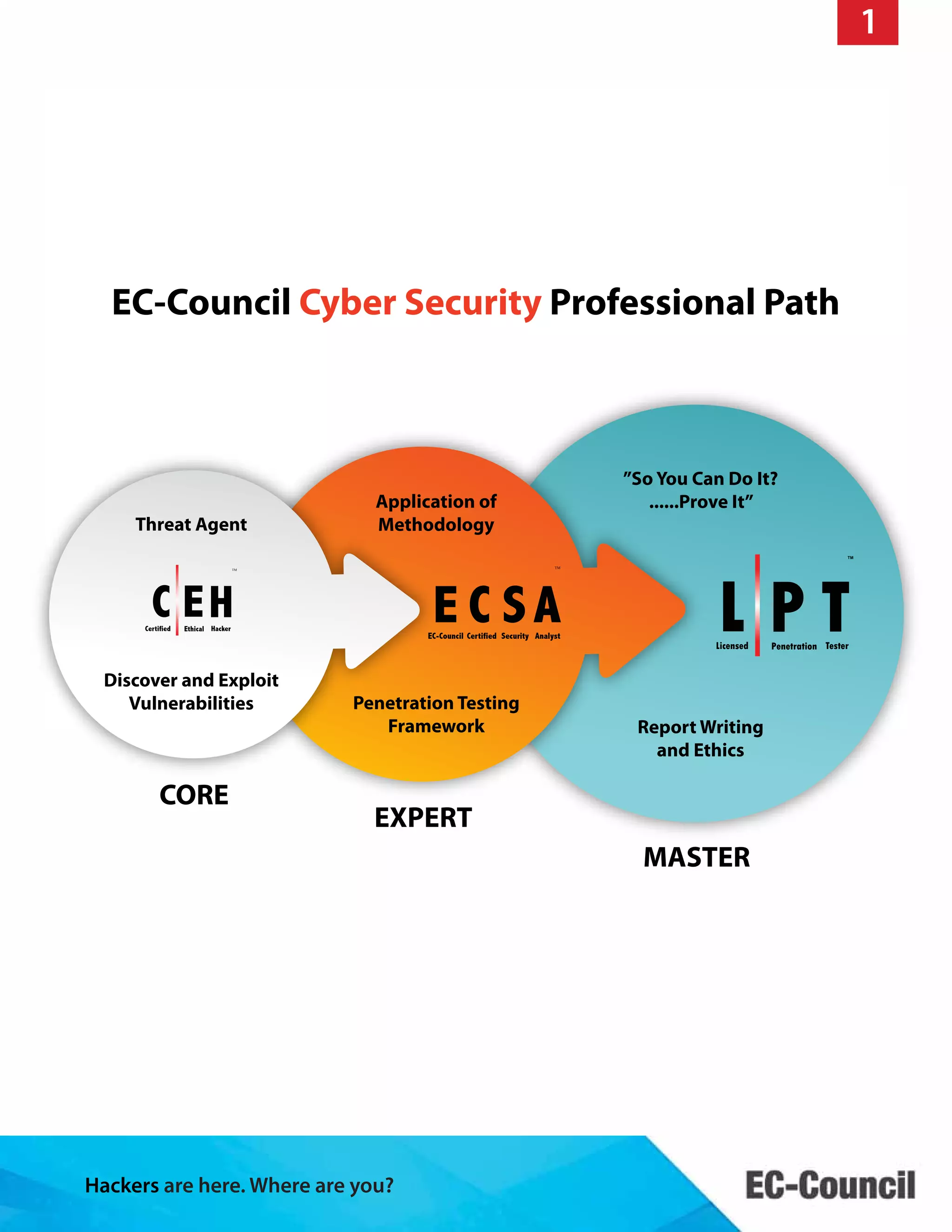
The document discusses the EC-Council Security Analyst (ECSA) program, which provides hands-on training for penetration testing and equips students with practical skills to become competent security professionals. The course focuses on various penetration testing methodologies and includes a practical assessment through a cyber range, where candidates must perform real-world tests and submit detailed reports. The document outlines the curriculum, eligibility requirements, and the certification process required to achieve the ECSA credential.