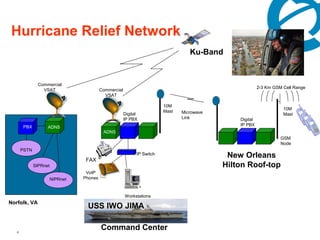
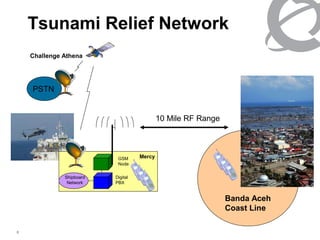
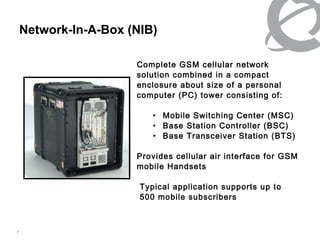
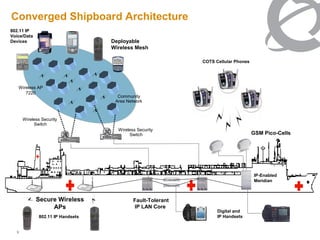
The document discusses network solutions provided by Nortel for the US Navy. It describes a converged shipboard network architecture that supports up to 300 shore users and 80 ship users scalable to 160. The network enhances ship-to-shore collaboration with solutions like secure wireless access points, IP handsets, and mobile devices. It enables seamless communications between the Navy's second fleet headquarters and deployed flagships through commercial satellite links, digital IP PBX systems, and network management software.