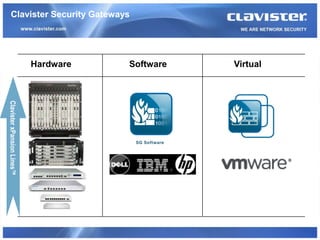
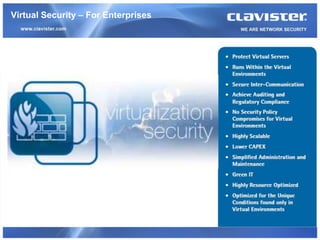
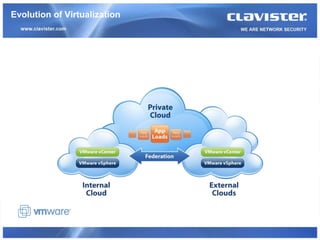
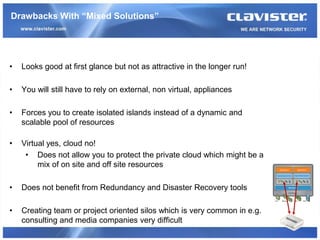
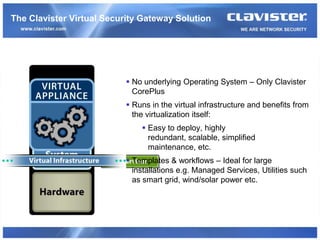
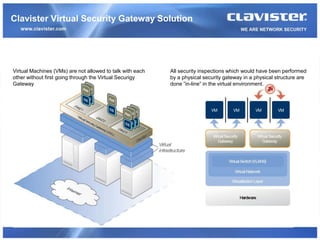
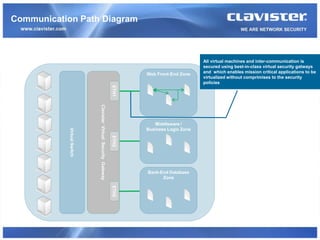
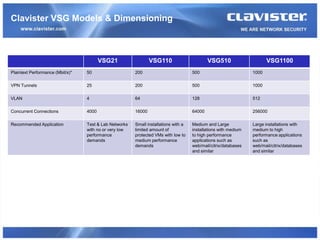
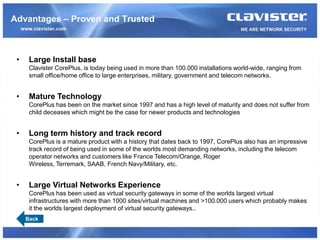
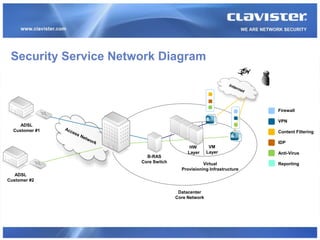
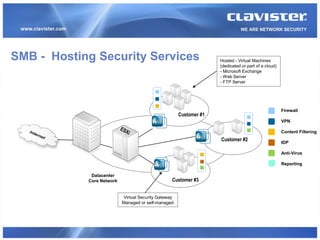
Clavister provides network security solutions including virtual security gateways. Their solutions protect against hackers, intrusions, information theft, and other threats. Clavister has over 20 years of experience securing networks and has protected over 100,000 networks. Their complete product portfolio is designed for performance and scalability. Clavister's virtual security gateways provide network security within private cloud infrastructures and enable auditing and compliance for virtual environments without compromising security policies.
![Clavister – Virtual Security
May 2010
[Nicola Sotira, VP Sales Italia]](https://image.slidesharecdn.com/clapresclavistervirtualsecurity03-100517071758-phpapp01/75/Clavister-security-for-virtualized-environment-1-2048.jpg)