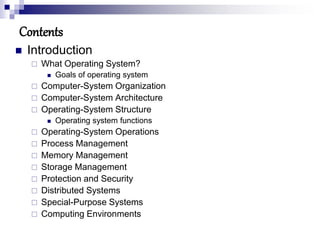
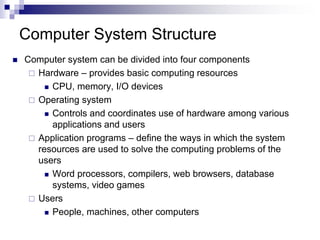
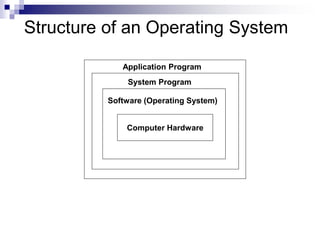
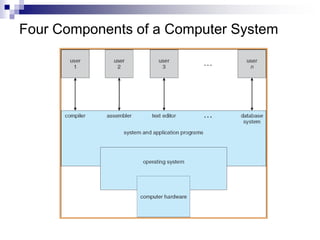
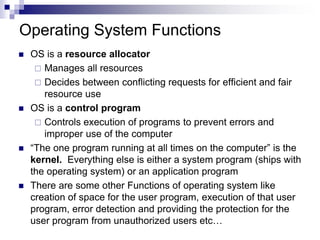
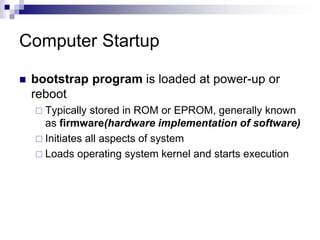
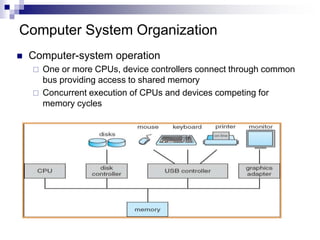
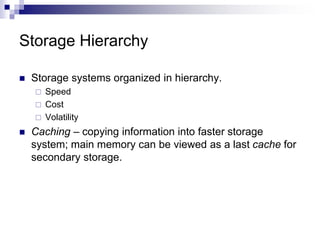
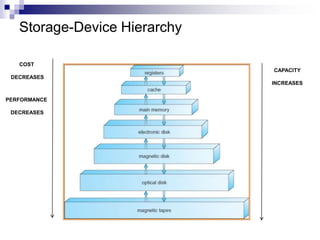
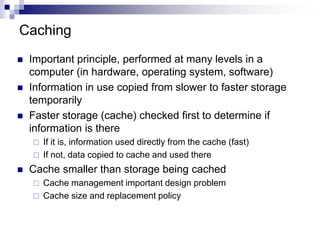
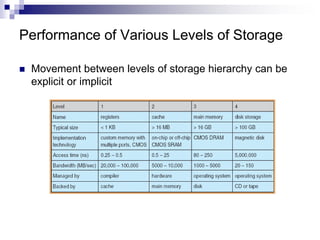
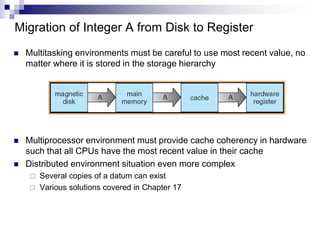
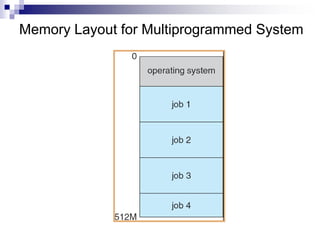
The document discusses the key concepts of operating systems including their goals, structure, functions and management of processes, memory, storage and security. Specifically, it describes how an operating system acts as an intermediary between the user and hardware to execute programs efficiently while making resource allocation decisions. It also outlines the hierarchy of computer storage and caching strategies used to optimize performance.