This document provides information about assembly language and data movement instructions for microprocessors. It discusses conventions for moving data between registers and memory using instructions like MOV, PUSH, and POP. It also covers related topics like the stack organization, segment overrides, logical and arithmetic operations, data types including signed and unsigned integers, and examples of simple assembly language programs. The document is presented as lecture slides with definitions, syntax examples, and illustrations to explain key concepts in assembly language programming for microprocessors.
![1 Assembly Language Microprocessors I 2 Assembly Language Microprocessors I
Data Movement ⎯ Abbreviations
src = source ()מקור
dest = destination ()יעד
acc = accumulator (AL or AX)
8086 Instruction Set PTR = pointer ()מצביע
DWORD = double word (32 bits)
. = concatenation (AX = AH.AL)
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
3 Assembly Language Microprocessors I 4 Assembly Language Microprocessors I
Data Movement ⎯ Conventions Data Movement ⎯ Scope
AX ← BX BYTE PTR[1000]
Copy BX to AX Memory byte at address 1000
REGS[AX] ←⎯⎯⎯⎯⎯ REGS[BX] ⎯ WORD PTR[1000]
16- bits Memory word (2 bytes) at address 1000 and address 1001
AL ← [1000] DWORD PTR[1000]
Copy memory byte at address 1000 to AL Memory dword (4 bytes) at addresses
1000, 1001, 1002, 1003
REGS[AL] ←⎯⎯⎯⎯ MEM[1000]⎯
8- bits AX ← [BX]
AL ← [BX] AX ← WORD PTR[BX]
Copy memory byte at address stored in BX to AL AL ← [BX] and AH ← [BX+1]
REGS[AL] ←8 MEM[ REGS[BX] ]
REGS[AL] ←⎯⎯⎯⎯ MEM[ REGS[BX] ]
⎯ REGS[AH] ←8 MEM[ REGS[BX] + 1 ]
8- bits
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-1-320.jpg)
![5 Assembly Language Microprocessors I 6 Assembly Language Microprocessors I
How are Assembly Instructions Used? Simple Assembly Program
Instructions Instructions written as list
MOV dest, src ; dest ← src MOV DX, 1122 ; DX ← 1122
ADD dest, src ; dest ← dest + src MOV AX, [3344] ; AX ← [DS:3344]
ADD AX, DX ; AX ← AX + DX
MOV BX, 5566 ; BX ← 5566
Program set-up by Operating System
MOV SI, 0008 ; SI ← 0008
1. Load program and data into memory
ADD AX, [BX+SI] ; AX ← AX + [DS:BX+SI]
2. Set CS, DS, SS, ES, IP, SP to program locations
MOV [BX], AX ; [DS:BX] ← AX
3. Set AX = BX = CX = DX = SI = DI = BP = 0
4. Load and run program from CS:IP CPU
Fetches next instruction in list
Decodes fetched instruction
Executes decoded instruction
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
7 Assembly Language Microprocessors I 8 Assembly Language Microprocessors I
MOV Stack Organization
MOV dest, src dest ← src
8086 provides user stack 12
MOV AX, 1234 REGS[AX] ←⎯⎯⎯⎯⎯ 1234 34 Full
16-bits Last In First Out (LIFO) buffer
56 Part
MOV AX, BX REGS[AX] ←⎯⎯⎯⎯⎯ REGS[BX] SS:SP points to top of stack 78 of
16-bits
Last filled location in stack 9A Stack
REGS[AX] ←⎯⎯⎯⎯⎯ MEM[1234] SP → BC
Stack expands down
MOV AX, [1234]
16-bits
REGS[AL] ←⎯⎯⎯⎯⎯ MEM[1234] Fills from higher to lower addresses
8-bits
PUSH src
REGS[AH] ←⎯ ⎯⎯⎯⎯ MEM[1235] copies scr to top of stack Empty
8-bits
Part
SP ← SP - 2
MOV AL, [1234] REGS[AL] ←⎯⎯⎯⎯⎯ MEM[1234] of
8-bits
SS:SP ←⎯⎯⎯ src
16-bits
⎯ Stack
MOV AX, [BX] REGS[AX] ←⎯⎯⎯⎯⎯ MEM[ REGS[BX] ] POP dest
16-bits
moves top of stack to dest SS →
MOV AX, [BX+SI] REGS[AX] ←⎯⎯⎯⎯⎯ MEM[ REGS[BX] + REGS[SI] ]
16-bits dest ←⎯⎯⎯ SS:SP
16-bits
⎯
MOV AX, [BX+SI+1234] REGS[AX] ←⎯⎯⎯⎯⎯ MEM[ REGS[BX] + REGS[SI] + 1234 ] SP ← SP + 2
16-bits
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-2-320.jpg)
![9 Assembly Language Microprocessors I 10 Assembly Language Microprocessors I
PUSH PUSH
DS = 1122 12 DS = 1122 12
34 34
ES = 3344 ES = 3344
56 Full 56
78 Part 78 Full
PUSH DS SP ← SP – 2 9A of PUSH DS SP ← SP – 2 9A Part
[SS:SP] ← DS BC Stack MEM[SS:SP] ← DS BC of
11 11 Stack
SP → 22 22
PUSH ES SP ← SP – 2 33
MEM[SS:SP] ← ES SP → 44
Empty
Part Empty
of Part
Stack of
Stack
SS → SS →
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
11 Assembly Language Microprocessors I 12 Assembly Language Microprocessors I
POP PUSHA / POPA
DS = 1122 12 PUSHA POPA
34 Saves registers to stack Restores registers
ES = 3344
56 Full
Equivalent to executing Equivalent to executing
78 Part
POP CS CS ← [SS:SP] 9A of PUSH AX POP DI
SP ← SP + 2 BC Stack PUSH CX POP SI
11 PUSH DX POP BP
SP → 22 PUSH BX POP SP (value is
CS = 3344
33 discarded)
PUSH SP (value of SP
44
Empty before PUSH AX) POP BX
Part PUSH BP POP DX
of PUSH SI POP CX
Stack
PUSH DI POP AX
SS →
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-3-320.jpg)
![13 Assembly Language Microprocessors I 14 Assembly Language Microprocessors I
Segment Override Bitwise Logical Operations
dest ← not dest
CS: MOV [BP],CX CS:[BP] ← CX NOT dest
NOT 11001111 → 00110000
ES: MOV [BP],CX ES:[BP] ← CX
DS: MOV [BP],CX DS:[BP] ← CX dest ← dest AND src
AND dest, src
10110000 AND 11001111 → 10000000
SS: MOV [BP],CX SS:[BP] ← CX
dest ← dest OR src
OR dest, src
10110000 OR 11001111 → 11111111
dest ← dest XOR src
XOR dest, src
10110000 XOR 11001111 → 01111111
TEST dest, src dest AND src ; update flags
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
15 Assembly Language Microprocessors I 16 Assembly Language Microprocessors I
Using Boolean Operations Unsigned Integers
; AX ← 0 n-bit number is usual binary representation n=3
XOR AX,AX 7 111
Represents value from 0 to 2n-1 6 110
5 101
Integers determined modulo 2n
MOV AX,1122 ; AX ← 1122 4 100
Overflow 3 011
AND AX,00FF ; AX ← 0022 a + b > 2n-1
2 010
1 001
Carry Flag is set 0 000
MOV AX,1122 ; AX ← 1122 CF 3-Bit Integer
TEST AX,8000 ; ZF ← 1 (tests high 0
111
+ 001
order bit) 1 000
CF 3-Bit Integer
MOV AX,0001 ; AX ← 0001 0
000
; AX ← FFFE
- 001
NOT AX 1 111
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-4-320.jpg)
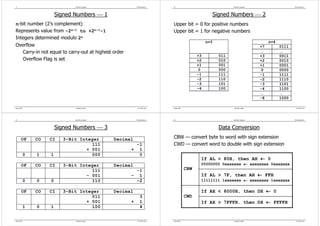
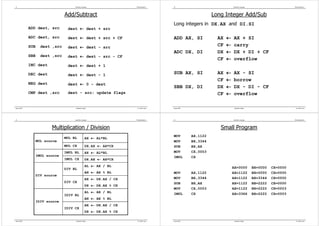
![25 Assembly Language Microprocessors I 26 Assembly Language Microprocessors I
Shift Instructions Rotate Instructions
SHR ROL — Rotate Left
Shift Right
SAR
Shift Arithmetic Right ROR — rotate right
Shift bits right with
sign preservation
RCL — rotate carry left
SAL
Shift Arithmetic Left
Shift left, sign bit to CF
OF = 1 if sign bit changes RCR — rotate carry right
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
27 Assembly Language Microprocessors I 28 Assembly Language Microprocessors I
String Instructions ⎯ 1 String Instructions ⎯ 2
Store ES:[DI] ← AL ES:[DI] ← DS:[SI]
STOSB String If DF = 0, DI ← DI+1 Move If DF = 0, DI ← DI+1
Byte If DF = 1, DI ← DI-1 MOVSB String SI ← SI+1
Store ES:[DI] ← AL; ES:[DI+1] ← AH
Byte If DF = 1, DI ← DI-1
STOSW String If DF = 0, DI ← DI+2 SI ← SI-1
Word If DF = 1, DI ← DI-2 ES:[DI] ← DS:[SI]
ES:[DI+1] ← DS:[SI+1]
Load AL ← DS:[SI] Move
If DF = 0, DI ← DI+2
LODSB String If DF = 0, SI ← SI+1 MOVSW String
SI ← Sl+2
Byte If DF = 1, SI ← SI-1. Word
If DF = 1, DI ← DI-2
Load AL ← DS:[SI]: AH ← DS:[SI+1]
SI ← SI-2
LODSW String If DF = 0, SI ← SI+2; AL-ES:[DI]; update flags
Scan
Word If DF = 1, SI ← SI-2 SCASB String If DF = 0, DI ← DI+1
Byte If DF = 1, DI ← DI-1
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-7-320.jpg)
![29 Assembly Language Microprocessors I 30 Assembly Language Microprocessors I
String Instructions ⎯ 3 String Instructions ⎯ 4
AX-ES:[DI+l:DI];
Scan Update flags STOSB
SCASW String
If DF = 0, DI ← DI+2 REP STOSB CX ← CX - 1
Word
If DF = I, DI ← DI-2 Repeat until CX = 0
DS:[SI]-ES:[DI];
Update flags STOSW
Compare If DF = 0, DI ← DI+I REP STOSW CX ←CX - 1
CMPSB String
SI ← SI+1 Repeat until CX = 0
Byte
If DF = 1 , DI ← DI-1
SI ← SI-1 MOVSB
DS:[SI+I:SI]-ES:[DI+1:DI]; REP MOVSB CX ← CX - 1
Update flags Repeat until CX = 0
Compare If DF = 0, DI ← DI+2
CMPSW String
SI ← SI+2 MOVSW
Word
If DF = 1, DI ← DI-2 REP MOVSW CX ← CX - 1
SI ← SI-2 Repeat until CX = 0
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
31 Assembly Language Microprocessors I 32 Assembly Language Microprocessors I
Working with Strings Branch Instructions
PUSH ES ; SP ← SP – 2 Changes program execution order
branch
; [SS:SP] ← ES Changes default IP to new IP under
fall through
program control
PUSH DS ; SP ← SP – 2 Used to build for, while, if,
short target
; [SS:SP] ← DS switch, … blocks short
jump
POP ES ; ES ← DS Target
New IP after branch is executed near target
; SP ← SP + 2 near
jump
Fall-through
MOV SI,0000 ; SI ← 0 Instruction below branch in program
MOV DI,1000 ; DI ← 1000 listing
MOV CX,200 ; CX ← 200 Default IP points to fall-through far target
far
REP MOVSB ; COPY 200 H BYTES FROM Displacement jump
Displacement = Target IP – Fall-through IP
; DS:0000 – DS:01FF TO
; DS:1000 – DS:11FF Displacement > 0 is forward jump
Displacement < 0 is backward jump
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-8-320.jpg)
![33 Assembly Language Microprocessors I 34 Assembly Language Microprocessors I
Jump Distance Jump Instruction
branch
Displacement = Target IP – Fall-through IP fall through
JMP target ⇒ JMP near target (assembler chooses near or short)
JMP FAR
short target
Near Short short
jump
JMP 1024 IP ←16 1024
Target in same code segment near target
near JMP target JMP NEAR [1024] IP ←16 [1024]
Displacement is byte jump
-12810 = 80 ≤ displacement ≤ 7F = 12710 JMP NEAR [SI] IP ←16 [SI]
CS ←16 1122
Near Jump JMP FAR 1122:3344
far target
far
IP ←16 3344
Target in same code segment jump
CS ←16 [1026]
Displacement is word (2 bytes) JMP far target JMP FAR [1024]
IP ←16 [1024]
-32,76810 = 8000 ≤ displacement ≤ 7FFF = 32,76710 CS ←16 [SI+2]
JMP FAR [SI]
Far Jump IP ←16 [SI]
Target in different code segment
Pointer is double word (4 bytes)
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
35 Assembly Language Microprocessors I 36 Assembly Language Microprocessors I
Conditional Jumps Unsigned Compare ⎯ 1
ALU operations set flags in the status word
COMP ZF CF
Conditional jumps test the flags and jump if flag is set A < B 0 1
Takes short target A = B 1 0
A > B 0 0
Mnemonic Condition Test
JC Carry CF = 1
JE/JZ Equal/zero ZF = 1 A < B ⇒ CF =1
JP/JPE Parity / parity even PF = 1 A ≤ B ⇒ (ZF XOR CF) = 1
JNC Not carry CF = 0 A = B ⇒ ZF = 1
JNE/JNZ Not equal/not zero ZF = 0 A ≥ B ⇒ CF = 0
JNP/JPO Not Parity / parity odd PF = 0
A > B ⇒ (ZF XOR CF) = 0
(ZF = CF = 1 is impossible)
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-9-320.jpg)

![41 Assembly Language Microprocessors I 42 Assembly Language Microprocessors I
Call and Return Indirect Far Call
stack stack
CALL near target SP ← SP-2; [SP] ← IP; IP ← target SP
CALL 1024 SP ← SP-2; [SP] ← IP; IP ← 1024 fall-through CS
fall-through IP
CALL [SI] SP ← SP-2; [SP] ← IP; IP ← [SI] SP
CALL far target SP ← SP-2; [SP] ← CS; CS ← SEG;
SP ← SP-2; [SP] ← IP; IP ← OFF
CALL 1122:3344 SP ← SP-2; [SP] ← CS; CS ← 1122 IP = 1122
SP ← SP-2; [SP] ← IP; IP ← 3344 CS = 3344
CALL [SI] SP ← SP-2; [SP] ← CS; CS ← [SI+2]
SP ← SP-2; [SP] ← IP; IP ← [SI]
RET IP ← [SP]; SP ← SP+2
IP fall-through fall-through
RETF IP ← [SP]; SP ← SP+2; CALL [SI] CALL [SI]
CS
CS ← [SP]; SP ← SP+2 44 44
33 33
22 22
SI 11 SI 11
DS DS
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
43 Assembly Language Microprocessors I 44 Assembly Language Microprocessors I
Software Interrupt (Trap) Software Interrupt Instructions
Interrupts Program Flow INT type INT 20H SP ← SP-2; [SP] ← flags
Transfers control to Interrupt Service Routine (ISR) IF ← 0; TF ← 0;
ISR can be stored anywhere in memory SP ← SP-2; [SP] ← CS;
CS ← [00083H:00082H];
Pointer to ISR stored in Interrupt Vector Table Table SP ← SP-2; [SP] ← IP;
starts at 00000 IP ← [00081H:00080H]
Each Vector is 4 bytes long (2×CS+2×IP) IRET none IRET IP ← [SP];
Vector 0 is at physical address 00000 SP ← SP+2;
Vector 1 is at physical address 00004 CS ← [SP];
SP ←
Vector 2 is at physical address 00008 SP+2;
flags ← [SP];
ISR vector address is: INT_type×4 SP ← SP+2
Vector is: IP(L), IP(H), CS(L), CS(H)
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-11-320.jpg)
![45 Assembly Language Microprocessors I 46 Assembly Language Microprocessors I
Interrupt Hardware Interrupts
stack stack
INTR line on chip causes interrupt
SP
flags INT_type is on address lines A0 to A7
NMI line on chip causes non-maskable interrupt
fall-through CS
SP fall-through IP
Cannot be masked (turned off)
Always points to INT type 4
IP = 1122
A7
CS = 3344 A6
A5
A4 8086
A3 CPU
A2
IP fall-through fall-through A1
INT 21 INT 21 A0
CS
44 44
33 33 INTR
22 22
00084 11 00084 11 NMI
00000 00000
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
47 Assembly Language Microprocessors I 48 Assembly Language Microprocessors I
Processor Control Instructions More Data Movement Instructions
STC CF ← I Set carry flag XCHG dest, src dest ↔ src
CLC CF ← 0 Clear carry flag XCHG AX, BX AX ↔ BX
CMC CF ← not(CF) Complement carry flag XCHG AL, AH AL ↔ AH
STD DF ← 1 Set direction flag XCHG AX, [SI] AX ↔ [SI]
CLD DF ← 0 Clear direction flag
STI IF ← I Set interrupt flag LAHF AH ←⎯⎯⎯ flags (low byte)
8-bits
CLI IF ← 0 Clear interrupt flag SAHF flags (low byte) ←⎯⎯⎯ AH
8-bits
HLT None Halt
WAIT None Enter wait state
NOP None No operation
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-12-320.jpg)
![49 Assembly Language Microprocessors I 50 Assembly Language Microprocessors I
Translate — XLAT LEA
Replaces AL with (AL+1)st value in a table Load Effective Address
Uses AL as index into 256 byte table beginning at [BX] Similar to MOV
Copies address (pointer) of memory location
XLAT AL ← [BX+AL]
Does not access memory
MOV AL, 3 A3
XLAT 77
66
LEA dest, [EA] dest ←⎯⎯⎯ EA
16-bits
⎯
AL ← [BX+3] = 33 55
44
LEA AX, [1234] AX ←⎯⎯⎯ 1234
⎯
BX+AL → 33 16-bits
22 REGS[AX] ←⎯⎯⎯ 1234
16-bits
⎯
11
LEA CX, [SI+12] CX ←⎯⎯⎯ SI+12
⎯
BX → 00 16-bits
97 REGS[CX] ←⎯⎯⎯ REGS[SI]+12
16-bits
⎯
54 LEA DX, [BX + DI] DX ←⎯⎯⎯ BX + DI
⎯
34 16-bits
DS REGS[DX] ←⎯⎯⎯ REGS[BX]+ REGS[DI]
16-bits
⎯
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
51 Assembly Language Microprocessors I 52 Assembly Language Microprocessors I
Moving Data Around LDS and LES
MOV SI,1122 ; SI ← 1122 Loads a 32-bit logical address of type DS:EA or ES:EA
MOV [0000],SI ; [DS:0000] ← 1122
MOV BX,3344 ; BX ← 3344 LDS dest, [EA] dest ←⎯⎯⎯ [EA]
16-bits
⎯
MOV [BX],SI ; [DS:3344] ← 1122 DS ←⎯⎯⎯ [EA + 2]
16-bits
⎯
MOV [BX+SI],BX ; [DS:4466] ← 3344 11
BX ←⎯⎯⎯ [SI]
⎯ 22
LEA BX,[BX+SI] ; BX ← 4466 LDS BX, [SI] 16-bits 33
DS ← 3344
MOV CS,[BX] ; CS ← [DS:4466] DS ←⎯⎯⎯ [SI+ 2]
16-bits
⎯ 44
55
MOV AX,[BX+2] ; AX ← [DS:4468] SI → 66
BX ← 5566
77
88
99
AA
LES dest, [EA] dest ←⎯⎯⎯ [EA]
16-bits
⎯ DS
ES ←⎯⎯⎯ [EA + 2]
16-bits
⎯
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-13-320.jpg)
![53 Assembly Language Microprocessors I 54 Assembly Language Microprocessors I
Switching Data Tables Data Movement ⎯ I/O Operations ⎯ 1
/* DO ARITHMETIC WITH DS:BX = 1111:2222 */
80x86 processors control an I/O signal on the memory bus
/* SWITCH DATA TABLES */
MOV [SI], 4444 ; [SI] ← 4444 I/O signal is off to select processor access to RAM
; [SI+2] ← 3333
MOV [SI+2], 3333
I/O signal is on to select processor access to I/O bus
PUSH DS ; SP ← SP – 2
; [SS:SP] ← 1111 MOV selects RAM access
PUSH BX ; SP ← SP – 2 IN and OUT select I/O access
; [SS:SP] ← 2222
LDS BX,[SI] ; BX ← 4444
; DS ← 3333 AL or AX are always src/dest for I/O instructions
/* DO ARITHMETIC WITH DS:BX = 3333:4444 */
/* SWITCH BACK TO FIRST DATA TABLE */ I/O address is called a port
POP [SI] ; [SI] ← 2222 can range from 0000 H to FFFF H
; SP ← SP + 2
POP [SI+2] ; [SI+2] ← 1111 direct mode ⎯ 1 immediate byte address
; SP ← SP + 2 indirect mode ⎯ 2 address bytes in DX
LDS BX,[SI] ; BX ← 2222
; DS ← 1111
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land
55 Assembly Language Microprocessors I 56 Assembly Language Microprocessors I
Data Movement ⎯ I/O Operations ⎯ 2 Data Movement ⎯ I/O Instructions ⎯ 3
Memory Bus אפיק זיכרון
IN AL,26H AL ← port 26H
input byte from
AL ← port 26H;
זיכרון IN AX,26H port 0 ⎯ 255
מטמון זיכרון ראשי AH ← port 27H
מתאם IN acc, port
cache memory IN AL,DX AL ← port DX input byte from
אפיק
Data/Address
Main Memory
Bus AL ← port DX port 0 ⎯ 65,535
I/O (RAM) IN AX,DX
Adapter AH ← port DX+1 (address in DX)
יהידת החישוב
המרכזי output byte to
port DX ← AL
Central Processing I/O Bus אפיק קלט/פלט OUT port, acc OUT DX,AX port 0 ⎯ 65,535
Unit (CPU) port DX+1 ← AH (address in DX)
בקר קלט/פלט בקר קלט/פלט בקר קלט/פלט
I/O Controller I/O Controller I/O Controller
Disk ממשק רשת תקשורת
משתמש communications
network
Spring 2009 Hadassah College Dr. Martin Land Spring 2009 Hadassah College Dr. Martin Land](https://image.slidesharecdn.com/slide03-100722114557-phpapp02/85/instruction-set-of-8086-14-320.jpg)