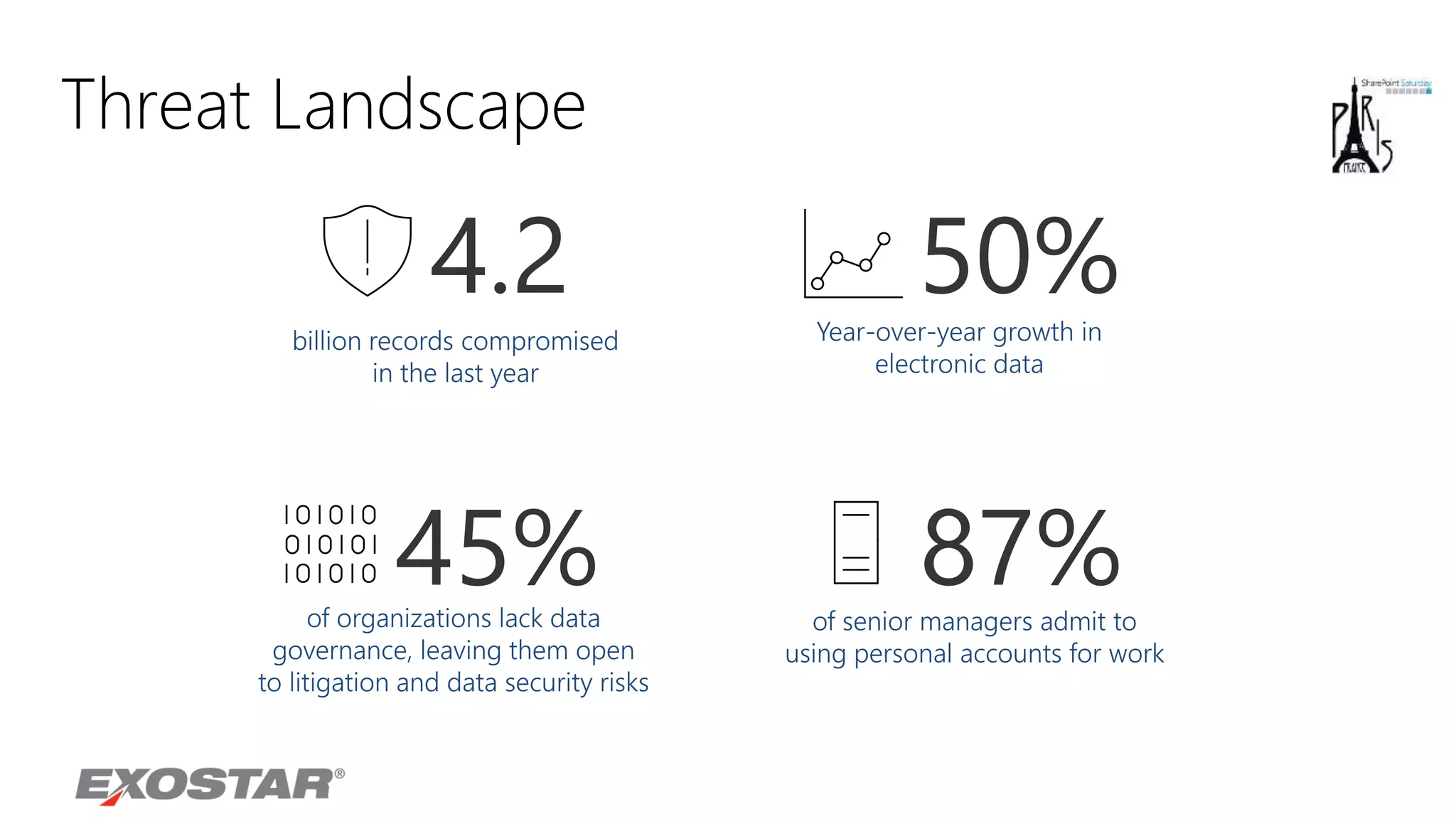
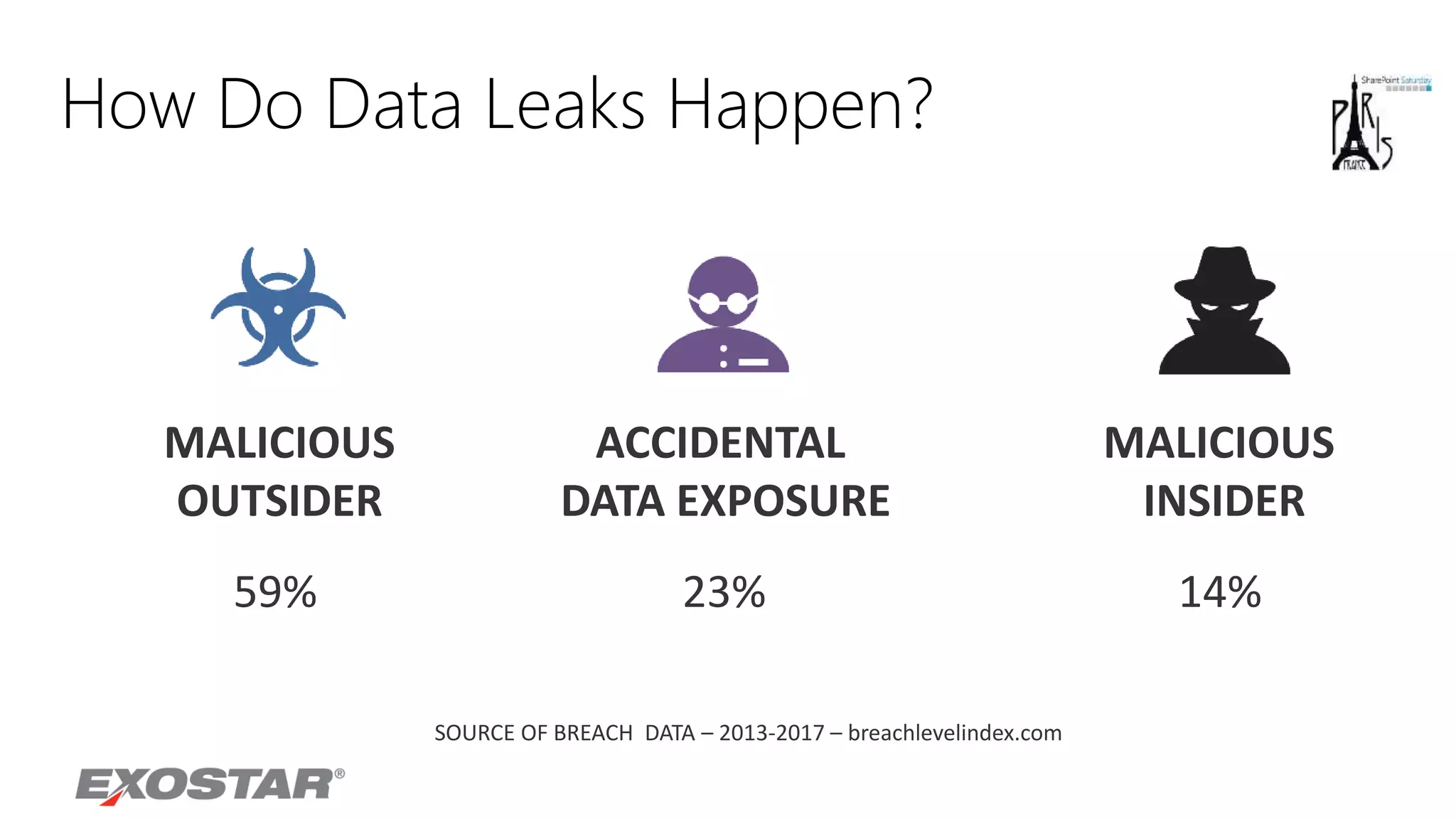
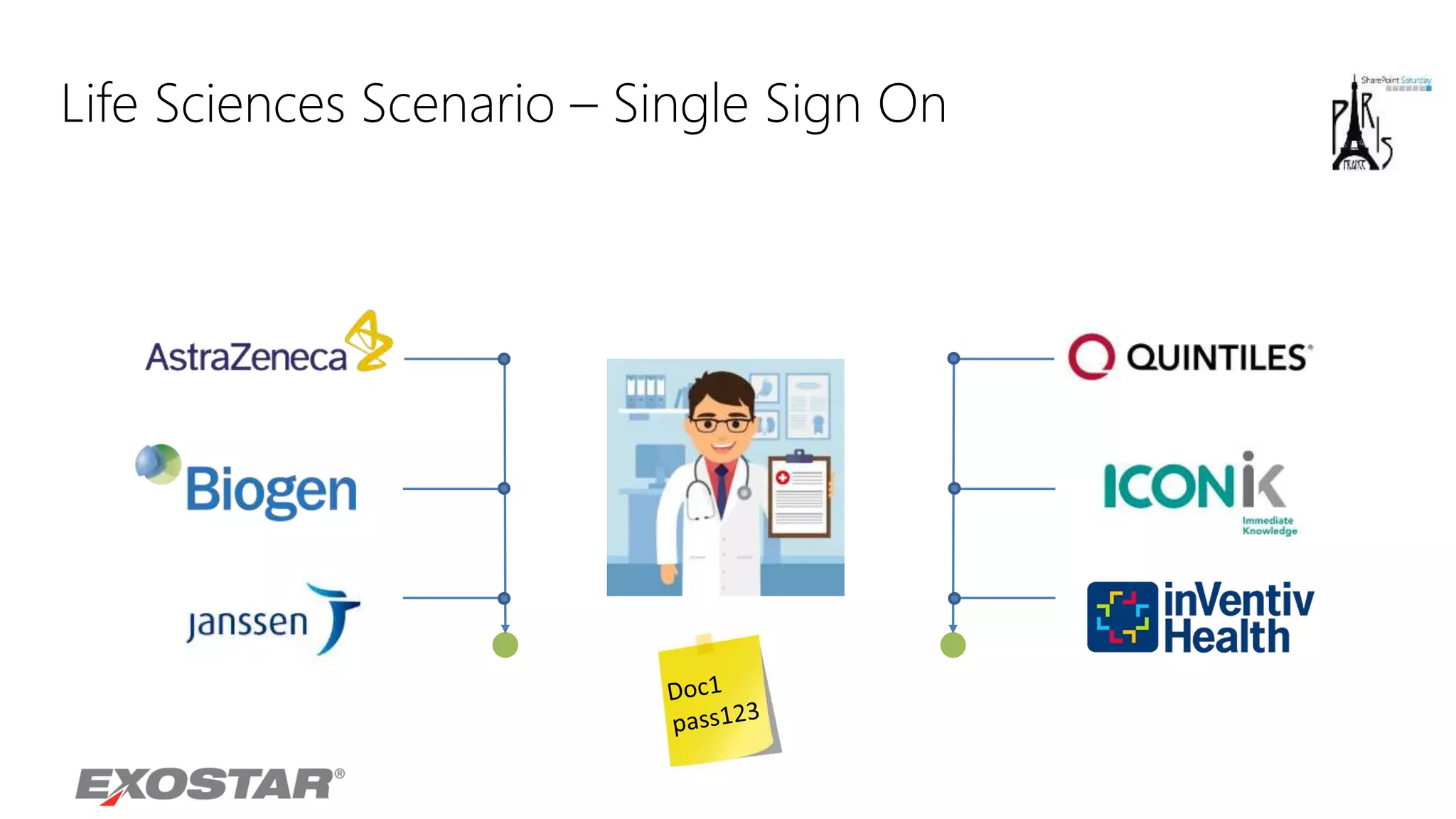
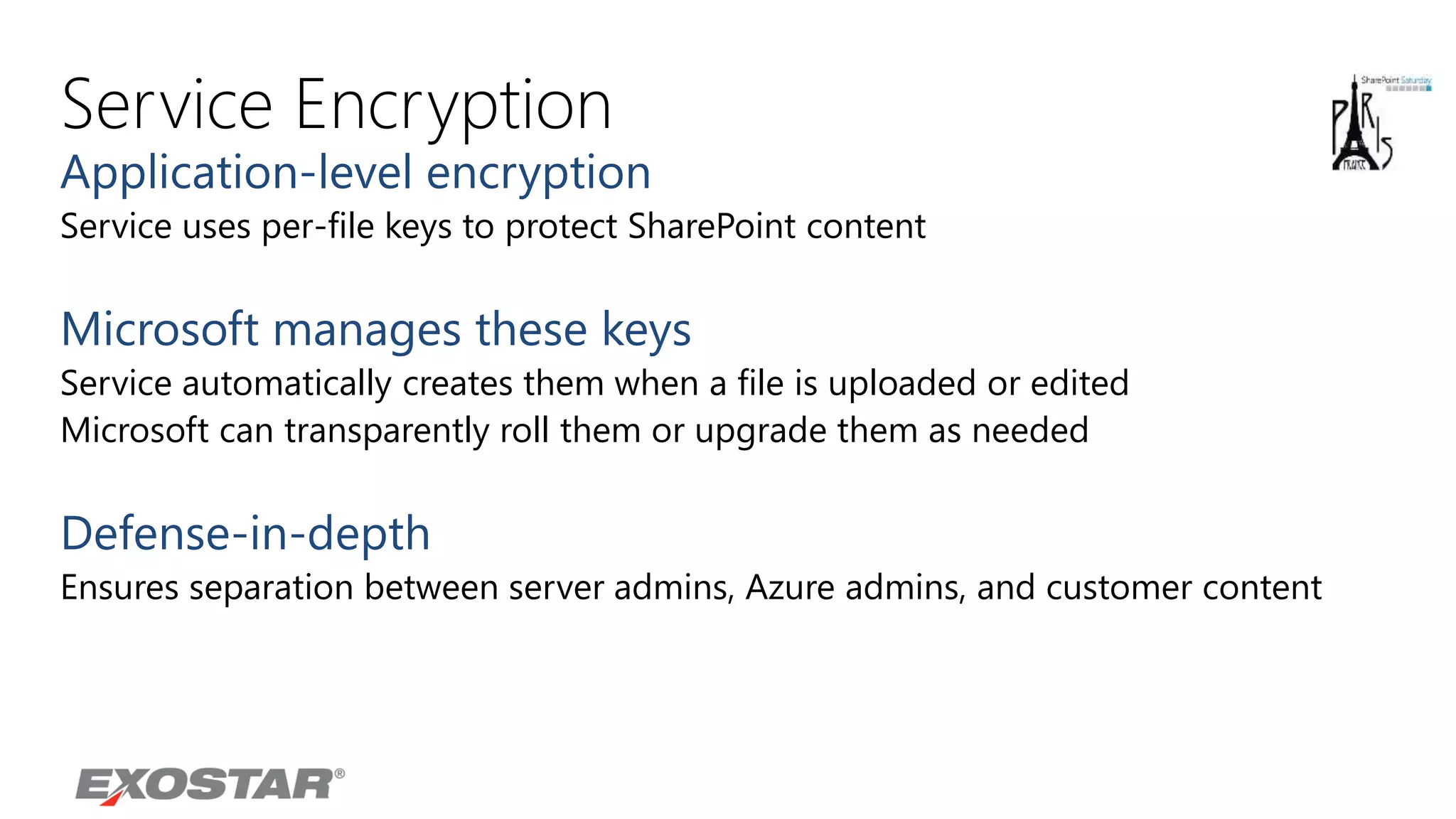
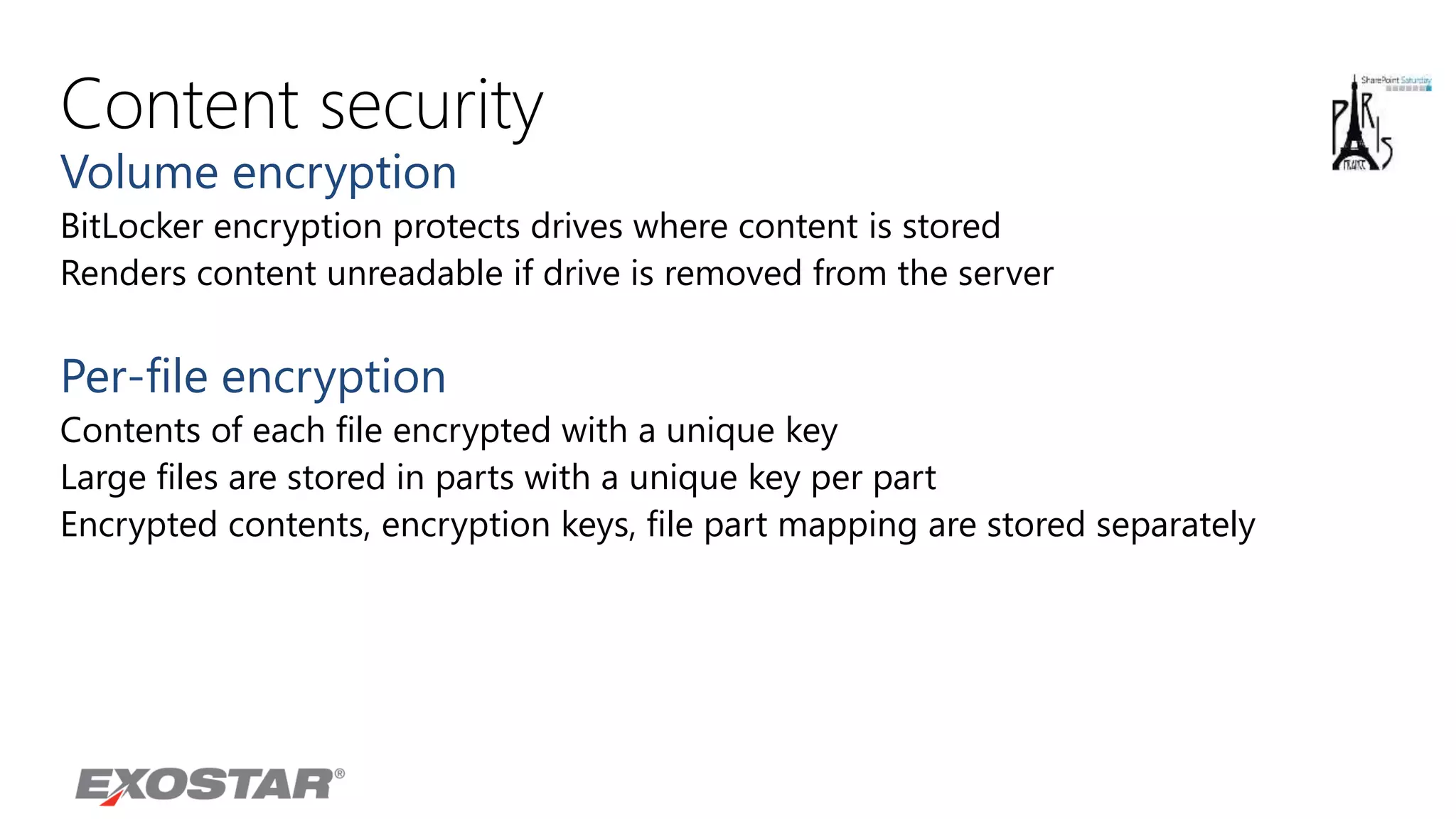
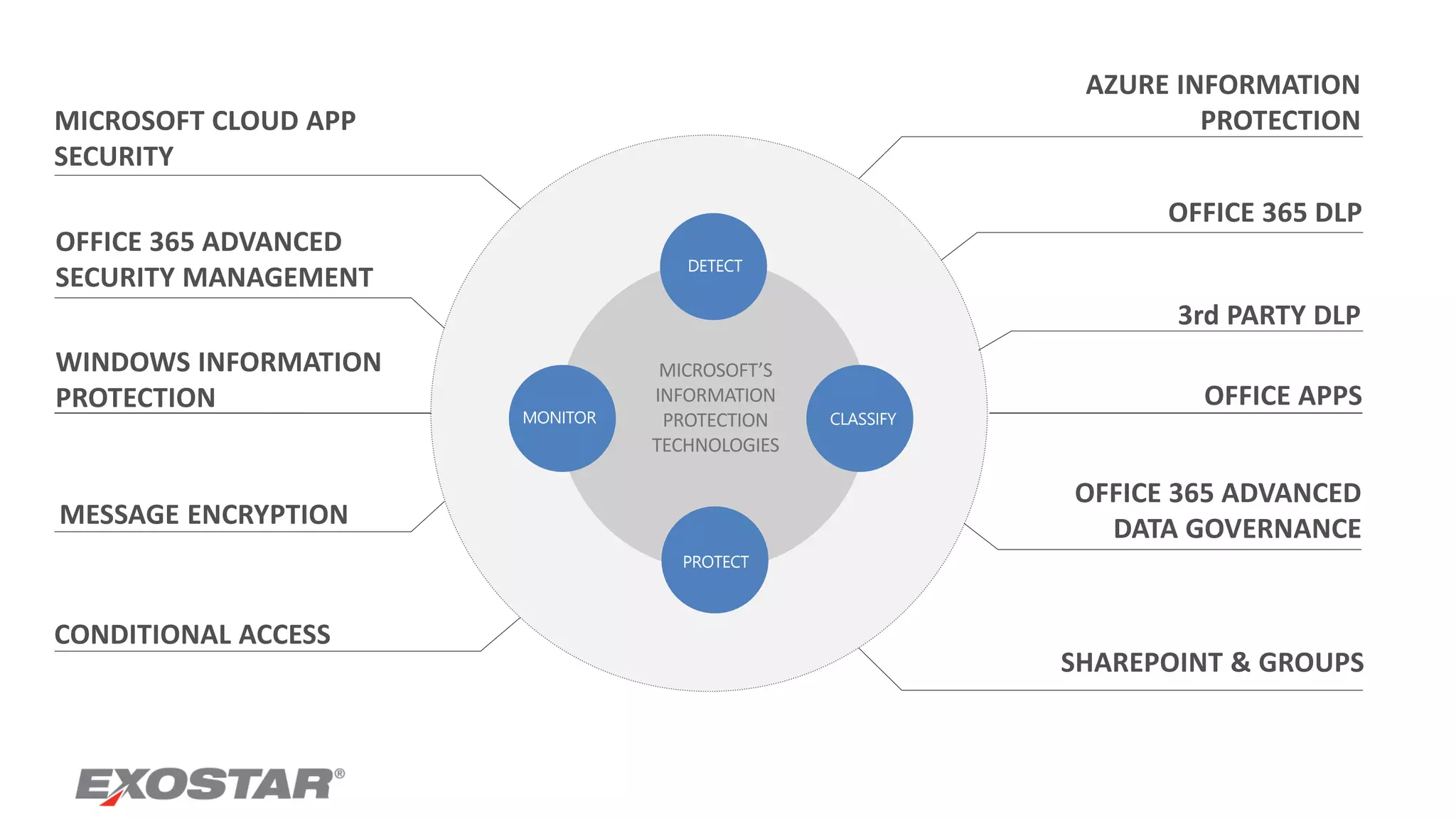
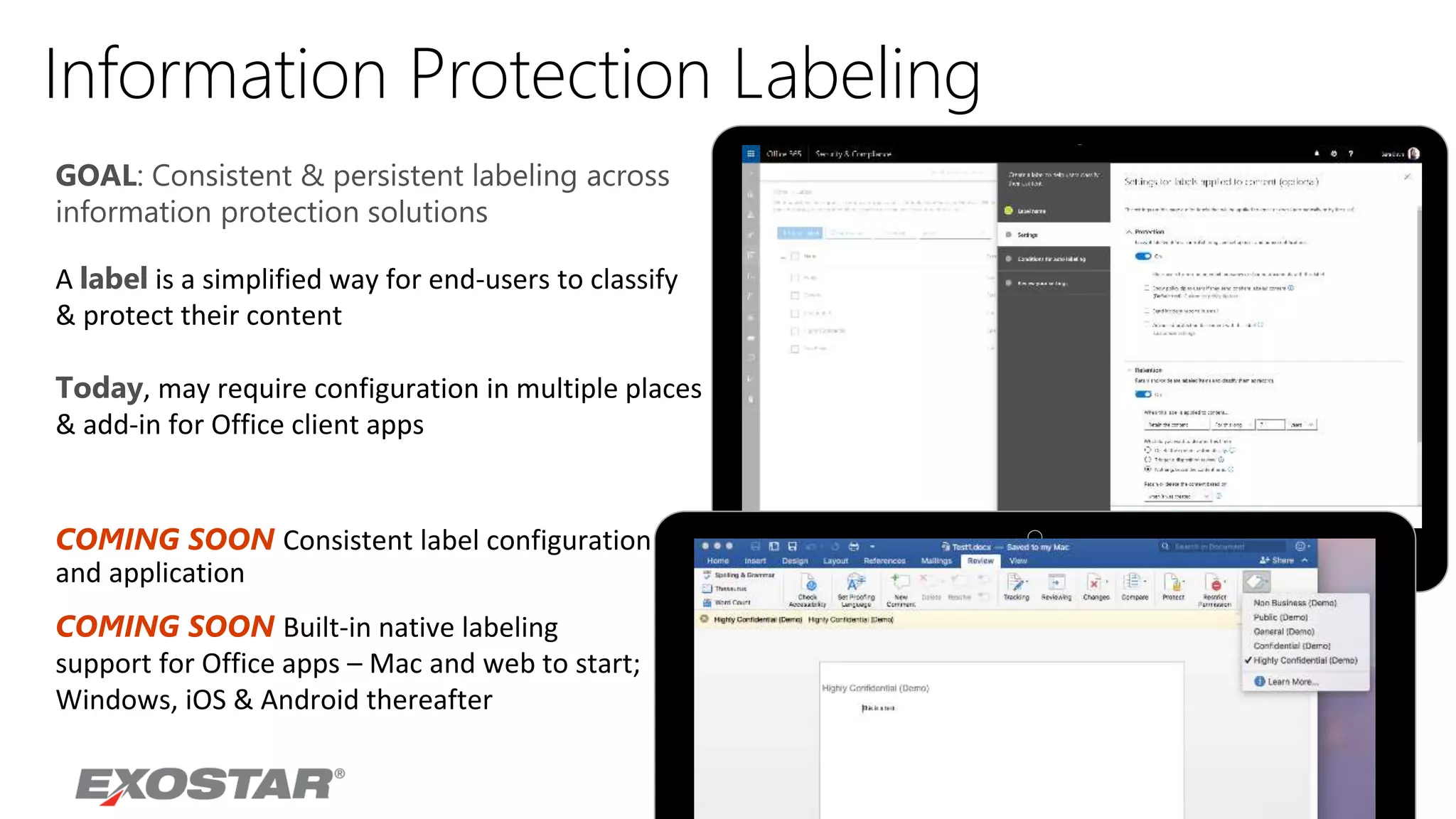
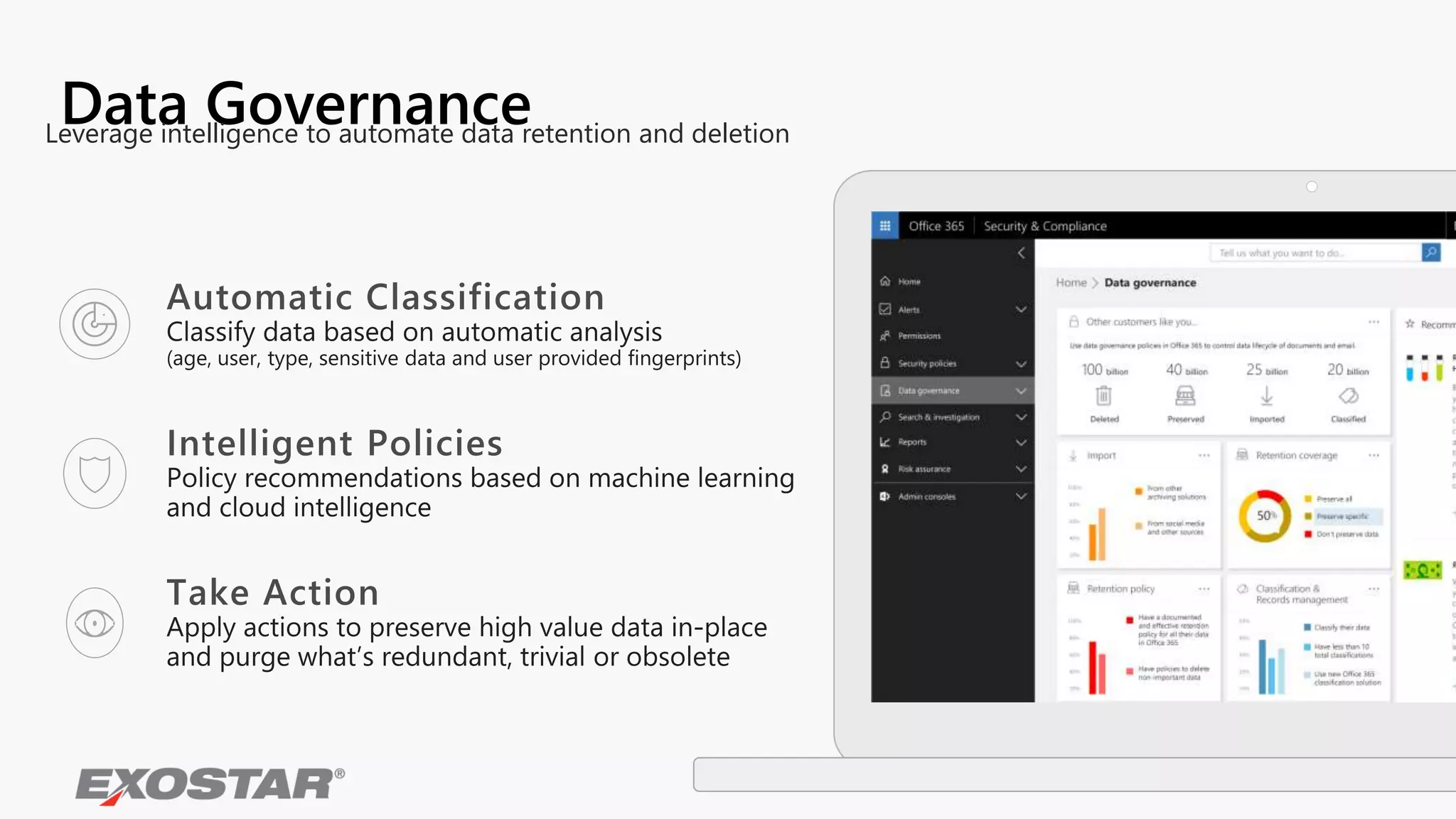
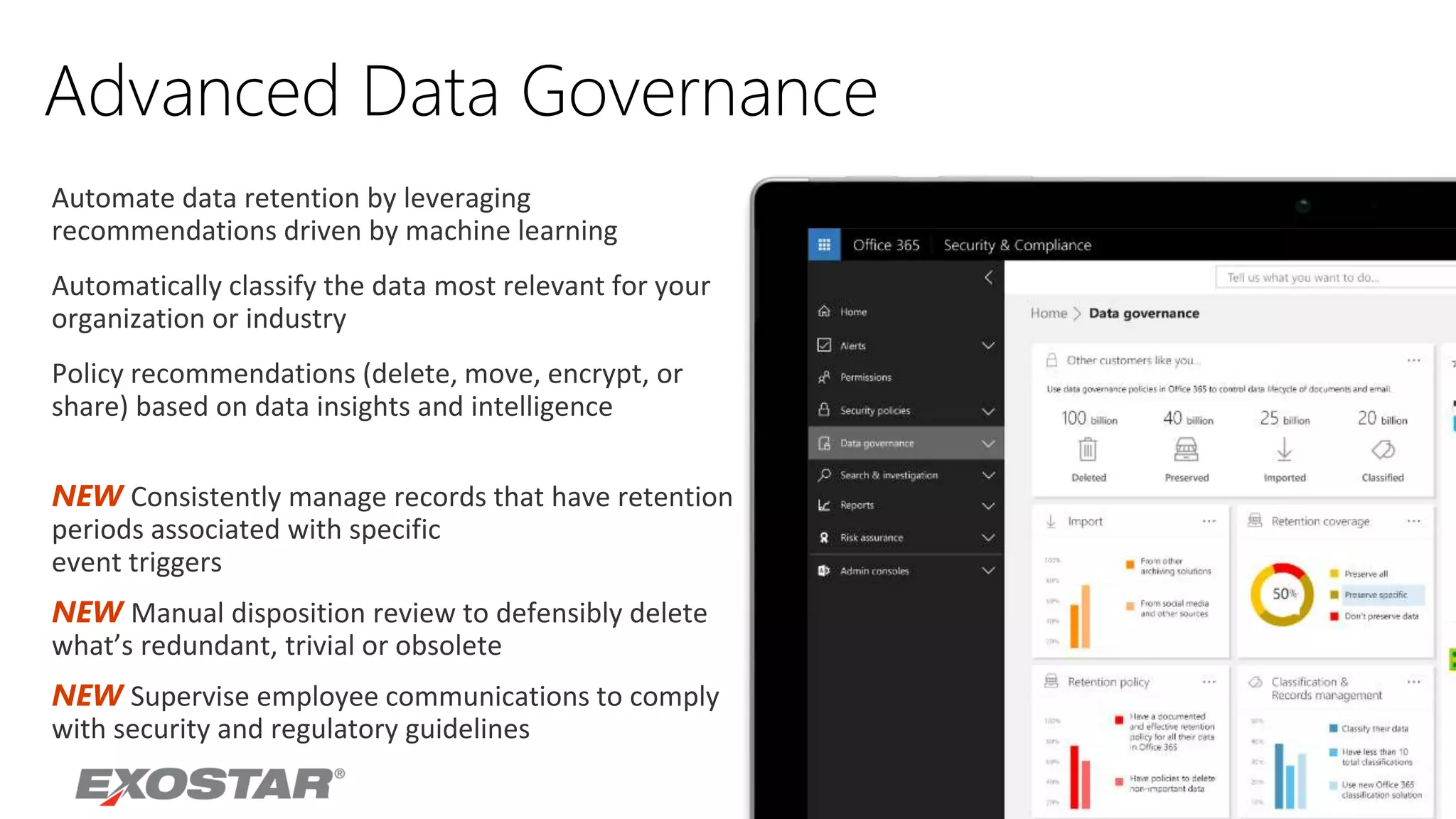
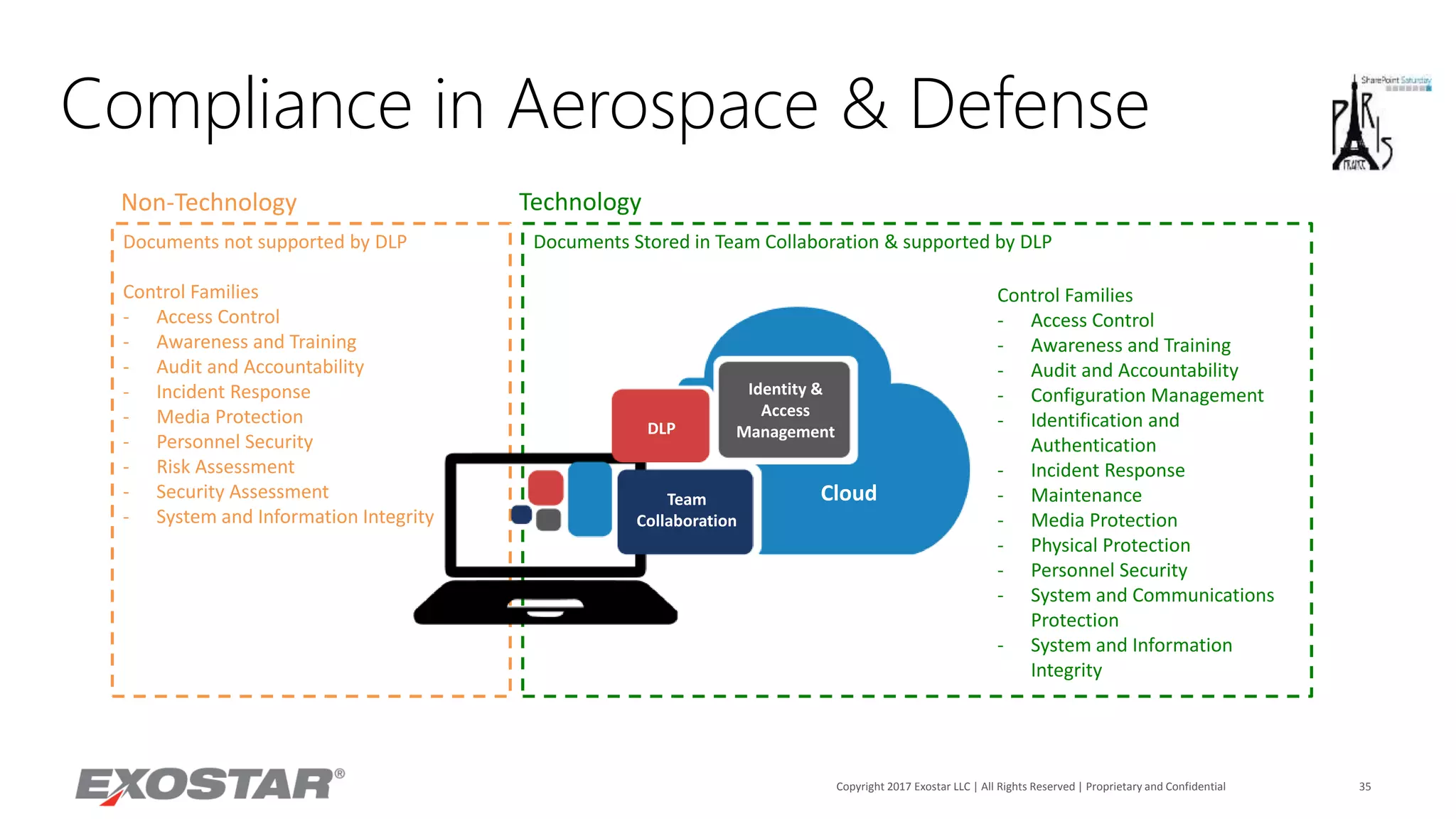
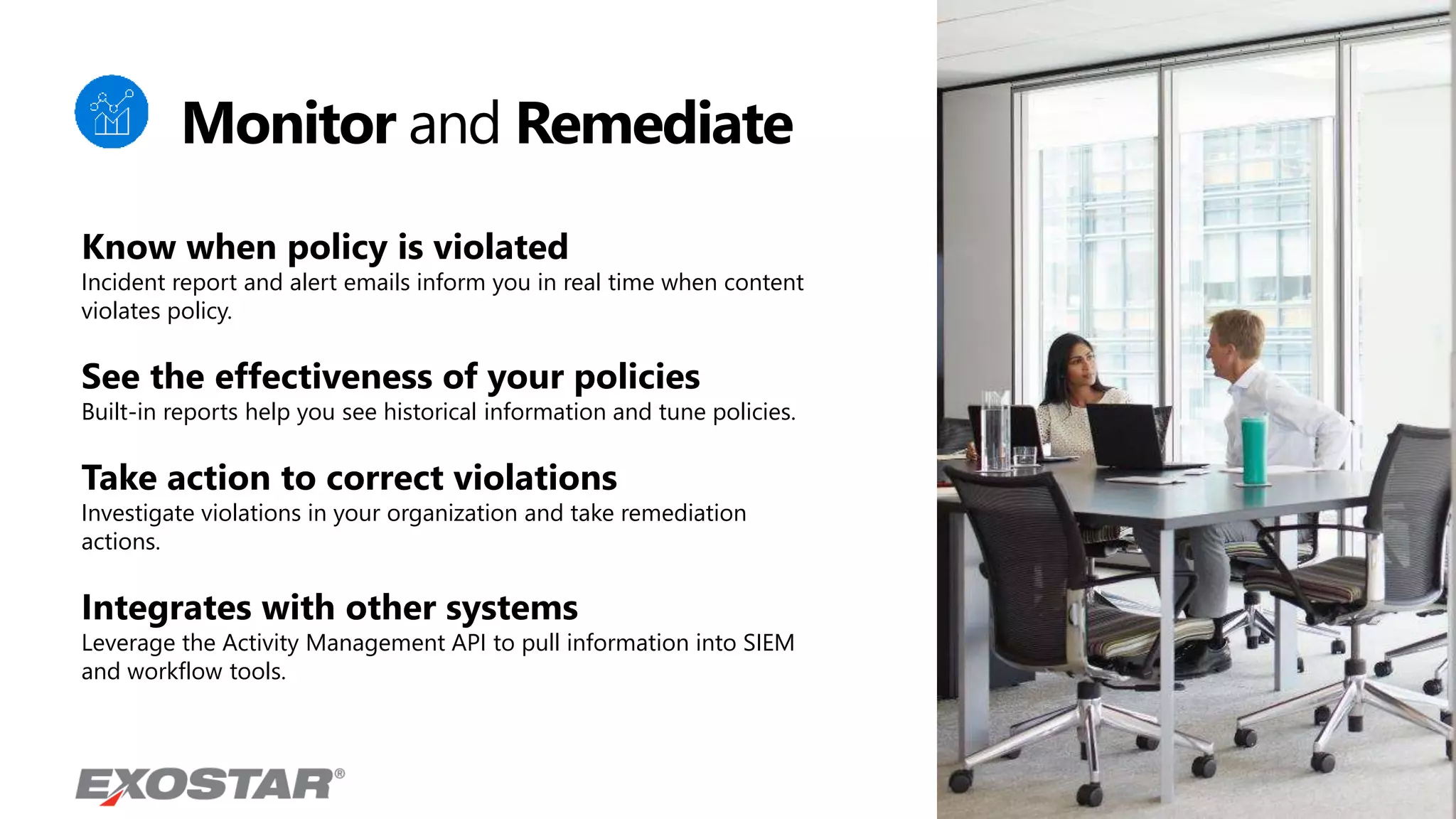
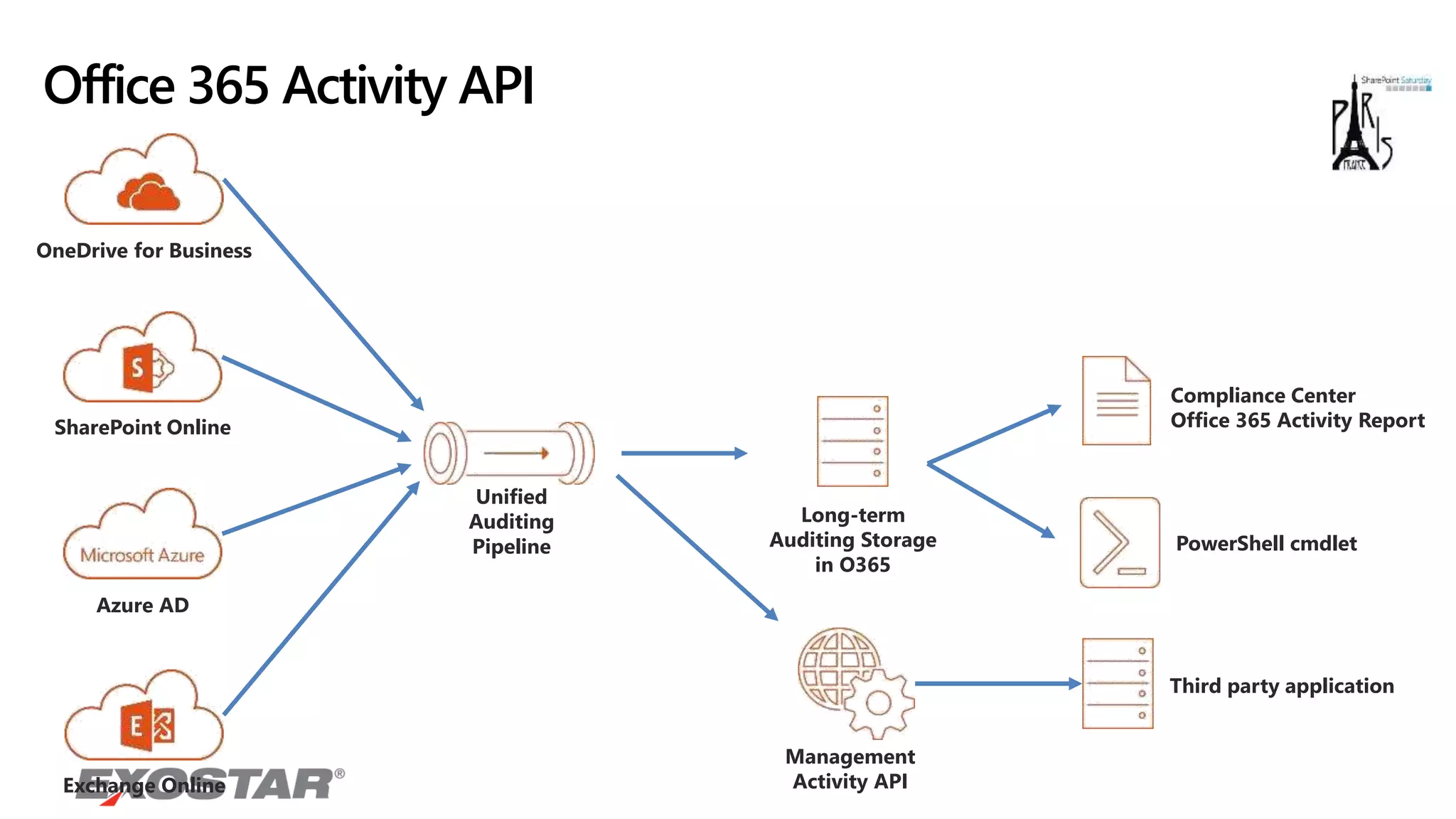
The document discusses the evolving landscape of content security, highlighting the frequency and financial impact of cyber incidents. It provides strategies for organizations to protect their content and manage data access, emphasizing the need for user awareness, classification, and multi-layered defenses. Additionally, it outlines Microsoft’s security features, compliance measures, and tools for monitoring and protecting organizational data.