This document discusses strategies for designing a scalable enterprise network. It introduces the hierarchical network design model with access, distribution, and core layers to organize network traffic. This model, along with using modular and expandable equipment, hierarchical addressing, and redundant links between devices allows the network to scale effectively over time as business needs change and grow. The goals are to limit the impact of failures, provide a path for network expansion, and create a reliable infrastructure.













![18
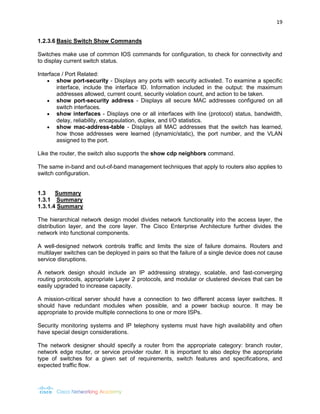
1.2.3.5 Basic Switch CLI Commands
Basic switch configuration includes the hostname for identification, passwords for security, and assignment of IP addresses for connectivity. In-band access requires the switch to have an IP address.
To verify and save the switch configuration using the copy running-config startup-config command. To clear the switch configuration, use the erase startup-config command and then the reload command. It may also be necessary to erase any VLAN information using the command delete flash:vlan.dat. When switch configurations are in place, view the configurations using the show running-config command.
Switch# enable
Switch# configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
Switch (config)# hostname S1
S1 (config)# banner motd %Unauthorized access prohibited%
S1 (config)# enable password cisco
S1 (config)# enable secret class
S1 (config)# line console 0
S1 (config-line)# password cisco
S1 (config-line)# login
S1 (config-line)# line vty 0 4
S1 (config-line)# password cisco
S1 (config-line)# login
S1 (config-line)# interface vlan 1
S1 (config-if)# ip address 192.168.1.5 255.255.255.0
S1 (config-if)# no shutdown
S1 (config-if)# exit
S1 (config)# ip default-gateway 192.168.1.1
S1 (config)# interface fa0/2
S1 (config-if)# switchport mode access
S1 (config-if)# switchport port-security
S1 (config-if)# end
S1#
S1# copy running-config startup-config
Destination filename [startup/config]?
Building configuration...
[OK]
S1#
By running the command:
S1 # show running-config
This will show the results of the configuration commands that were entered on the left side.](https://image.slidesharecdn.com/chapter1-introductiontoscalingnetworks-141105200023-conversion-gate01/85/Chapter-1-introduction-to-scaling-networks-18-320.jpg)