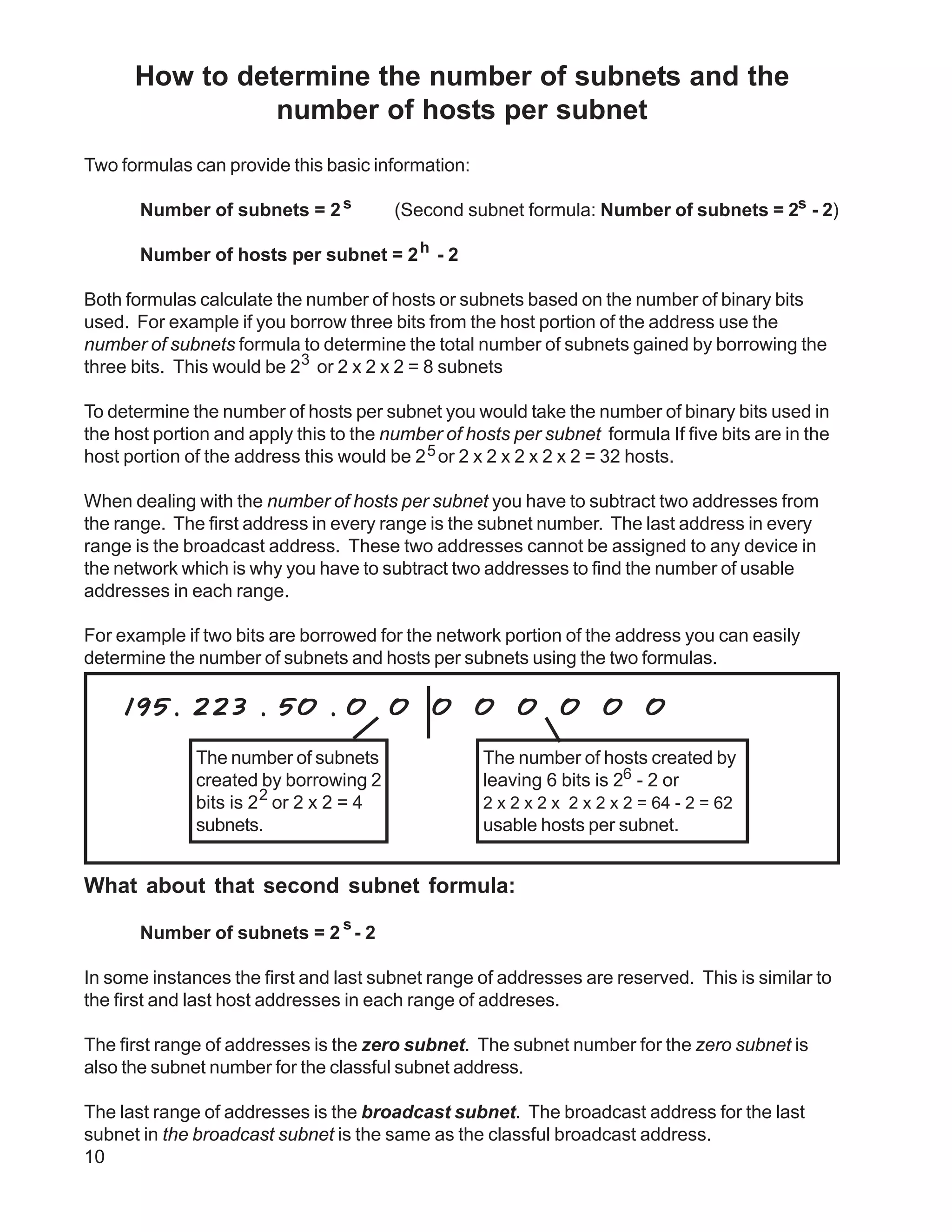
Two formulas can determine the number of subnets and hosts per subnet: the number of subnets equals 2s, and the number of hosts per subnet equals 2h - 2. These formulas calculate the values based on the number of binary bits used. A custom subnet mask can divide a single network into multiple subnets, with each range having a set number of usable addresses. ANDing the IP address with the custom subnet mask shows which subnet range it belongs to.