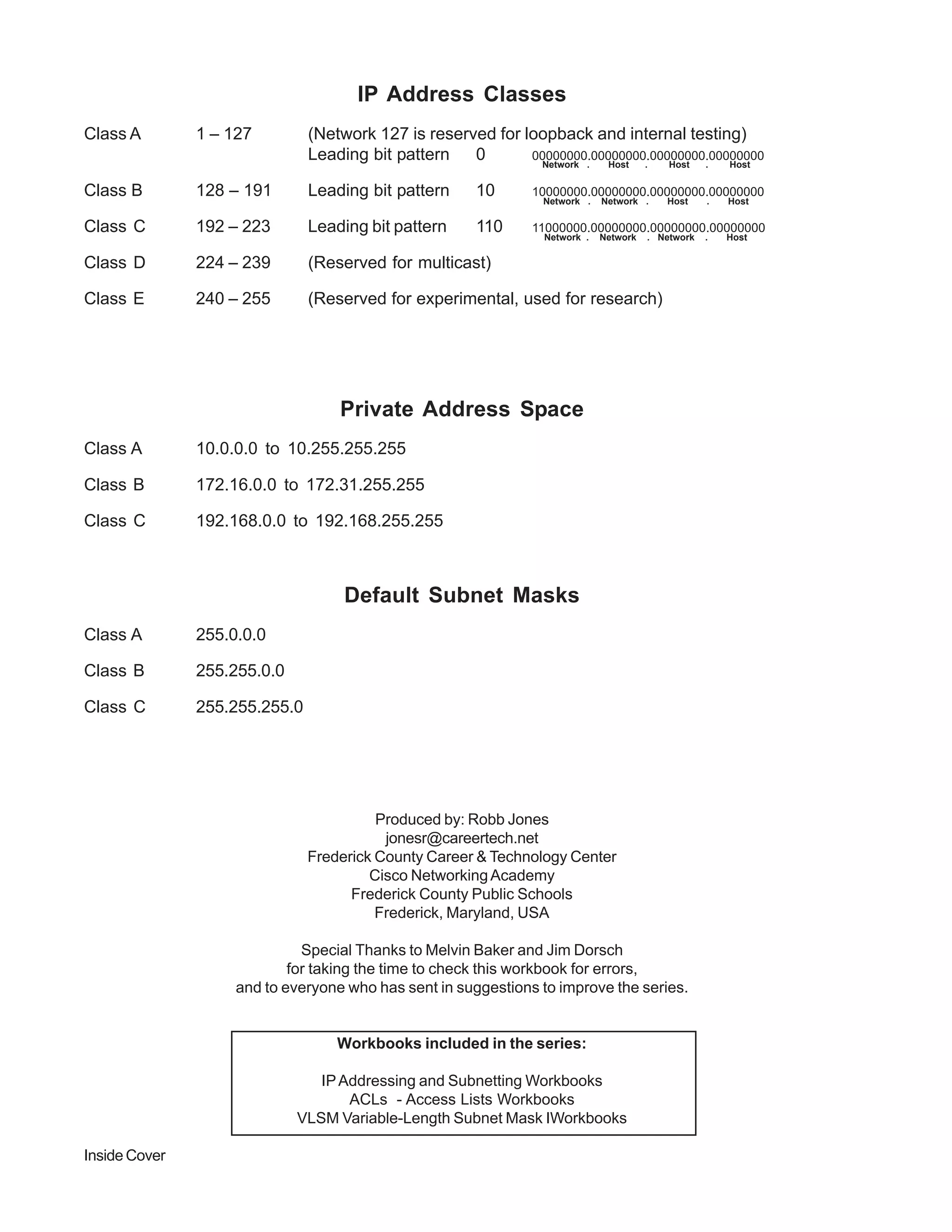
This document discusses IP address classes and subnetting. It defines the five classes of IP addresses (A, B, C, D, E), their address ranges, and default subnet masks. Class A addresses have a network portion of 8 bits, Class B 10 bits, and Class C 16 bits. Private address spaces are also noted for classes A, B, and C. The document explains that computers determine the network and host portions of an IP address by ANDing the address with the default subnet mask.