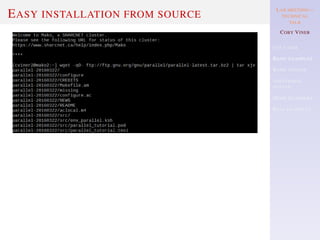
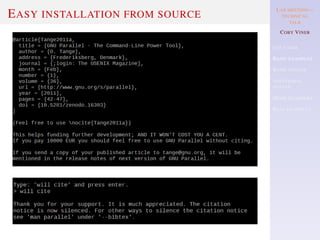
Coby Viner gave a technical talk at a lab meeting about GNU Parallel, a tool for executing jobs in parallel using one or more computers. Viner covered why GNU Parallel is useful, basic examples from its tutorial on syntax and usage, additional syntax for more complex tasks, and real examples of how they have used it. The talk provided an overview and introduction to GNU Parallel for parallelizing tasks, with a focus on explaining its syntax and capabilities through examples.
![LAB MEETING—
TECHNICAL
TALK
COBY VINER
USE CASES
BASIC EXAMPLES
BASIC SYNTAX
ADDITIONAL
SYNTAX
MORE EXAMPLES
REAL EXAMPLES
OVERVIEW
WHY USE GNU PARALLEL?
BASIC EXAMPLES FROM THE TUTORIAL
BASIC ELEMENTS OF SYNTAX [FROM THE TUTORIAL]
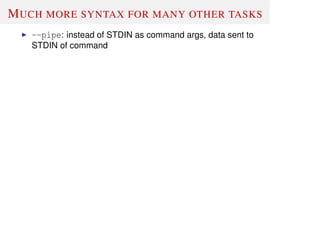
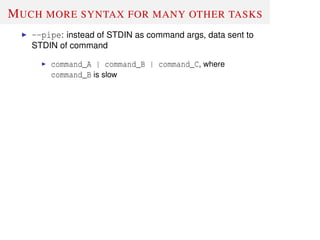
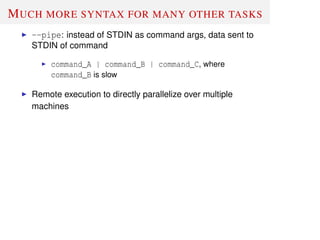
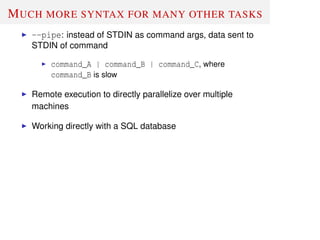
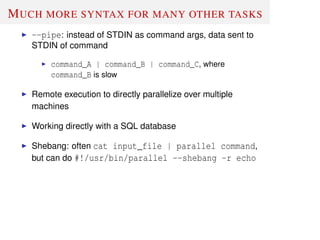
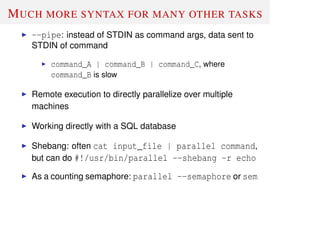
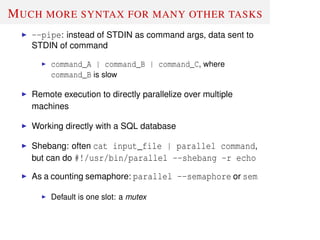
MUCH MORE SYNTAX FOR MANY OTHER TASKS
MORE TUTORIAL EXAMPLES
SOME EXAMPLES OF MY GNU PARALLEL USAGE](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-2-320.jpg)
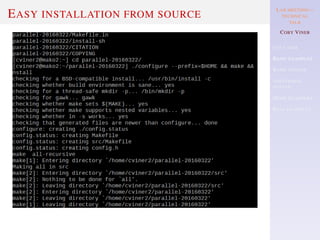
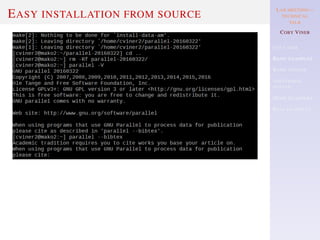
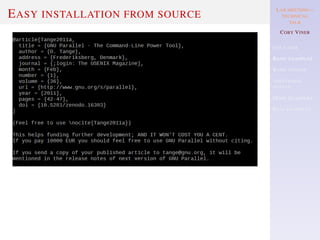
![A BASIC [MAN PAGE] EXAMPLE: “WORKING
AS XARGS -N1. ARGUMENT APPENDING”
find . -name '*.html' | parallel gzip --best](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-10-320.jpg)
![A BASIC [MAN PAGE] EXAMPLE: “WORKING
AS XARGS -N1. ARGUMENT APPENDING”
find . -name '*.html' | parallel gzip --best
find . -type f -print0 |
parallel -q0 perl -i -pe 's/FOO BAR/FUBAR/g'](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-11-320.jpg)
![ANOTHER BASIC [MAN PAGE] EXAMPLE:
“INSERTING MULTIPLE ARGUMENTS”
bash: /bin/mv: Argument list too long
ls | grep -E '.log$' | parallel mv {} destdir](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-17-320.jpg)
![ANOTHER BASIC [MAN PAGE] EXAMPLE:
“INSERTING MULTIPLE ARGUMENTS”
bash: /bin/mv: Argument list too long
ls | grep -E '.log$' | parallel mv {} destdir
ls | grep -E '.log$' | parallel -m mv {} destdir](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-18-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Input:
parallel echo ::: A B C # command line
cat abc-file | parallel echo # from STDIN
parallel -a abc-file echo # from a file](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-19-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Input:
parallel echo ::: A B C # command line
cat abc-file | parallel echo # from STDIN
parallel -a abc-file echo # from a file
Output [line order may vary]:
A
B
C](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-20-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Multiple inputs.
Input:
parallel echo ::: A B C ::: D E F
cat abc-file | parallel -a - -a def-file echo
parallel -a abc-file -a def-file echo
cat abc-file | parallel echo :::: - def-file # alt. file
parallel echo ::: A B C :::: def-file # mix cmd. and file](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-21-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Multiple inputs.
Input:
parallel echo ::: A B C ::: D E F
cat abc-file | parallel -a - -a def-file echo
parallel -a abc-file -a def-file echo
cat abc-file | parallel echo :::: - def-file # alt. file
parallel echo ::: A B C :::: def-file # mix cmd. and file
Output [line order may vary]:
A D
A E
A F
B D
B E
B F
C D
C E
C F](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-22-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Matching input.
Input:
parallel --xapply echo ::: A B C ::: D E F](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-23-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Matching input.
Input:
parallel --xapply echo ::: A B C ::: D E F
Output [line order may vary]:
A D
B E
C F](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-24-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Matching input.
Input:
parallel --xapply echo ::: A B C ::: D E F
Output [line order may vary]:
A D
B E
C F
-xapply will wrap, if insufficient input is provided.](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-25-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Replacement strings: The 7 predefined replacement strings
Input:
parallel echo {} ::: A/B.C
parallel echo {.} ::: A/B.C
Output:
A/B.C
A/B](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-26-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Replacement strings: The 7 predefined replacement strings
Input:
parallel echo {} ::: A/B.C
parallel echo {.} ::: A/B.C
Output:
A/B.C
A/B
Rep. String Result
. remove ext.
/ remove path
// only path
/. only ext. and path
# job number
% job slot number](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-27-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Customizing replacement strings
-extensionreplace to change {.} etc.
Shorthand custom (PCRE+) replacement strings
GNU parallel’s 7 replacement strings:
--rpl '{} '
--rpl '{#} $_=$job->seq()'
--rpl '{%} $_=$job->slot()'
--rpl '{/} s:.*/::'
--rpl '{//} $Global::use{"File::Basename"}
||= eval "use File::Basename; 1;"; $_ = dirname($_);'
--rpl '{/.} s:.*/::; s:.[^/.]+$::;'
--rpl '{.} s:.[^/.]+$::'](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-28-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Multiple input sources and positional replacement:
parallel echo {1} and {2} ::: A B ::: C D](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-29-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Multiple input sources and positional replacement:
parallel echo {1} and {2} ::: A B ::: C D
Always try to define replacements, with {<>} syntax.](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-30-320.jpg)
![BASIC ELEMENTS OF SYNTAX [FROM THE
TUTORIAL]
Multiple input sources and positional replacement:
parallel echo {1} and {2} ::: A B ::: C D
Always try to define replacements, with {<>} syntax.
Test with --dry-run first.](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-31-320.jpg)
![ANOTHER [MAN PAGE] EXAMPLE:
“AGGREGATING CONTENT OF FILES”
parallel --header : echo x{X}y{Y}z{Z} >
x{X}y{Y}z{Z}
::: X {1..5} ::: Y {01..10} ::: Z {1..5}](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-39-320.jpg)
![ANOTHER [MAN PAGE] EXAMPLE:
“AGGREGATING CONTENT OF FILES”
parallel --header : echo x{X}y{Y}z{Z} >
x{X}y{Y}z{Z}
::: X {1..5} ::: Y {01..10} ::: Z {1..5}
parallel eval 'cat {=s/y01/y*/=} >
{=s/y01//=}' ::: *y01*
This runs: cat x1y*z1 > x1z1, ∀x∀z](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-40-320.jpg)
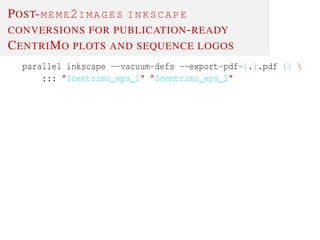
![POST-MEME2IMAGES INKSCAPE
CONVERSIONS FOR PUBLICATION-READY
CENTRIMO PLOTS AND SEQUENCE LOGOS
parallel inkscape --vacuum-defs --export-pdf={.}.pdf {}
::: "$centrimo_eps_1" "$centrimo_eps_2"
parallel "inkscape --vacuum-defs --export-pdf={.}.pdf {};
pdfcrop --hires --clip --margins '0 0 0 -12' {.}.pdf;
mv -f {.}-crop.pdf {.}.pdf
" ::: logo+([:digit:])$VECTOR_FILE_EXT](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-42-320.jpg)
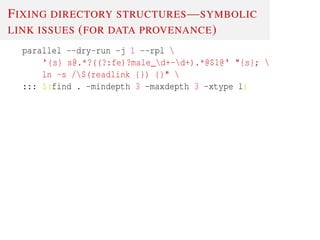
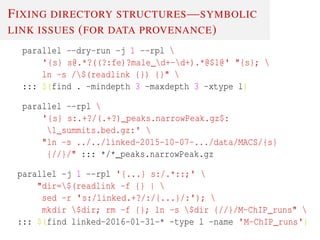
![EXPLORING/COLLATING COMPLEX CENTRIMO
RESULTS
parallel --dry-run -j 1
--rpl '{sex} s:.*?(w*male)-d+_d+.*:1:'
--rpl '{rep} s:.*?male-(d+_d+).*:1:'
--rpl "{TFinfo} s:.*?([^/]+)-expandedTo500bpRegions-
mod.*:1:"
--rpl '{thresh} s:.*?d+_d+-(0.d+).*:1:'
"awk '$0 !~ /^#/ {$1=""; $2="";
print "{TFinfo}","{sex}","{rep}","
{thresh}"$0;}' {} |
sed -r 's/[[:space:]]+/t/g'"
::: $(find ../MEME-ChIP_runs-initial_controls/
-mindepth 5 -wholename
'*hypothesis_testing_selected_controlledVars/
centrimo_out/centrimo.txt' | head
)](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-46-320.jpg)
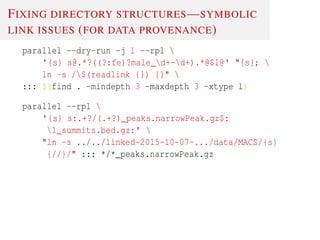
.*:$1:i;'
macs14 callpeak -t {} -n {/..SRF} -g 'mm'
-s 51 --bw 150 -S -p 0.0001
::: ../*.alignment.mm8.bed.gz](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-47-320.jpg)
.*:$1:i;'
macs14 callpeak -t {} -n {/..SRF} -g 'mm'
-s 51 --bw 150 -S -p 0.0001
::: ../*.alignment.mm8.bed.gz
parallel "zcat {} | awk 'BEGIN{FS=OFS="t"} NR > 1
{print $2,$3,$4;}' |
pigz -9 > {/.}.bed.gz" ::: ../*MACS_peaks_annot.txt.gz
liftoverAll '.bed.gz'](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-48-320.jpg)


![PIPELINE—PROCESSING BISULFITE
SEQUENCING DATA WITH METHPIPE
merge_methcount_cmds=$(
parallel -j $NSLOTS --joblog "x.log"
--rpl '{-../} s:.*/::; s:(.[^.]+)+$::; s:-d+$::;'
--dry-run
"echo "$MODULE_LOAD_CMD export LC_ALL=C;
cat $ALIGNED_DIR/{-../}*.tomr |
sort -k 1,1 -k 2,2n -k 3,3n -k 6,6 | ldots |
methcounts -v -c $BISMARK_REF
-o $COUNTS_DIR/{-../}_pool_ALL.meth /dev/stdin"
| tee -a /dev/stderr | qsub ldots
::: $IN_DIR/*.1.fastq.gz | sort -V | uniq
)](https://image.slidesharecdn.com/2016-04-13viner-tech-presentation-gnuparallel-191115190348/85/GNU-Parallel-51-320.jpg)