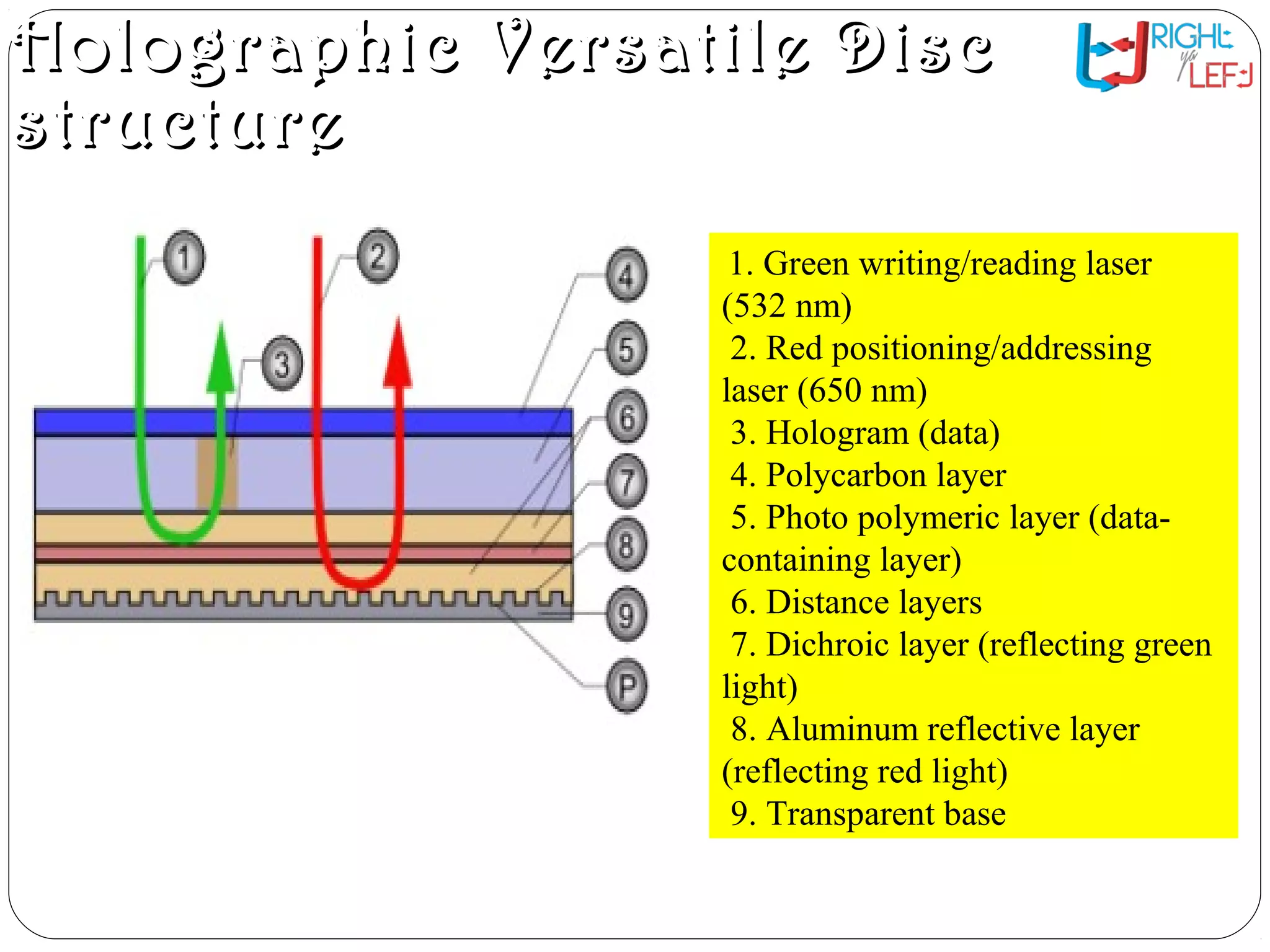
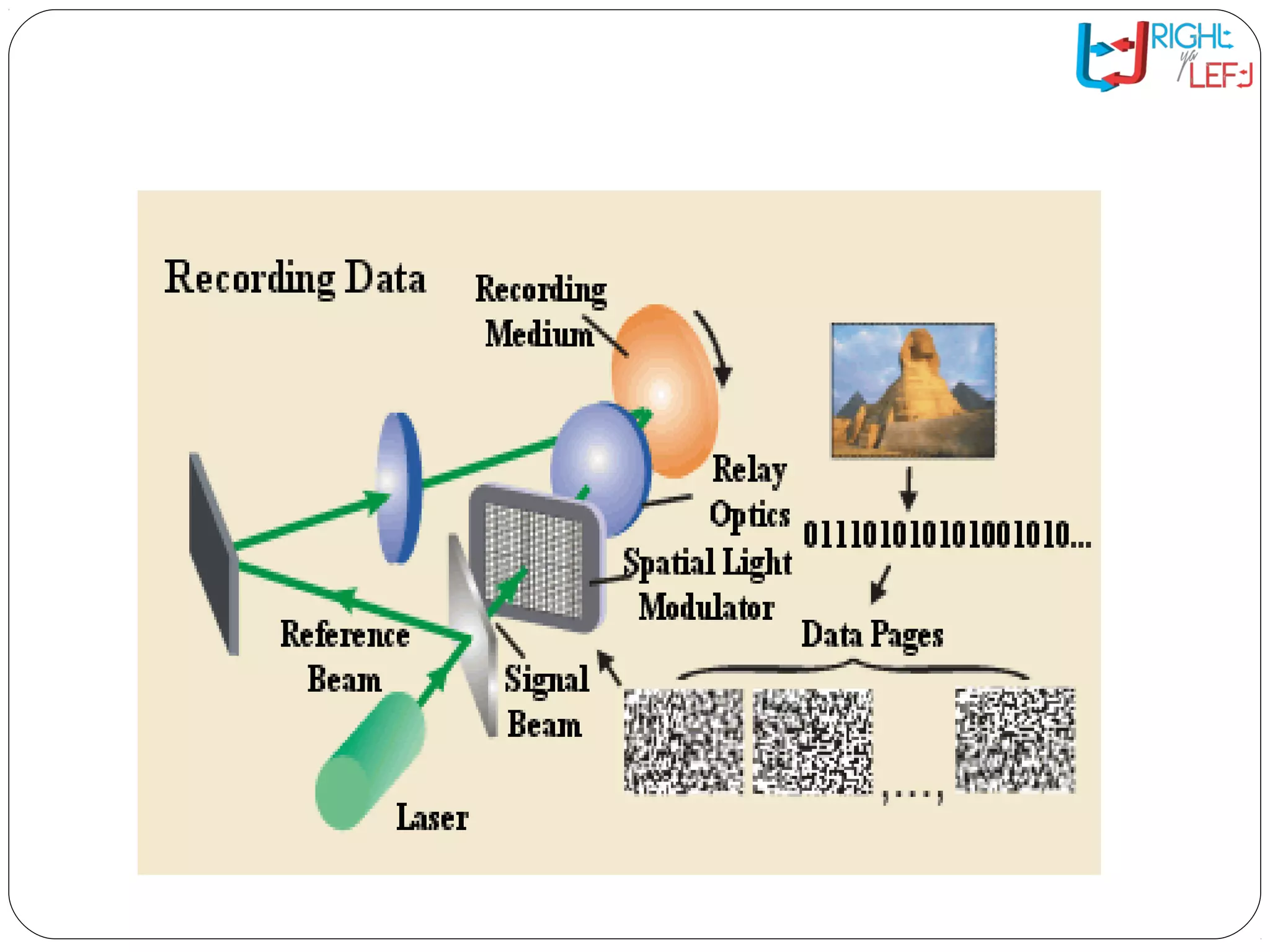
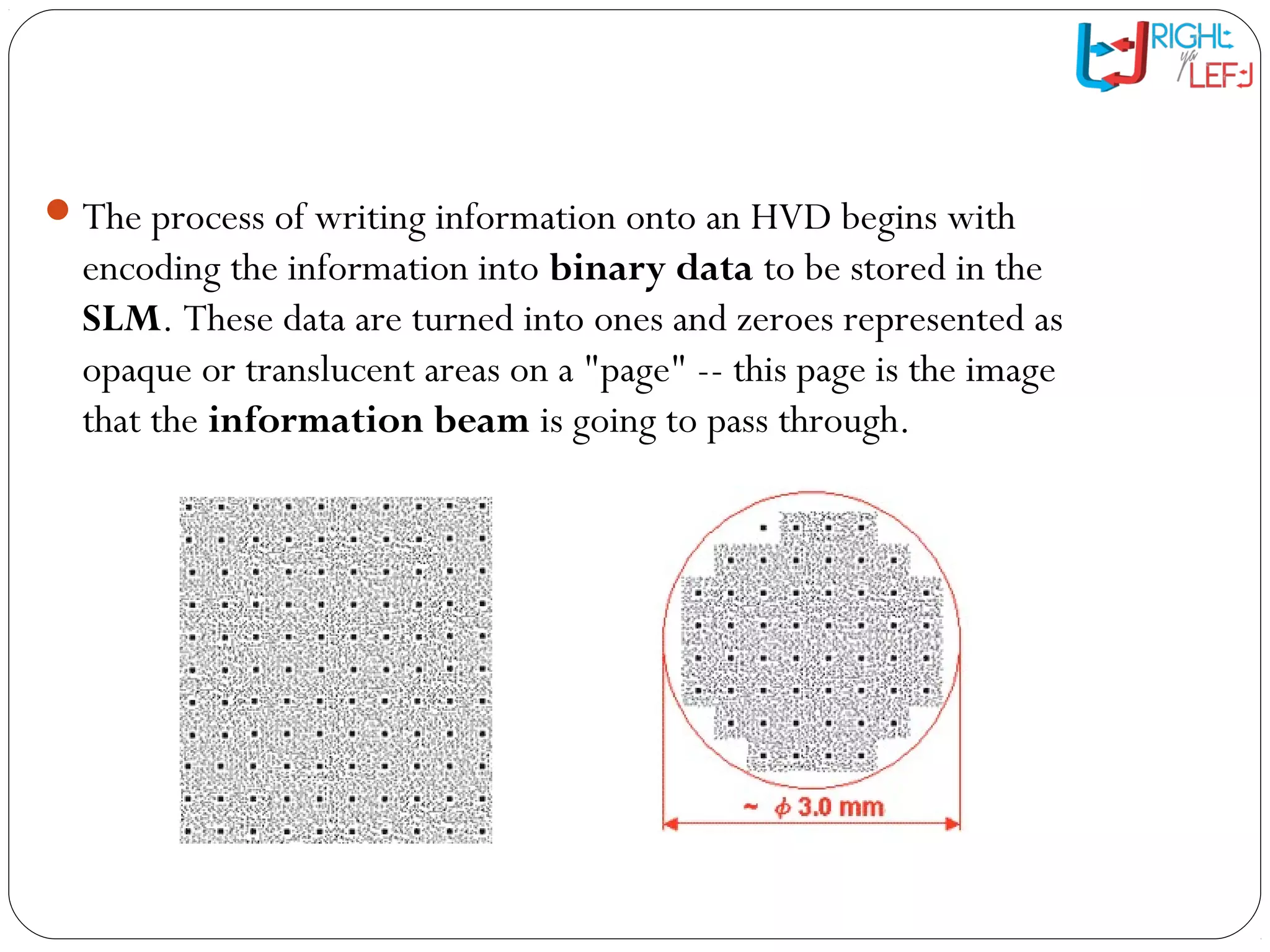
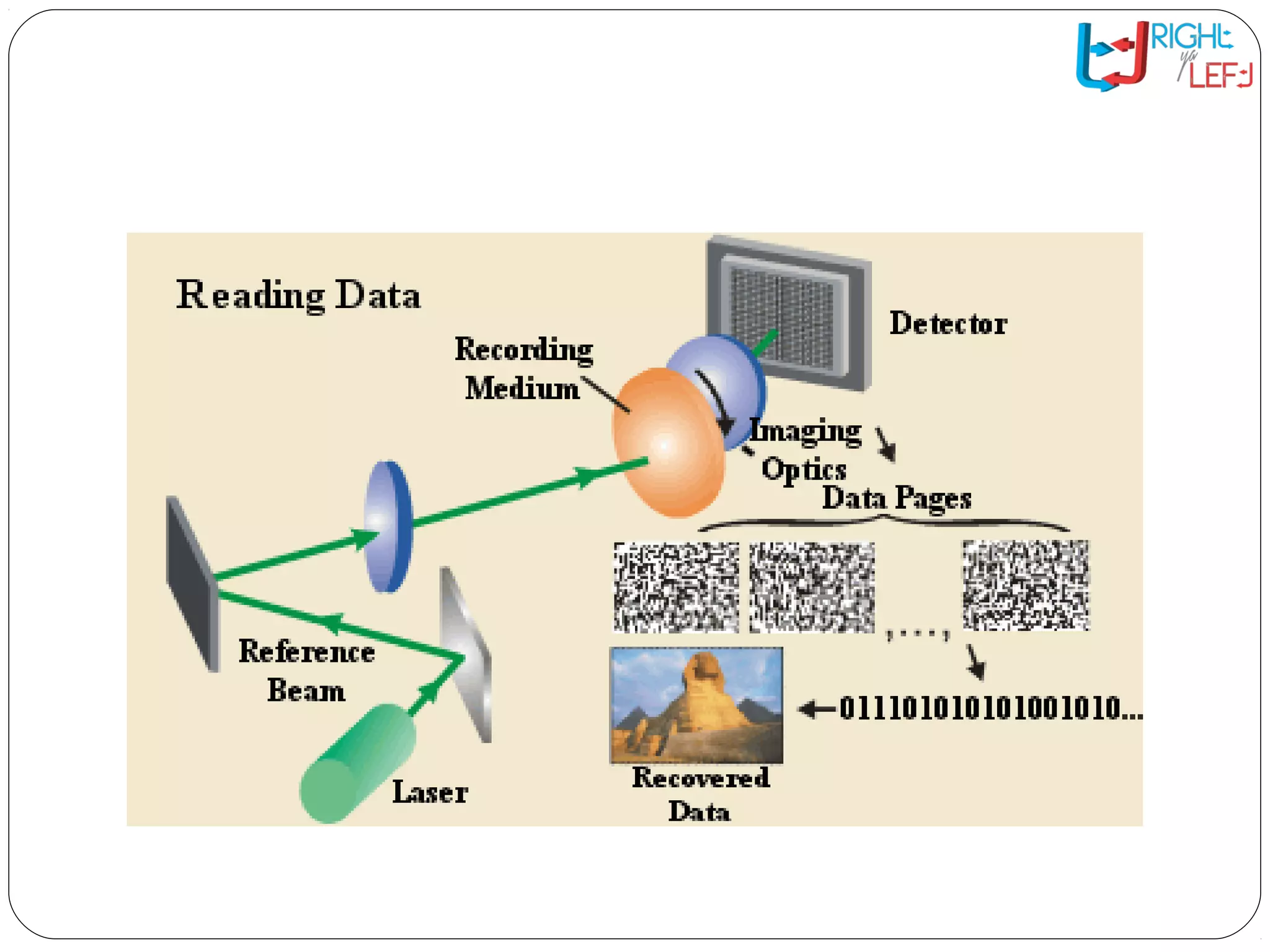
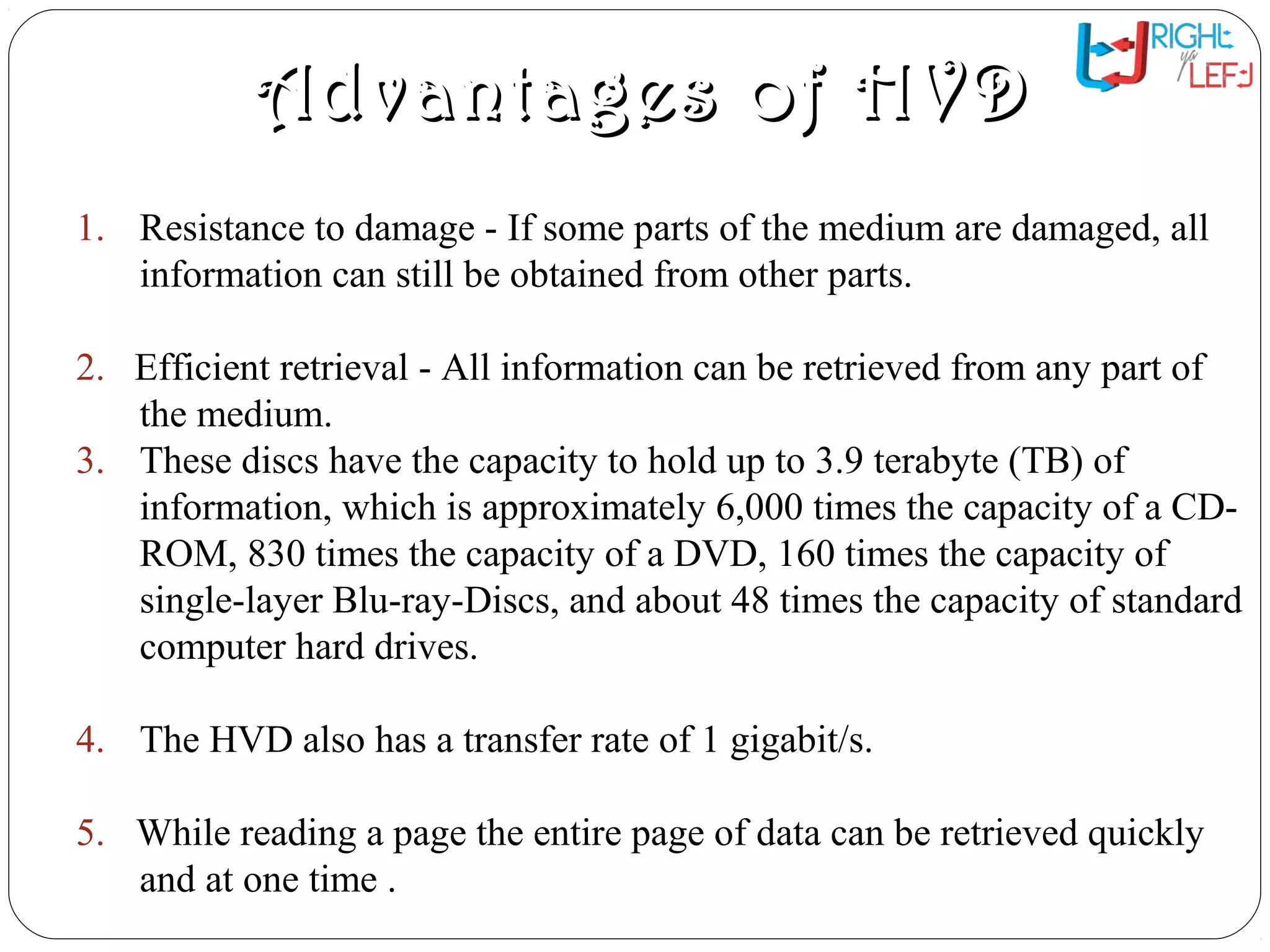
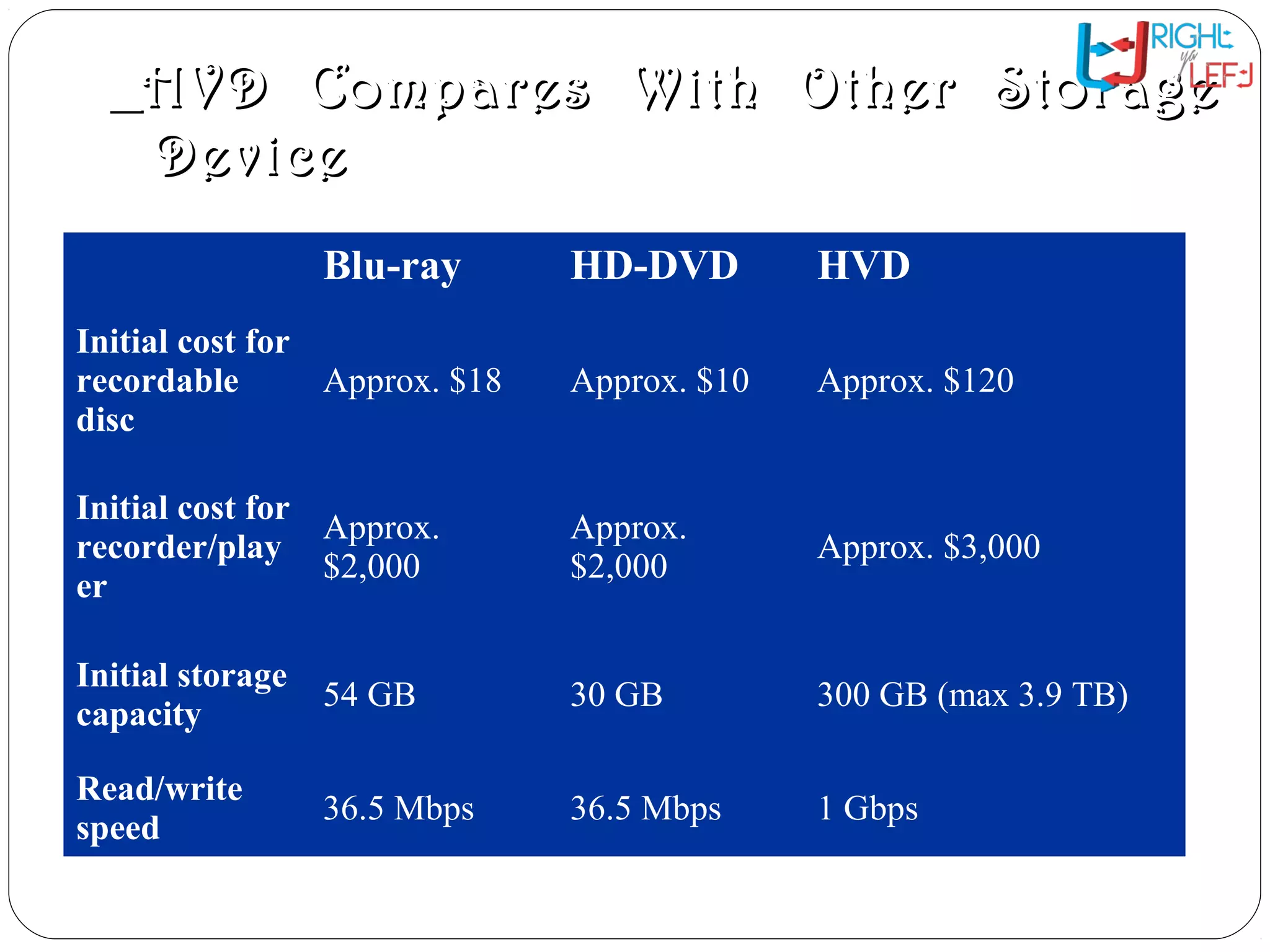
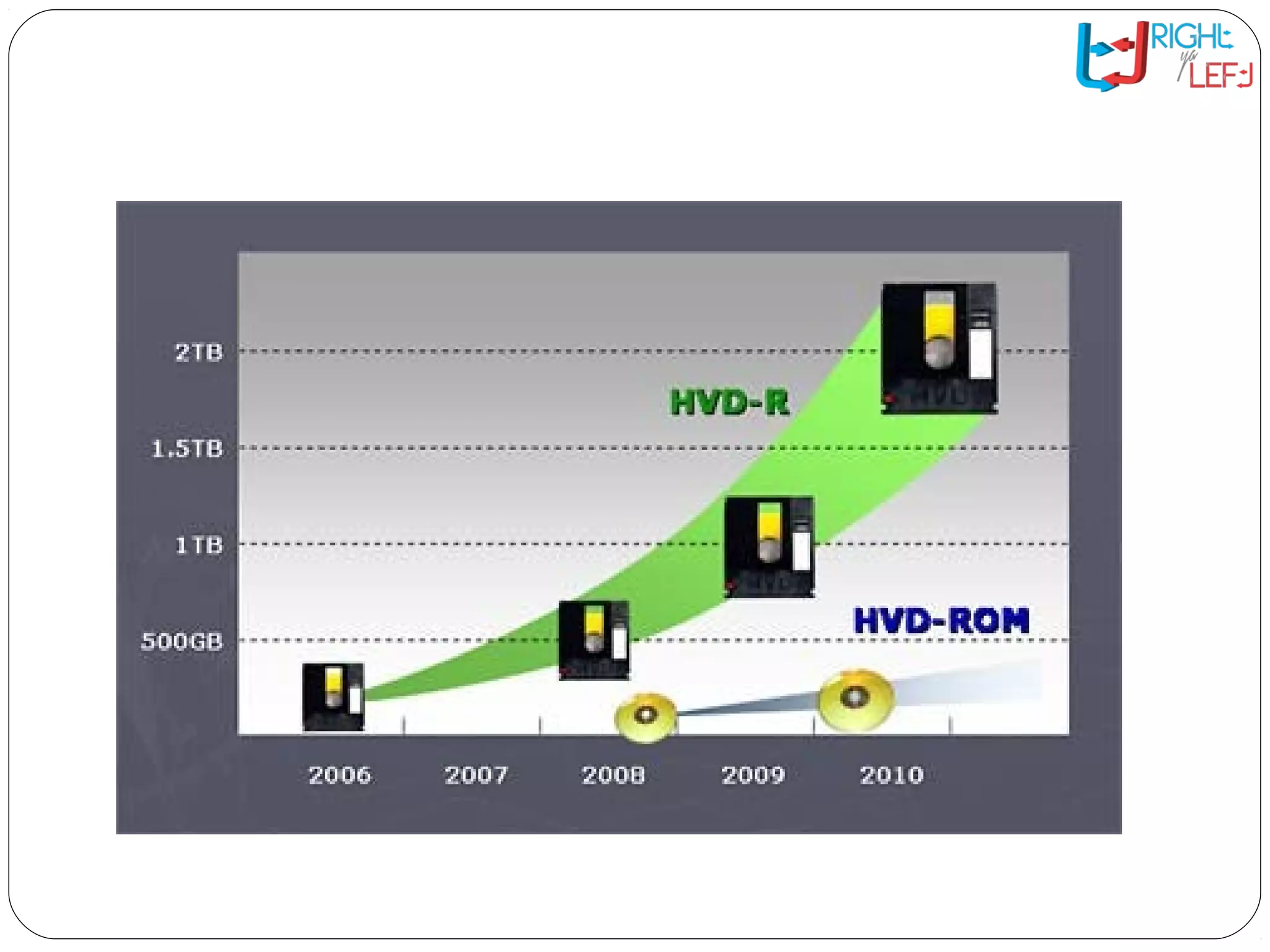
Holographic memory is an advanced three-dimensional data storage system capable of high-density information storage in crystals or photopolymers, making it a potential successor to traditional storage methods. The Holographic Versatile Disc (HVD) technology, currently in research, can store up to 3.9 terabytes of data with a transfer rate of 1 gigabyte per second, vastly outperforming existing media like CDs, DVDs, and Blu-rays. Its advantages include high capacity, efficient retrieval, and resilience to damage, positioning it as a significant advancement in data storage solutions.