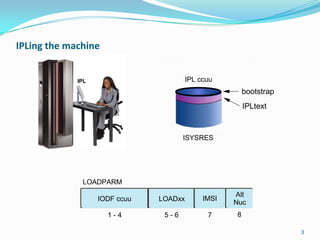
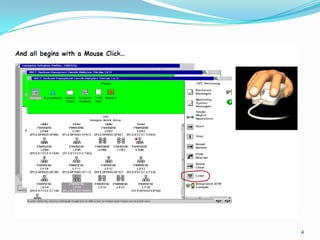
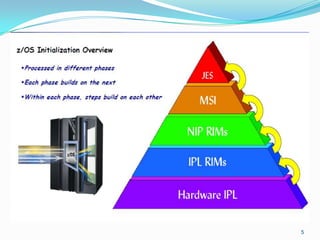
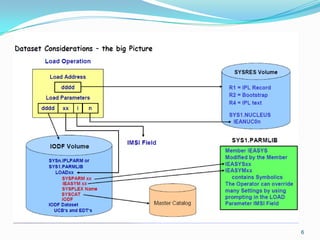
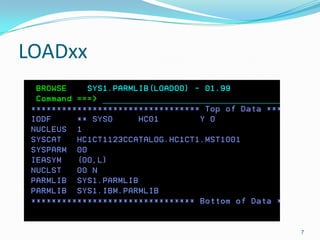
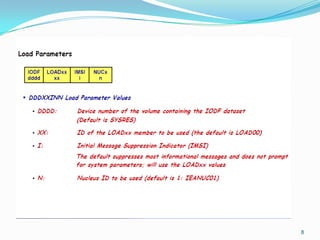
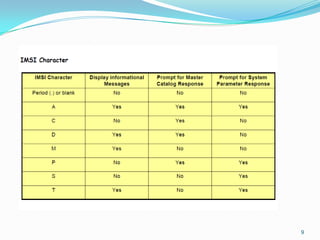
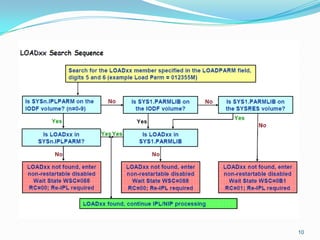
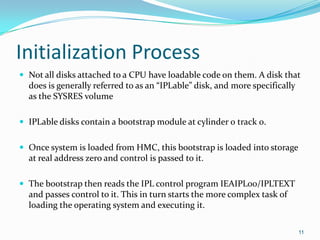
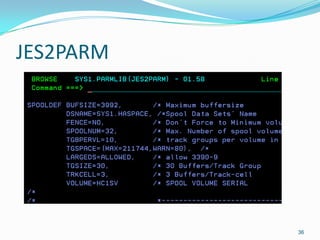
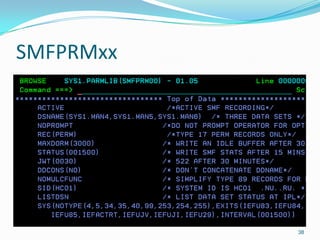
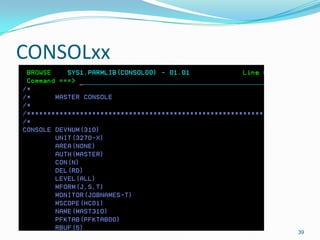
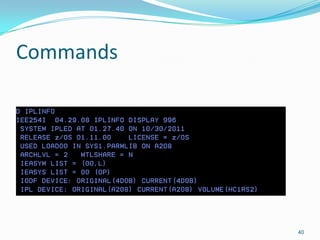
The document provides an overview of the initial program load (IPL) process in z/OS. It describes how the bootstrap loads the operating system from disk into memory and passes control to the IPL control program IEAIPL00. This program initializes the system environment and loads initialization programs that initialize system areas, address spaces, and subsystems to start the operating system. The document also discusses system parameters and parmlib members that control the initialization process.