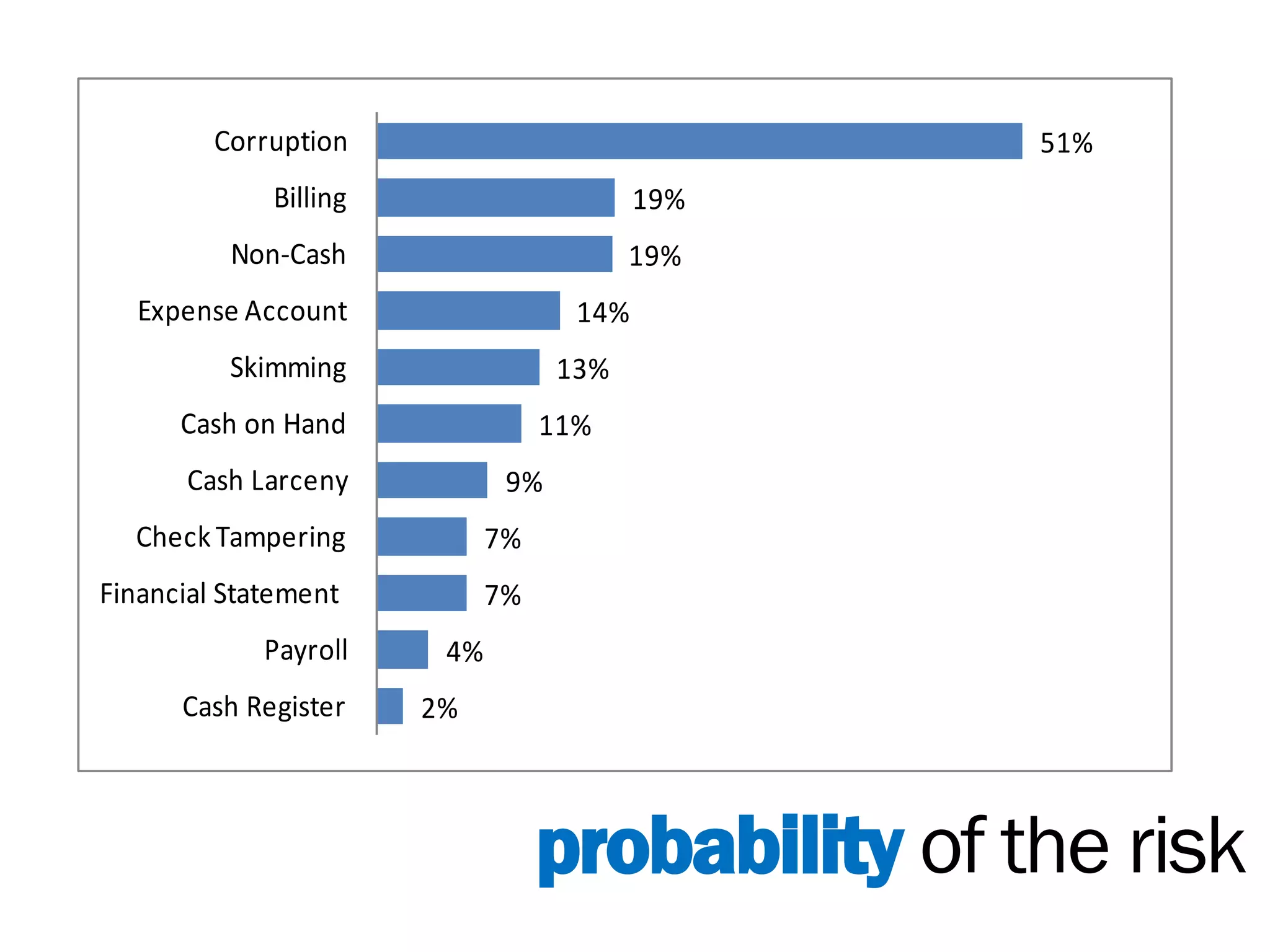
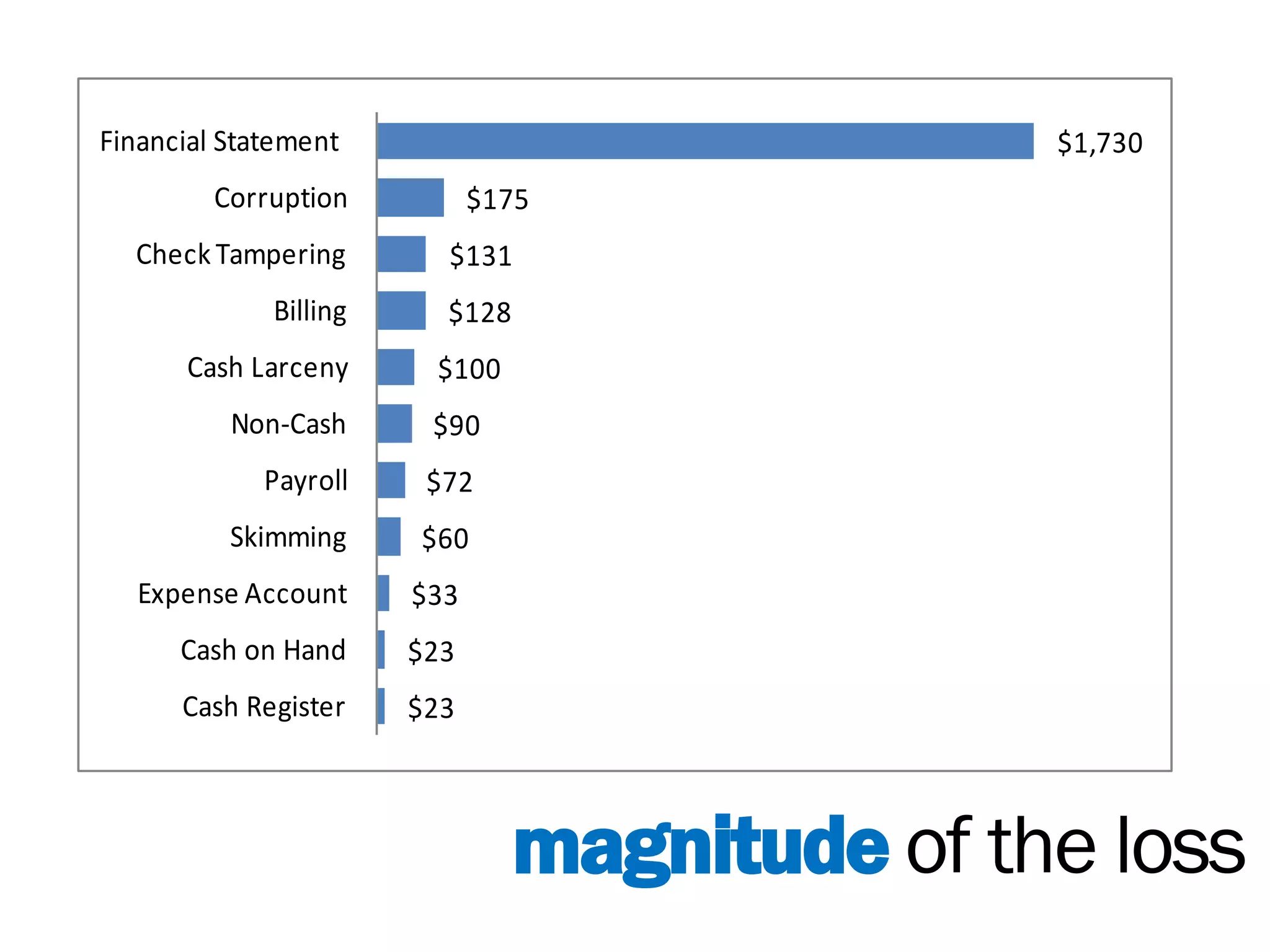
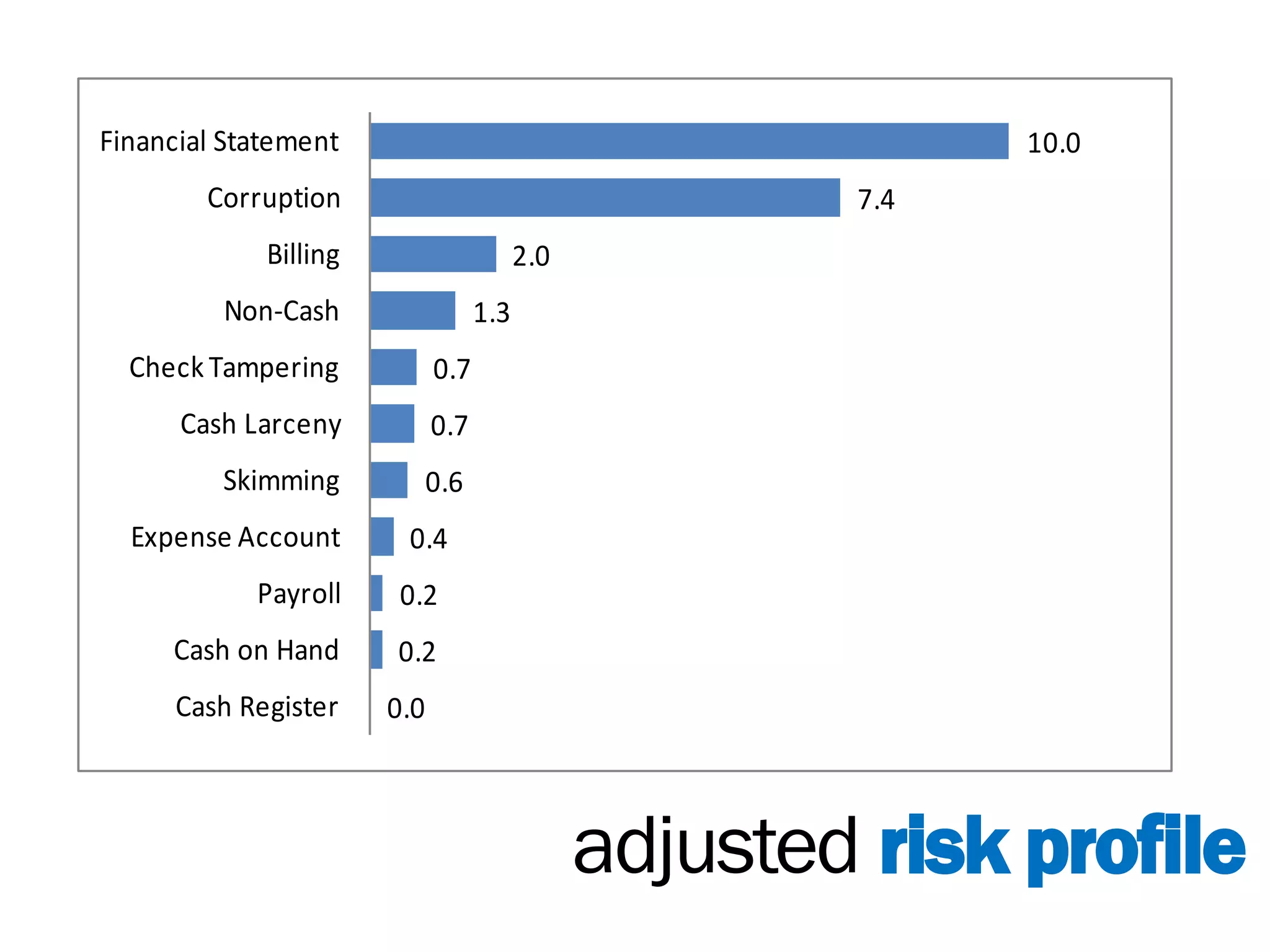
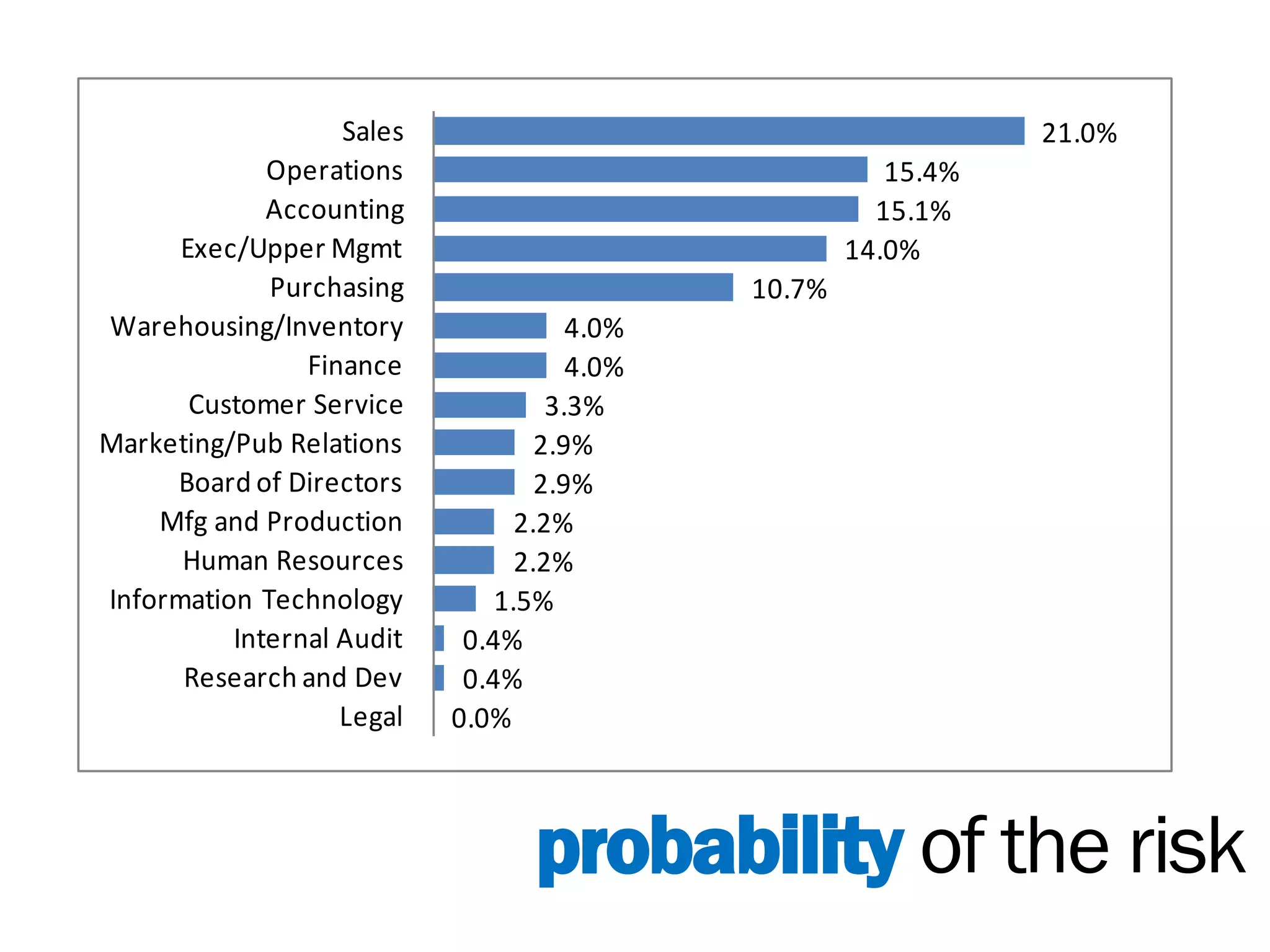
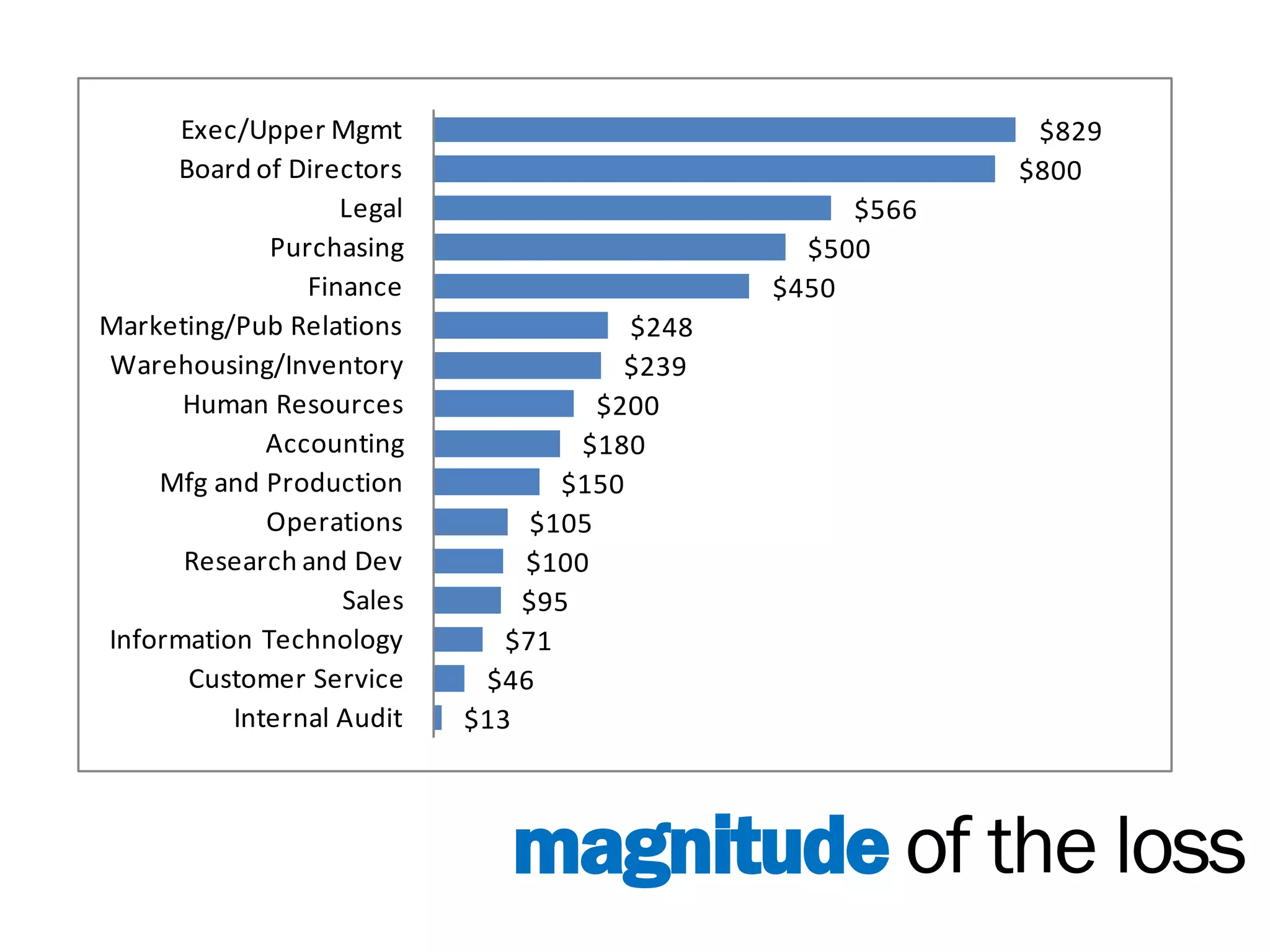
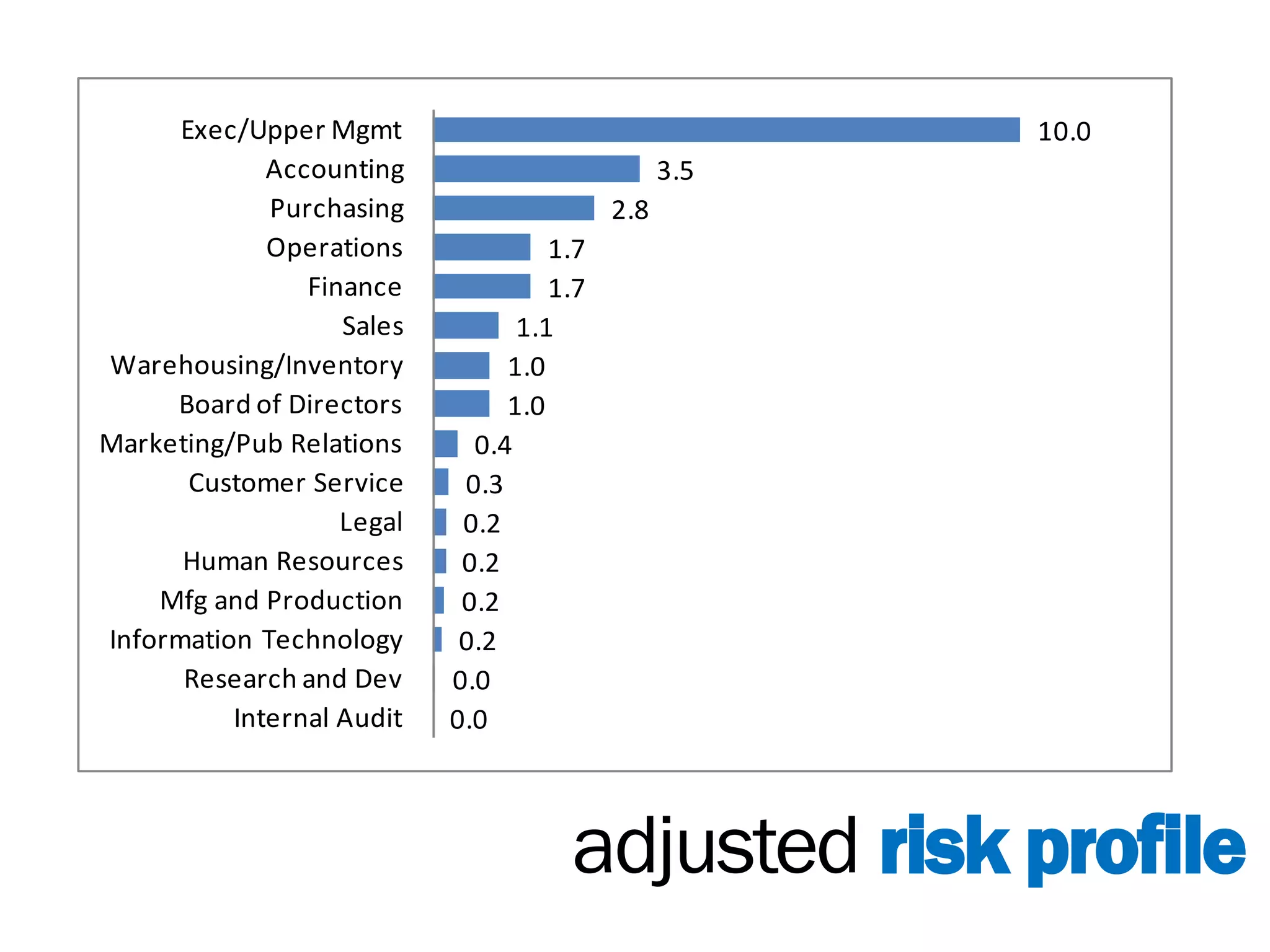
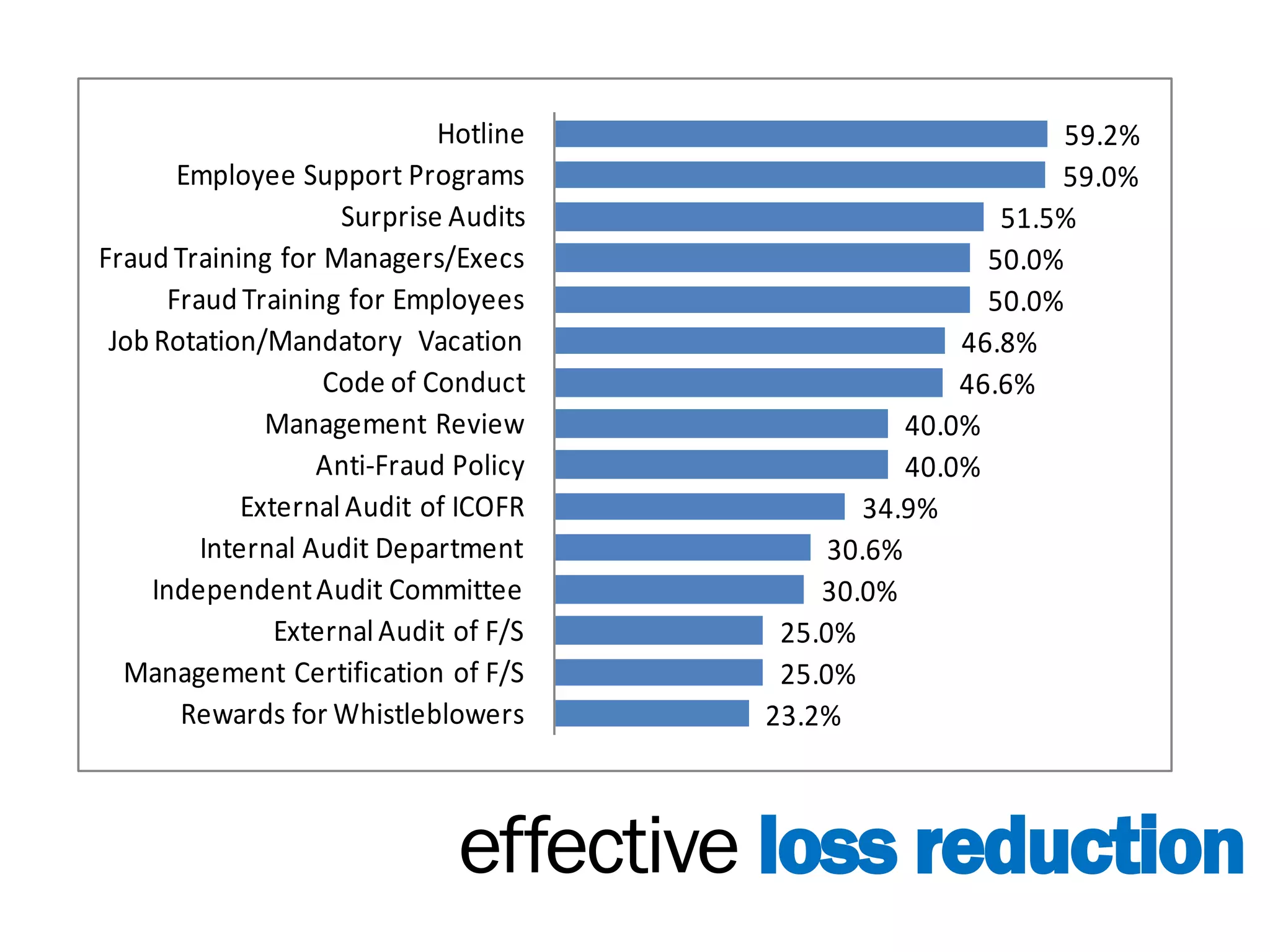
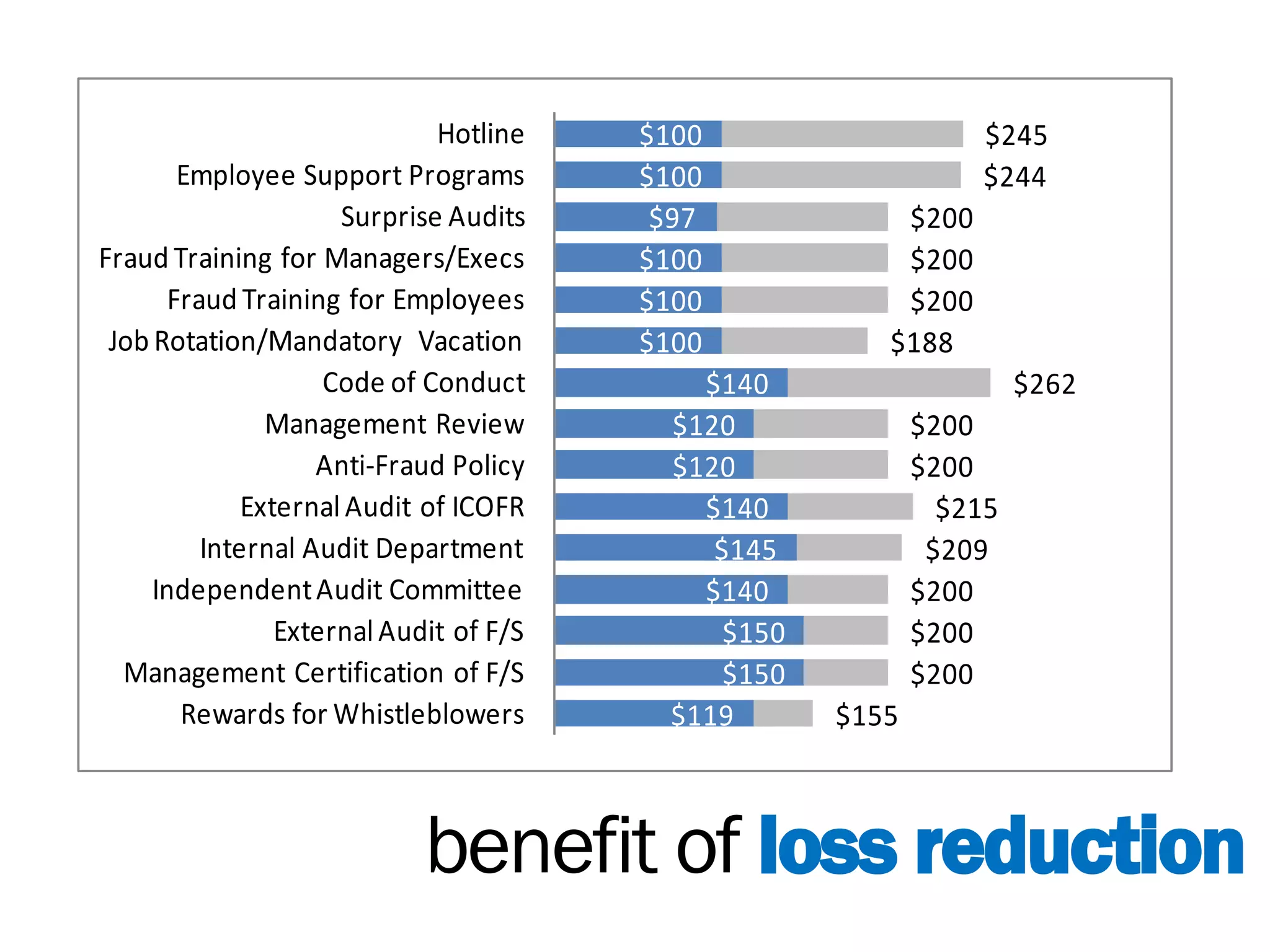
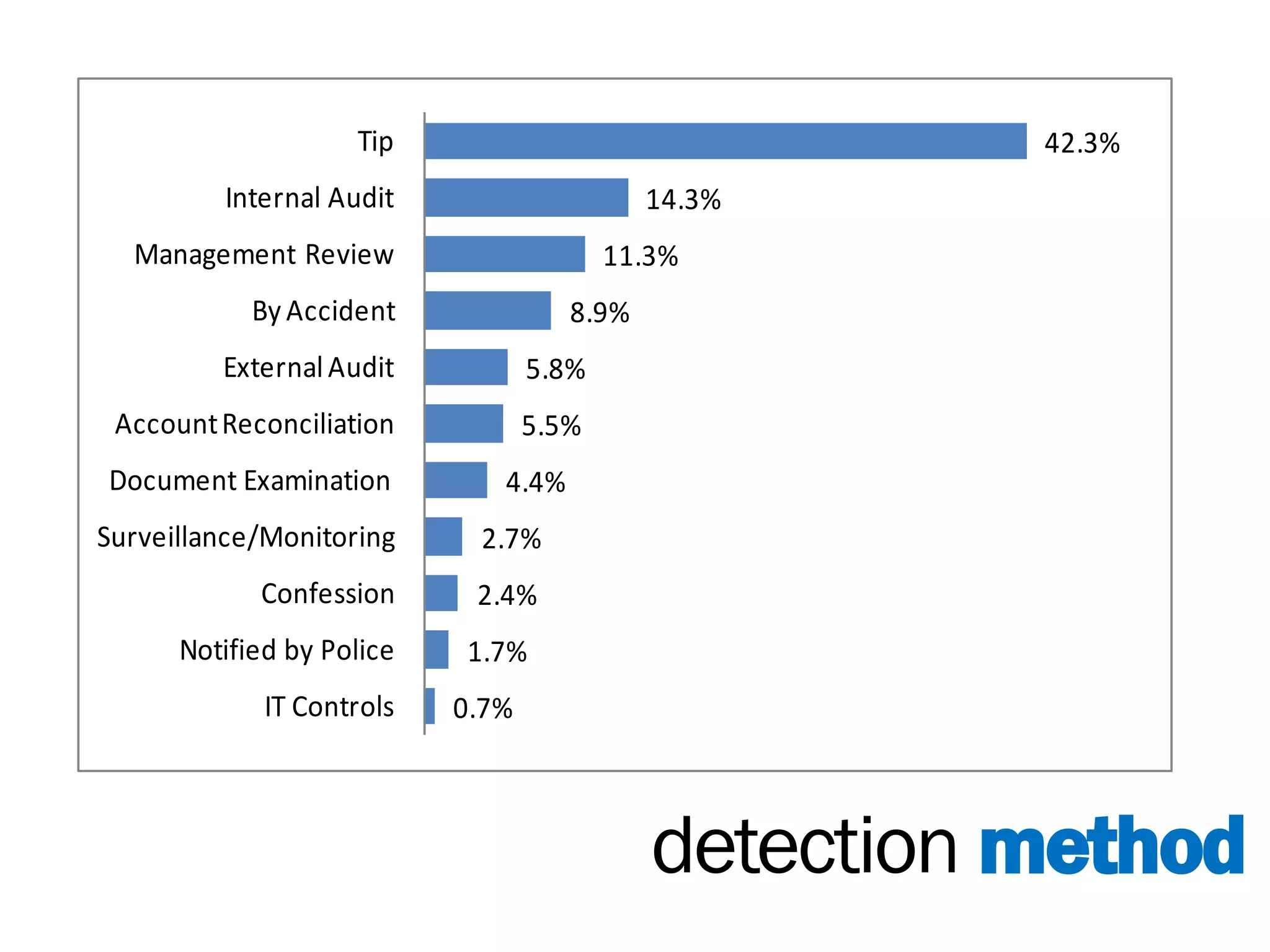
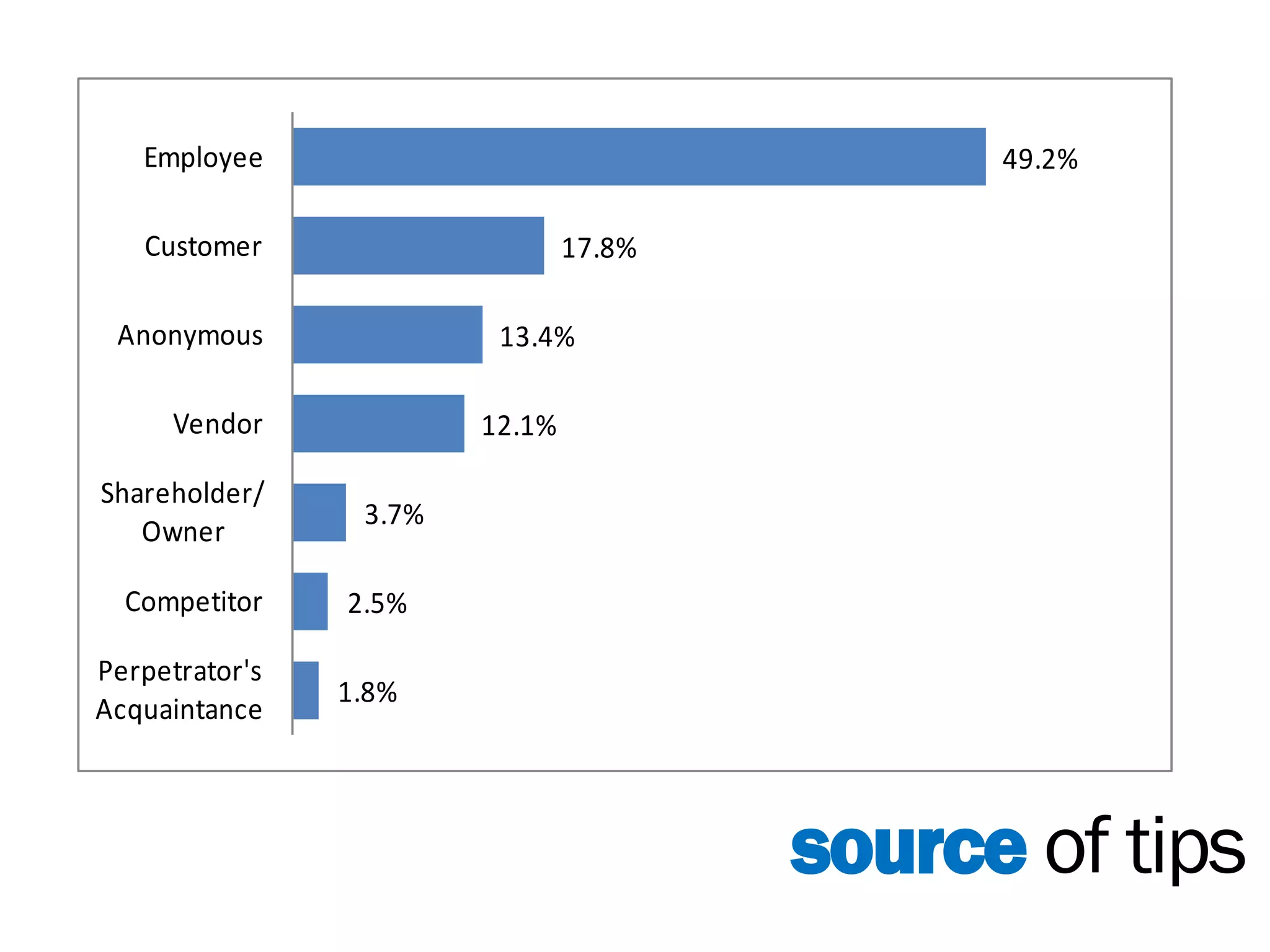
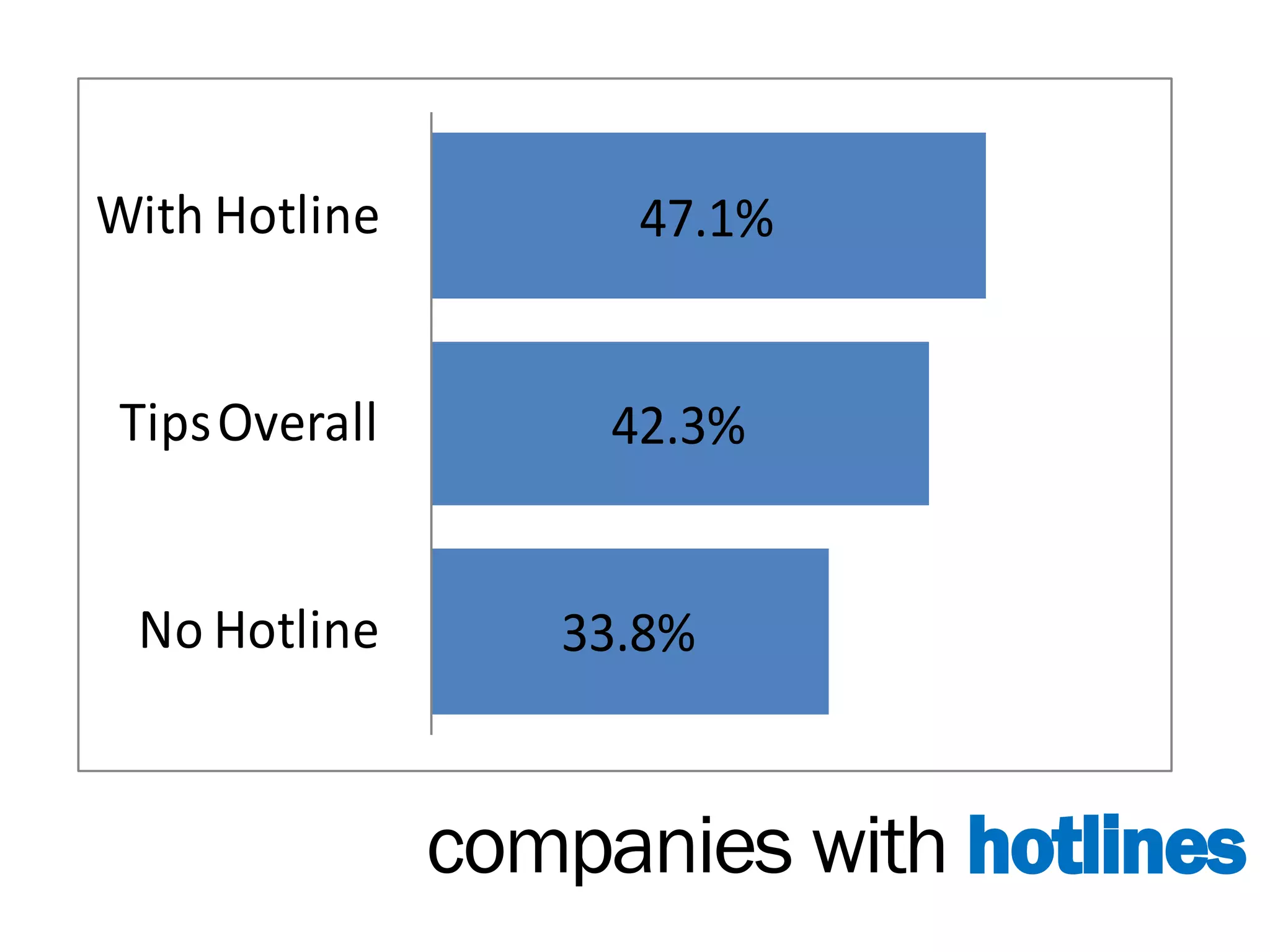
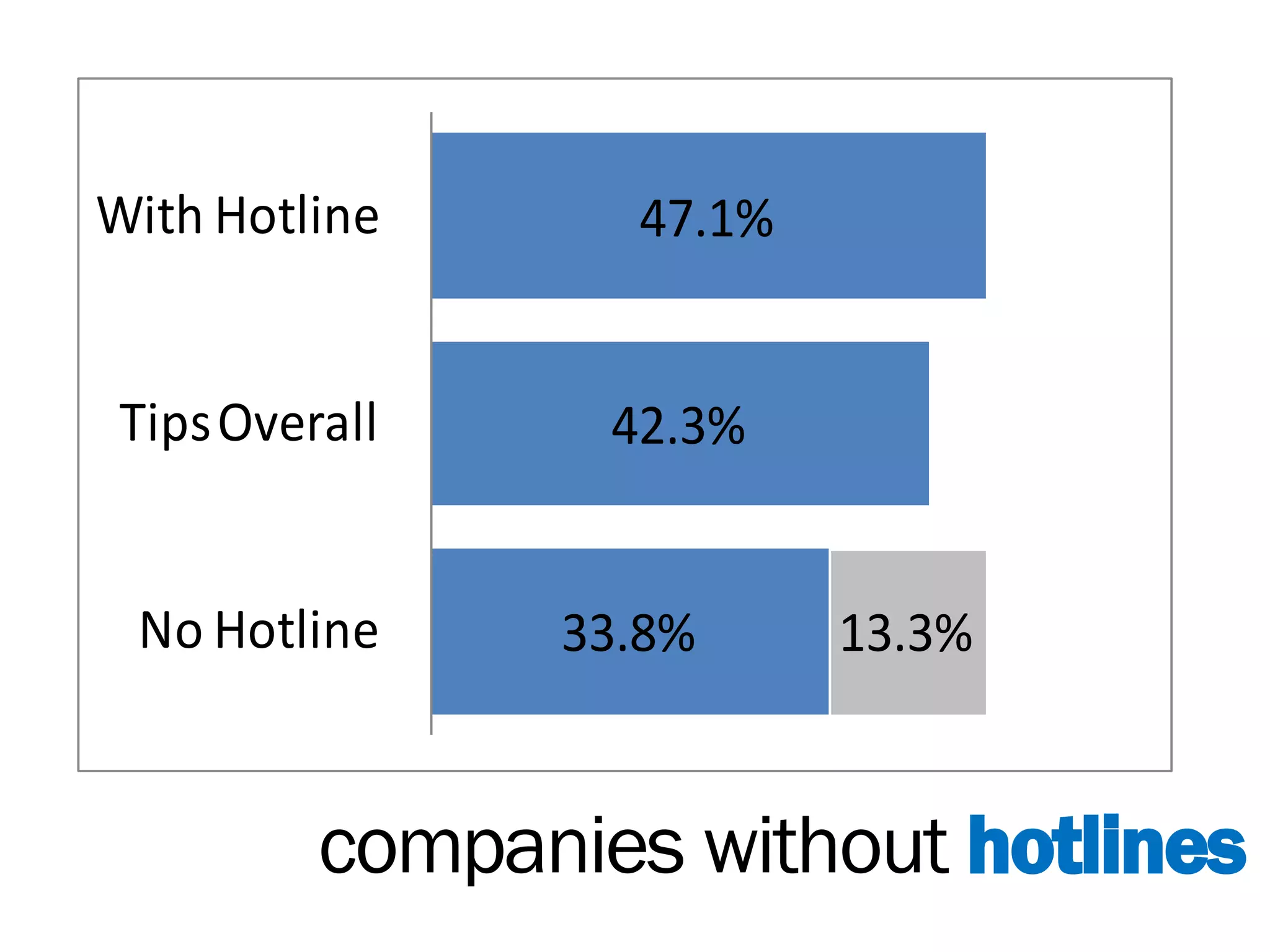
Eric Roring Pesik's presentation on effective internal controls emphasizes the importance of simple, effective, and efficient procedures to mitigate risks such as fraud and corruption. Key methods include segregation of duties, supervision, and the utilization of risk assessments to safeguard organizational integrity. The presentation highlights various risk categories and the effectiveness of different controls, including hotlines and training programs, in reducing losses.