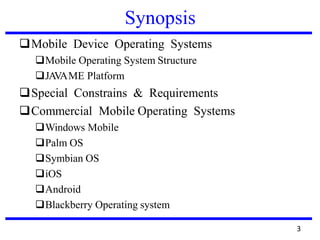
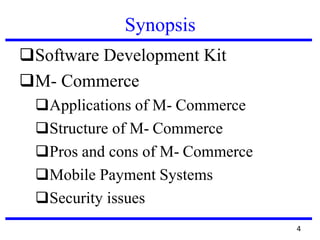
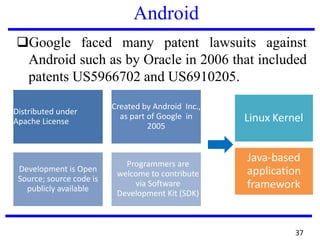
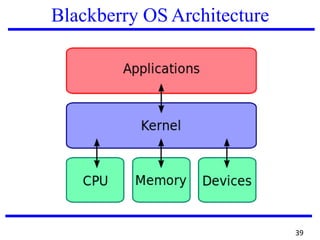
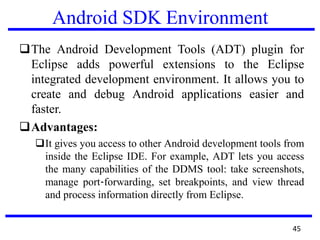
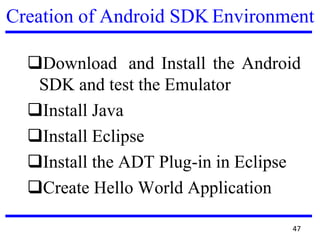
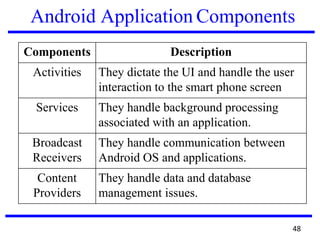
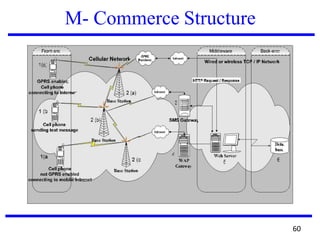
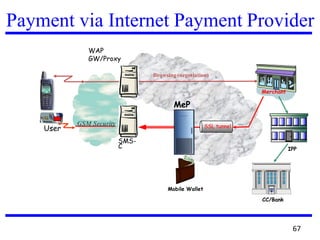
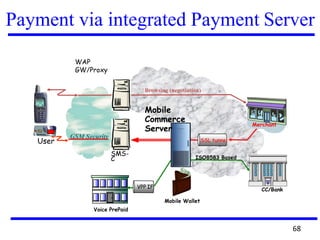
The document provides an overview of mobile platforms and applications. It discusses mobile device operating systems, their requirements and constraints. It describes several commercial mobile operating systems including iOS, Android, BlackBerry and Windows Phone. It also covers mobile commerce structures and applications, mobile payment systems, and related security issues. Software development kits for platforms like iOS and Android are explained.