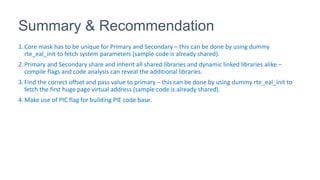
1. The document describes an MMAP failure occurring occasionally with a DPDK secondary application.
2. Address Space Layout Randomization (ASLR) can interfere with shared memory mappings between primary and secondary DPDK processes. Disabling ASLR may resolve MMAP failures.
3. Providing a fixed base virtual address with the "--base-virtaddr" option can ensure primary and secondary applications mmap shared memory at the same locations if ASLR is enabled.

![Problem Overview
• During lab run; occasional MMAP failure is been observed.
• Primary is modeled for main packet processing. While secondary
handles configuration and special packet processing.
• Applications should run inside Virtual Machines with Address Space
Layout Randomization enabled.
• “EAL: Could not mmap <n> bytes in /dev/zero at [0x7fcedbc00000], got
[0x7fcea1800000] - please use '--base-virtaddr' option“.](https://image.slidesharecdn.com/mmapfailureanalysis-170731044157/85/Mmap-failure-analysis-2-320.jpg)