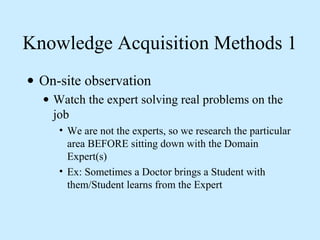
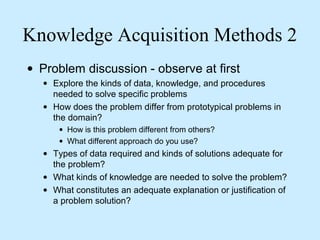
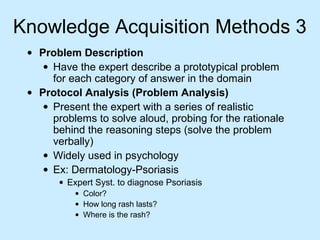
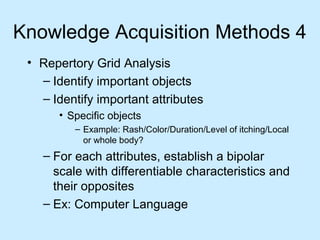
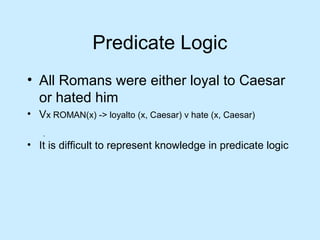
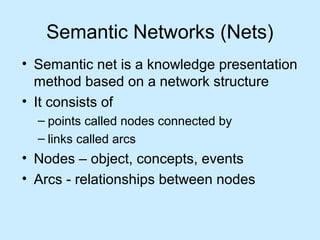
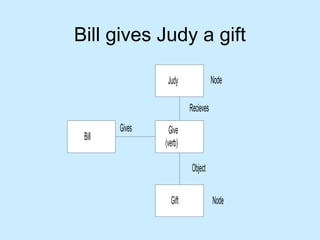
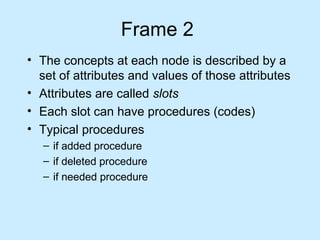
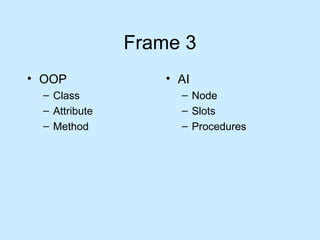
This document discusses different types of knowledge and methods for knowledge acquisition. It describes declarative and procedural knowledge, as well as the knowledge acquisition paradox where experts have difficulty verbalizing their knowledge. Various knowledge acquisition methods are outlined, including observation, problem discussion, and protocol analysis. Knowledge representation techniques like rules, semantic networks, frames, and predicate logic are also introduced.