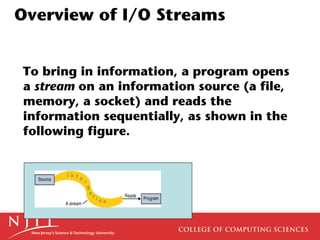
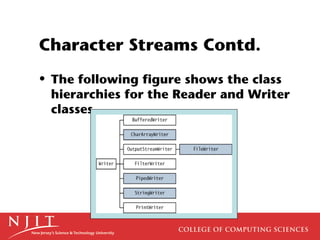
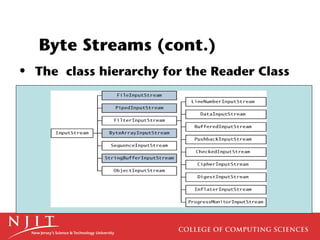
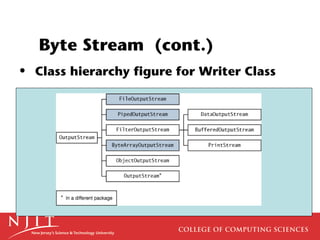
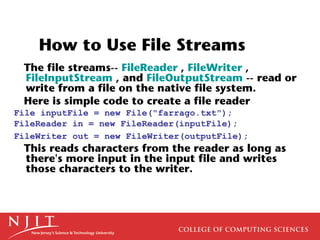
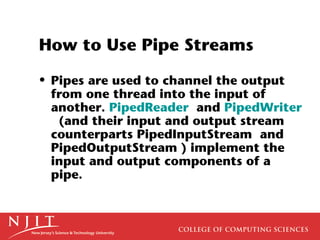
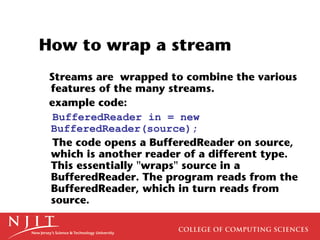
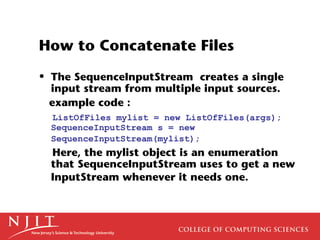
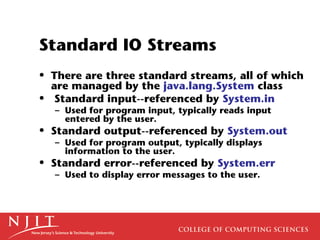
This document provides an overview of input/output (I/O) streams in Java, including character streams, byte streams, file streams, pipe streams, filter streams, object serialization, and random access files. It also discusses the standard input, output, and error streams in Java and how to read from and write to these streams.