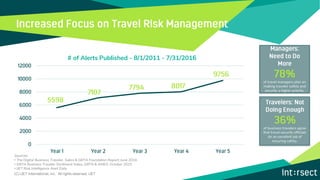
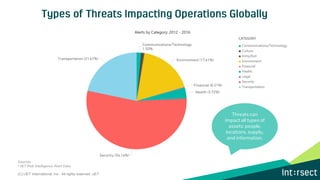
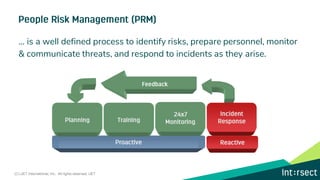
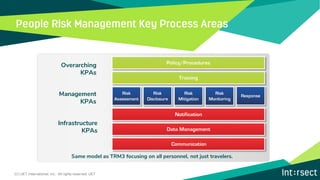
The document outlines the people risk management (PRM) framework used by iJet International, emphasizing its maturity model and systematic approach to identifying, preparing for, monitoring, and responding to risks that affect personnel beyond just travelers. It discusses the importance of traveler safety prioritization and highlights the potential financial and reputational impacts of inadequate risk management. Additionally, it details key components of the PRM solution, including communication, location awareness, and 24/7 response capabilities.