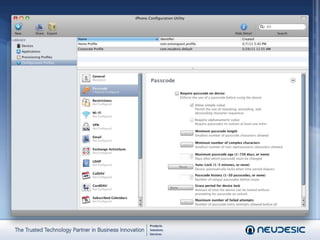
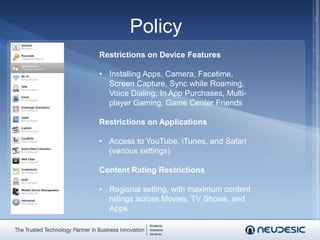
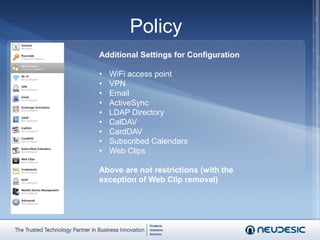
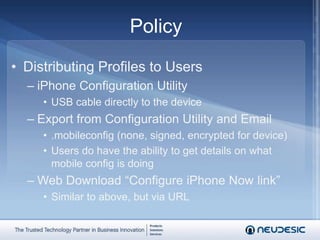
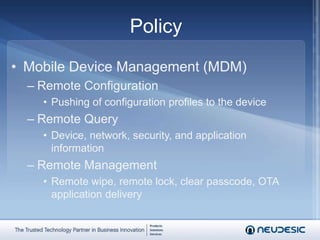
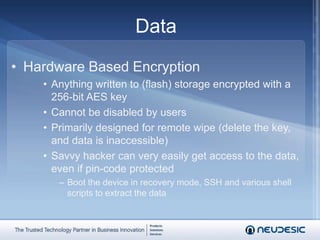
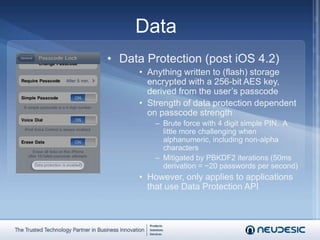
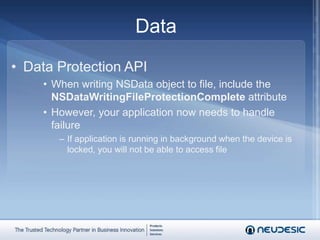
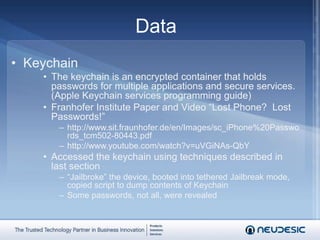
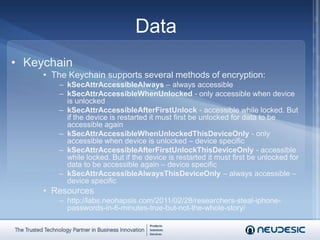
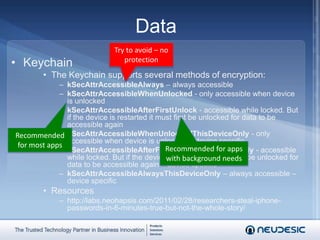
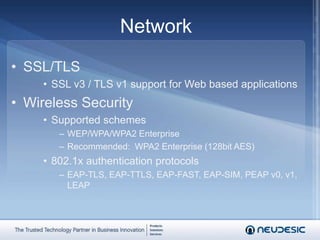
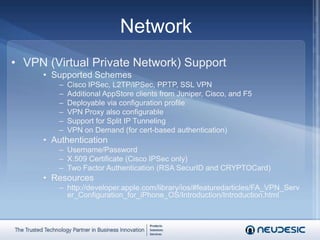
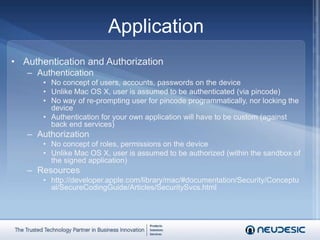
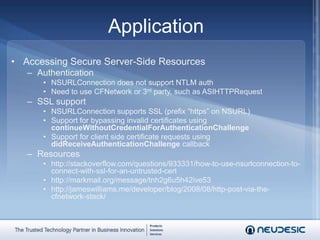
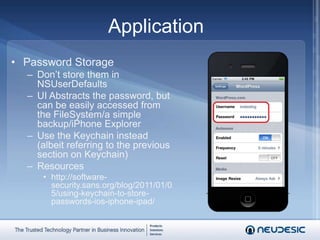
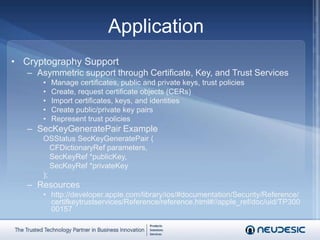
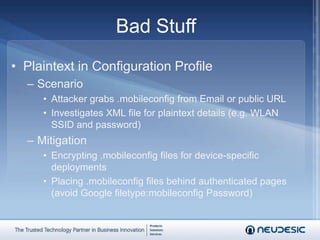
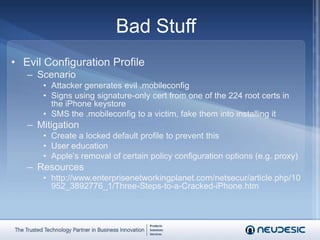
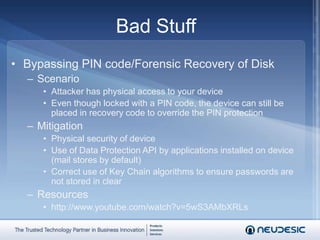
This document summarizes a presentation on iPhone and iPad security. It discusses how to configure passcode policy and other restrictions on devices through configuration profiles. It also covers securing data through encryption, securing network communications through VPNs and SSL, and developing secure applications that properly handle authentication, authorization, data storage and cryptography. The presentation warns of risks from jailbreaking devices and accessing unsecured configuration profiles and provides recommendations for addressing these risks.
![Common QuestionsI don’t want my employees doing [x]. How do I configure policy?What happens if I leave my device on the [bus|train|plane]?How do I secure communication from the device?I’m writing an application. How do I make my application secure?What other bad stuff should I be thinking about?](https://image.slidesharecdn.com/webcast-iphoneipadsecurity-110409000033-phpapp02/85/iPhone-and-iPad-Security-2-320.jpg)
![23451PolicyDataNetworkApplicationBad StuffAgendaI don’t want my employees doing [x] on their device. How do I configure policy?](https://image.slidesharecdn.com/webcast-iphoneipadsecurity-110409000033-phpapp02/85/iPhone-and-iPad-Security-4-320.jpg)