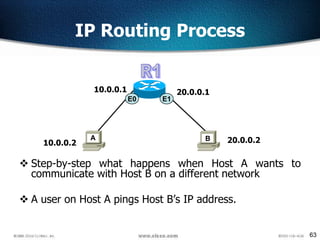
Here are the key steps in the IP routing process:
1. Host A checks its ARP table to see if it has the MAC address for Host B's IP address. Since Host B is on a different network, it does not have this information.
2. Host A sends the packet to its default gateway, Router A. The default gateway is the IP address of the router on the same network as Host A.
3. Router A checks its routing table to see how to reach the destination network for Host B. It sees that the next hop for that network is out its E1 interface.
4. Router A forwards the packet out its E1 interface towards Router B.
5. Router B receives

![69
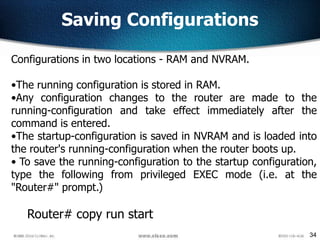
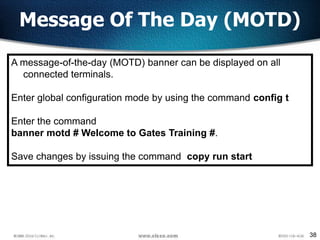
– R1(config)# iproute DestAddress SNM Nexthop address
R1(config)#ip route network [mask]
{address | interface}[distance] [permanent]
Static Route Configuration](https://image.slidesharecdn.com/ccna-day2-130802170150-phpapp02/85/Ccna-day2-67-320.jpg)
![70
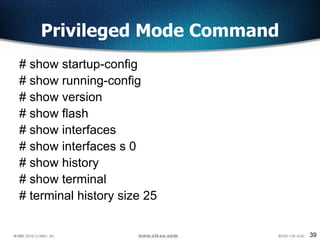
ip route The command used to create the static route.
destination_network The network you’re placing in the routing table.
mask The subnet mask being used on the network.
next-hop_address The address of the next-hop router that will receive the packet
and forward it to the remote network. This is a router interface that’s on a directly
connected network.
exitinterface You can use it in place of the next-hop address if you want, but it’s
got to be on a point-to-point link, such as a WAN
administrative_distance By default, static routes have an administrative
distance of 1 (or even 0 if you use an exit interface instead of a next-hop address)
permanent If the interface is shut down, or the router can’t communicate to the
next-hop router, the route will automatically be discarded from the routing table.
Choosing the permanent option keeps the entry in the routing table no matter what
happens.
ip route [destination_network] [mask] [next-hop_address or exitinterface]
[administrative_distance] [permanent
Static Route Configuration
R1(config)#ip route 30.0.0.0 255.0.0.0 20.0.0.2](https://image.slidesharecdn.com/ccna-day2-130802170150-phpapp02/85/Ccna-day2-68-320.jpg)
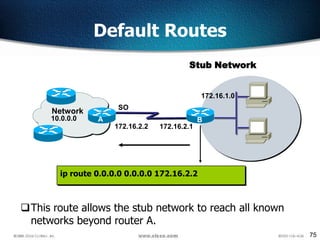
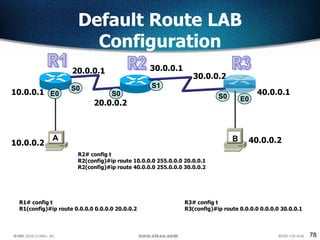
![76
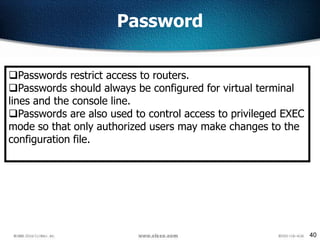
Configuring Default Routes
Default routes are used to route packets with destinations that do not
match any of the other routes in the routing table.
A default route is actually a special static route that uses this format:
ip route 0.0.0.0 0.0.0.0 [next-hop-address | outgoing interface]
This is sometimes referred to as a “Quad-Zero” route.
Example using next hop address:
Router(config)#ip route 0.0.0.0 0.0.0.0 172.16.4.1
Example using the exit interface:
Router(config)#ip route 0.0.0.0 0.0.0.0 s0/0](https://image.slidesharecdn.com/ccna-day2-130802170150-phpapp02/85/Ccna-day2-74-320.jpg)

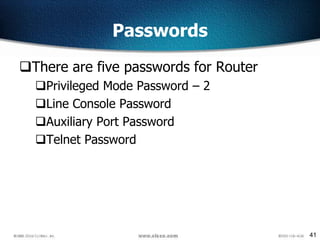
![130
Verifying the IGRP Routing Tables
LabA#sh ip route
[output cut]
I 192.168.50.0 [100/170420] via 192.168.20.2, Serial0/0
I 192.168.40.0 [100/160260] via 192.168.20.2, Serial0/0
I 192.168.30.0 [100/158360] via 192.168.20.2, Serial0/0
C 192.168.20.0 is directly connected Serial0/0
C 192.168.10.0 is directly connected, FastEthernet0/0
• The I means IGRP-injected routes. The 100 in [100/160360] is the
administrative distance of IGRP. The 160,360 is the composite
metric. The lower the composite metric, the better the route.
• To delete all routes
clear ip route](https://image.slidesharecdn.com/ccna-day2-130802170150-phpapp02/85/Ccna-day2-127-320.jpg)