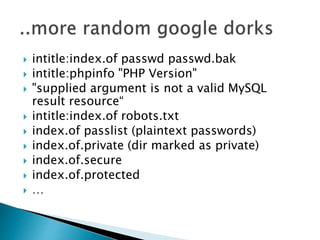
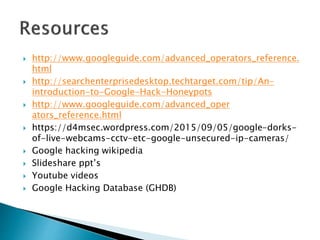
The document discusses Google searching techniques, focusing on how Google indexes the web using spiders and how users can manipulate search results with basic and advanced operators. It highlights methods for finding security vulnerabilities on poorly constructed web applications and offers examples of combined search queries to enhance results. Additionally, it introduces the concept of a Google hack honeypot, which is designed to trap would-be hackers by redirecting them to a logging script rather than exposing sensitive backend data.