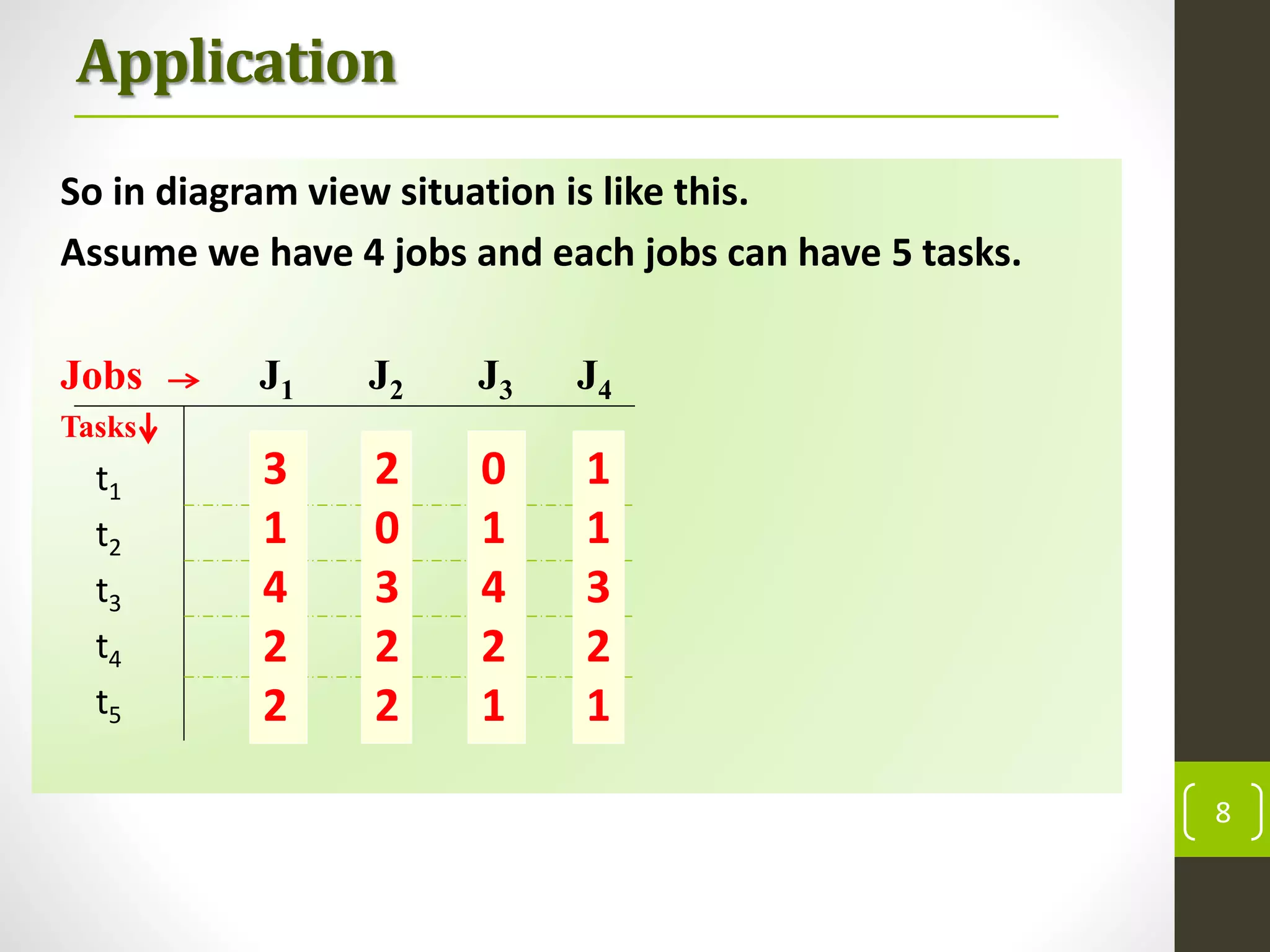
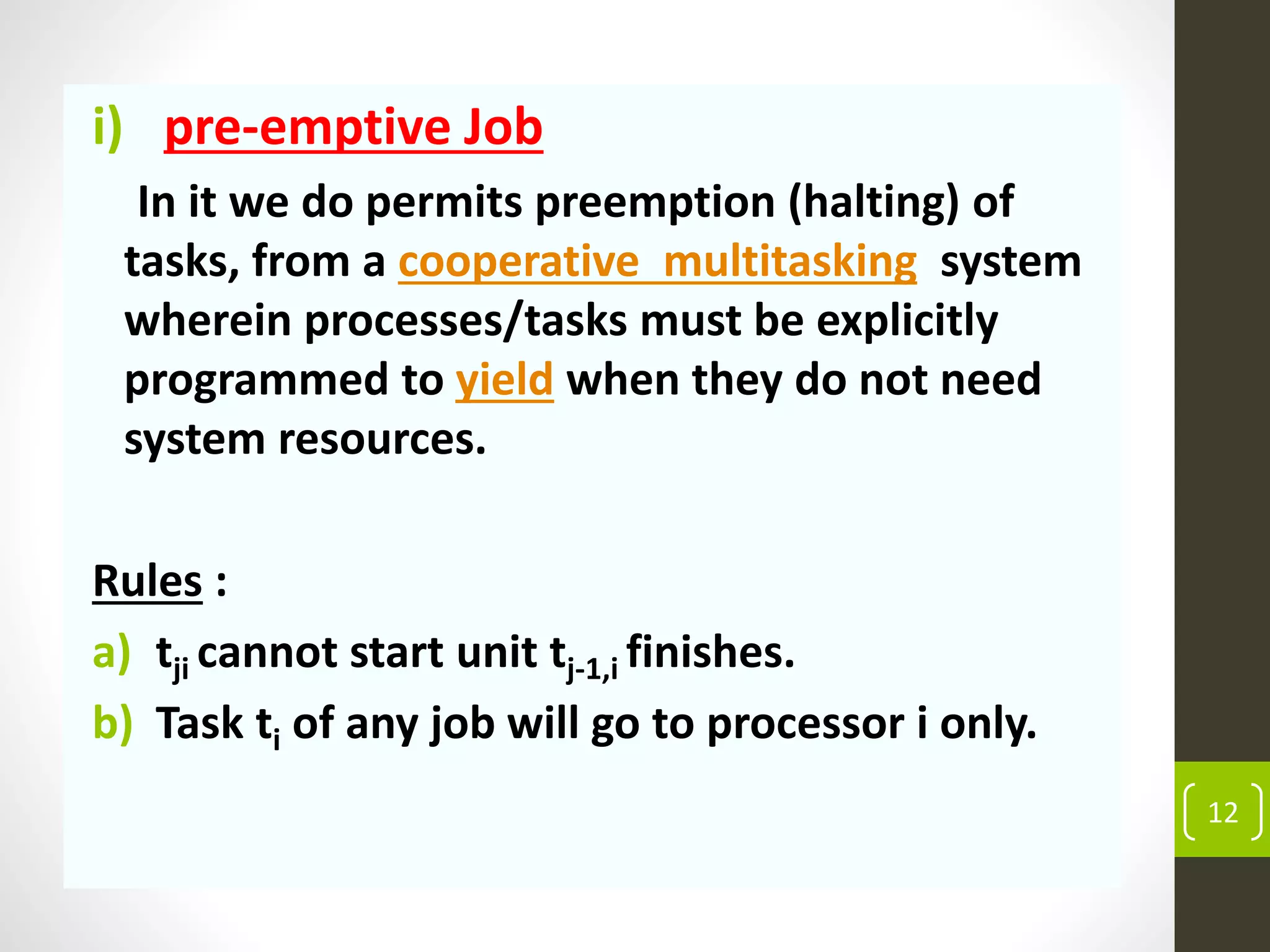
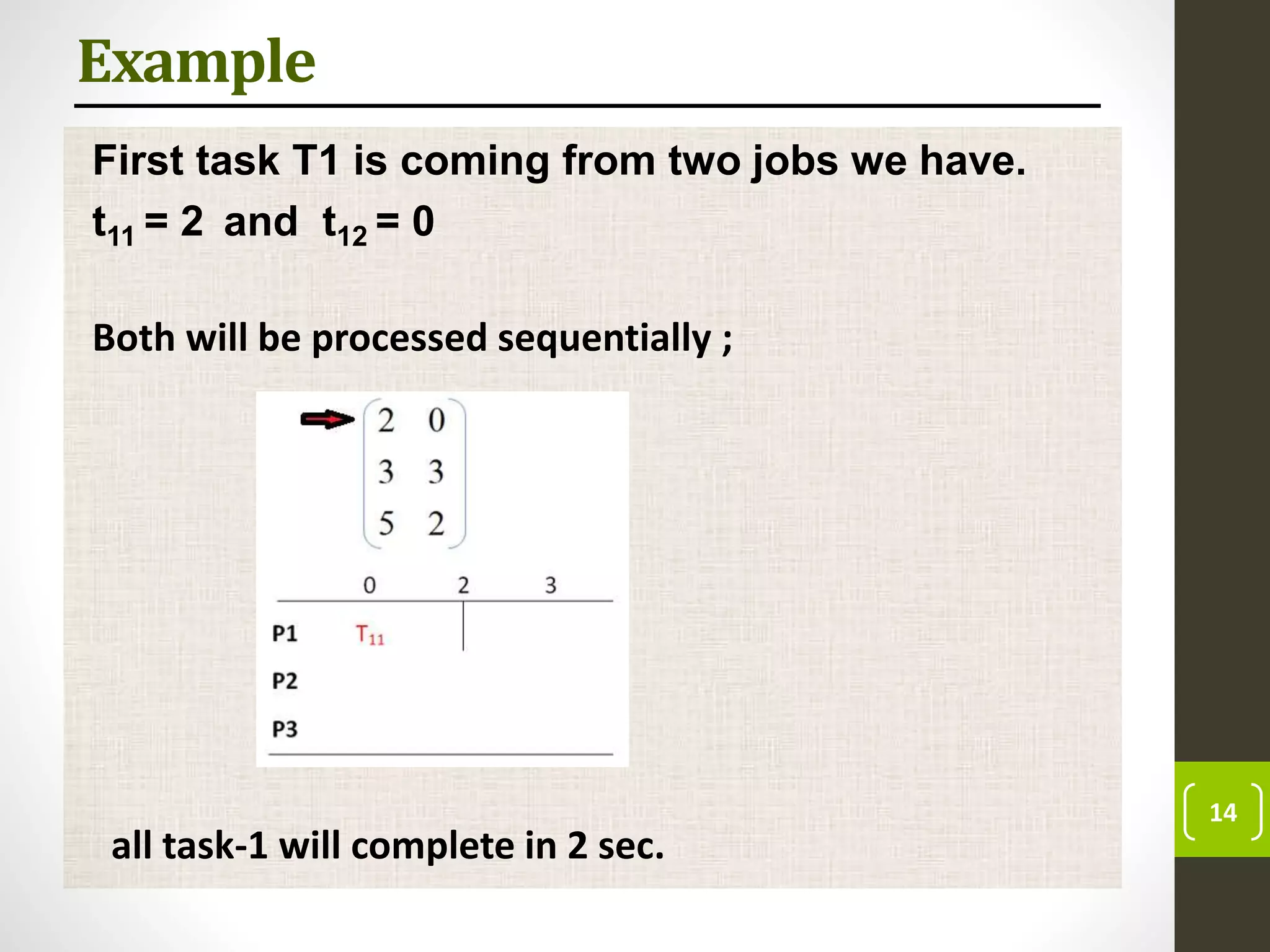
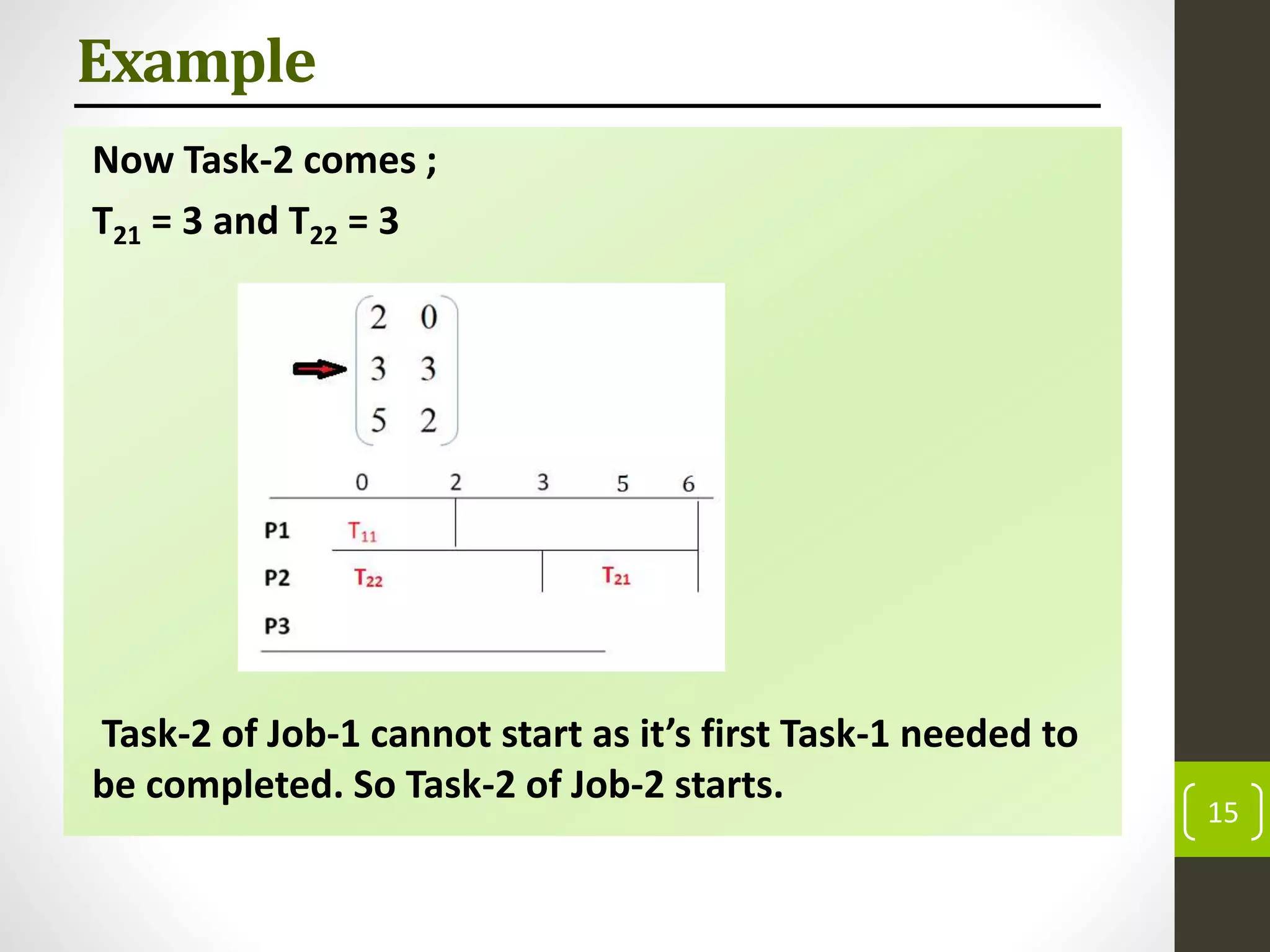
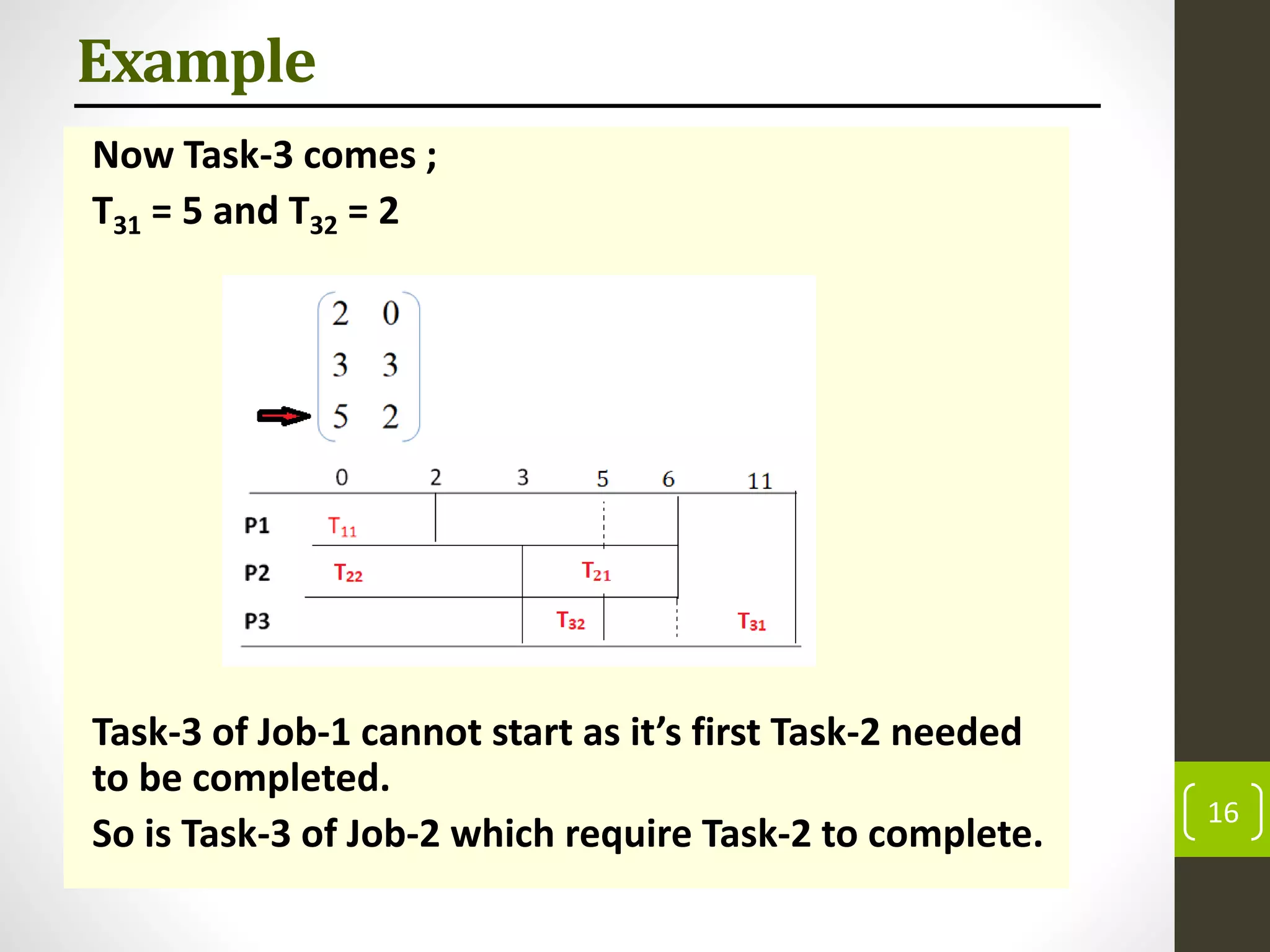
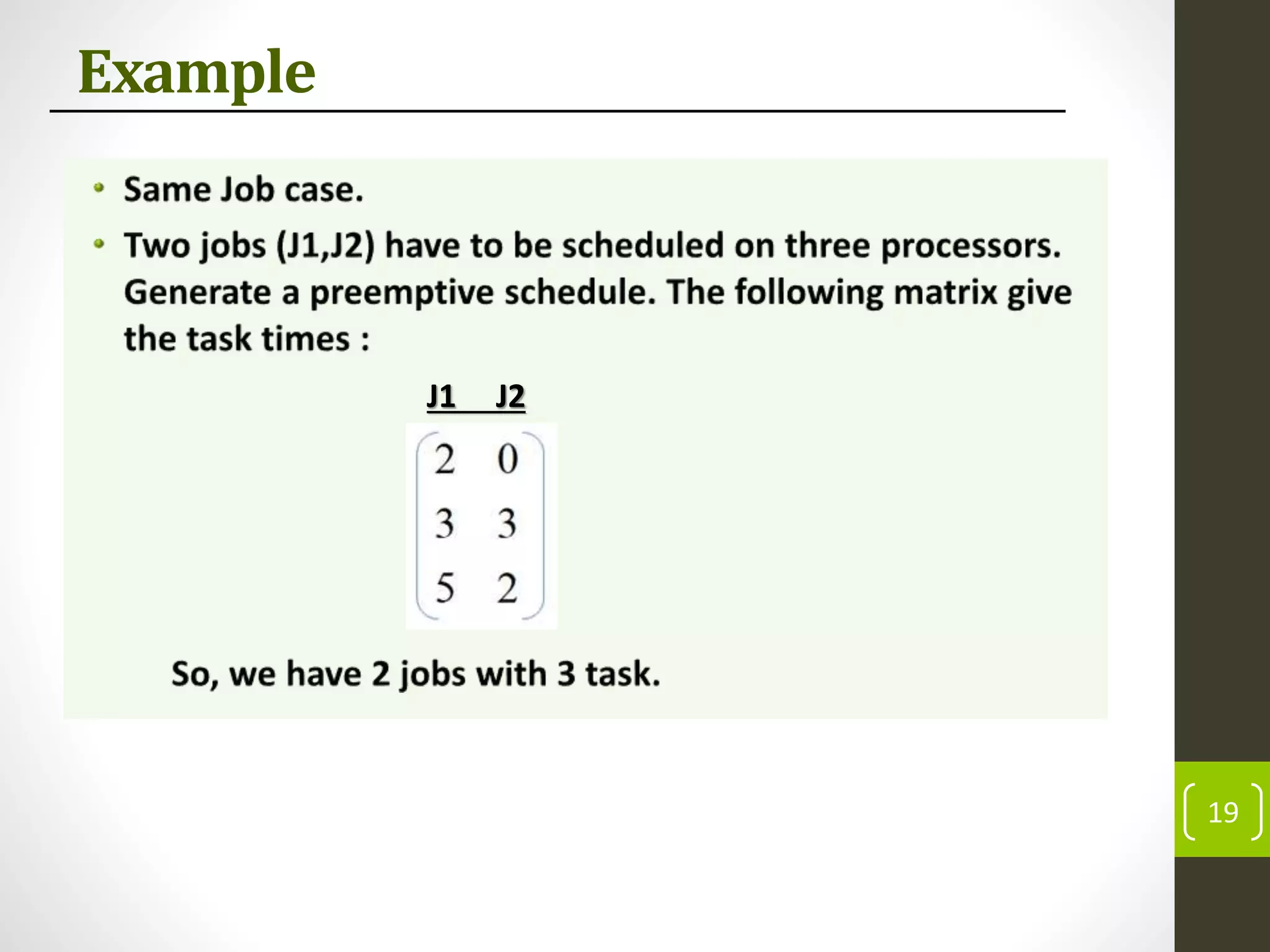
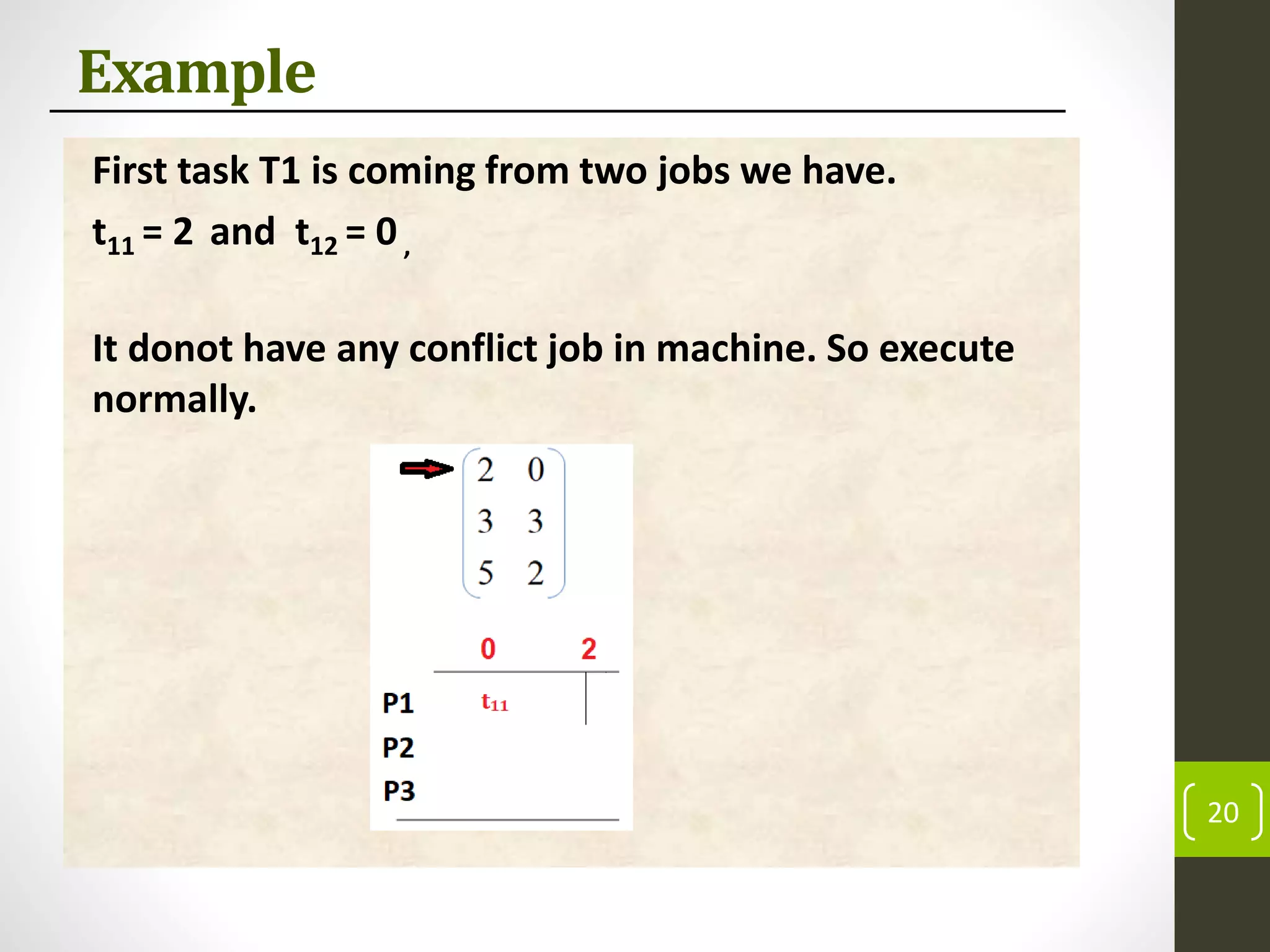
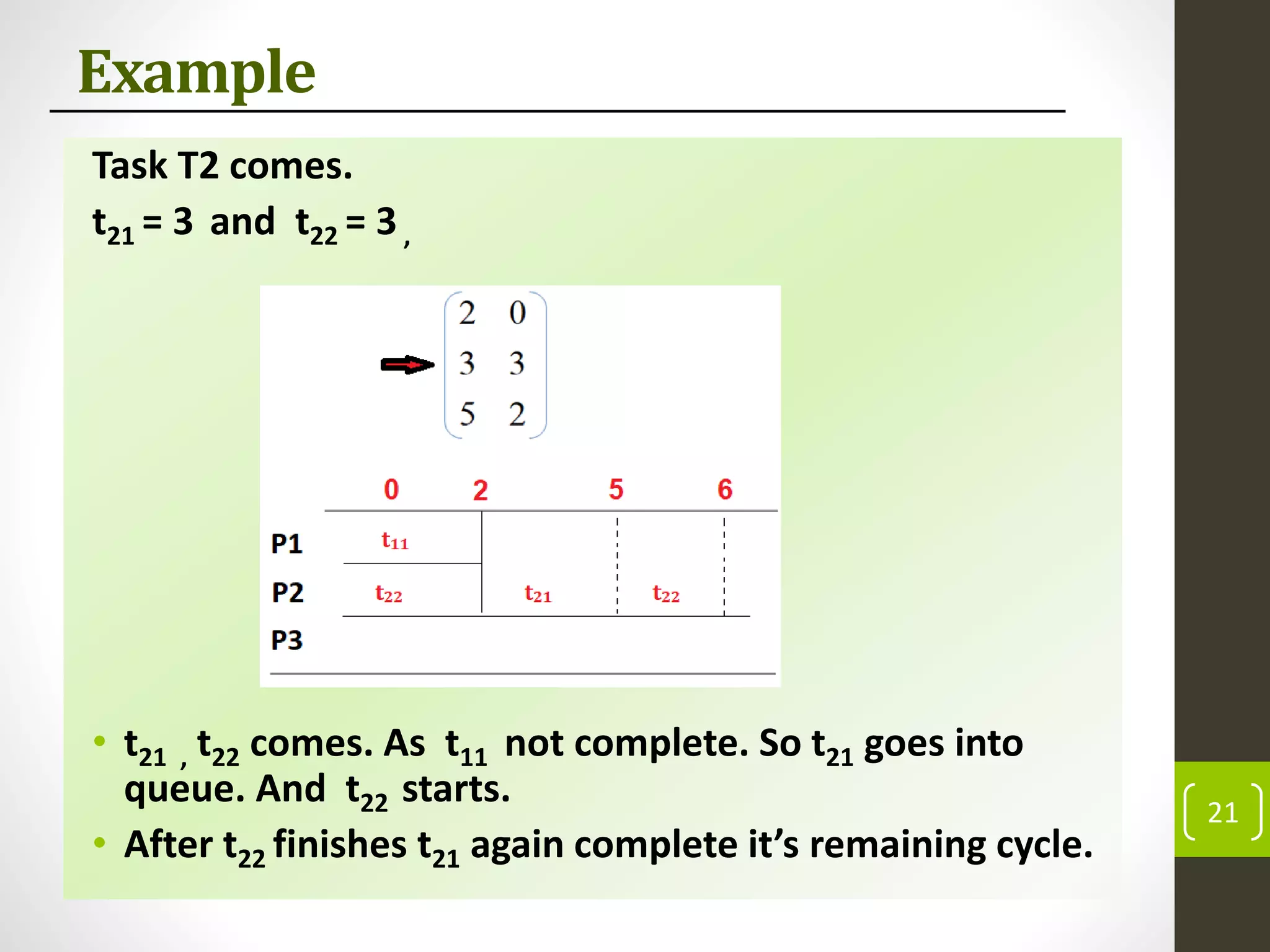
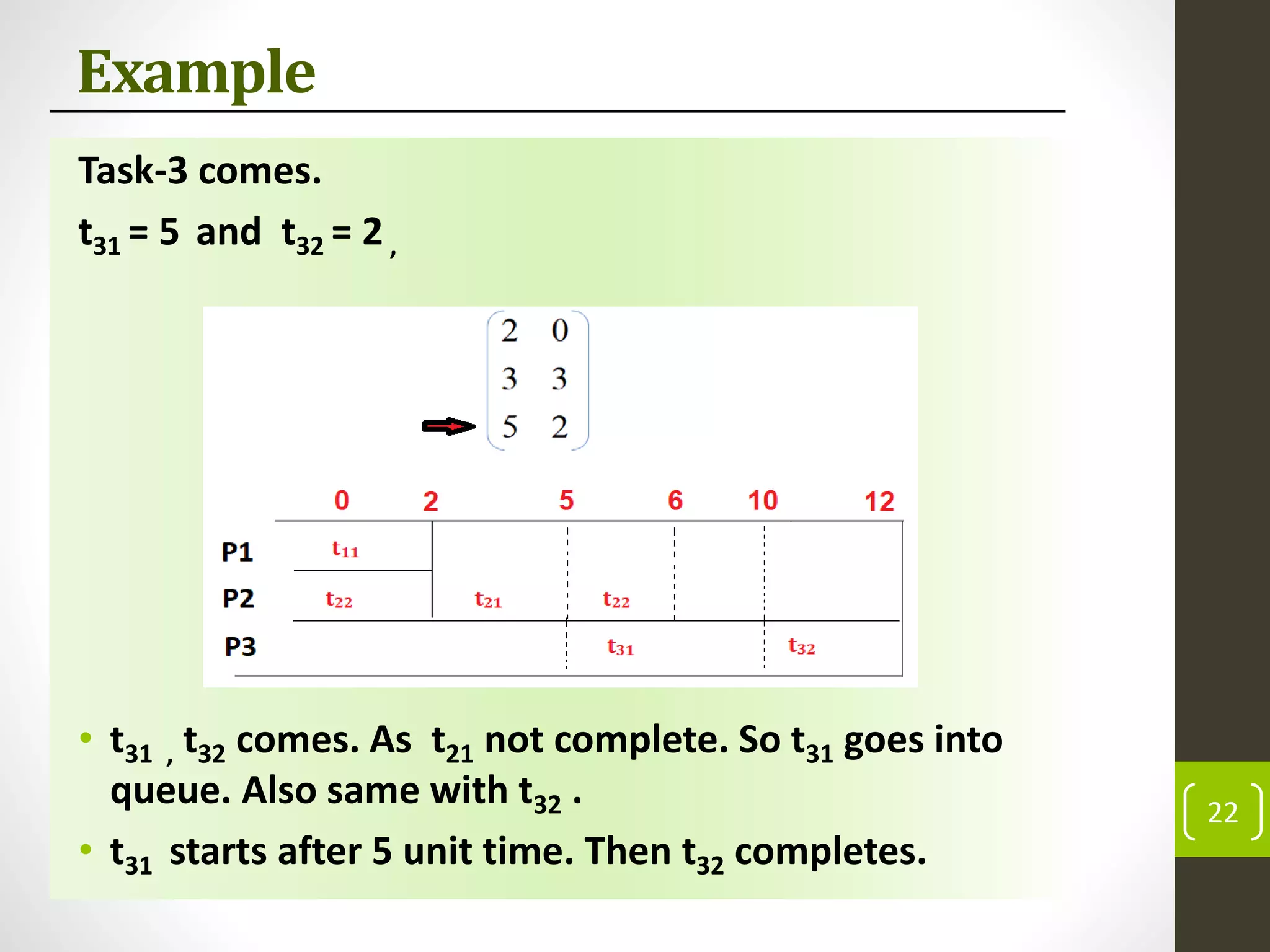
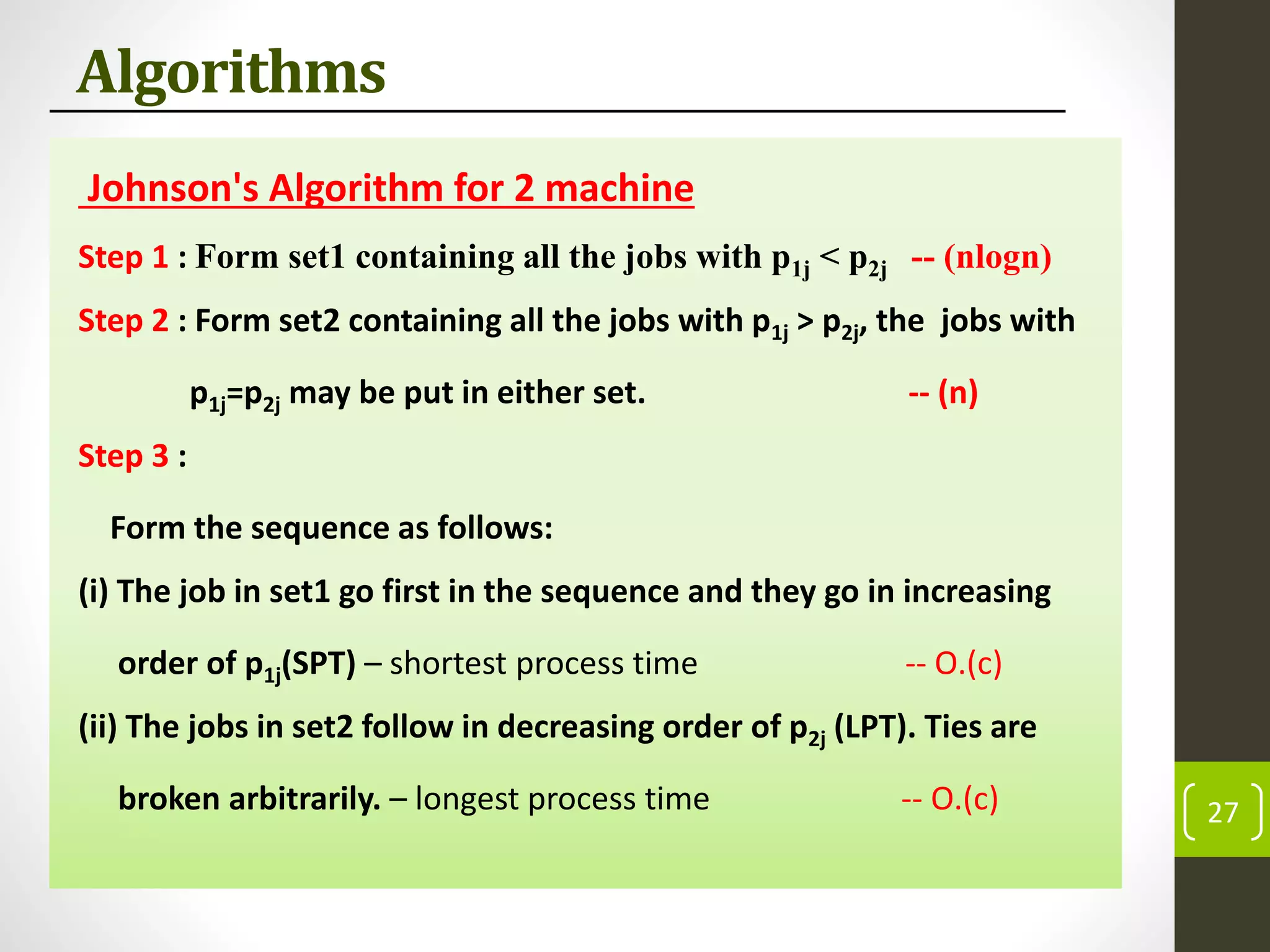
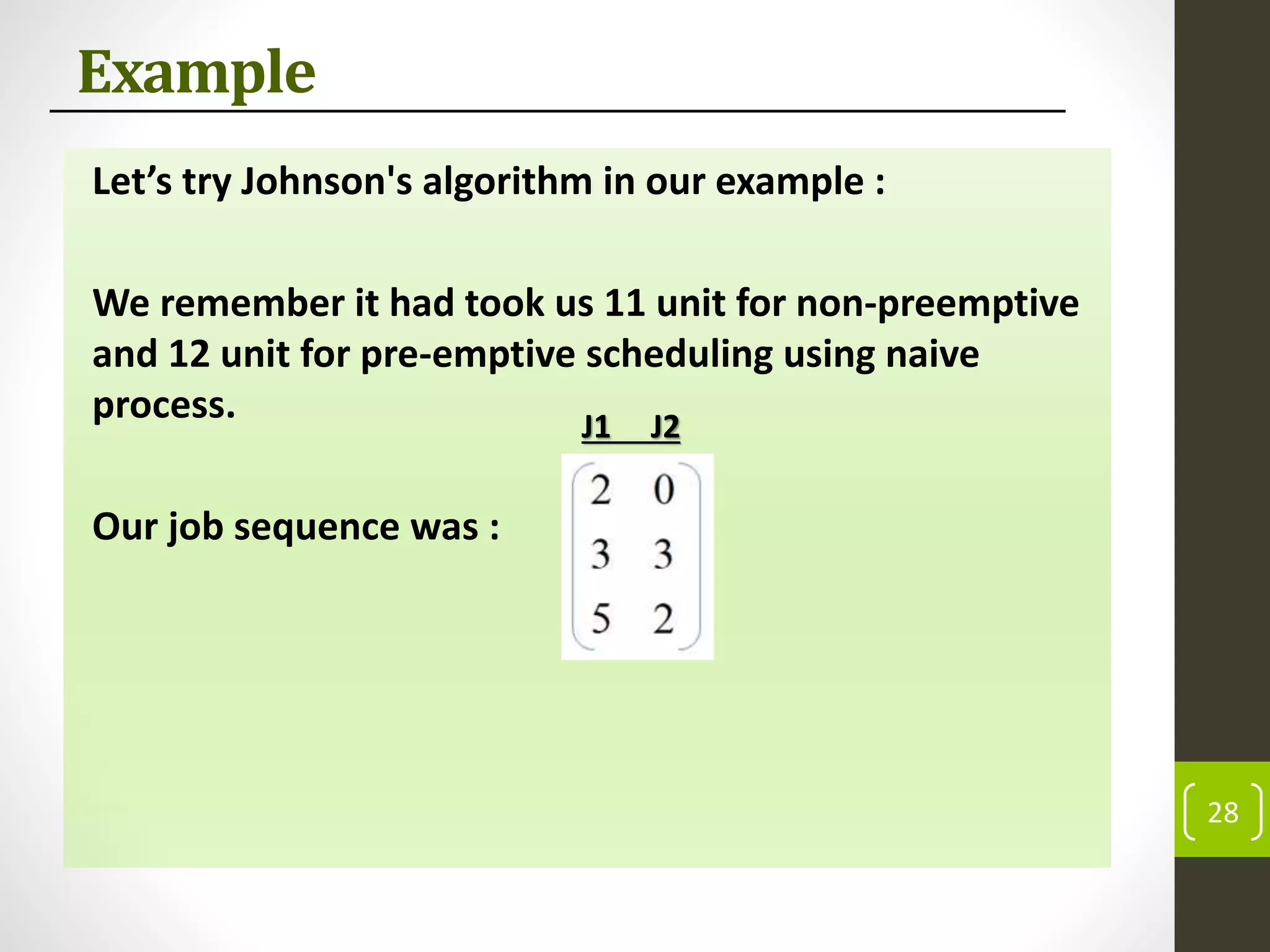
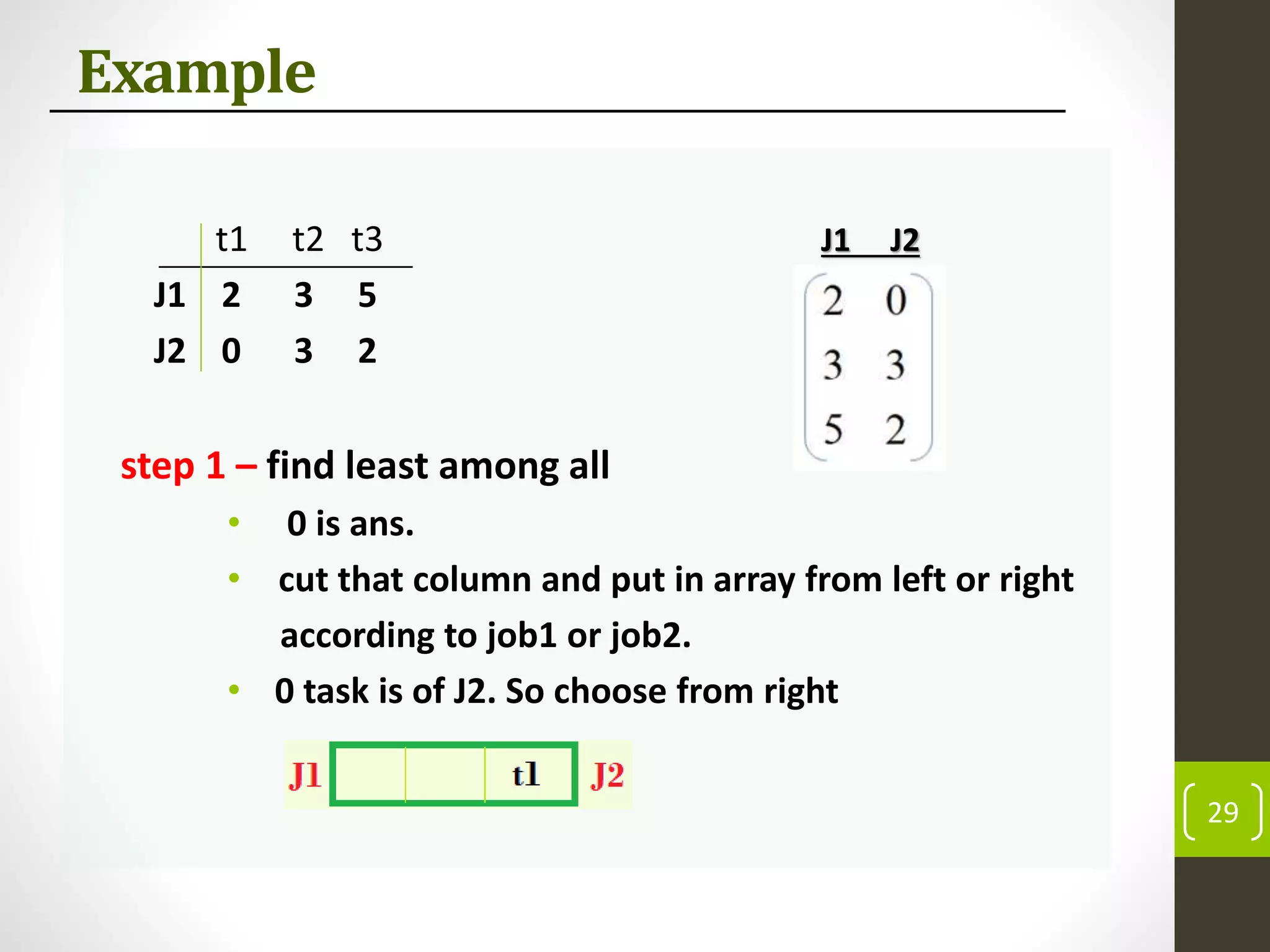
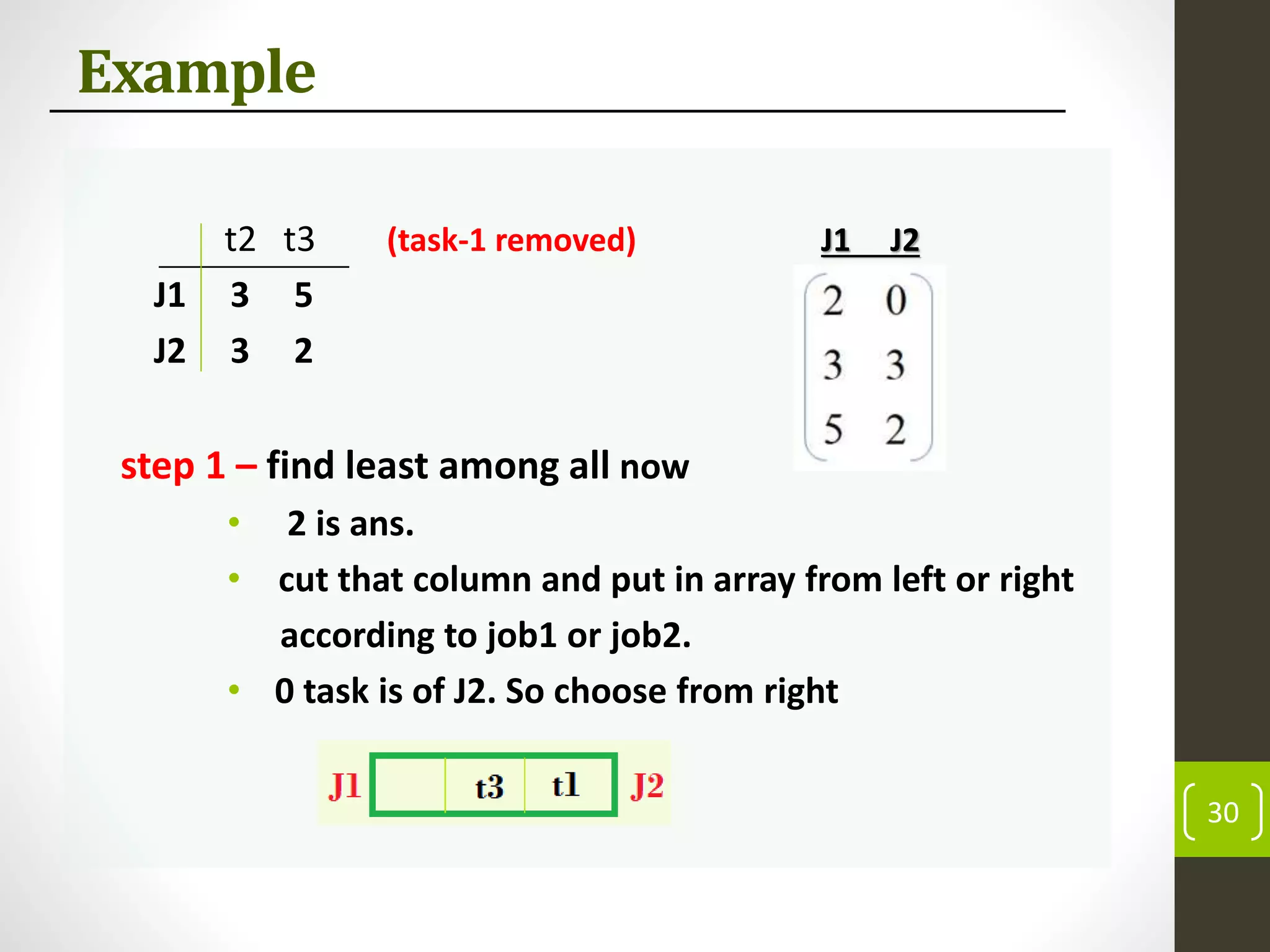
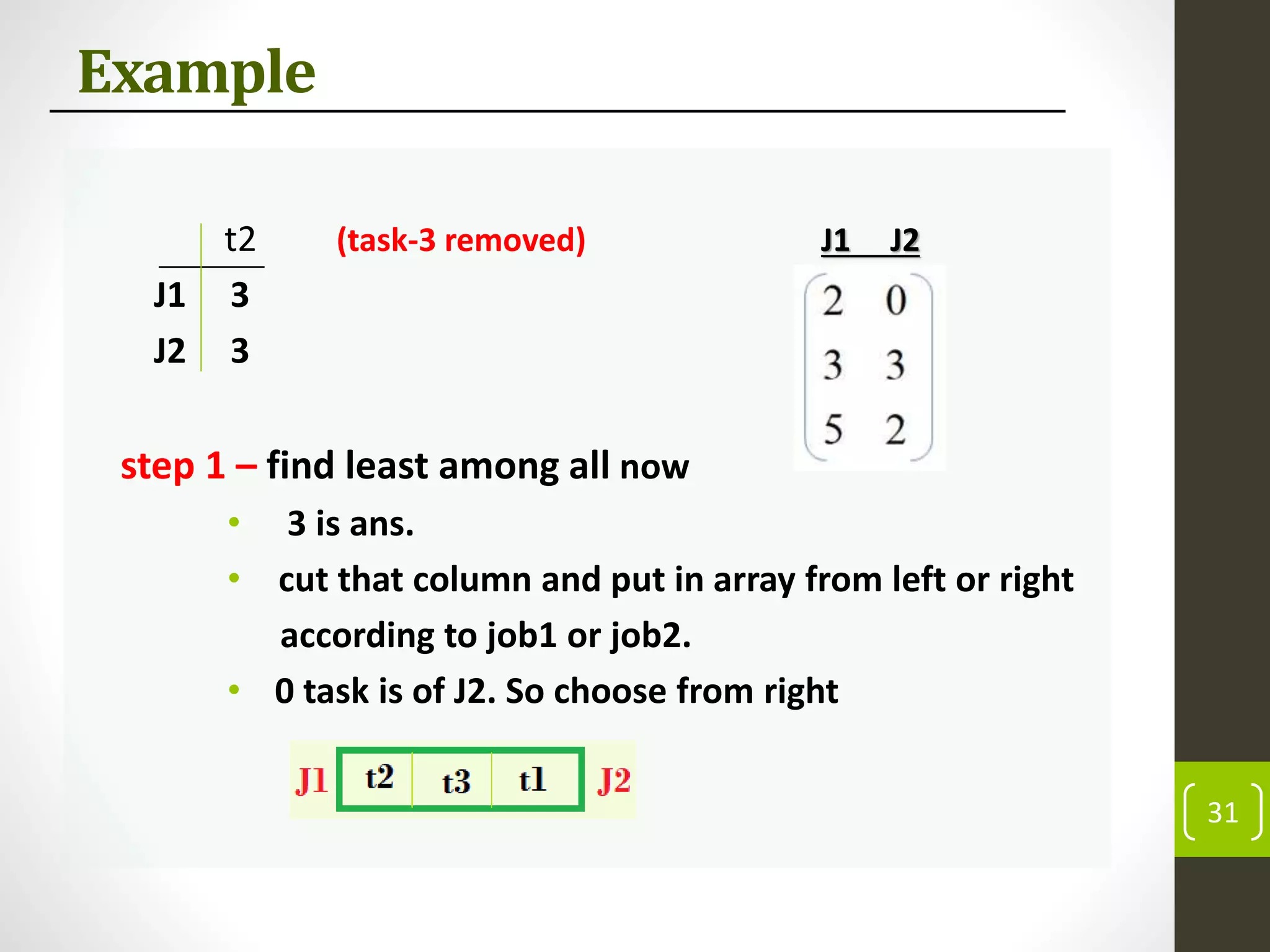
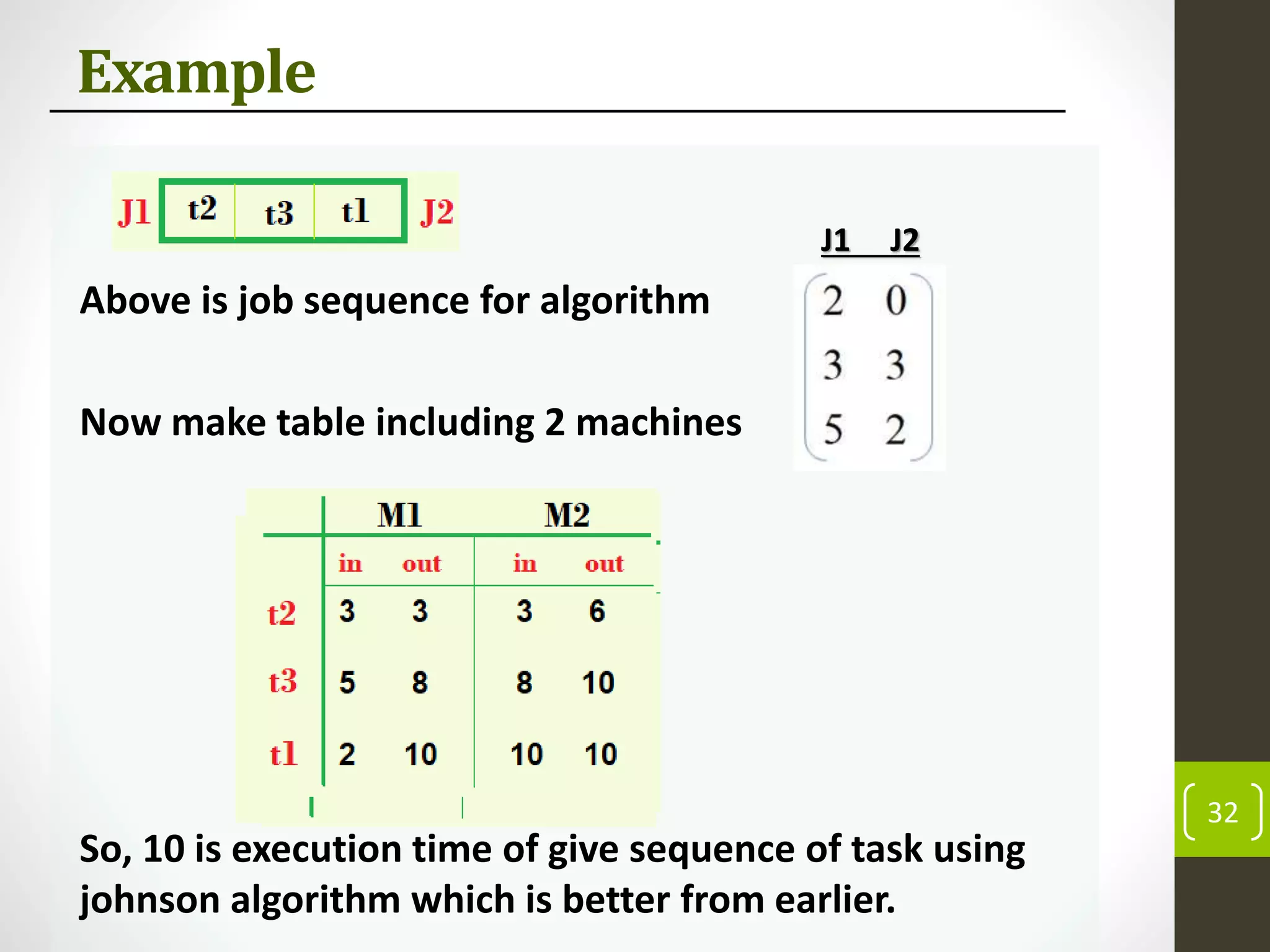
This document discusses flow shop scheduling, which involves sequencing jobs through a set of machines or processes where each job must visit the machines in the same order. It defines flow shop scheduling and provides examples of its applications in industries that require a strict production order. The document then describes two common methods for flow shop scheduling - preemptive and non-preemptive - and provides an example to illustrate the difference. Finally, it discusses algorithms for solving flow shop scheduling problems, focusing on Johnson's algorithm, which provides an optimal solution for problems with two machines.