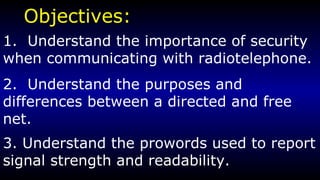
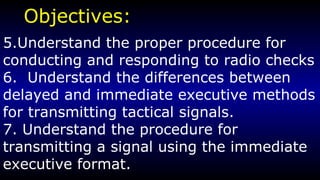
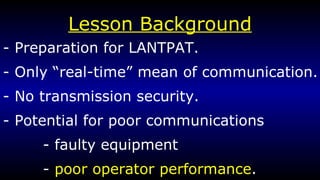
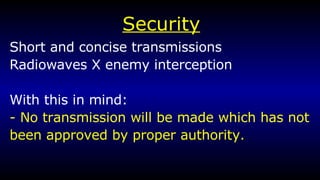
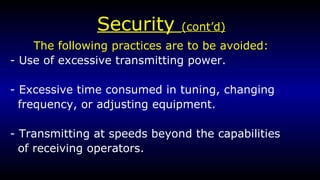
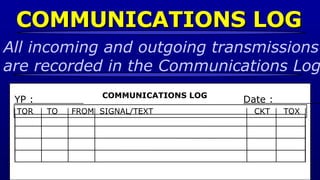
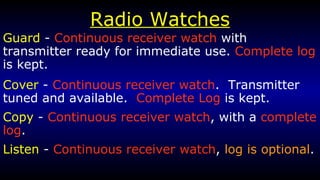
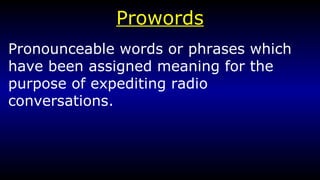
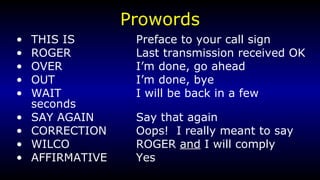
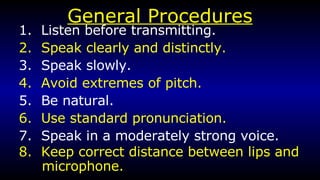
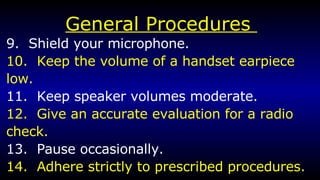
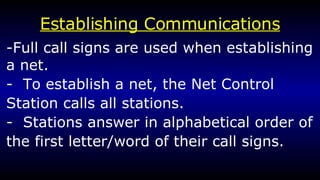
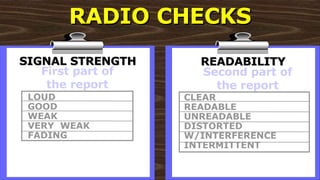
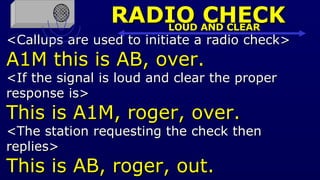
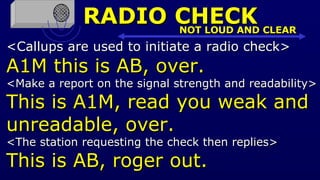
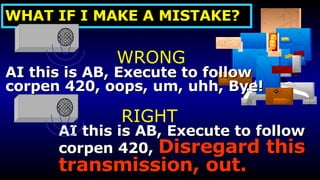
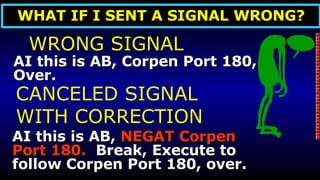
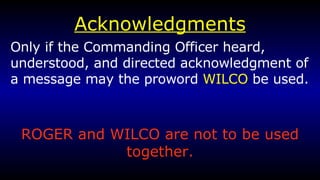
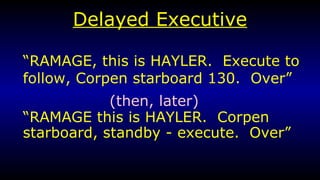
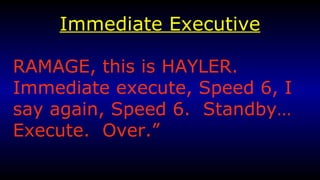
The document provides an overview of radiotelephone procedures and protocols for naval communications. It discusses the importance of security, types of nets, procedures for radio checks, phonetic alphabet, prowords, call signs, establishing communications, and transmitting tactical signals using delayed and immediate executive formats.