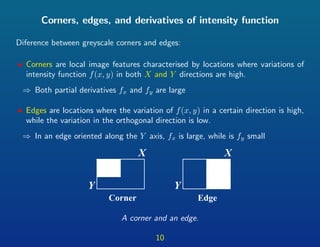
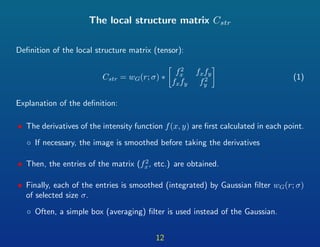
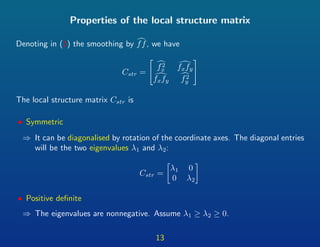
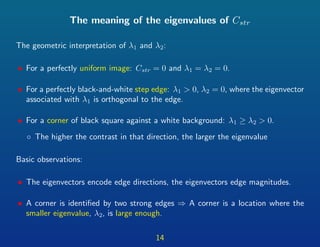
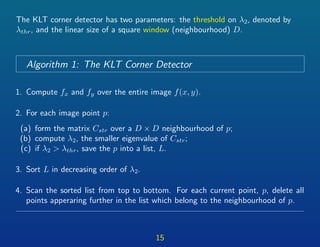
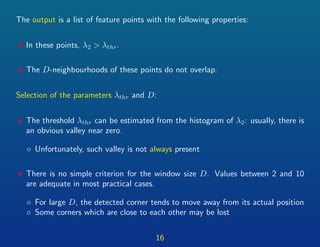
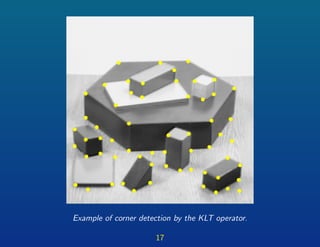
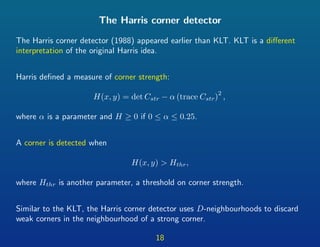
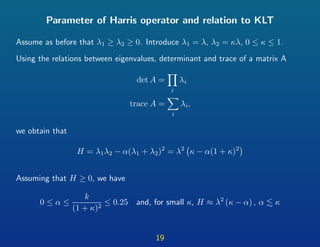
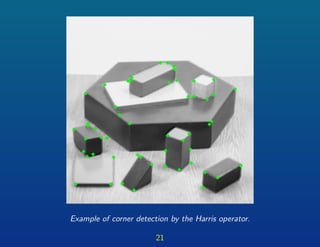
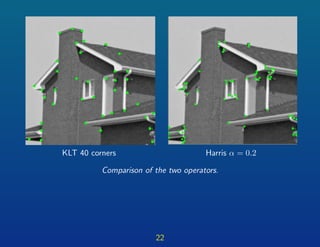
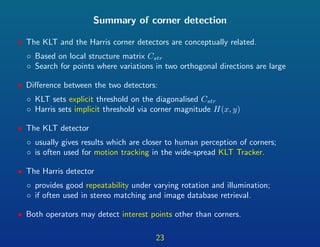
This document provides a summary of corner detection techniques in digital images. It discusses the local structure matrix, which is used in two popular corner detectors: the Kanade-Lucas-Tomasi (KLT) corner detector and the Harris corner detector. Both detectors identify corners as locations where variations of image intensity are high in two orthogonal directions, as measured by the eigenvalues of the local structure matrix. The KLT detector uses an explicit threshold on the smaller eigenvalue, while the Harris detector uses an implicit threshold through a corner response measure. Examples are given to compare the outputs of the two detectors.