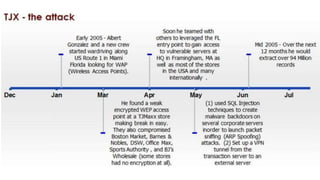
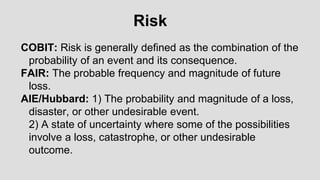
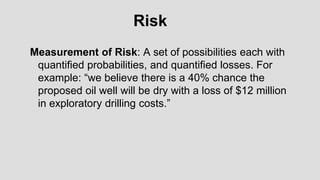
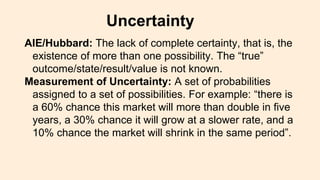
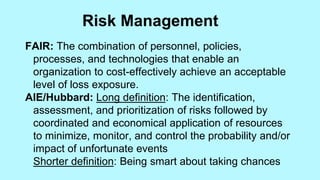
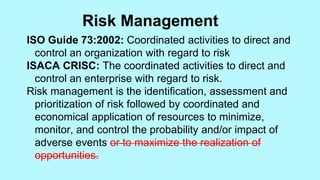
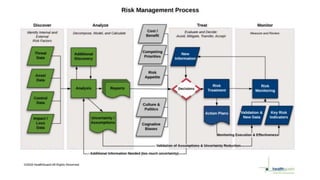
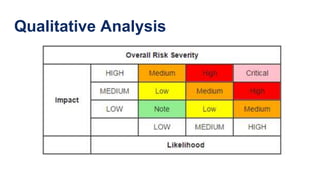
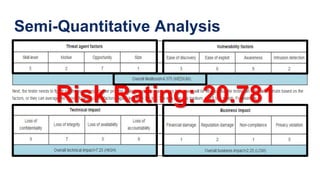
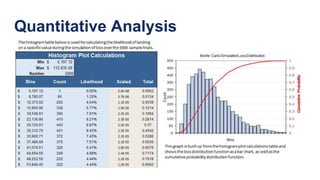
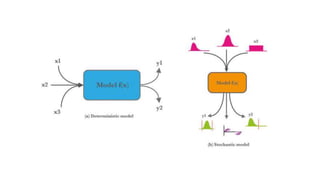
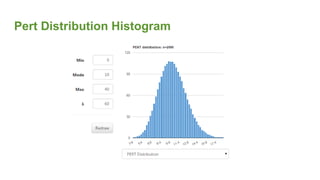
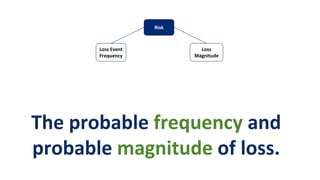
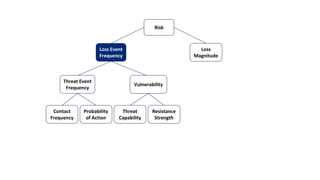
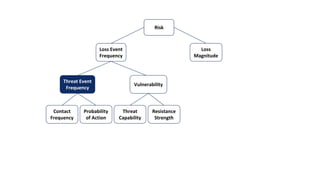
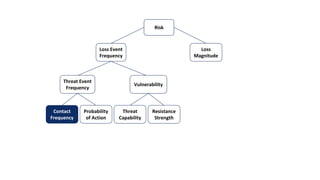
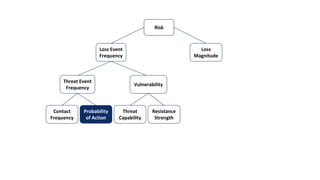
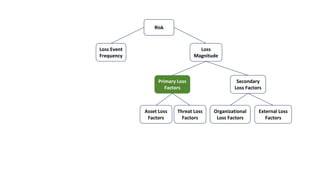
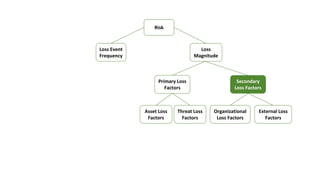
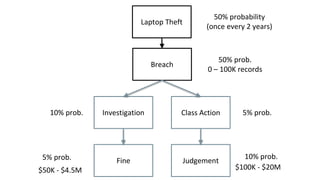
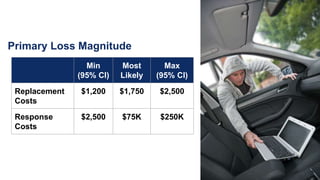
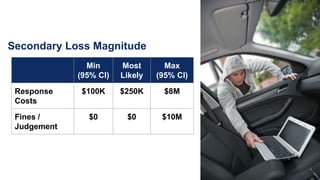
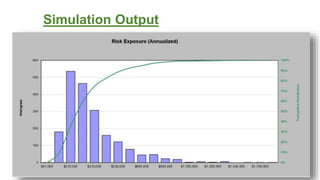
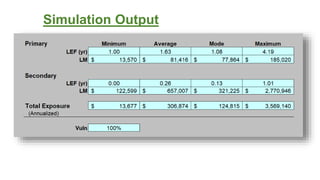
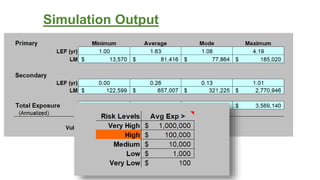
This document provides an agenda for a crash course on managing cyber risk using quantitative analysis. It covers concepts like risk, uncertainty, and risk management approaches. It then discusses qualitative, semi-quantitative, and quantitative risk analysis methods. Monte Carlo simulation and PERT distributions are presented as tools for quantitative analysis. Exercises are provided to demonstrate applying these concepts, including estimating the risk associated with unencrypted laptops being lost or stolen.