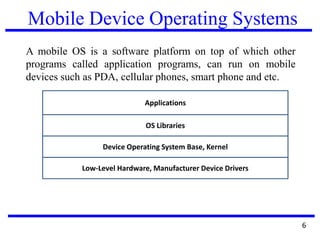
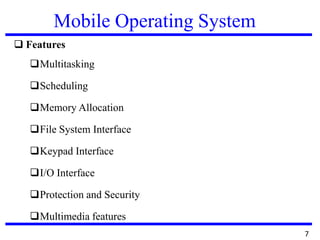
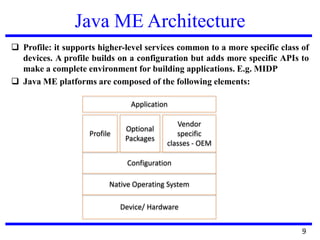
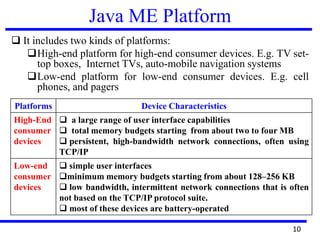
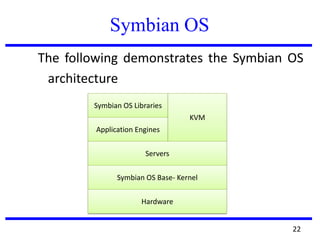
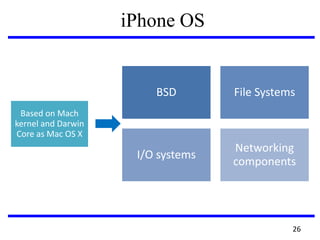
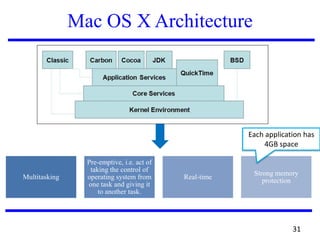
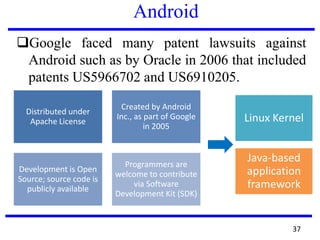
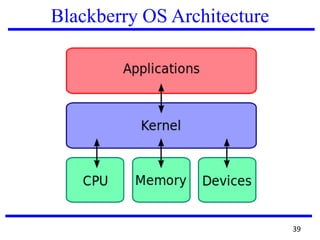
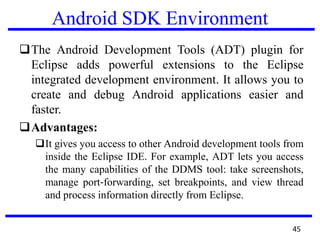
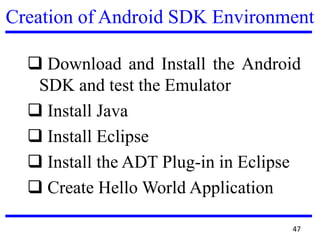
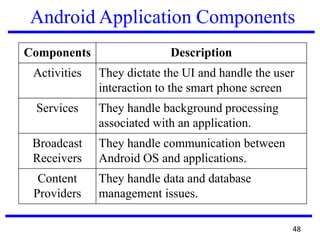
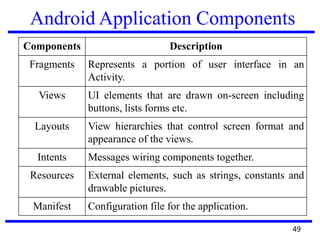
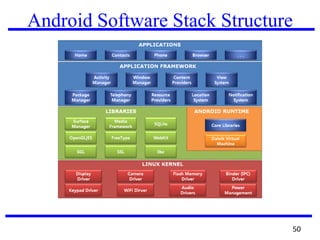
The document provides an overview of mobile device operating systems, including their structures, features, and commercial applications like m-commerce. It discusses various platforms such as iOS, Android, Windows Mobile, Palm OS, and Symbian OS, detailing their characteristics, advantages, and limitations. Additionally, it covers the Android software development kit and components for developing Android applications.