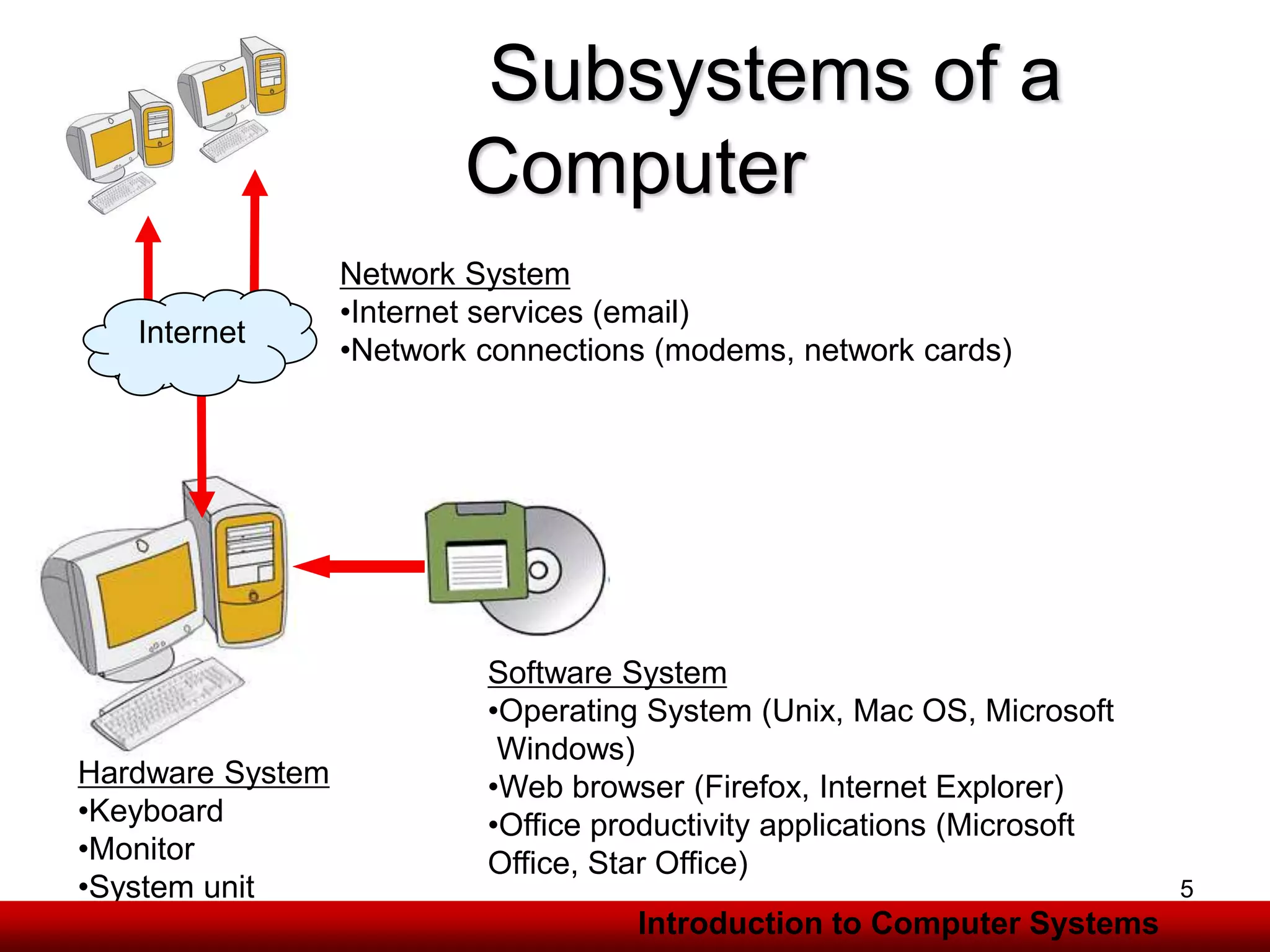
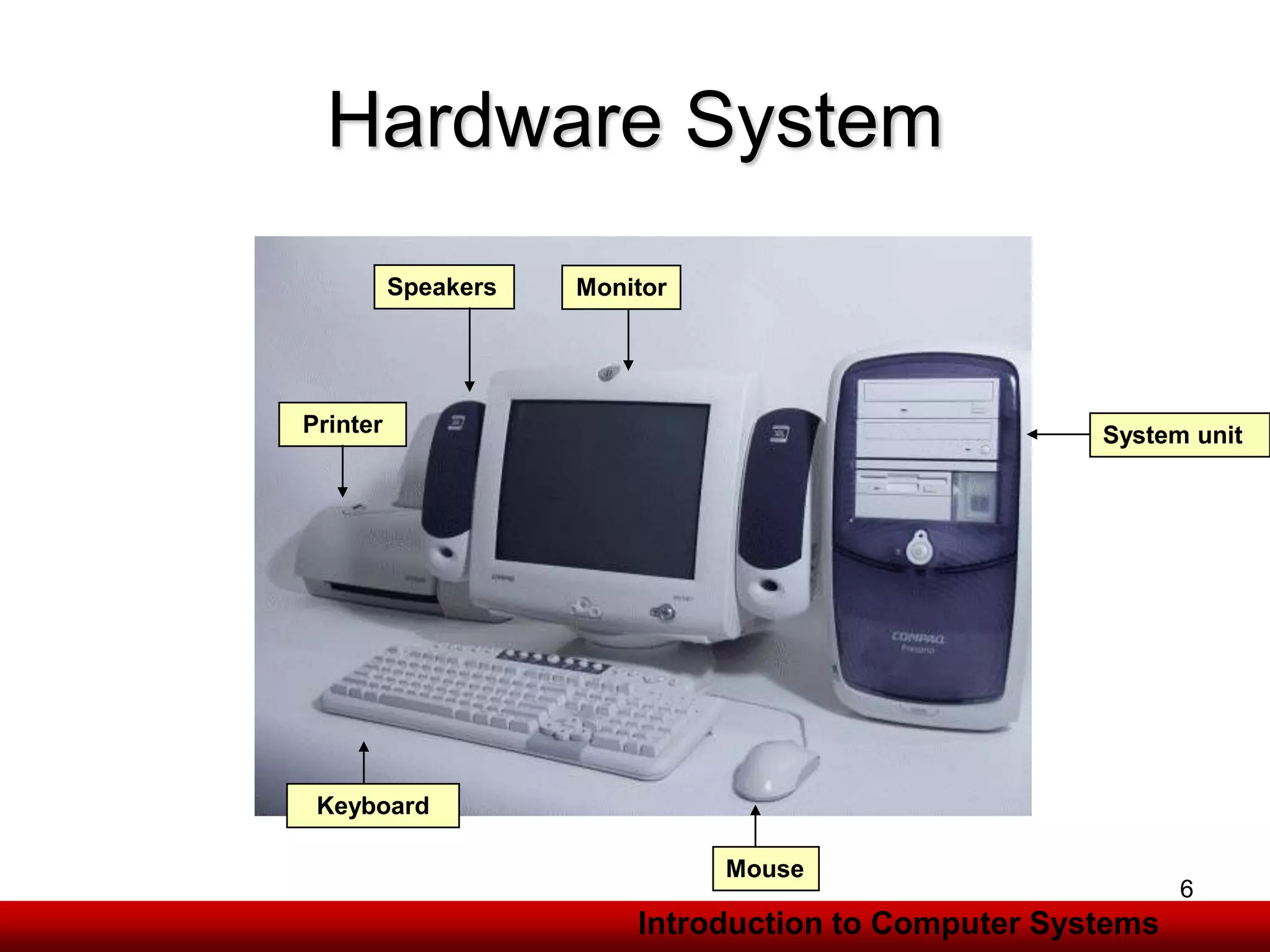
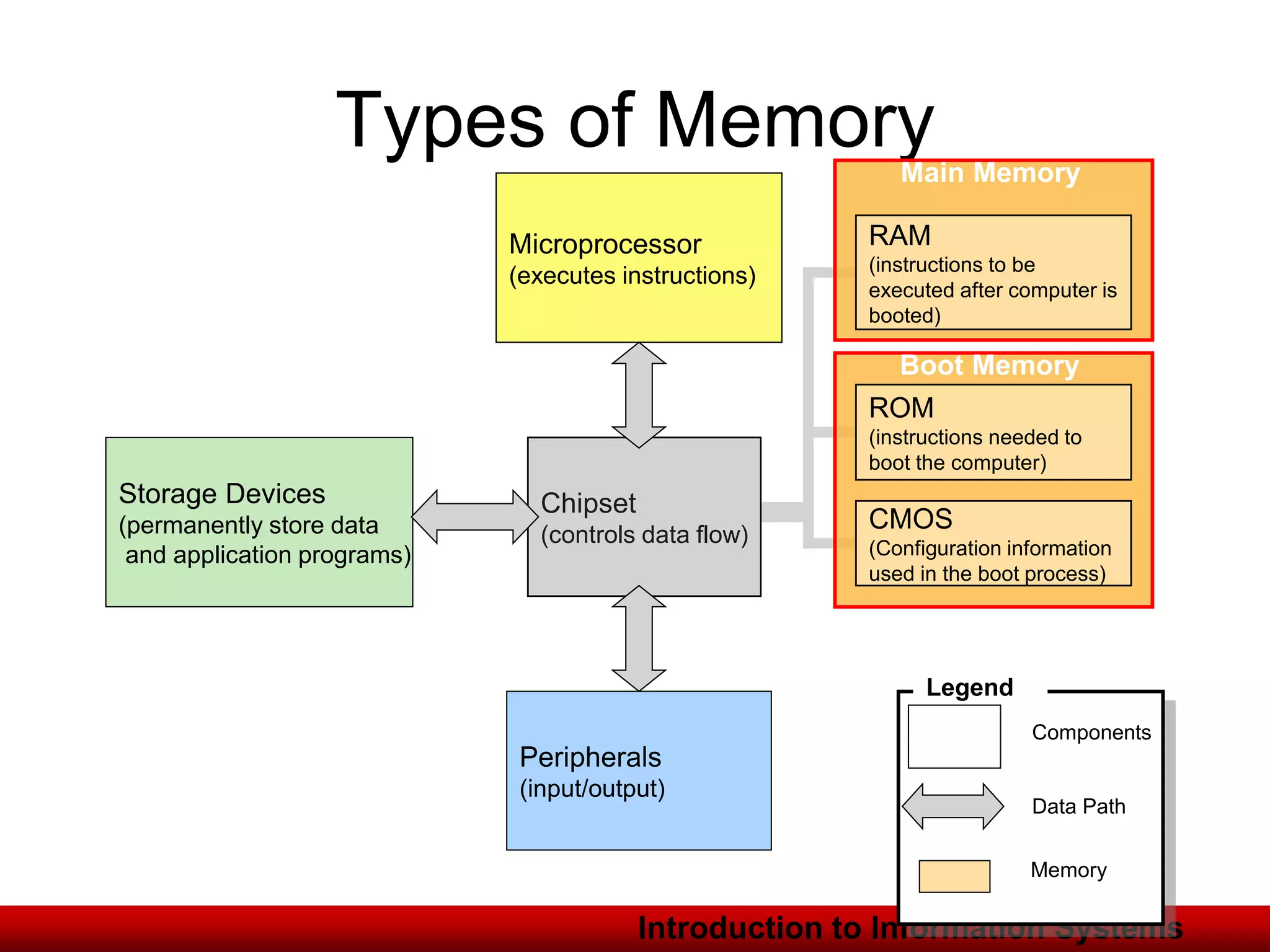
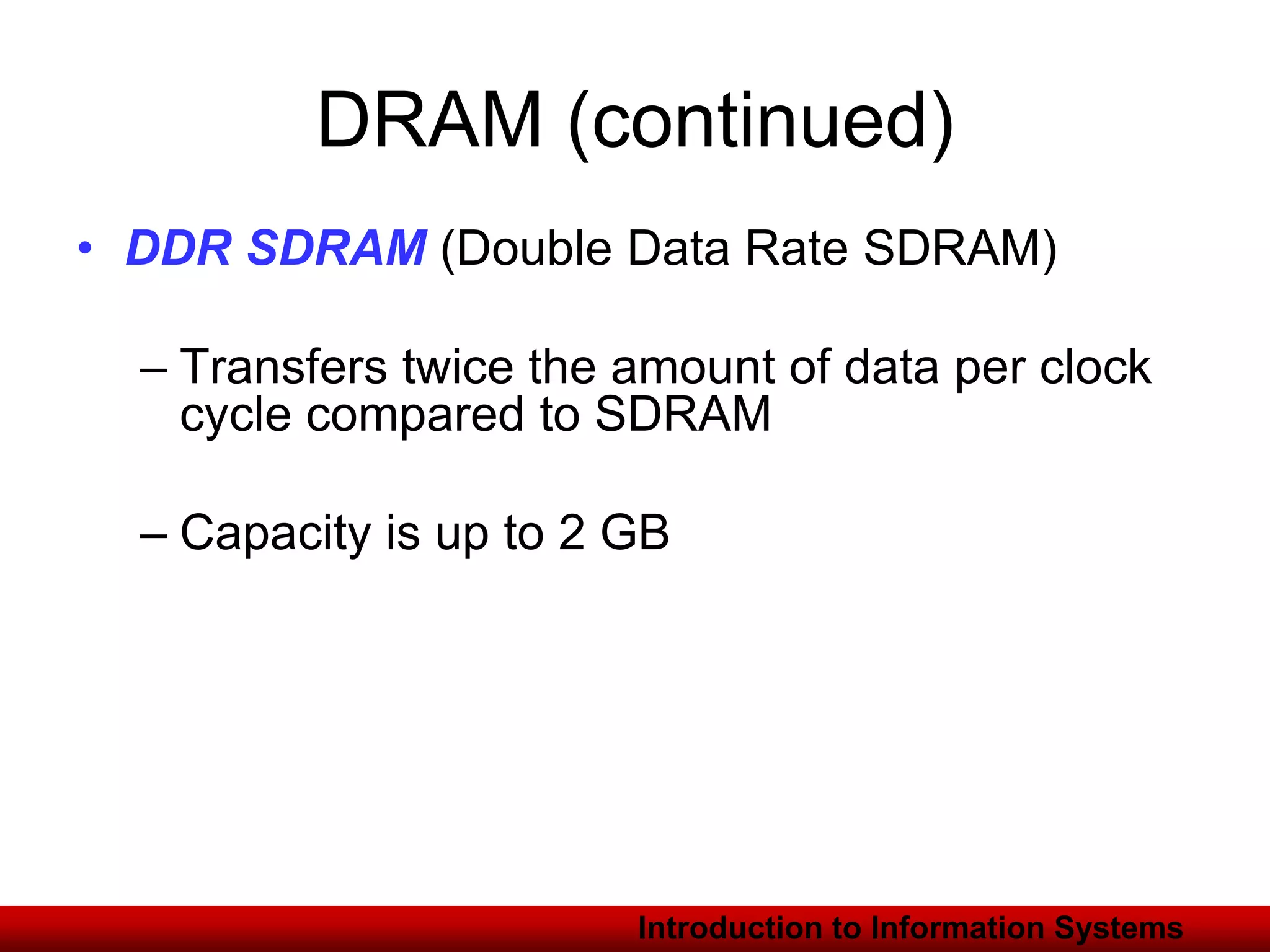
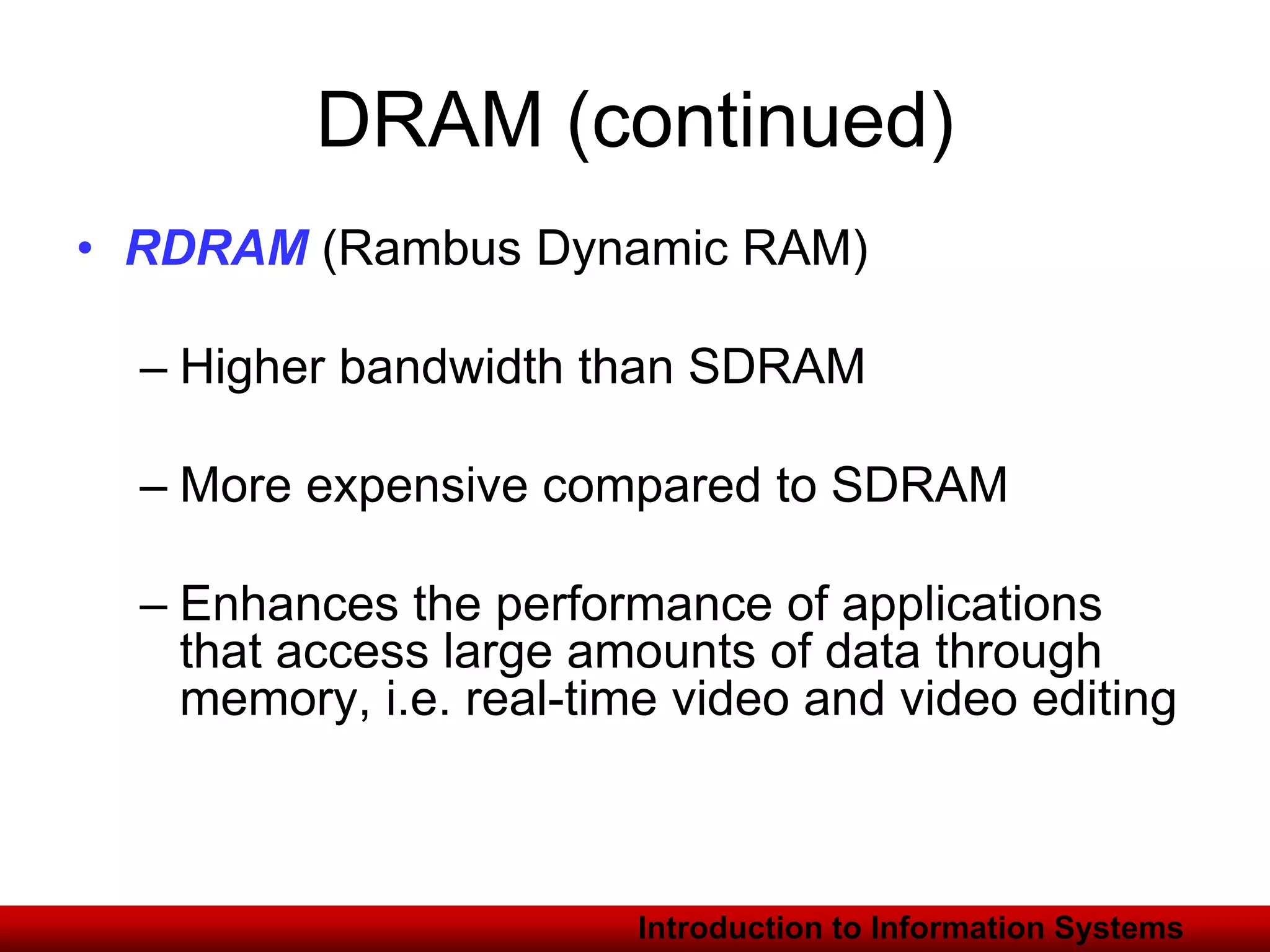
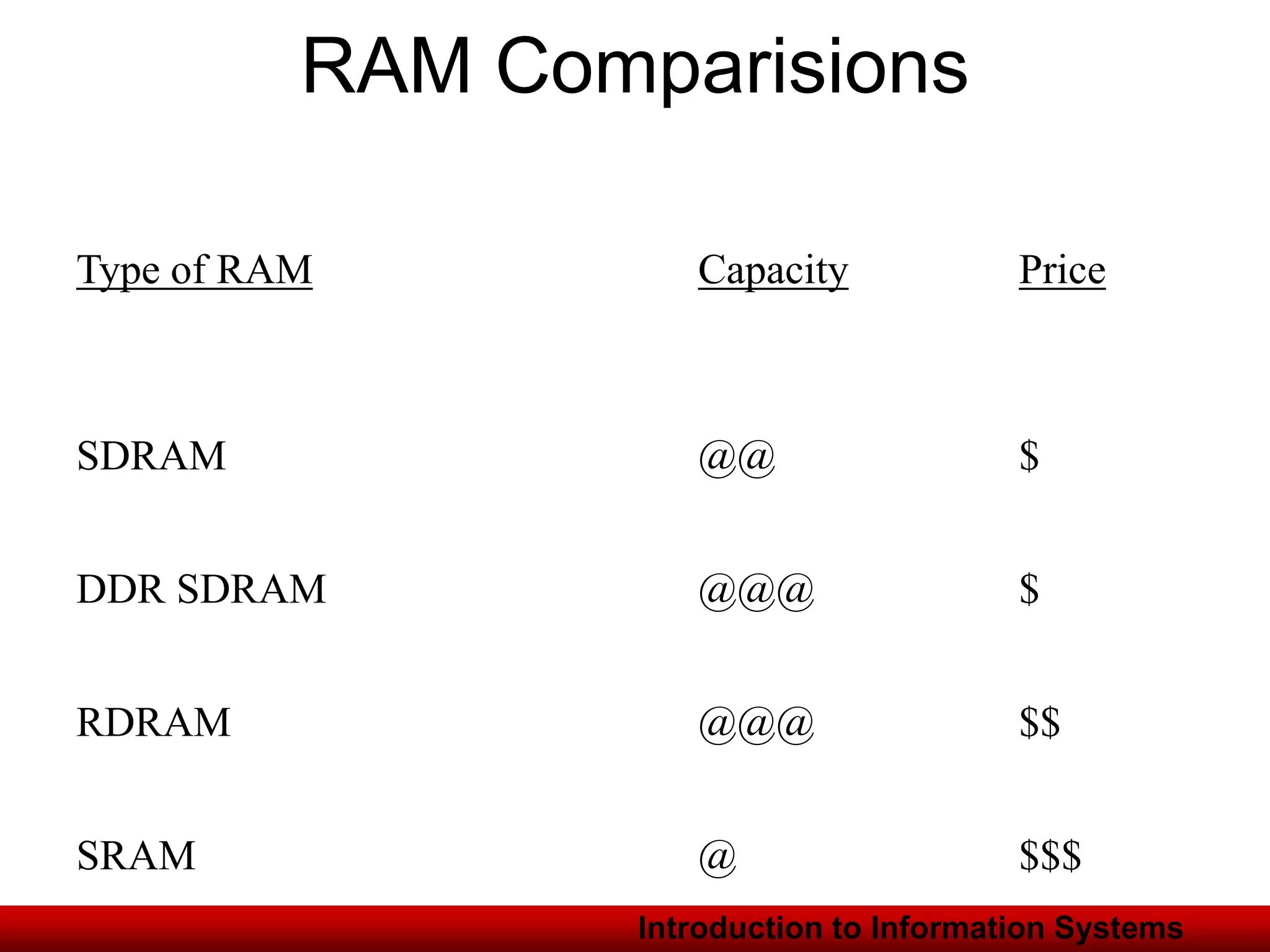
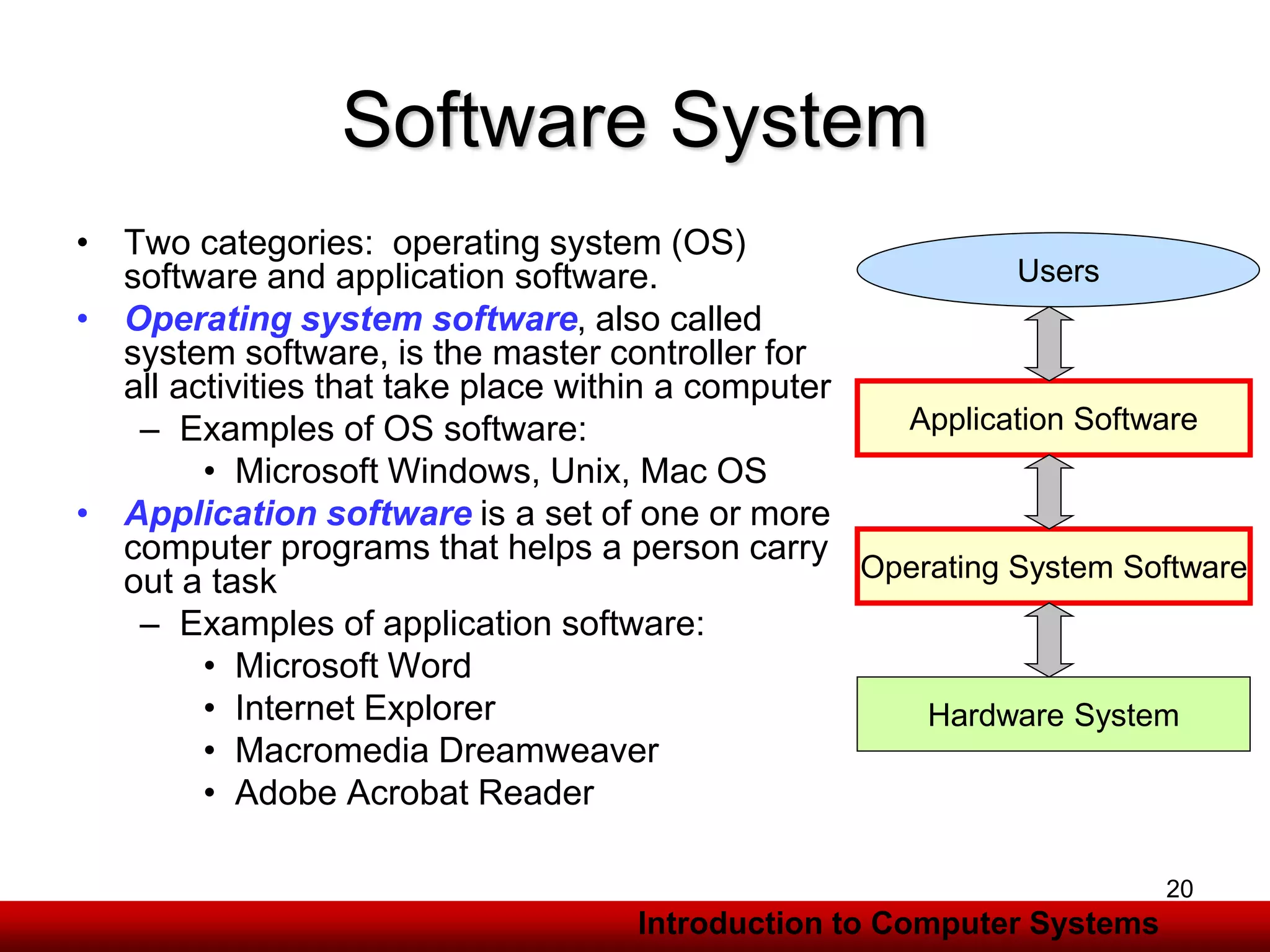
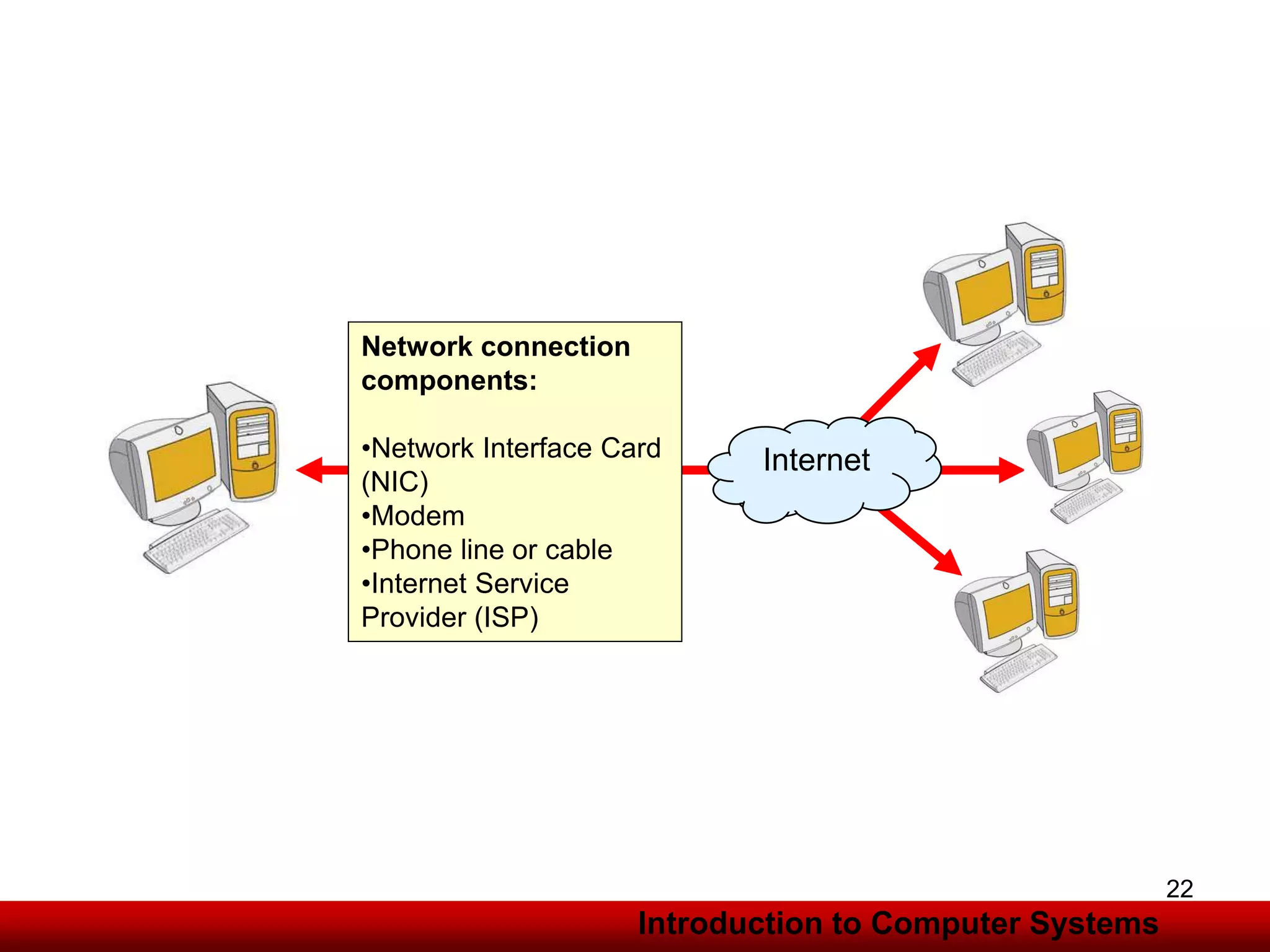
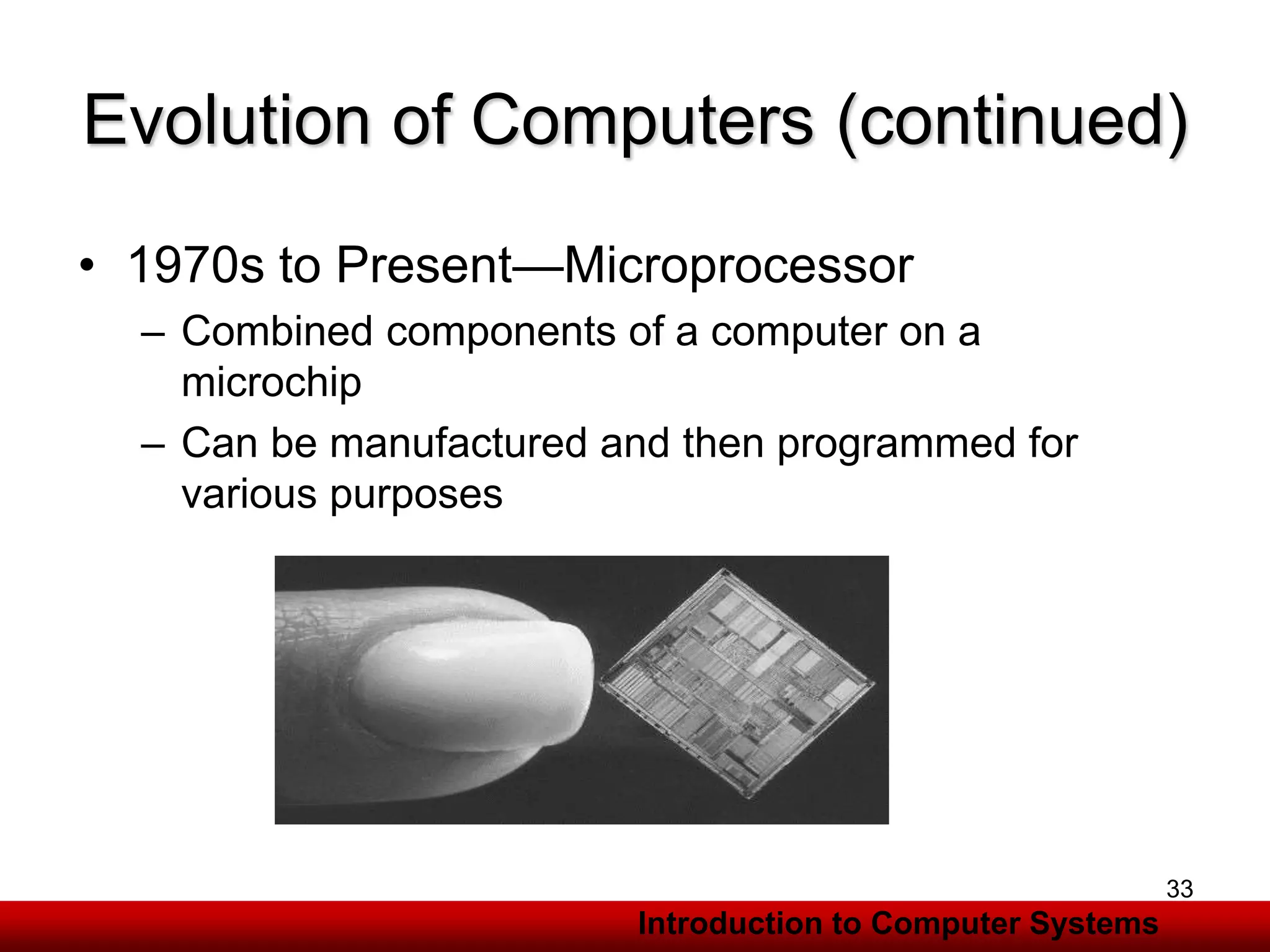
The document is a comprehensive introduction to information systems, detailing hardware and software requirements, components of computer systems, and the evolution of computing technology. It covers types of memory, RAM specifications, and distinct categories of software, highlighting the importance of networks and the history of computing advancements from manual devices to microprocessors. Additionally, it discusses applications of computer systems in education and business.