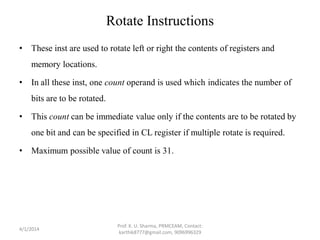
The document discusses assembly language programming concepts including shift, rotate, flag control, compare, and jump instructions. It provides examples and problems to explain the usage and effects of various instructions. Key points include:
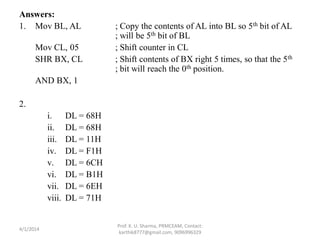
- Shift instructions move bits within a register or memory location based on a count. Common instructions are SHR, SAR, SHL, ROL, ROR.
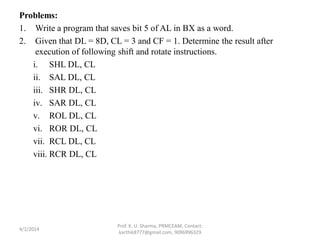
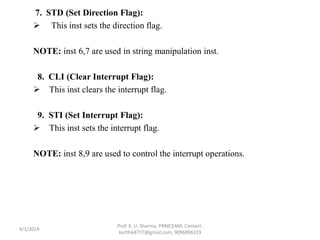
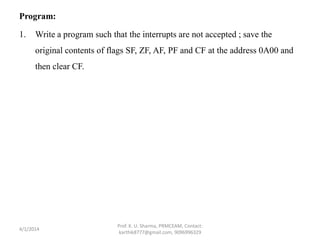
- Flag control instructions modify status flags. Common ones are LAHF, SAHF, CLC, STC.
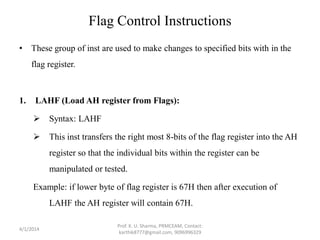
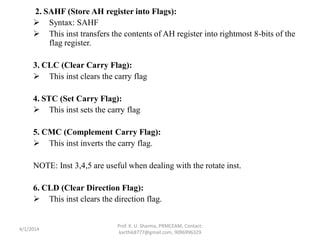
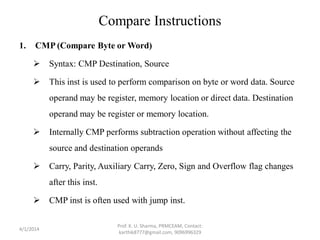
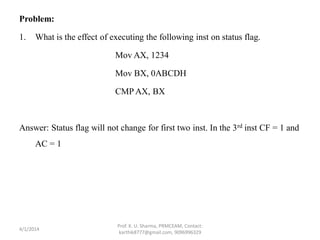
- Compare instruction CMP performs subtraction without affecting operands and updates flags.
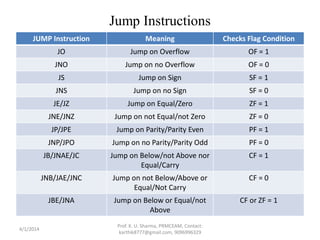
- Jump instructions conditionally transfer control based on status flag values like JO, JB, JE, JL.
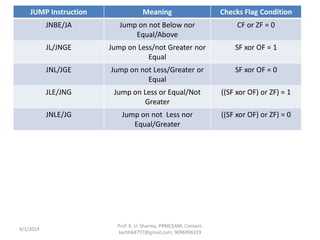
Pro



![Answer:
CLI ; Disable Interrupt
Mov AX, DATA_SEG ; Establish Data Seg.
Mov DS, AX ;
Mov BX, 0A00 ; Establish Destination
LAHF ; Get Flags
Mov [BX], AH ; and save at 00A0
CLC ; Clear CF
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-22-320.jpg)
![Answers:
1. Mov Al, N ; load the number in Al
Mov Bl, Al ; copy the into Bl
LABEL: DEC Bl ; decrement Bl by 1
JZ ABC ;
MUL BL
JMP LABEL ;
ABC: Mov [FACT], Al ; Result stored in FACT
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-28-320.jpg)
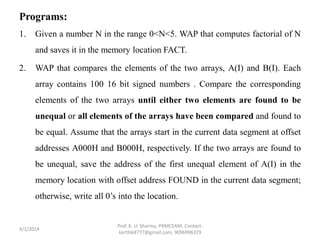
![2. Mov AX, Data_Seg ;
Mov DS, AX ; Setting the Segment
Mov CX, 64H ; Setting up the array counter
Mov SI, 0A000H ; Source Array Pointer
Mov DI, 0B000H ; Destination Array Pointer
A: Mov AX, [SI];
CMPAX, [DI] ; Compare the Array Pointers
JNE B ; jump if not equal
ADD SI, 2 ;
ADD DI, 2 ; Updating the pointers
DEC CX ;
JNZ A ; jump till CX = 0
Mov [FOUND], 0H ; if the arrays are equal
JMP C ;
B: Mov [FOUND], SI ; If unequal saving the address of first unequal
element in A(I)
C: Hlt
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-29-320.jpg)
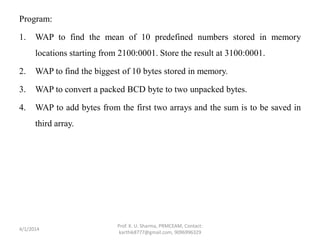
![Answer:
Mov CX, 64H ; Setting up the counter
Mov AX, Data_Seg ;
Mov DS, AX ; Setting the data segment
Mov BX, 0A000H ; pointer to the given array
Mov SI, 0B000H ; pointer to positive array
Mov DI, 0C000H ; pointer to negative array
XYZ: Mov AX, [BX] ; getting the next source element
CMP AX, 0H ; skip if positive
JGE POS ;
NEG: Mov [DI], AX ; else placing it in negative array
ADD DI, 2 ;
JMP ABC ; skip
POS: Mov [SI], AX ; place in the positive array
ADD SI, 2
ABC: ADD BX, 2
LOOP XYZ ; repeating for all elements
Hlt
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-33-320.jpg)

![Mov AX, DATASEGADDR ; Setting Data segment
Mov DS, AX ;
Mov CX, N ; setting the counter
Mov SI, BLK1ADDR ; pointer to BLK1ADDR
Mov DI, BLK2ADDR ; pointer to BLK2ADDR
ABC: Mov AL, [SI] ; Loading data in AL
Mov [DI], AL ; mov data to BLK1ADDR
INC SI ; point to the next data
INC DI
LOOP ABC ; Looping for all data
HLT
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-36-320.jpg)
![Answers:
1. Mov AX, 2100 ;
Mov DS, AX ; Setting the data segment
Mov SI, 0001 ; Initializing array address
Mov CX, 000A ; Setting up the counter
Mov AX, 0000 ; Initial Sum = 0
AGAIN: ADD AL, [SI]
JNC ABC
INC AH
ABC: INC SI
LOOP AGAIN
Mov BL, 0A ; Setting up the divisor
DIV BL
Mov DX, 3100 ;
Mov DS, DX ; Setting DS for result
Mov [0001], AL ; quotient of mean
Mov [0002], AH ; remainder of mean
Hlt
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-38-320.jpg)
![Answers:
4. Let the three arrays be ARRAY1, ARRAY2 and ARRAY3 and let there are N
elements in ARRAY1 and ARRAY2 .
Mov AX, DATA_SEG ;
Mov DS, AX ; Setting data segment
Mov CL, N ; setting counter
LEA SI, ARRAY1 ; offset of array1
LEA DI, ARRAY2 ; offset of array2
LEA BX, ARRAY3 ; offset of array3
ABC: Mov AL, [SI] ; load first byte
Mov BL, [DI] ; load second byte
ADD AL, BL
Mov [BX], AL ; result in array3
INC SI ;
INC BX ;
LOOP ABC ;
HLT
4/1/2014
Prof. K. U. Sharma, PRMCEAM, Contact:
karthik8777@gmail.com, 9096996329](https://image.slidesharecdn.com/unit3assemblylanguageprogramming-140408232650-phpapp02/85/Unit-3-assembly-language-programming-40-320.jpg)