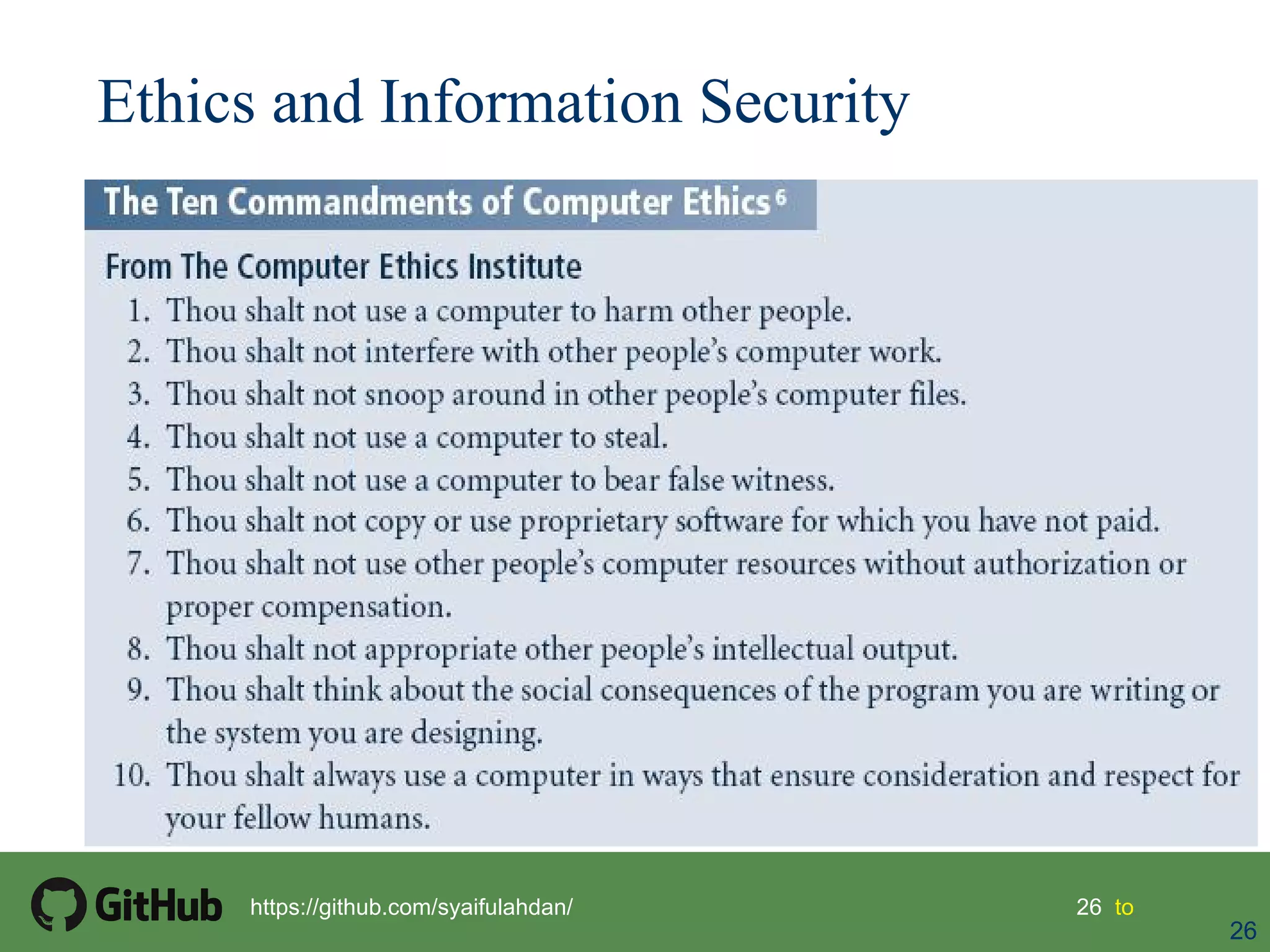
This document provides an overview of key concepts regarding law and ethics in information security. It discusses the differences between laws and ethics, and how policies function similarly to laws within an organization. Several major US laws are outlined, including those covering general computer crimes, privacy, identity theft, export and espionage, copyright, and financial reporting. International agreements and professional organizations relevant to information security ethics are also mentioned. The document aims to help readers understand the legal and ethical responsibilities for information security practitioners.