The document discusses face recognition using principal components analysis (PCA). It provides three key points:
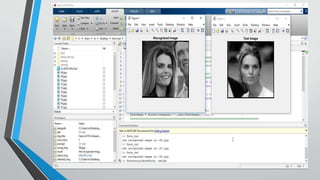
1. PCA is used to reduce the dimensionality of face image data to 2D or 3D by finding patterns in high-dimensional data and visualizing it. This allows for face recognition by representing each face as a set of weights of significant eigenvectors.
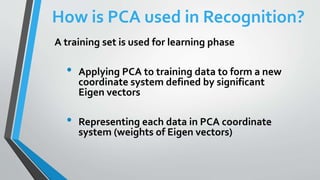
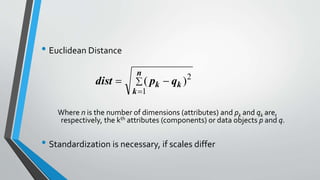
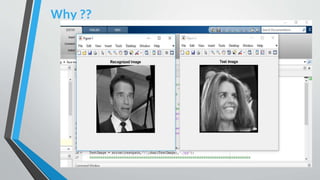
2. A training set is used to form the PCA coordinate system and represent each training face as weights of eigenvectors. A test face is then recognized as the closest training face based on Euclidean distance between their representations in the PCA space.
3. PCA allows for data compression, noise reduction, and classification of faces by projecting high-dimensional image data onto