Ethics Presentation
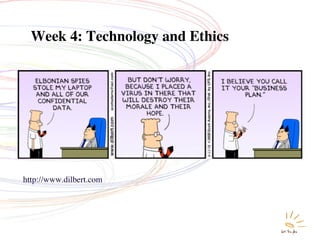
- 1. Week 4: Technology and Ethics http://www.dilbert.com
- 2. Ethics in Computing Ethics is the study of the general nature of morals and of the specific moral choices made by individuals. Because technology often moves faster than rules can be formulated to govern it, how technology is used is left up to the indiviual with the guidance of their personal ethics. Page 83
- 3. Challenges Technology challenges our ethics as individuals and as a society, especially with regards to 1. Social Justice 2. Intellectual Property (Fair Use) 3. Privacy 4. E-Commerce (Online Gambling) 5. Free Speech 6. Computer Abuse 7. The Environment Page 83
- 4. 1. Social Justice Freeman Dyson, American physicist “Science is concentrating too much on making toys for the rich instead of addressing the necessities of the poor.” He proposes three technologies that can turn poor rural areas into sources of wealth: solar energy, genetic engineering and Internet access. Page 85
- 5. Ethical Discussion is: Can technology be used to benefit all? Debate Issue is: Does technology provide economic opportunity for all?
- 6. 1. Social Justice Ethical Discussion: Can technology be used to benefit all? Point Counterpoint • Technology can improve • Problem of poverty is not an the quality of life of poor issue for technologists. if scientists and business Should be addressed by leaders get together. religious leaders/politicians/ • Technology can be an education experts. ethical force to humanize • Genetic engineering may us, giving us the ability to hold the promise of benefits impact the lives of all but should not be explored because of risks. More on Page 85 - 86
- 7. 2. Intellectual Property (IP) and Fair Use IP such as music, writing, and art us protected through copyright law. Four criteria: • What is the purpose of the “fair use” of the work (eg is it for-profit or educational use?) • What is the nature of the work (eg will it be published or unpublished?) • How much material is being used? • Would it decrease the number of copies of the original? Page 87
- 8. Ethical Discussion is: What is fair about fair use? Debate Issue is: What kind of fair use standards are beneficial?
- 9. 2. IP and Fair Use Ethical Discussion: What is Fair about Fair Use? Point Counterpoint • Allowing an open • Existing laws have worked interpretation of far use well for print media and do encourages dissemination not need to be modified. of information. • Copyright holders are winin • Existing laws cannot cope their rights to be aggressive. with widespread Artists or critics can use the dissemination of material but must be able to information possible with pay the licensing fee. Internet More on Page 87 - 88
- 10. 3. Privacy Simply put, privacy is the right to be left alone to do as one pleases, to not have to explain your behaviour to others. In the digital age, we leave a trail of electronic breadcrumbs almost everywhere we go.
- 11. Ethical Discussion is: Is personal privacy a casualty of the modern age? Debate Issue is: Should personal privacy be protected
- 12. 3. Privacy Ethical Discussion: Should privacy be protected? Point Counterpoint • If I’m not doing • If you aren’t doing anything wrong, you anything wrong, you have have no reason to nothing to hide. watch. • It’s not possible to put a • Requiring national ID price on freedom or is like Nazis or security therefore projects Soviets and like surveillance and implementation is a national ID are worth the waste of tax money. cost of implementation. Page 90
- 13. Surveillance
- 14. Surveillance Factors propelling the surveillance revolution: 1. Improved technology. 2. Centralized surveillance. 3. Unexamined assumptions that cameras provide security. These developments are creating powerful momentum toward pervasive surveillance of our public spaces.
- 16. 4. Communication and Free Speech Ethical Discussion is: When does big business limit free speech? Debate Issue is: Did Google make the right choice in China by self-censoring? Page 87
- 17. 4. Free Speech Discussion: Does big business limit (Google) free speech? Point Counterpoint Google acted unethically Google’s actions justified • Google sacrificed free- • Companies are free to pursue speech for business. profits as long as they follow • Cooperating with the country’s laws. China violates human • Withdrawing from China rights. would further restrict free speech. More on Page 94
- 18. 5. Computer Abuse Using a computer or the Internet to harm another individual. By providing anonymity the Internet facilitates such unsavory activities. Everyone agrees that protecting children from harm is an important goal but the question is how best to accomplish it?
- 19. Ethical Discussion is: Does restricting online information protect children? Debate Issue is: Is filtering or monitoring software helpful?
- 20. 5. Computer Abuse Ethical Discussion: Does restricting online information protect children? Point Counterpoint • Filtering software is • Filtering routinely blocks the only way to good as well as bad. protect children • Educating children about from violence and responsible Internet use is porn. more effective. • Parents need to be • Filtering widens the assured that schools “digital divide” by and libraries are adversely affecting the “safe havens.” poor. Page 96
- 21. 6. Environmental Issues Ethical Discussion: Does excessive gadgetry lead to excessive levels of hazardous e-waste. http://www.youtube.com/watch?v=67j7JlEZzpQ&feature=related
