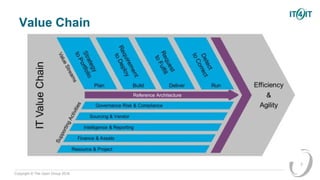
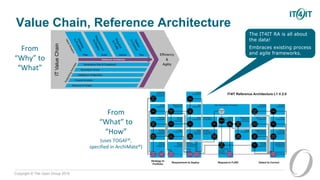
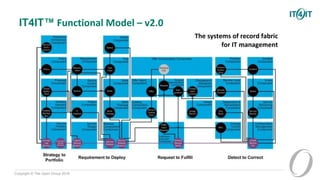
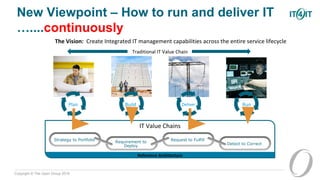
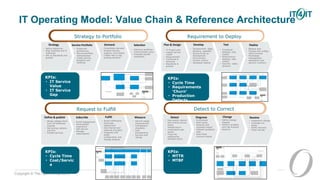
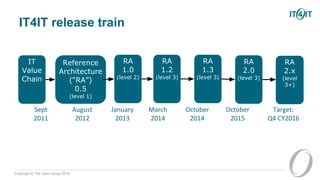
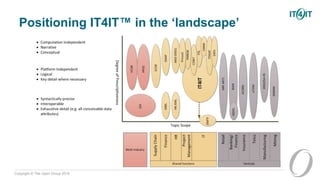
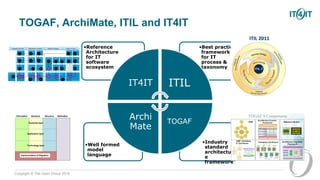
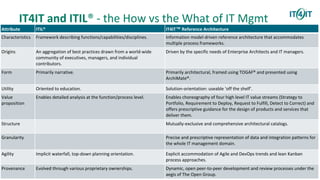
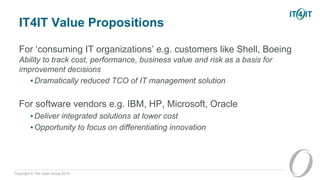
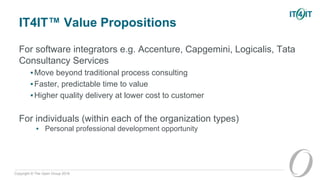
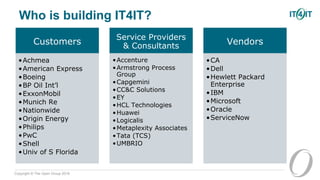
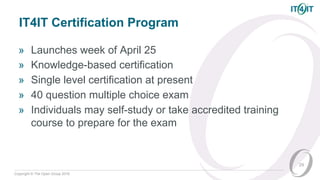
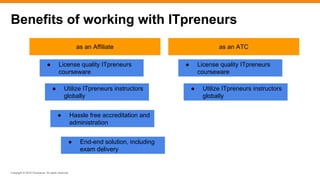
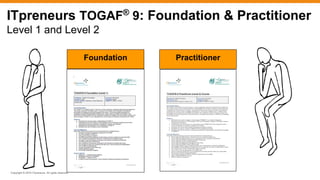
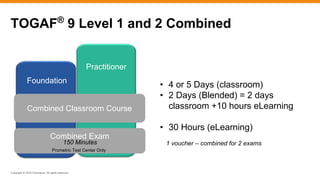
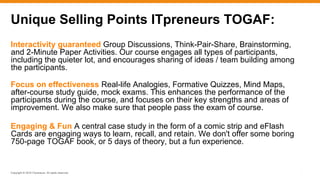
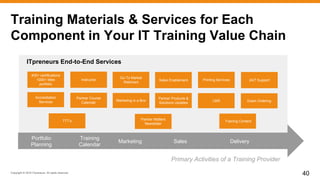
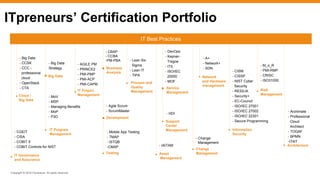
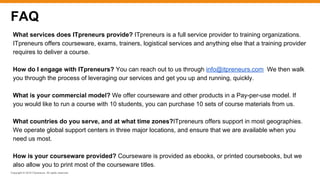
The document outlines the IT4IT standard developed by The Open Group, which serves as a framework for managing IT processes with a focus on improving efficiency and reducing risks. It emphasizes the evolution and integration of IT management tools across various methodologies such as ITIL and TOGAF, highlighting the benefits for both organizations and individuals in the IT sector. Additionally, it details the training opportunities and resources available through ITpreneurs, including certification programs and a comprehensive suite of services for IT training providers.