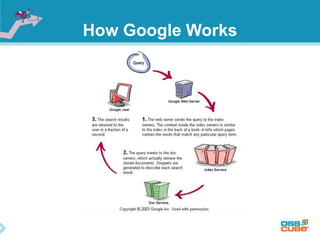
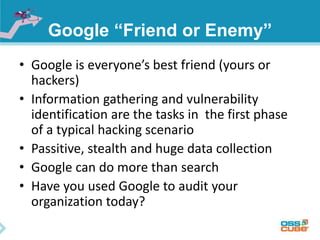
Google dorks, also known as Google hacking, involves using specific search operators and techniques on Google to find sensitive information on websites. Some key points made in the document include:
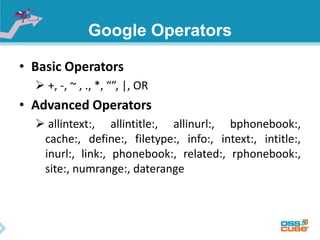
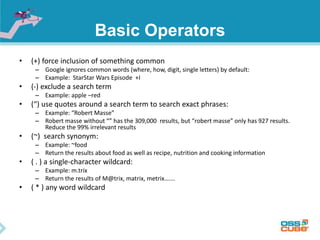
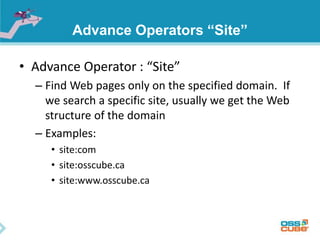
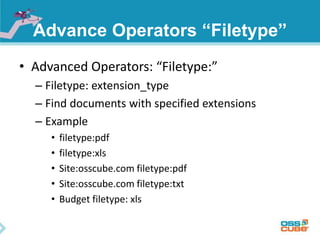
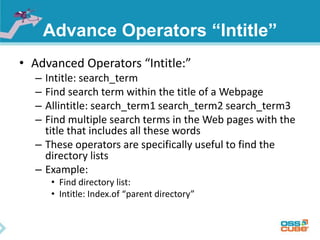
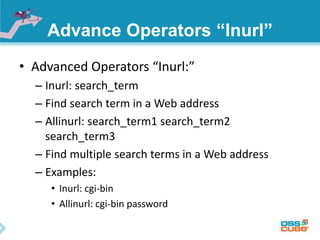
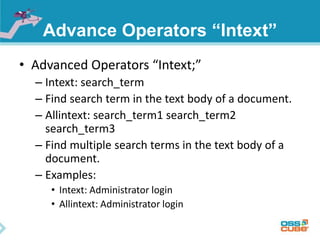
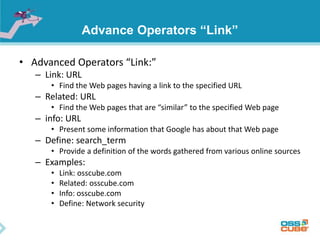
- Google dorking uses operators like "site:", "filetype:", "intitle:", and "inurl:" to refine search results and maximize search value. This can be used to uncover private information, configurations, backups, and vulnerabilities.
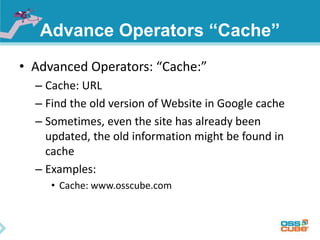
- Information found through Google hacking may remain exposed in Google's cache for months after being removed from websites.
- Google indexes everything publicly available on the internet, making it a powerful tool for passive information gathering, which is an important first step for hackers.
- The document encourages
![August 21,2014
Kaushal Kishore [ kaushal@osscube.com ]
Lead Engineer OSSCube
Google Dorks
(Google Hacking)](https://image.slidesharecdn.com/googledorks-140822060647-phpapp01/75/Google-Dorks-1-2048.jpg)