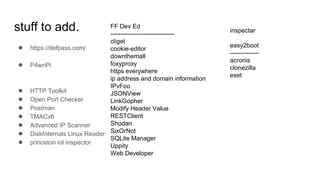
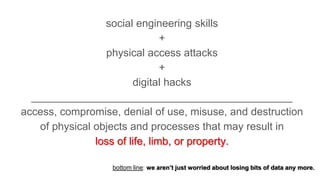
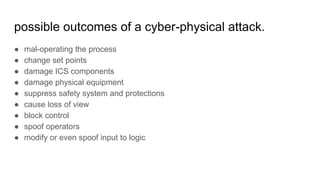
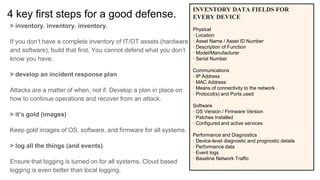
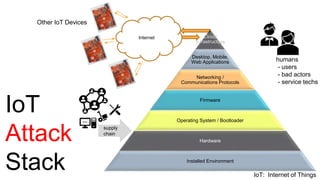
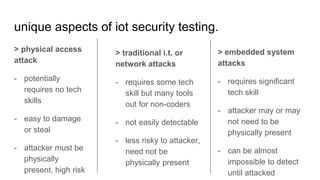
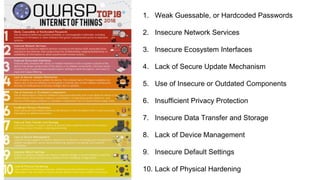
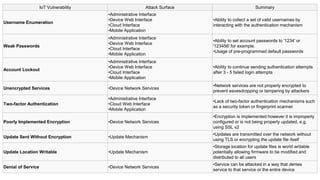
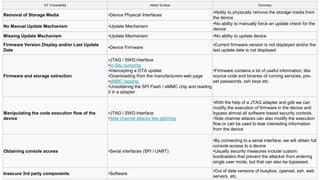
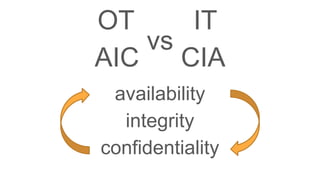
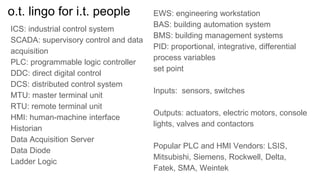
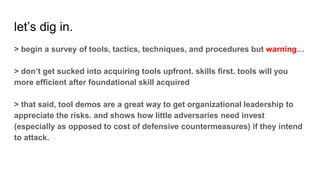
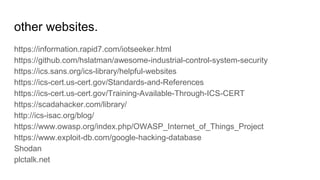
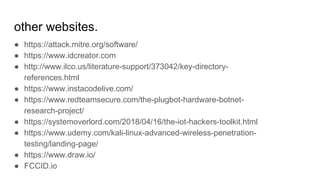
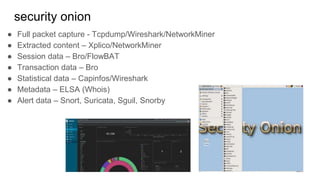
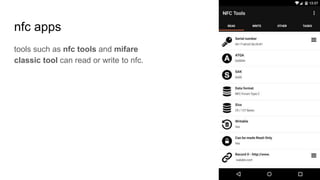
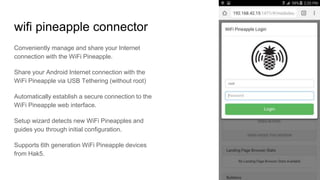
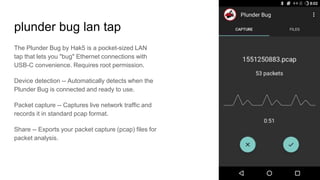
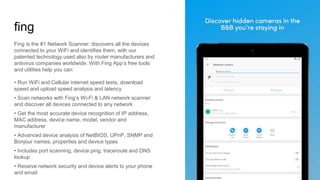
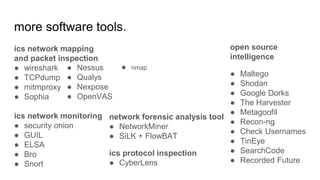
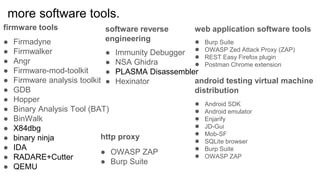
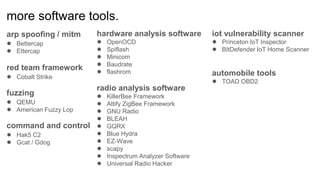
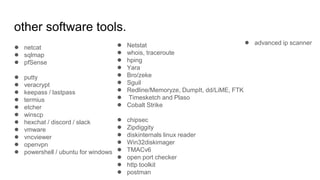
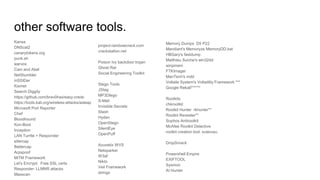
The document discusses the importance of cybersecurity in the context of the Internet of Things (IoT), emphasizing the need for a comprehensive inventory of assets and robust defense strategies against cyber-physical attacks. It outlines best practices, tools, and techniques for security professionals, highlighting the asymmetric nature of threats where attackers need only one vector to succeed while defenders must shield against all possible vulnerabilities. Additionally, it stresses the significance of continuous monitoring, incident response planning, and employee education to enhance overall security posture in an increasingly connected world.