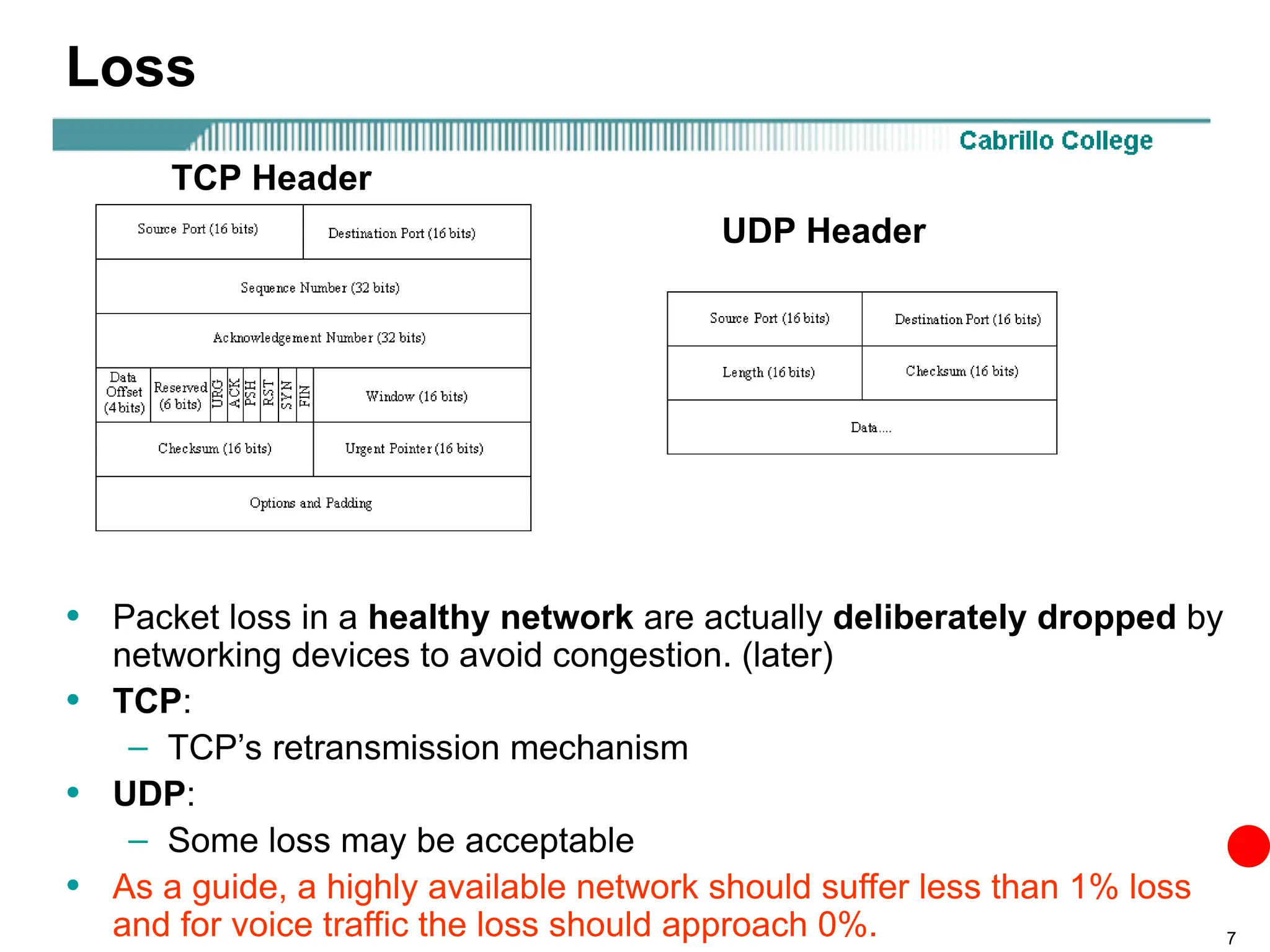
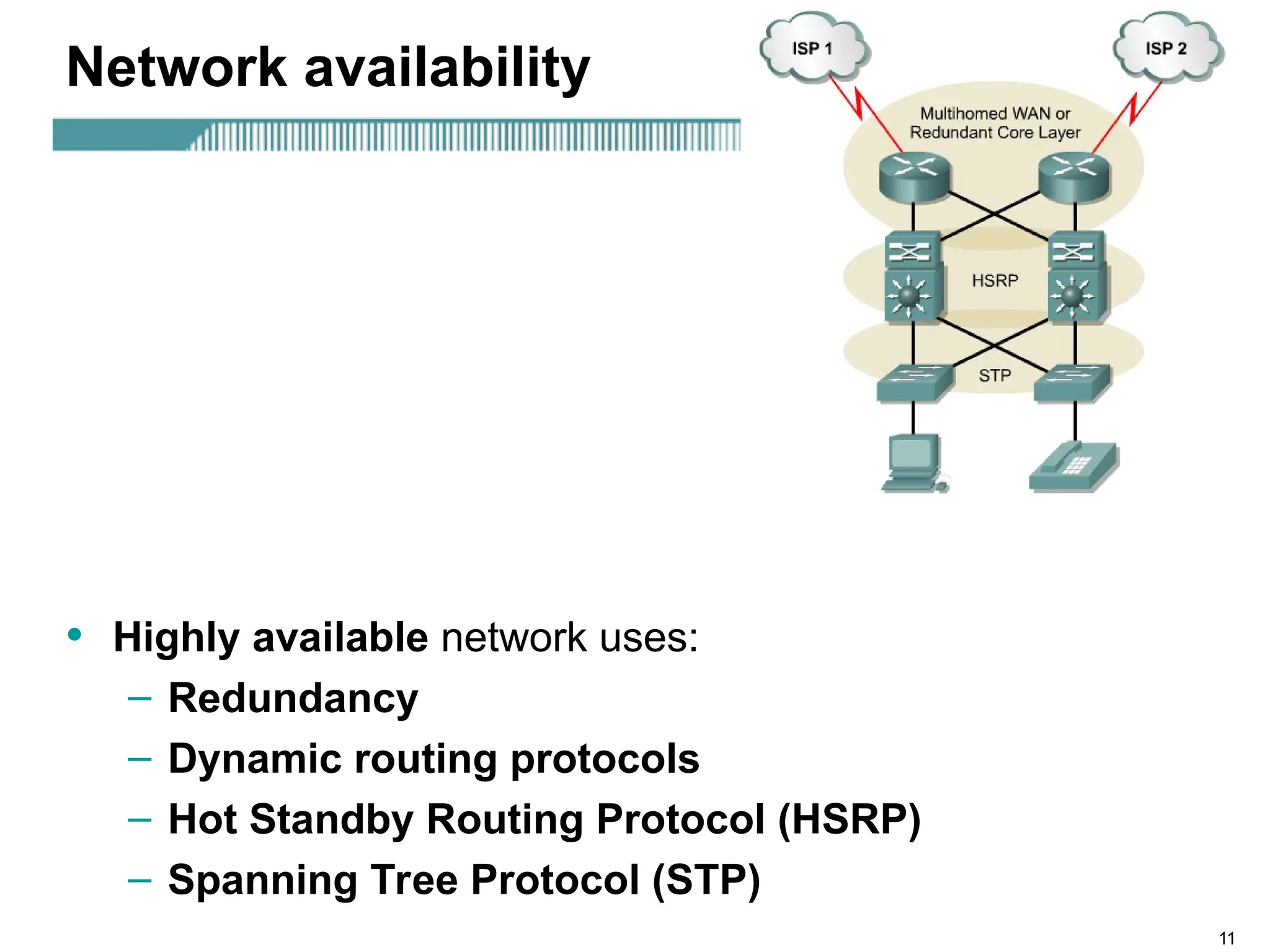
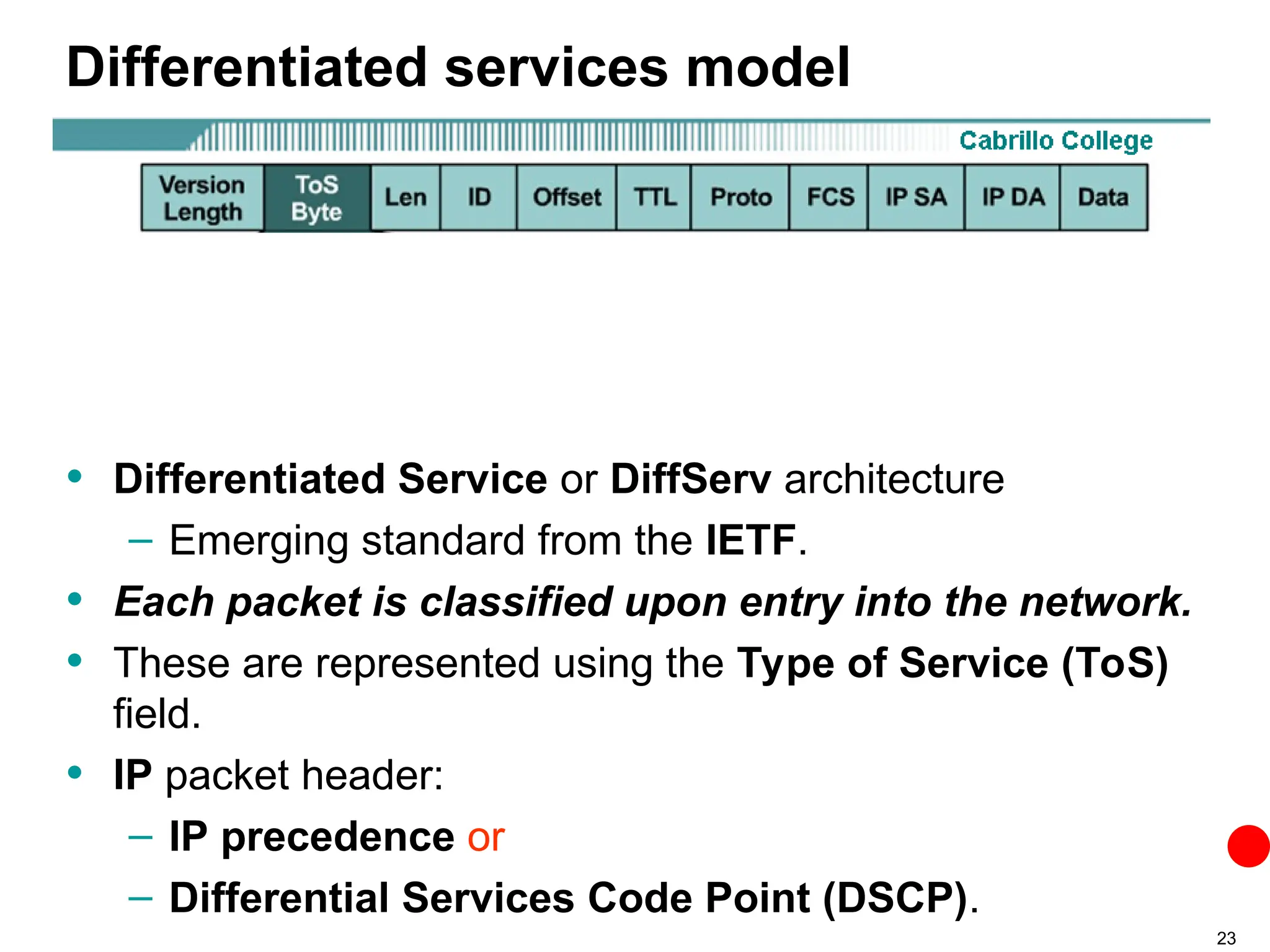
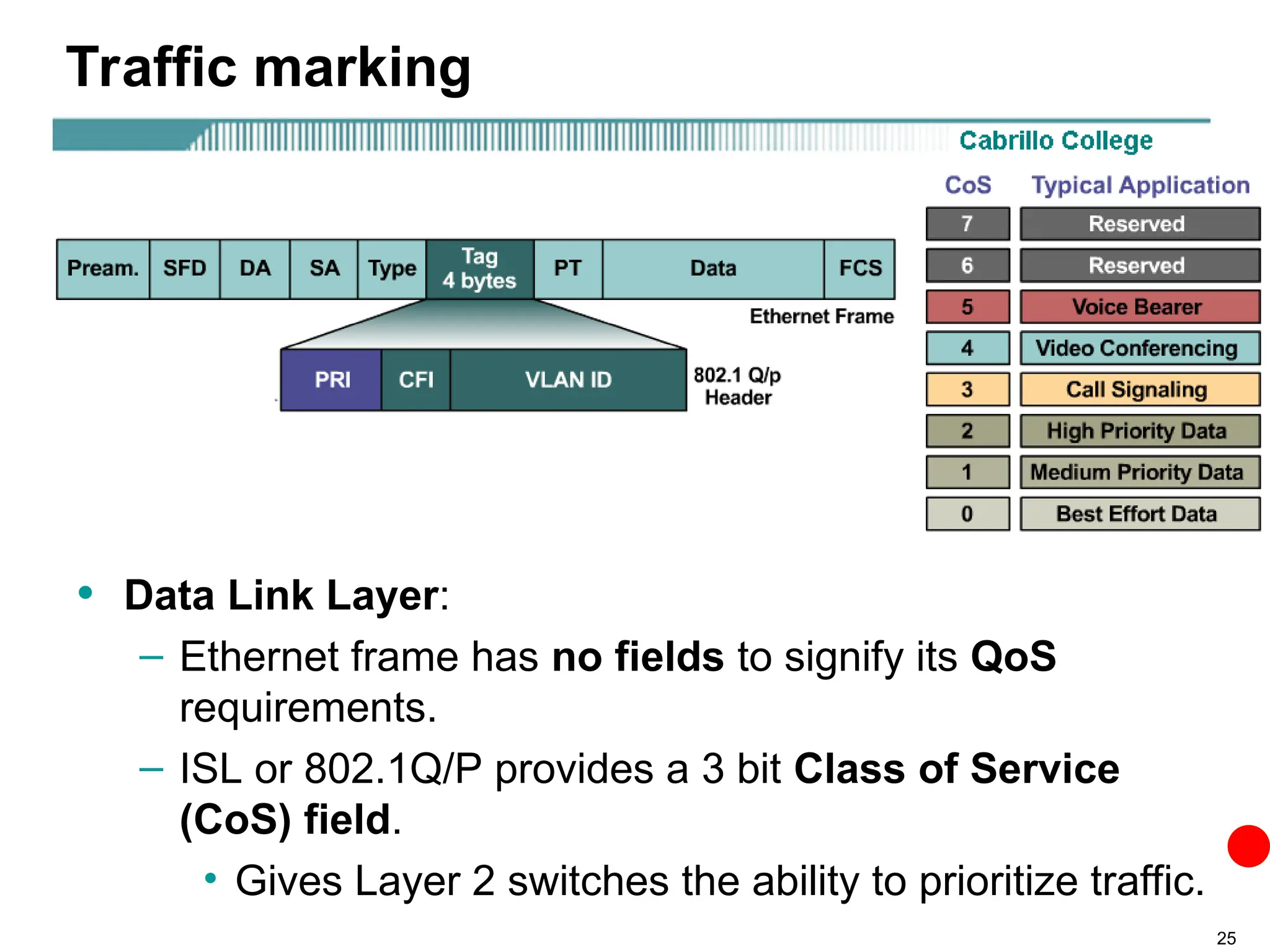
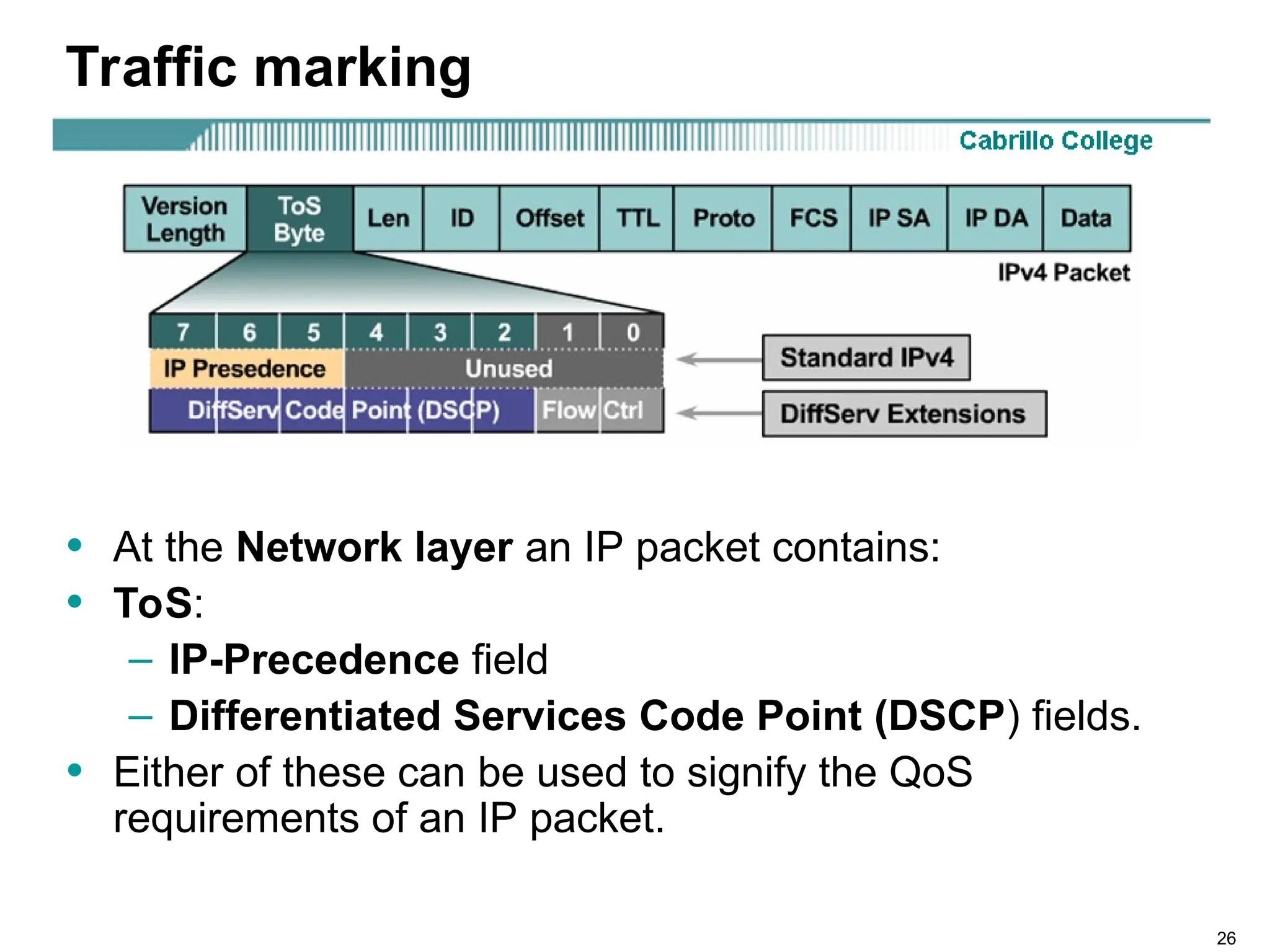
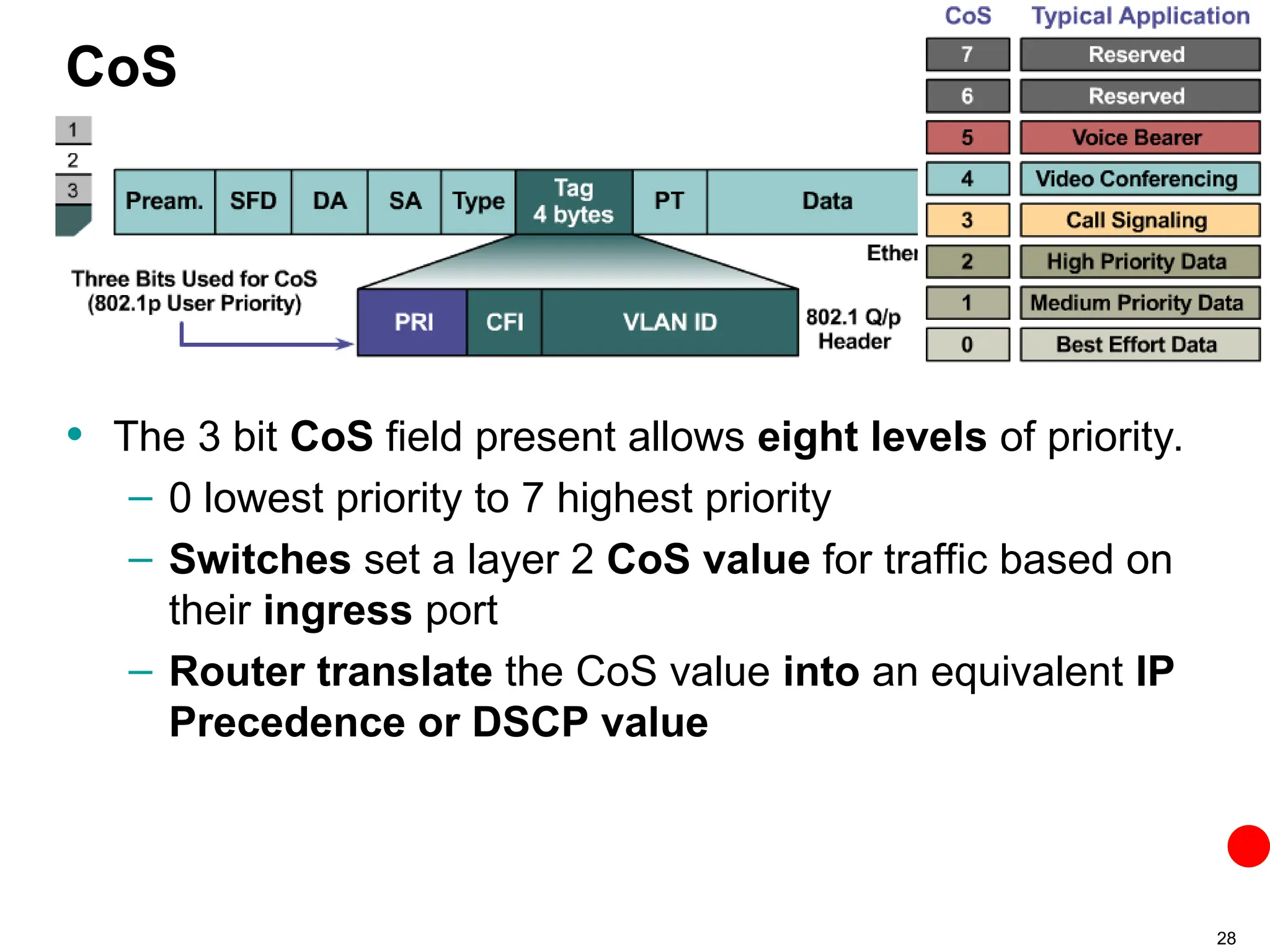
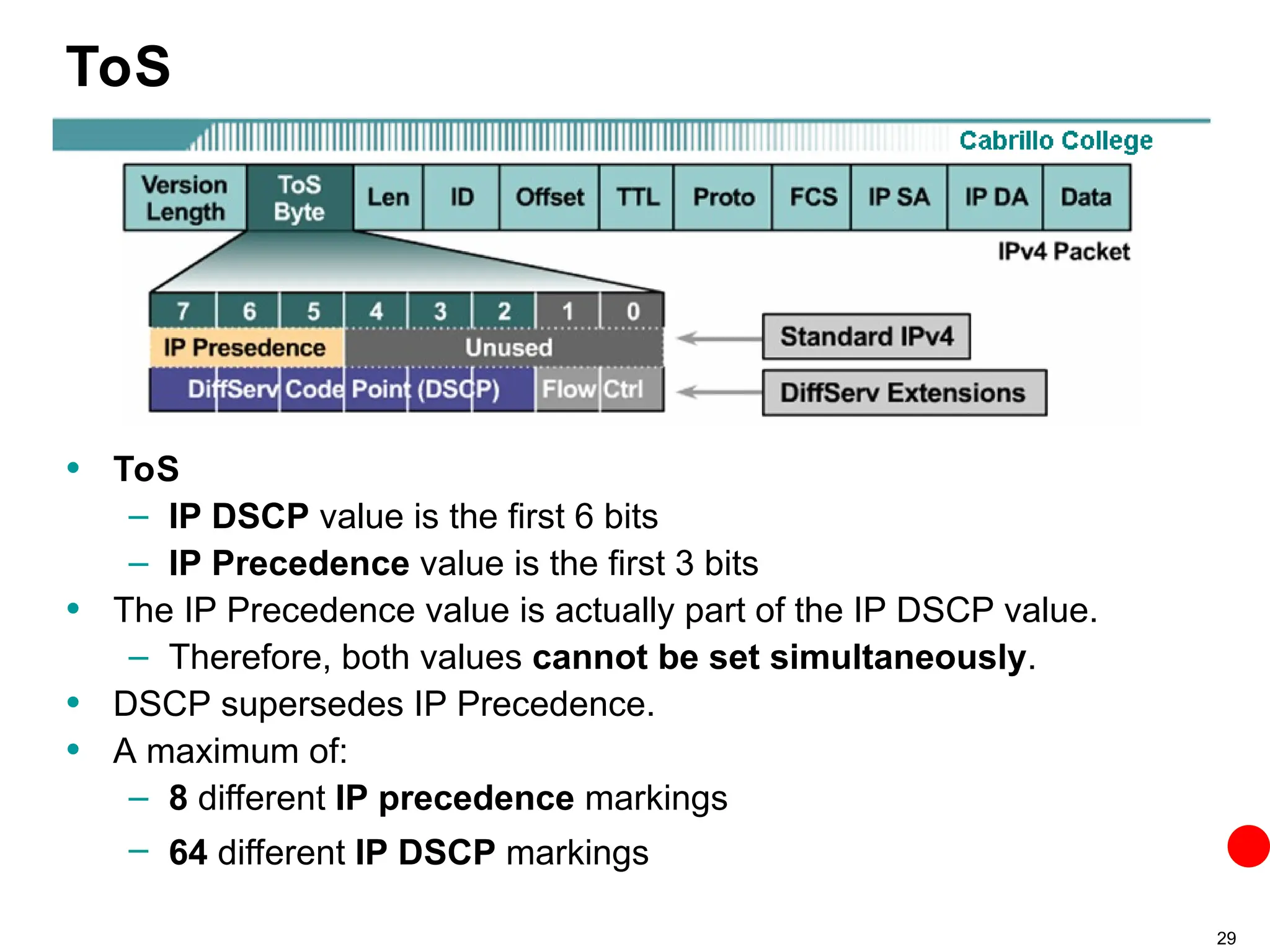
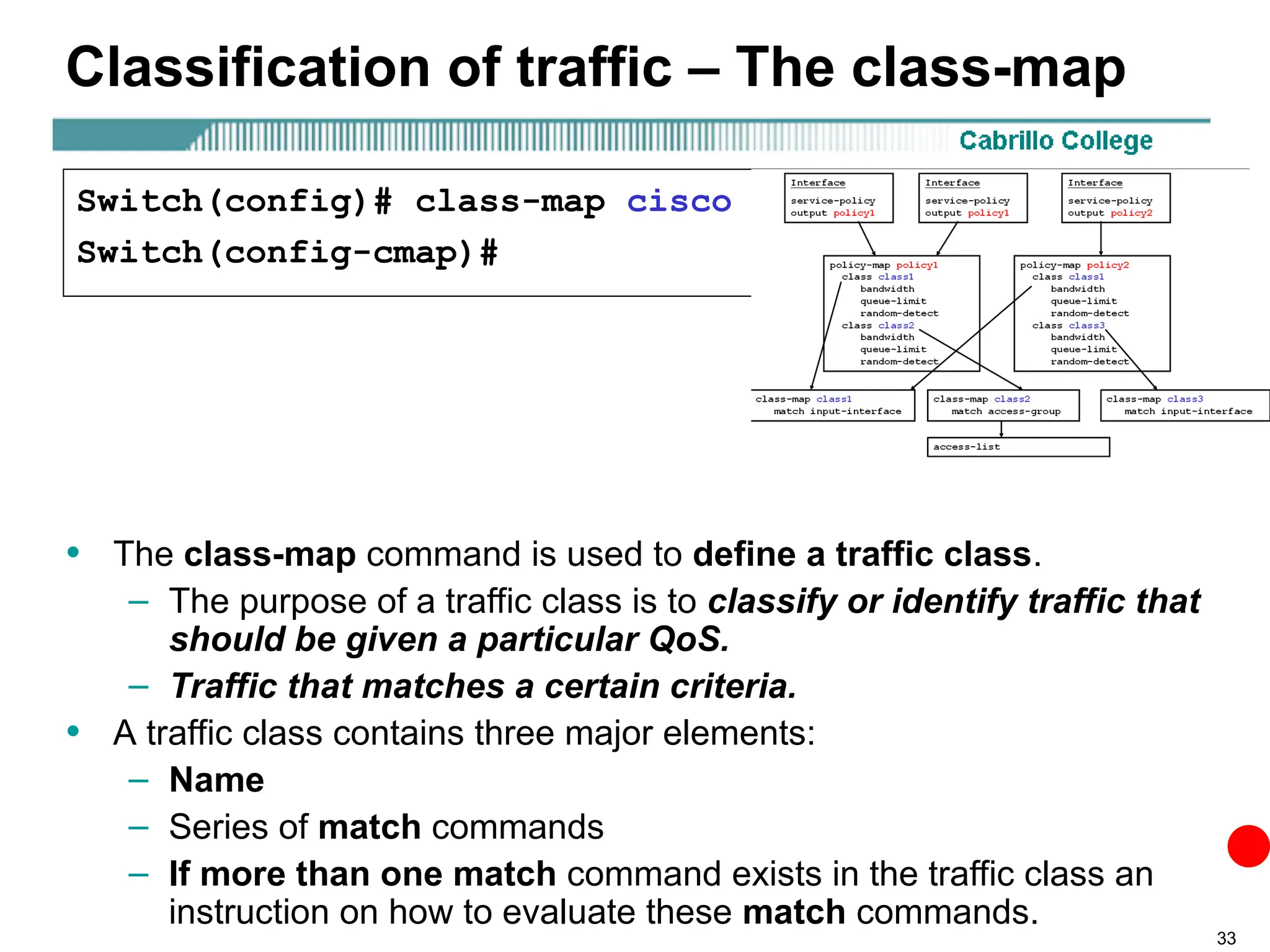
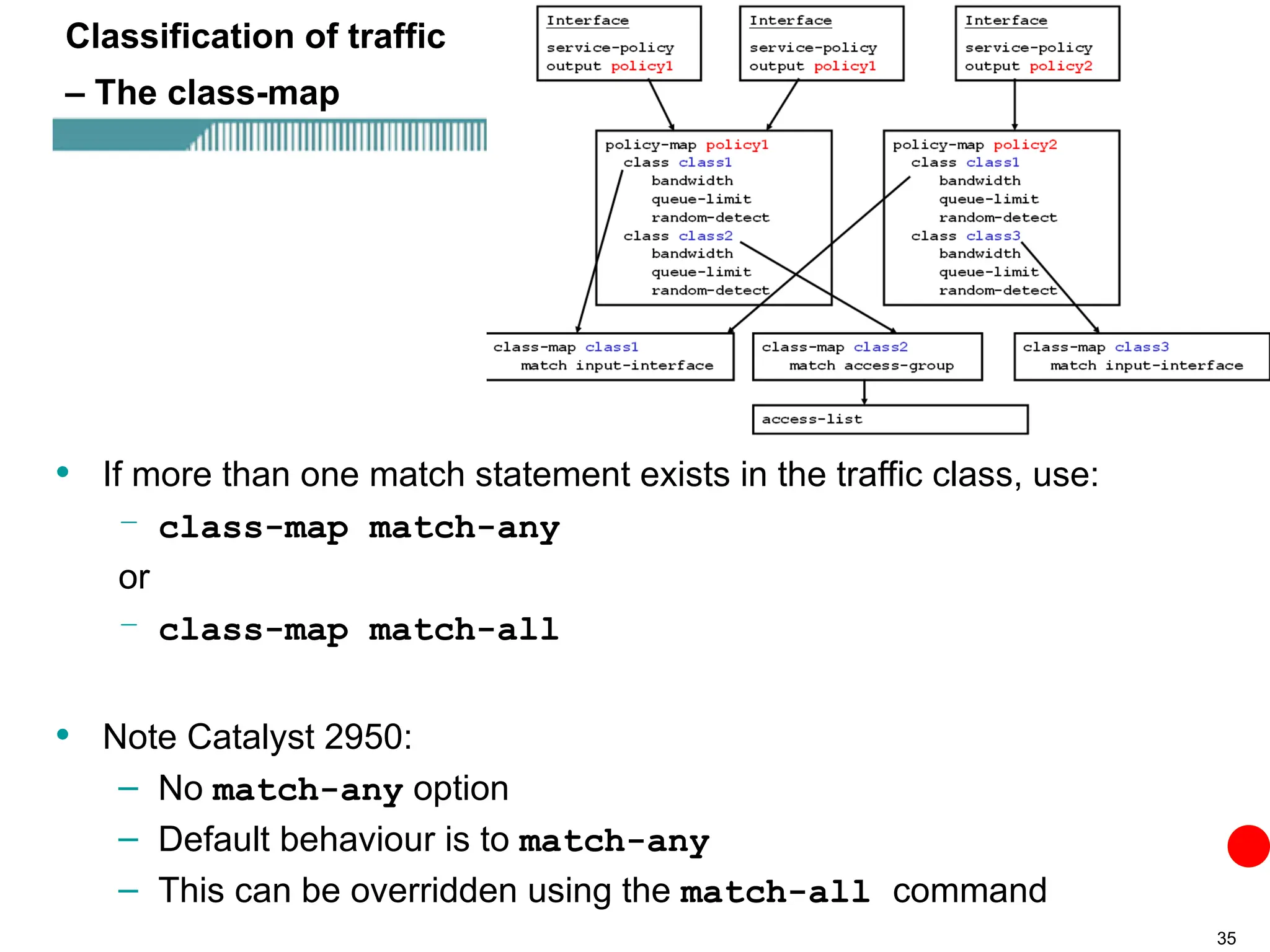
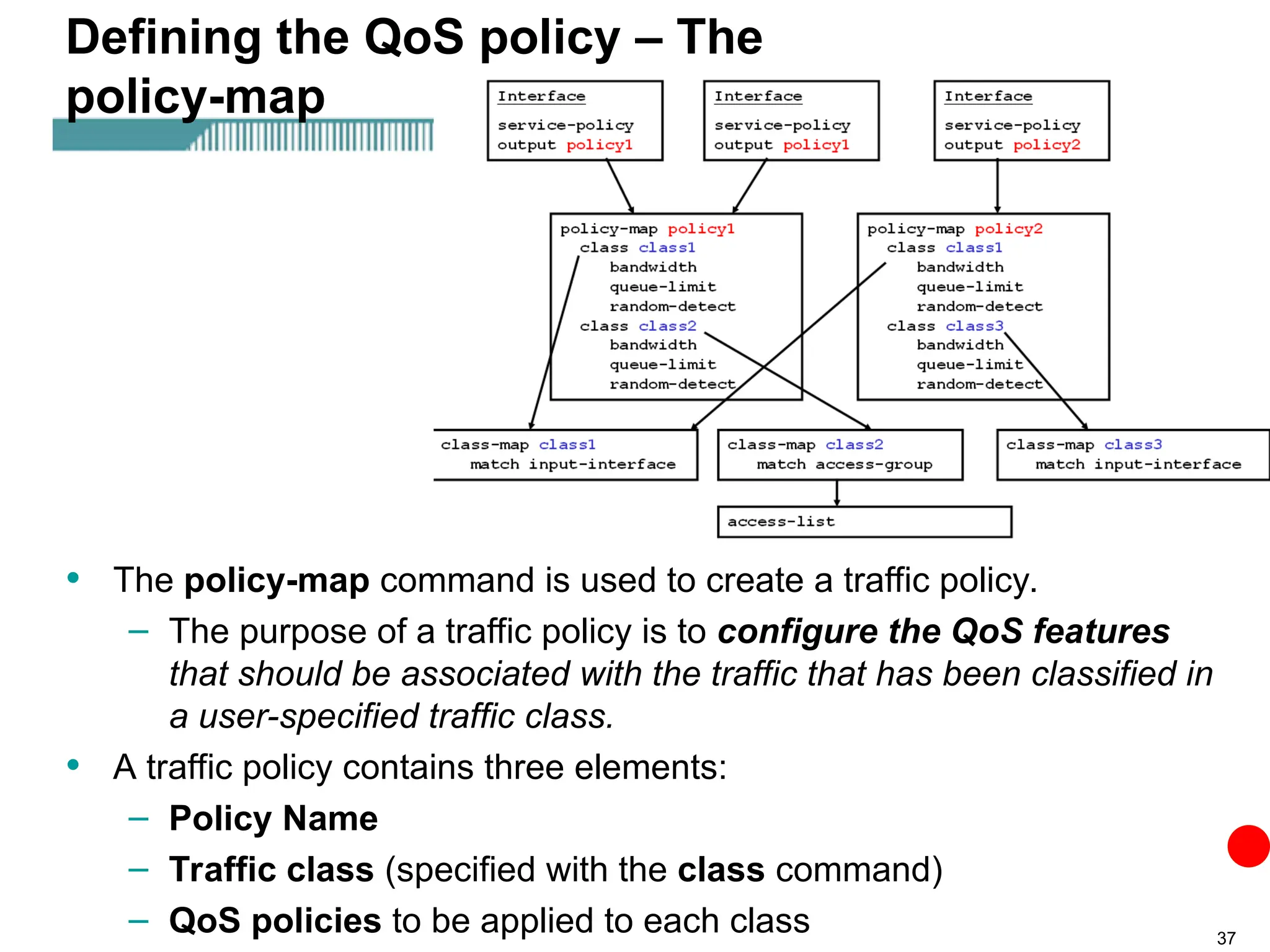
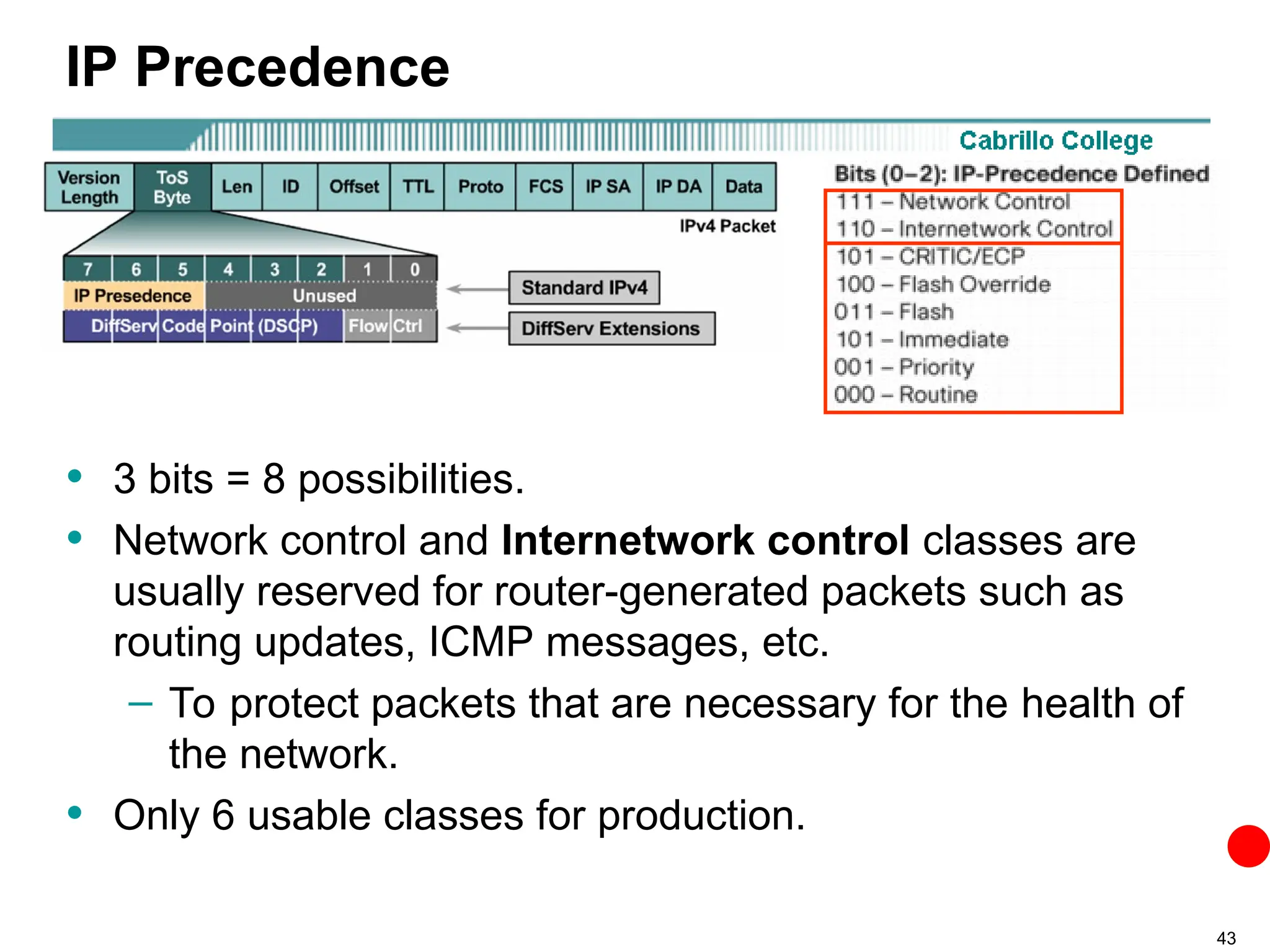
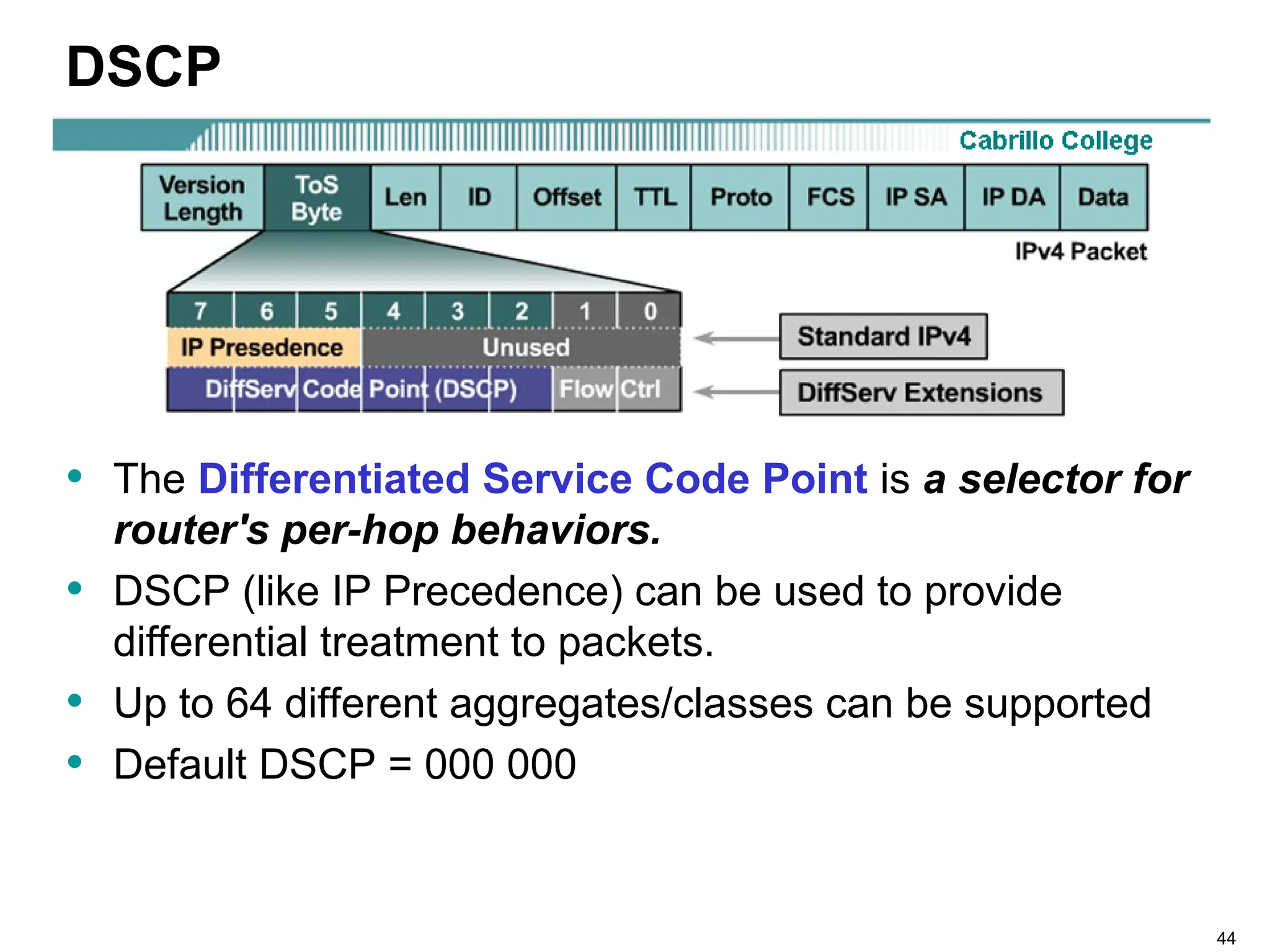
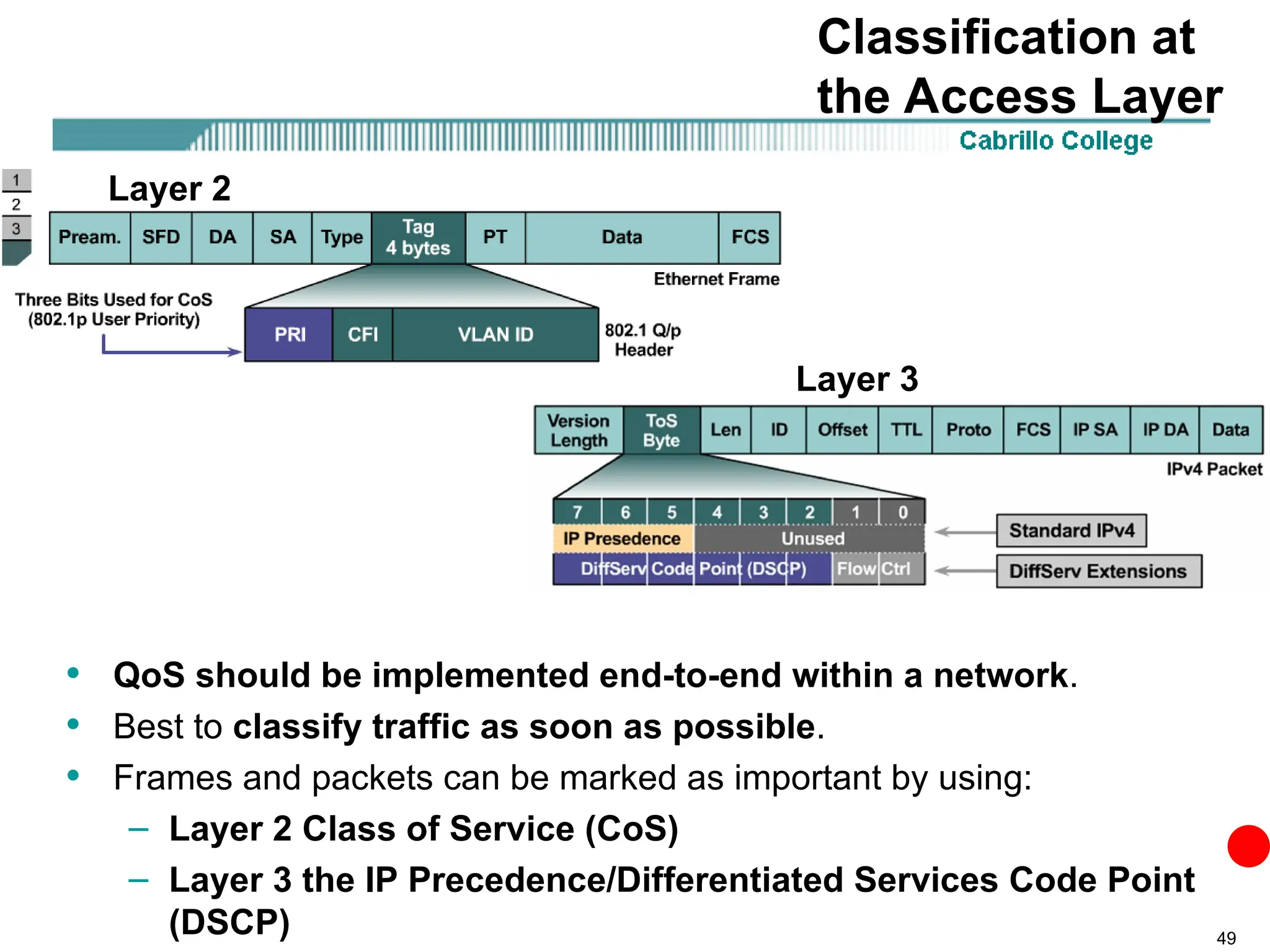
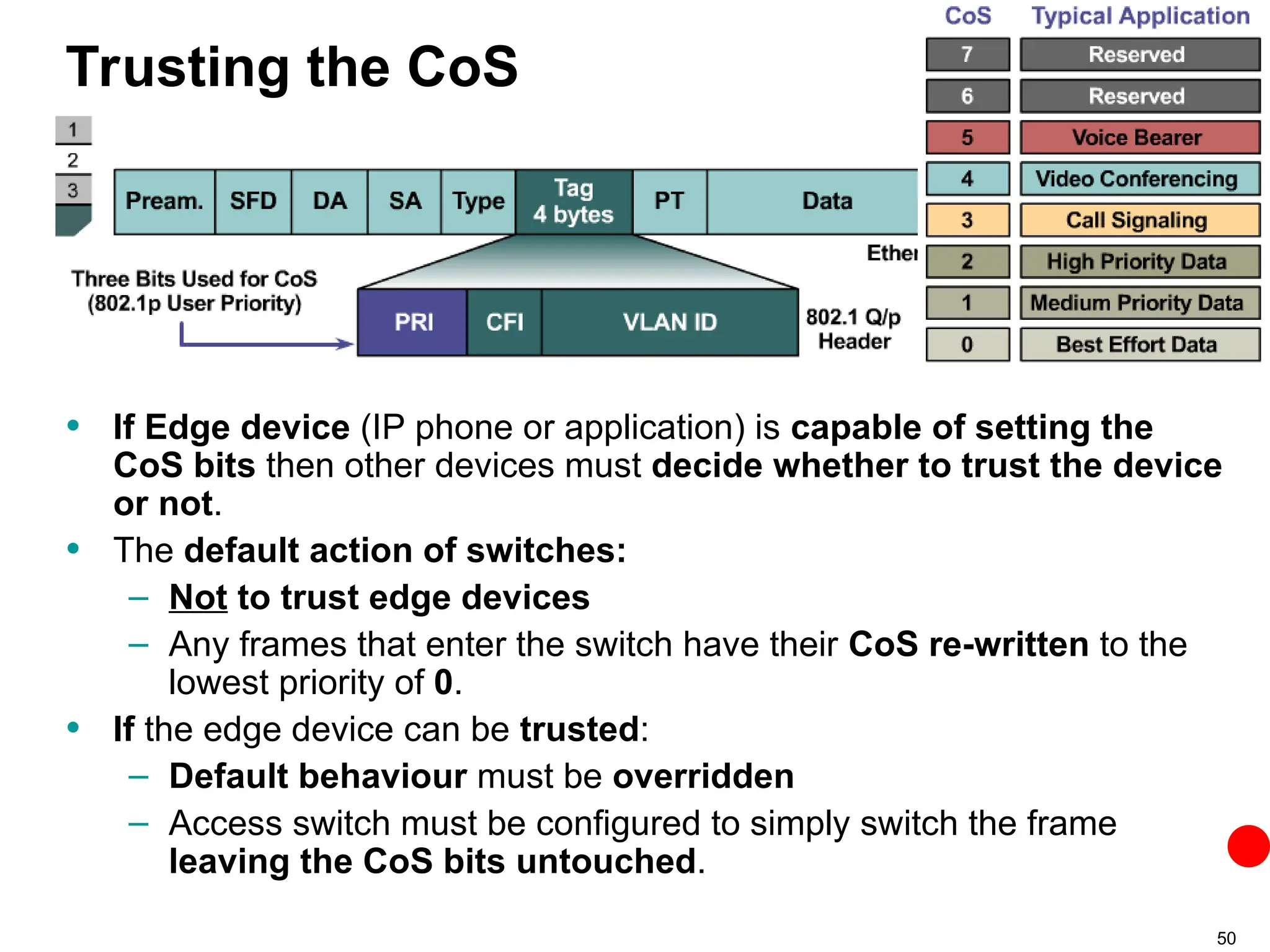
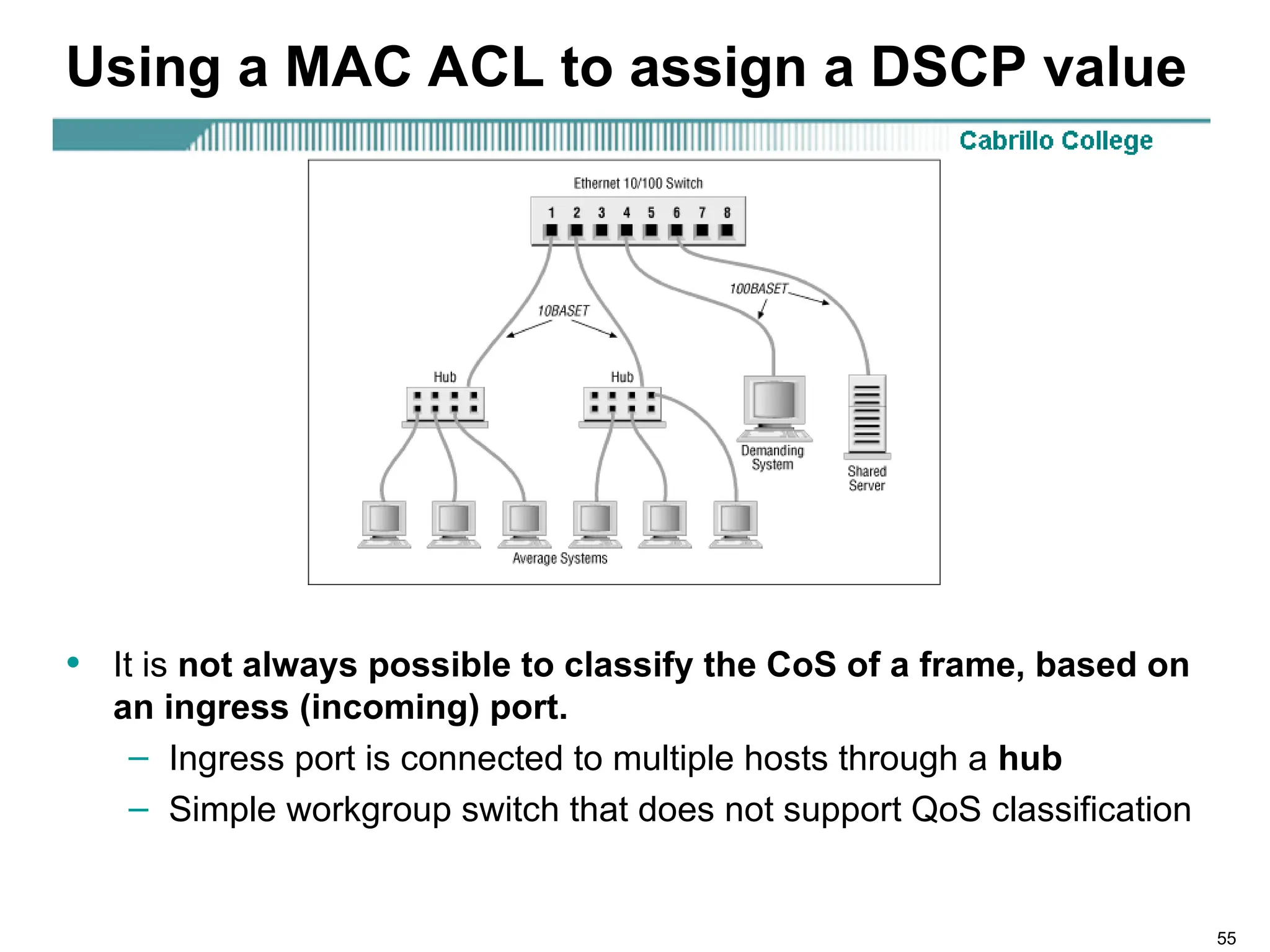
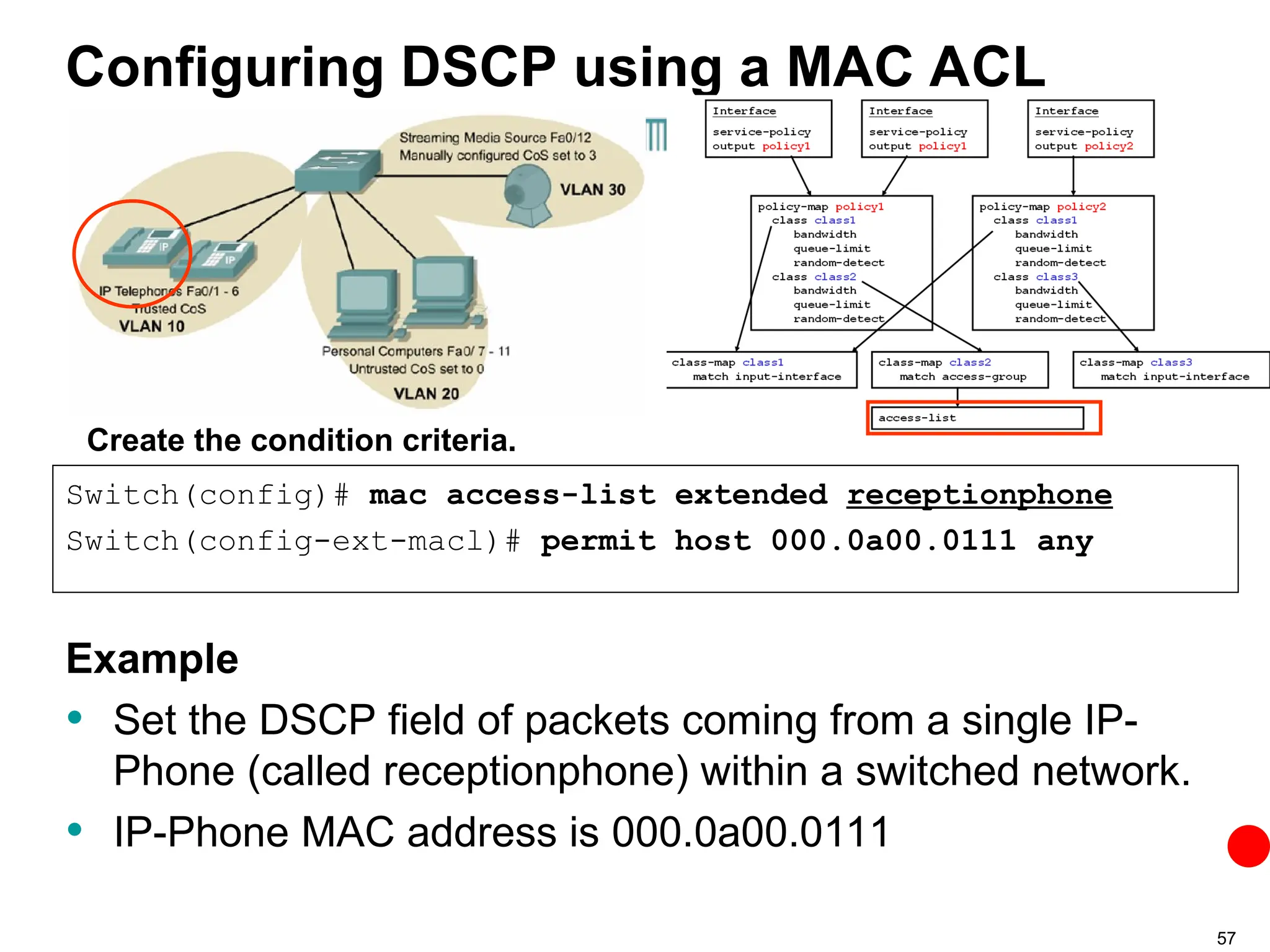
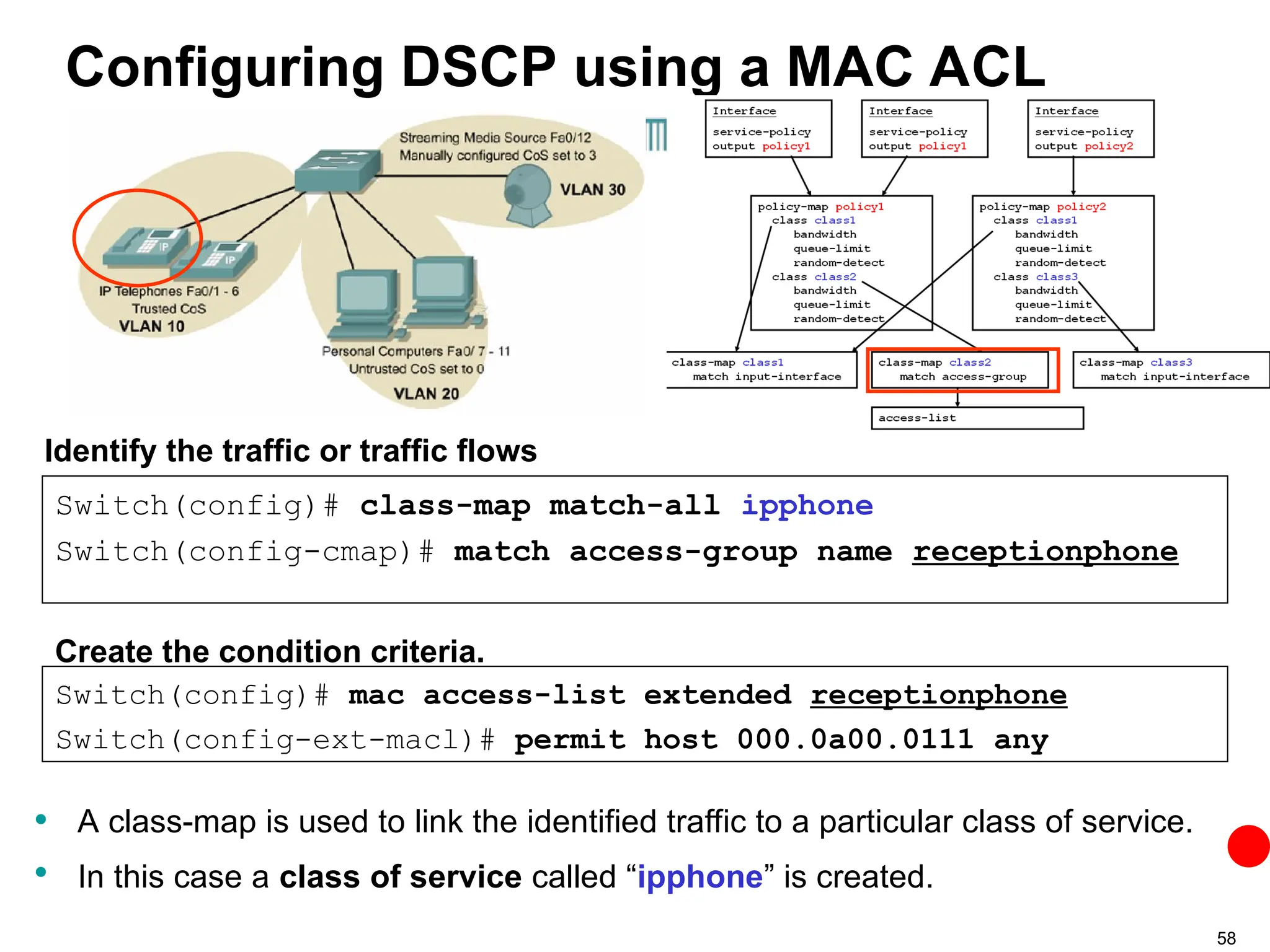
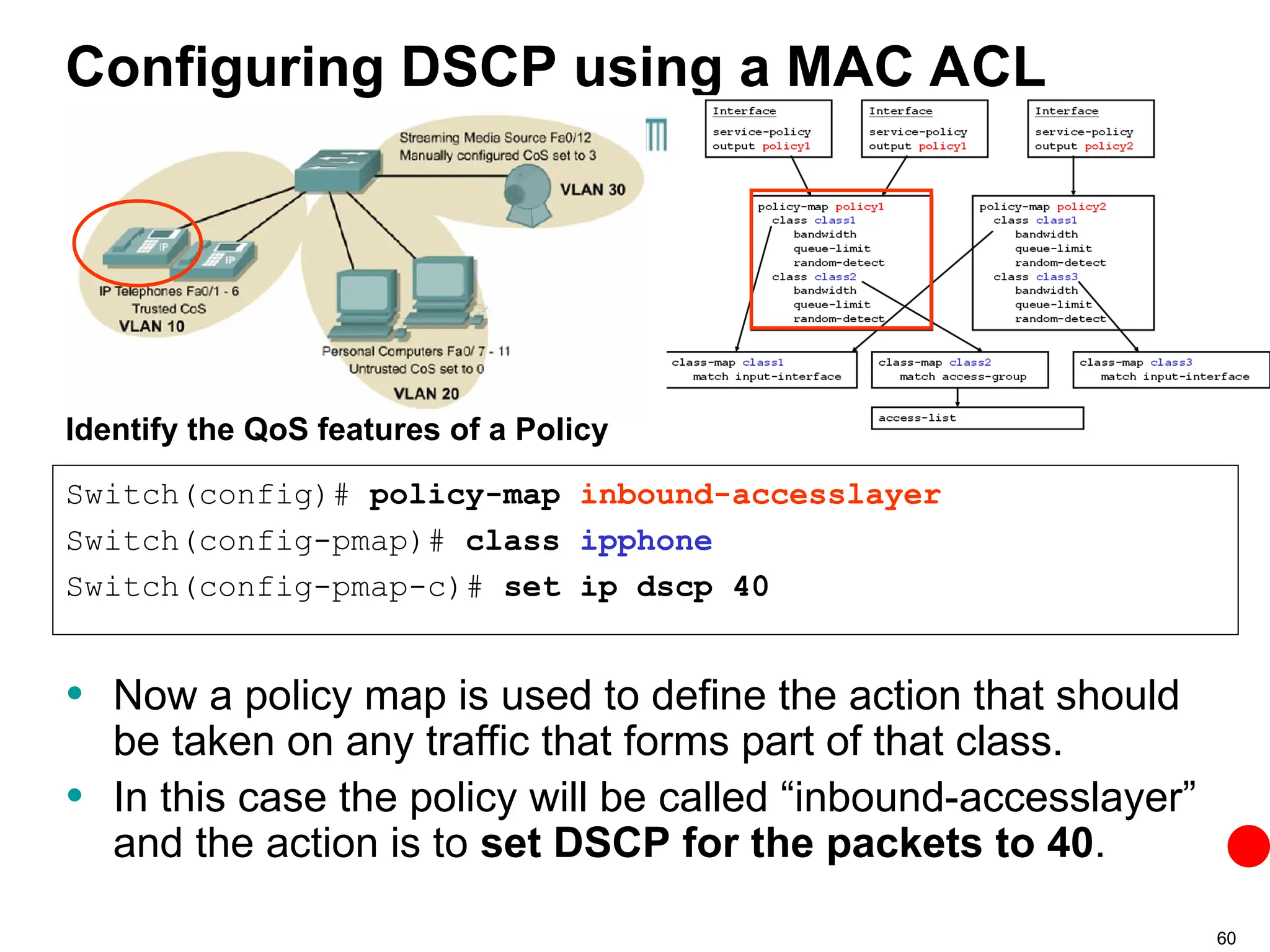
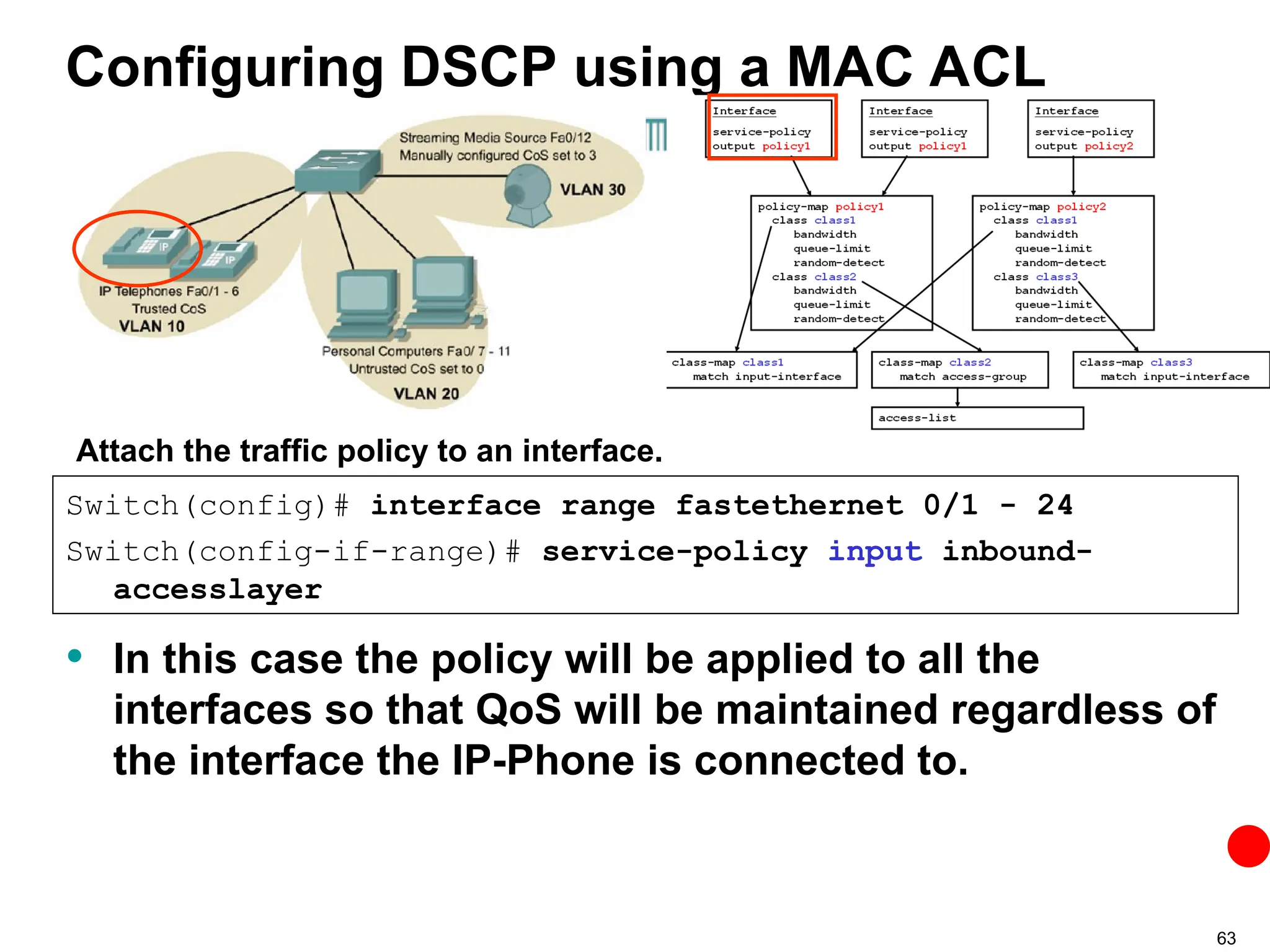
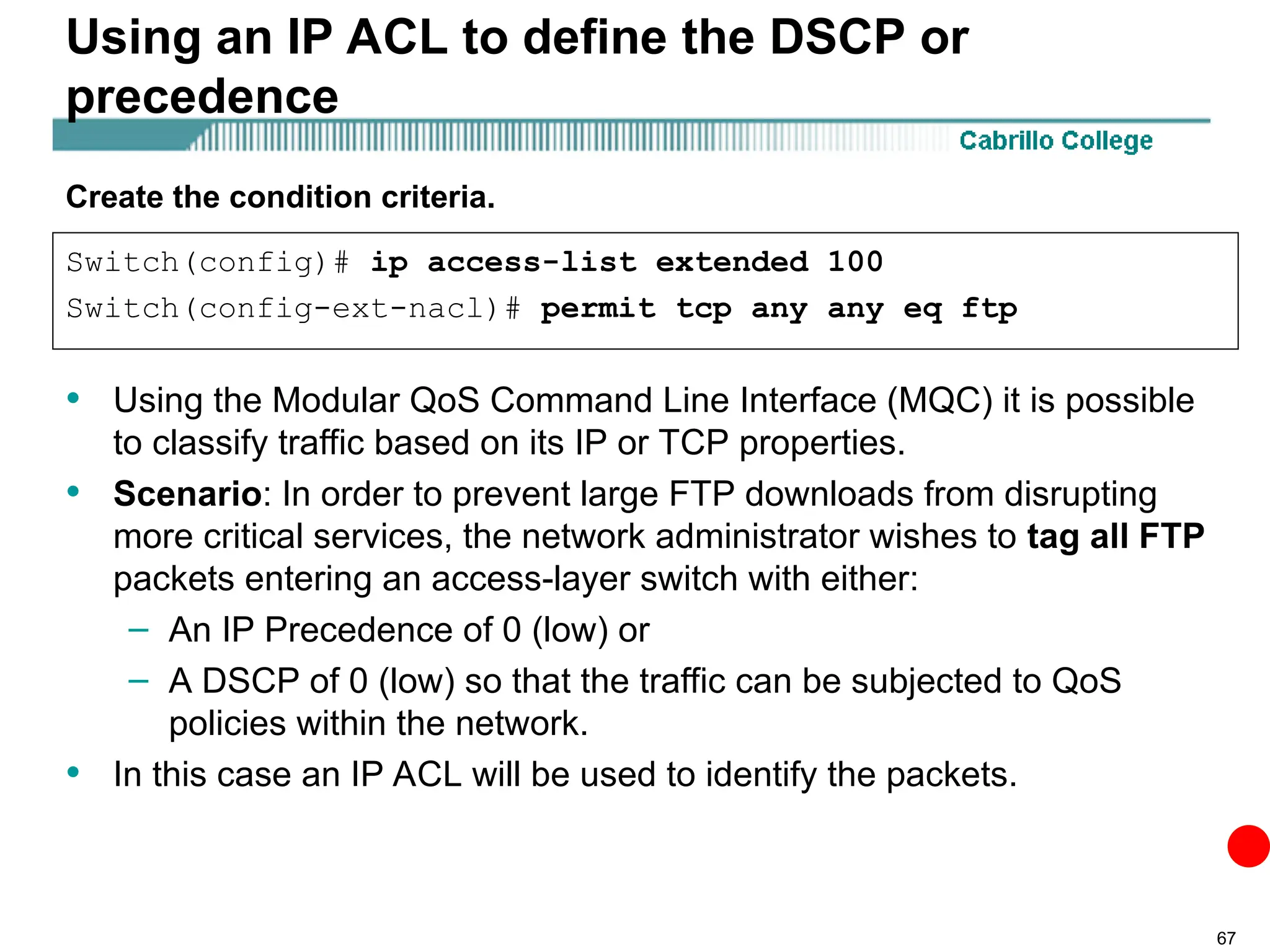
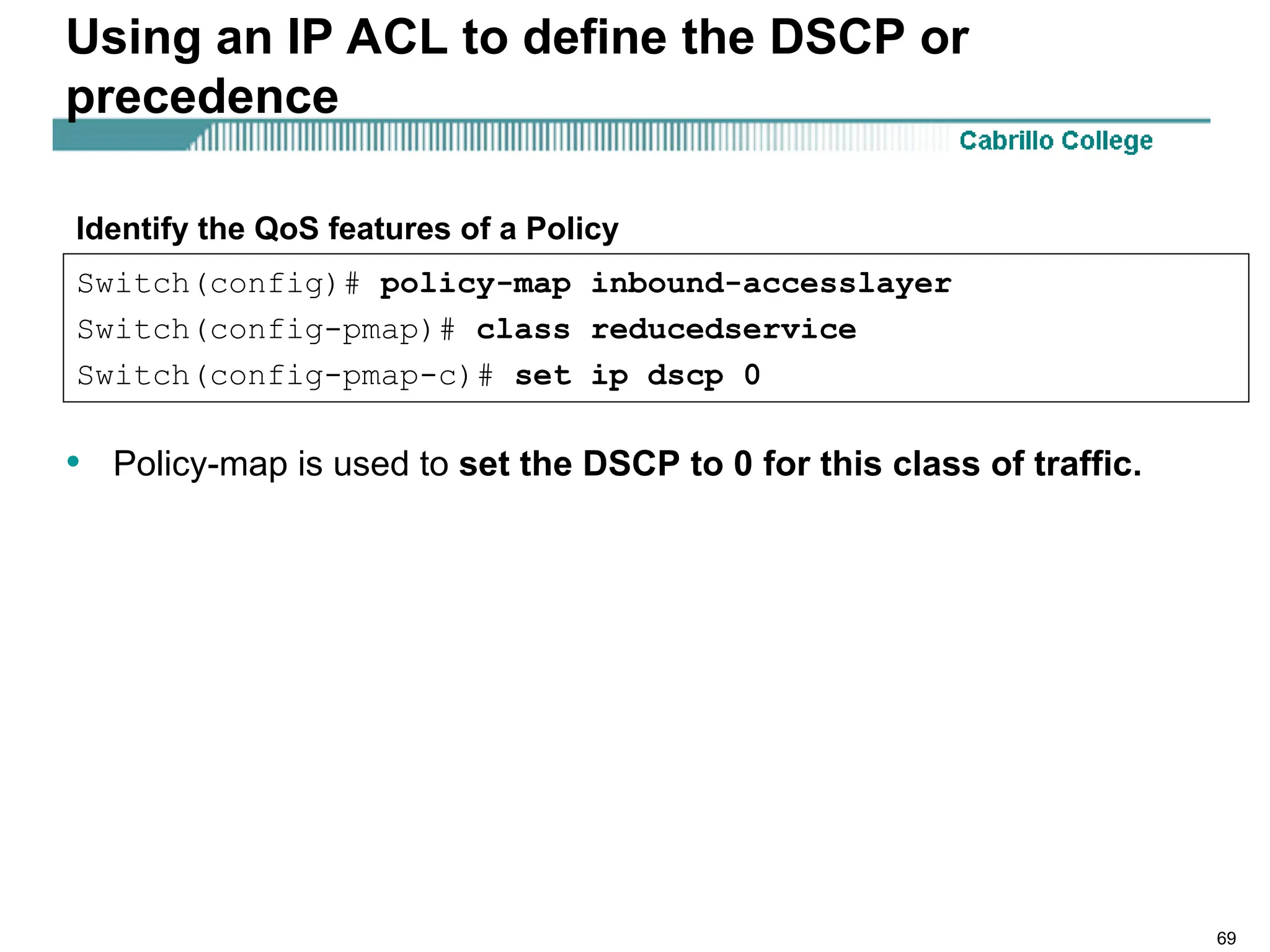
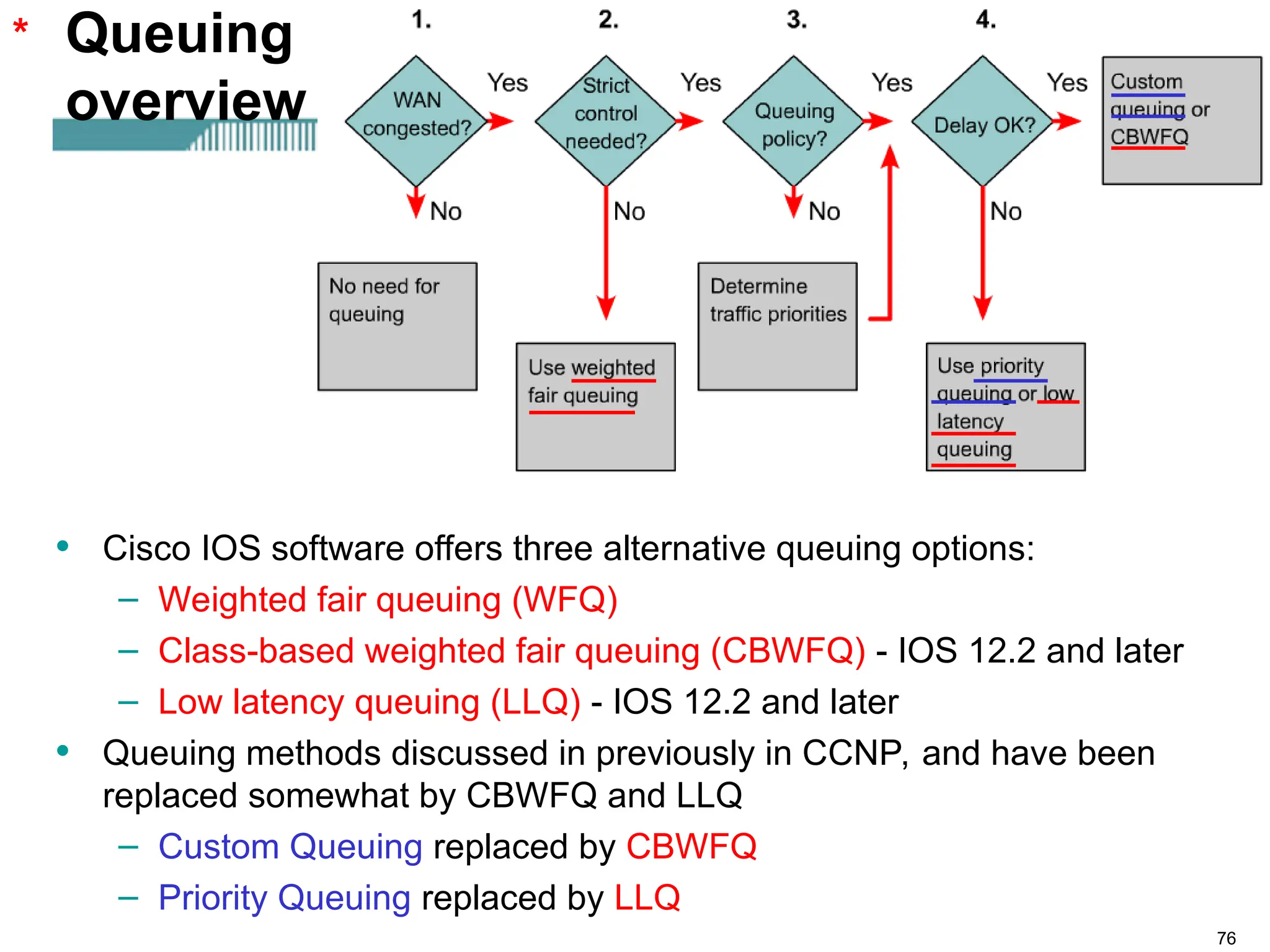
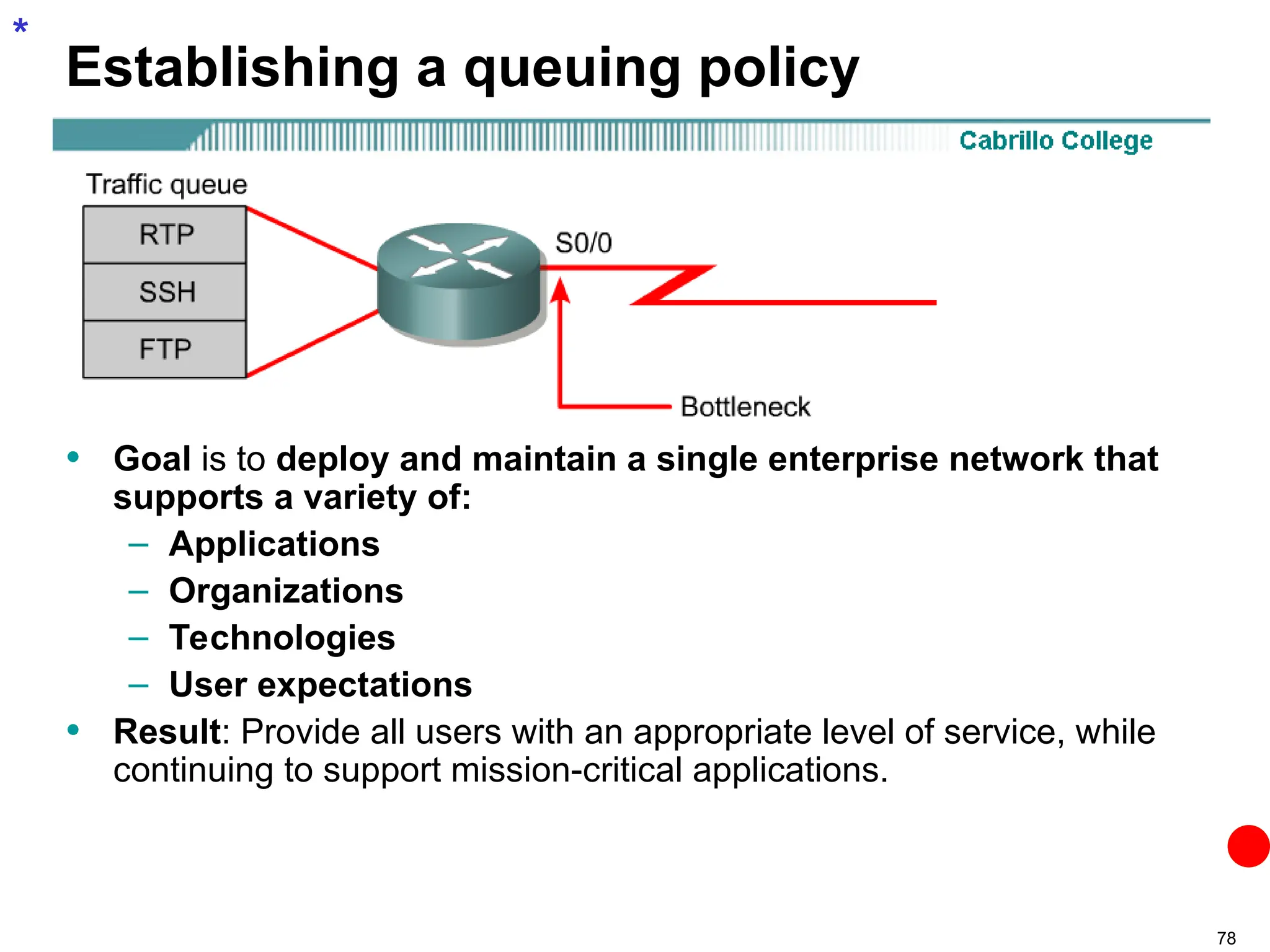
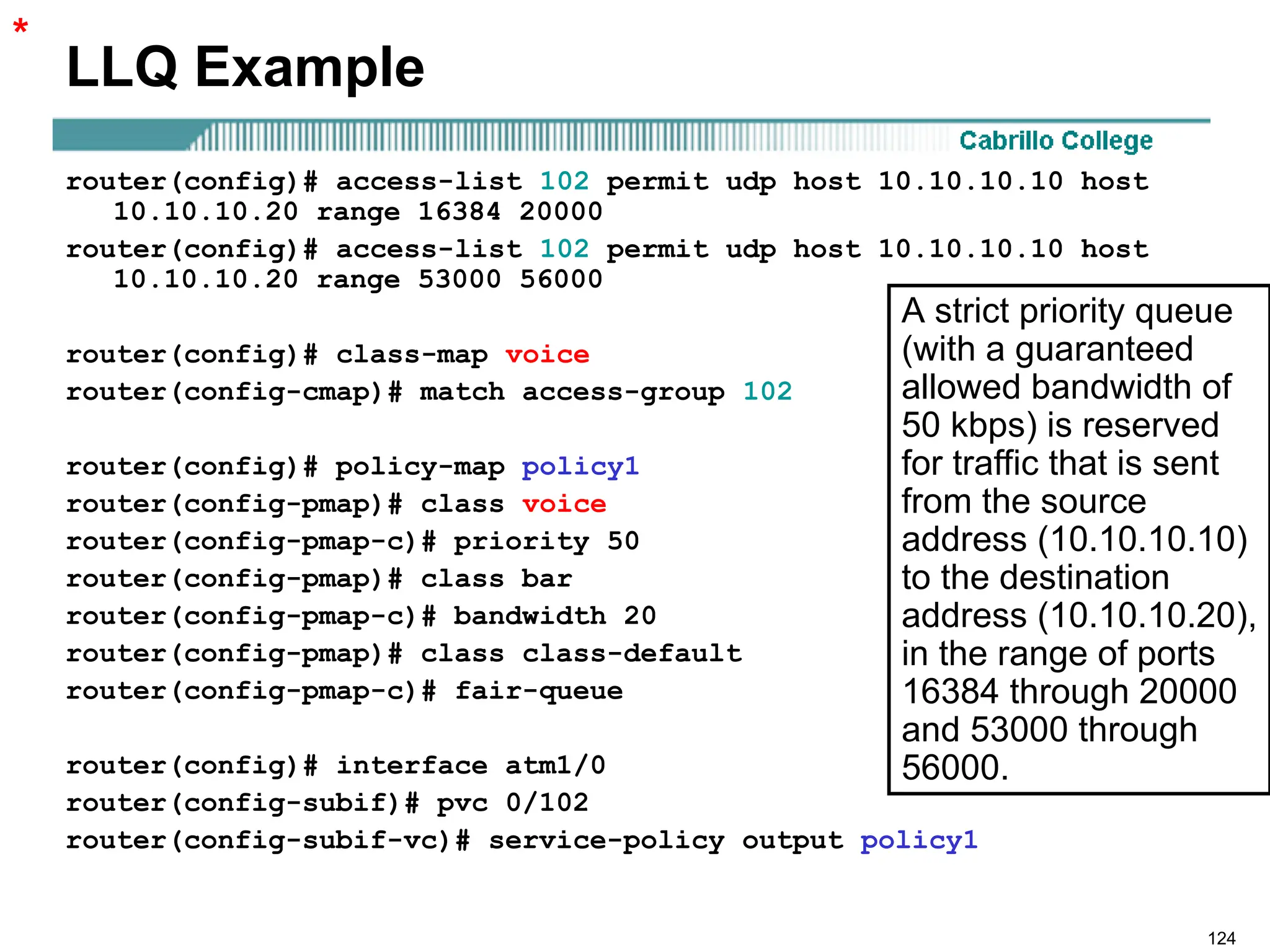
The document outlines Quality of Service (QoS) in multilayer switched networks, emphasizing the integration of voice, video, and data traffic into a single multi-service network. It defines QoS, its impact on network performance, and highlights mechanisms like traffic classification, prioritization, and service models (best-effort, integrated, and differentiated services). Additionally, it discusses specific QoS requirements for data, voice, and video applications, along with classification techniques and the importance of maintaining low packet loss, delay, and jitter.