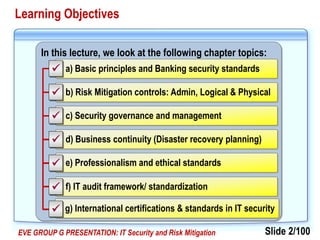
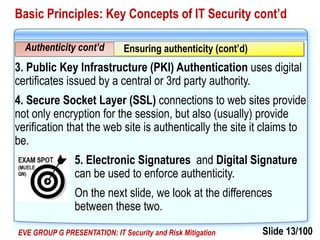
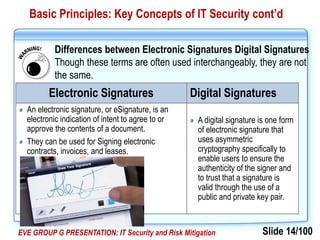
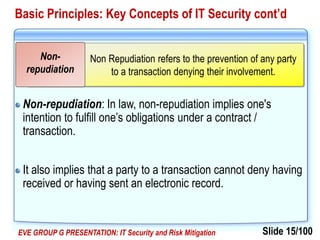
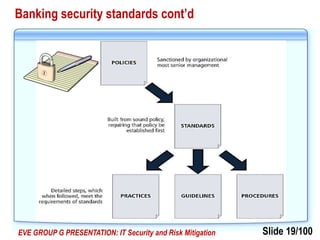
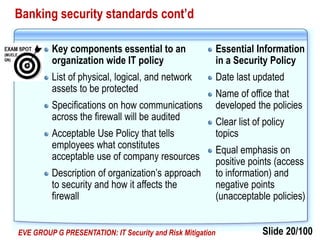
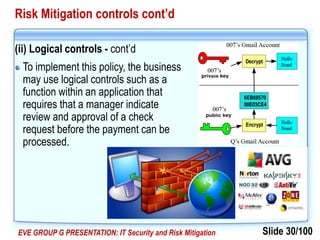
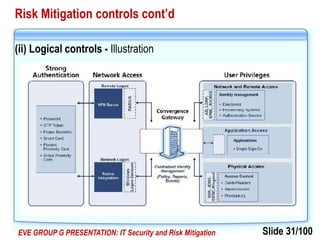
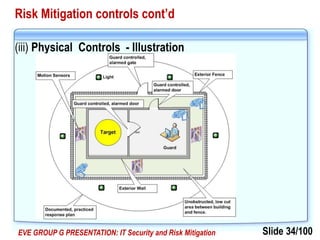
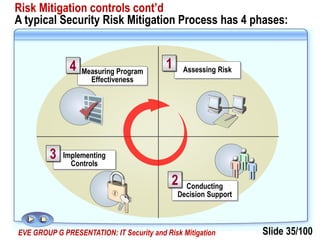
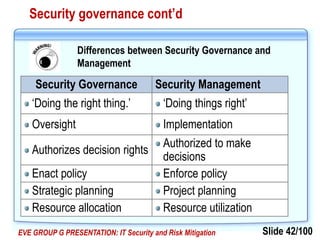
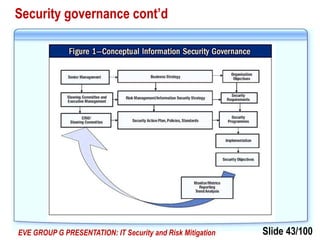
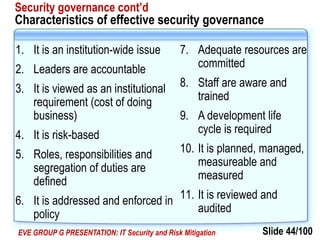
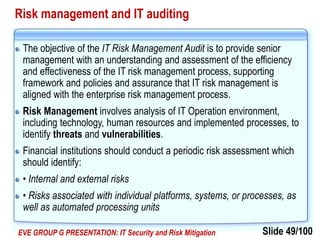
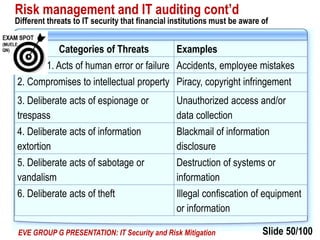
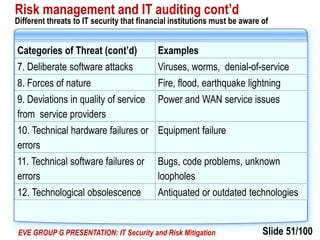
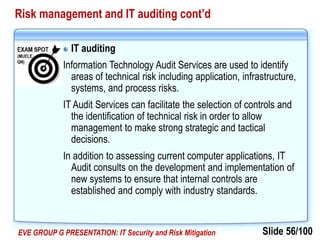
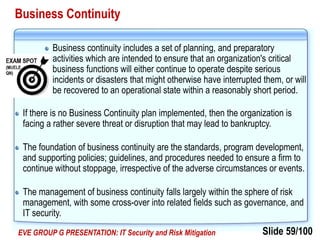
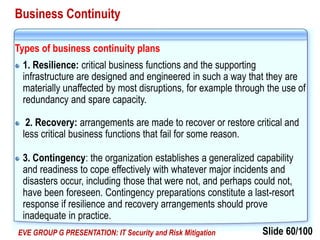
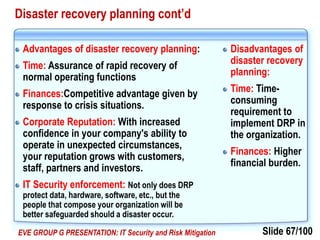
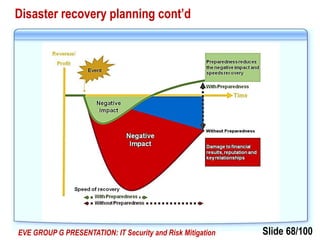
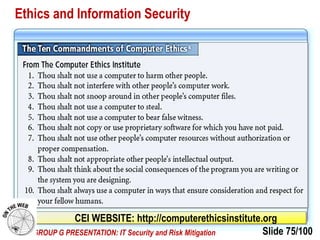
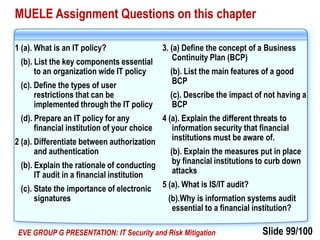
The document discusses various topics related to IT security and risk mitigation. It begins with an overview of basic IT security principles such as confidentiality, integrity, availability, authenticity, non-repudiation and accountability. It also discusses banking security standards and the importance of having policies, procedures, and standards to ensure security. Finally, it covers the different types of risk mitigation controls including administrative, logical, and physical controls that can be implemented to minimize security risks.