Report
Share
Recommended
Dining Philosopher Problem and Solution

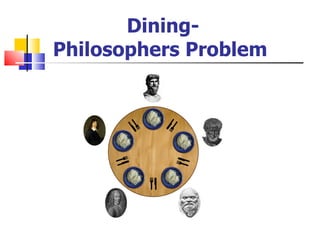
The Dining Philosopher Problem – The Dining Philosopher Problem states that K philosophers seated around a circular table with one chopstick between each pair of philosophers. There is one chopstick between each philosopher. A philosopher may eat if he can pick up the two chopsticks adjacent to him.
Dining Philosopher's Problem

A presentation on the Dining Philosopher's Problem, explaining the problem, issues while solving the problem and solutions to the problem. The presentation then takes the user through the Requirement Engineering for the problem via its 4 phases, including, Requirement Discovery, Analysis, Validation and Management. The presentation also includes Use Case Diagrams and Data Flow Diagrams.
Dining philosopher

Dining Philosopher’s Problem
Possibility of Deadlock
Possibility of Starvation
Critical Regions
Semaphore
Algorithms
Operating system 32 logical versus physical address

How to utilize memory optimally by manipulating objects in the memory is referred to as memory management.
Program must be brought (from disk) into memory and placed within a process for it to be run
Main memory and registers are only storage CPU can access directly
Memory unit only sees a stream of addresses + read requests, or address + data and write requests
Register access in one CPU clock (or less)
Main memory can take many cycles, causing a stall
Cache sits between main memory and CPU registers
Protection of memory required to ensure correct operation
Recommended
Dining Philosopher Problem and Solution

The Dining Philosopher Problem – The Dining Philosopher Problem states that K philosophers seated around a circular table with one chopstick between each pair of philosophers. There is one chopstick between each philosopher. A philosopher may eat if he can pick up the two chopsticks adjacent to him.
Dining Philosopher's Problem

A presentation on the Dining Philosopher's Problem, explaining the problem, issues while solving the problem and solutions to the problem. The presentation then takes the user through the Requirement Engineering for the problem via its 4 phases, including, Requirement Discovery, Analysis, Validation and Management. The presentation also includes Use Case Diagrams and Data Flow Diagrams.
Dining philosopher

Dining Philosopher’s Problem
Possibility of Deadlock
Possibility of Starvation
Critical Regions
Semaphore
Algorithms
Operating system 32 logical versus physical address

How to utilize memory optimally by manipulating objects in the memory is referred to as memory management.
Program must be brought (from disk) into memory and placed within a process for it to be run
Main memory and registers are only storage CPU can access directly
Memory unit only sees a stream of addresses + read requests, or address + data and write requests
Register access in one CPU clock (or less)
Main memory can take many cycles, causing a stall
Cache sits between main memory and CPU registers
Protection of memory required to ensure correct operation
Introduction to parallel processing

This presentation contains flynn's classification,difference between SIMD and MIMD some applications of parallel processing
Operating system 25 classical problems of synchronization

Classical problems used to test newly-proposed synchronization schemes
Bounded-Buffer Problem
Readers and Writers Problem
Dining-Philosophers Problem
Process synchronization in Operating Systems

A brief introduction to Process synchronization in Operating Systems with classical examples and solutions using semaphores. A good starting tutorial for beginners.
Dead Lock in operating system

How and why dead lock occur in operating system. Briefly explain in this presentation.
Threads in Operating System | Multithreading | Interprocess Communication

1.Interprocess communication ( IPC )
2. Introduction to threads
3. Difference between threads and process
4. Multiprocessing vs multithreading
5. Multithreading challenges
Reader/writer problem

This ppt covers the reader/writer problem in process synchronization in Operating systems.
dining philosophers problem using montiors

term presentation on operating systems. monitors and solution of dining philosophers using monitors
The Dining Philosophers problem in Bangla

The dining philosophers problem is an example problem often used in concurrent algorithm design to illustrate synchronization issues and techniques for resolving them.
More Related Content
What's hot
Introduction to parallel processing

This presentation contains flynn's classification,difference between SIMD and MIMD some applications of parallel processing
Operating system 25 classical problems of synchronization

Classical problems used to test newly-proposed synchronization schemes
Bounded-Buffer Problem
Readers and Writers Problem
Dining-Philosophers Problem
Process synchronization in Operating Systems

A brief introduction to Process synchronization in Operating Systems with classical examples and solutions using semaphores. A good starting tutorial for beginners.
Dead Lock in operating system

How and why dead lock occur in operating system. Briefly explain in this presentation.
Threads in Operating System | Multithreading | Interprocess Communication

1.Interprocess communication ( IPC )
2. Introduction to threads
3. Difference between threads and process
4. Multiprocessing vs multithreading
5. Multithreading challenges
Reader/writer problem

This ppt covers the reader/writer problem in process synchronization in Operating systems.
What's hot (20)
Operating system 25 classical problems of synchronization

Operating system 25 classical problems of synchronization
Threads in Operating System | Multithreading | Interprocess Communication

Threads in Operating System | Multithreading | Interprocess Communication
Viewers also liked
dining philosophers problem using montiors

term presentation on operating systems. monitors and solution of dining philosophers using monitors
The Dining Philosophers problem in Bangla

The dining philosophers problem is an example problem often used in concurrent algorithm design to illustrate synchronization issues and techniques for resolving them.
Producer consumer

this ppt is about the famous producer-consumer problem in operating systems.and a thorough solution of this problem
READER/WRITER SOLUTION

The .NET Framework provides several threading locking primitives. The Reader Writer Solution is one of them.
The Reader Writer Solution class is used to synchronize access to a resource. At any given time, it allows concurrent read access to multiple (essentially unlimited) threads, or it allows write access for a single thread. In situations where a resource is read frequently but updated infrequently, a Reader Writer Solution will provide much better throughput than the exclusive Monitor lock.
Course: Operating System
SlideShare 101

The SlideShare 101 is a quick start guide if you want to walk through the main features that the platform offers. This will keep getting updated as new features are launched.
The SlideShare 101 replaces the earlier "SlideShare Quick Tour".
Operating Systems - Process Synchronization and Deadlocks

PROCESS SYNCHRONIZATION: BACKGROUND, CRITICAL-SECTION PROBLEM, SYNCHRONIZATION HARDWARE, SEMAPHORES, CLASSICAL PROBLEM OF SYNCHRONIZATION, CRITICAL REGION, MONITOR
DEADLOCKS: MODEL, CHARACTERIZATION, METHODS FOR HANDLING DEADLOCKS, PREVENTION, AVOIDANCE, DETECTION, RECOVERY, COMBINED APPROACH TO DEADLOCK HANDLING
Viewers also liked (20)
Operating Systems - Process Synchronization and Deadlocks

Operating Systems - Process Synchronization and Deadlocks
More from Ramasubbu .P
More from Ramasubbu .P (20)
Recently uploaded
Chapter -12, Antibiotics (One Page Notes).pdf

This is a notes for the D.Pharm students and related to the antibiotic drugs.
Supporting (UKRI) OA monographs at Salford.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
Francesca Gottschalk - How can education support child empowerment.pptx

Francesca Gottschalk from the OECD’s Centre for Educational Research and Innovation presents at the Ask an Expert Webinar: How can education support child empowerment?
A Survey of Techniques for Maximizing LLM Performance.pptx

A Survey of Techniques for Maximizing LLM Performance
Biological Screening of Herbal Drugs in detailed.

Biological screening of herbal drugs: Introduction and Need for
Phyto-Pharmacological Screening, New Strategies for evaluating
Natural Products, In vitro evaluation techniques for Antioxidants, Antimicrobial and Anticancer drugs. In vivo evaluation techniques
for Anti-inflammatory, Antiulcer, Anticancer, Wound healing, Antidiabetic, Hepatoprotective, Cardio protective, Diuretics and
Antifertility, Toxicity studies as per OECD guidelines
The French Revolution Class 9 Study Material pdf free download

The French Revolution, which began in 1789, was a period of radical social and political upheaval in France. It marked the decline of absolute monarchies, the rise of secular and democratic republics, and the eventual rise of Napoleon Bonaparte. This revolutionary period is crucial in understanding the transition from feudalism to modernity in Europe.
For more information, visit-www.vavaclasses.com
The approach at University of Liverpool.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
How to Make a Field invisible in Odoo 17

It is possible to hide or invisible some fields in odoo. Commonly using “invisible” attribute in the field definition to invisible the fields. This slide will show how to make a field invisible in odoo 17.
Chapter 3 - Islamic Banking Products and Services.pptx

Chapter 3 - Islamic Banking Products and Services.pptxMohd Adib Abd Muin, Senior Lecturer at Universiti Utara Malaysia
This slide is prepared for master's students (MIFB & MIBS) UUM. May it be useful to all.1.4 modern child centered education - mahatma gandhi-2.pptx

Child centred education is an educational approach that priorities the interest, needs and abilities of the child in the learning process.
A Strategic Approach: GenAI in Education

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH ANSWERS.
Digital Artifact 2 - Investigating Pavilion Designs

Digital Artifact 2 - Pavilions
NGV Architecture Commission Competition
MPavilion Commission Competition
Other Pavilion Designs
Recently uploaded (20)
Francesca Gottschalk - How can education support child empowerment.pptx

Francesca Gottschalk - How can education support child empowerment.pptx
A Survey of Techniques for Maximizing LLM Performance.pptx

A Survey of Techniques for Maximizing LLM Performance.pptx
The French Revolution Class 9 Study Material pdf free download

The French Revolution Class 9 Study Material pdf free download
Multithreading_in_C++ - std::thread, race condition

Multithreading_in_C++ - std::thread, race condition
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI fund...
Chapter 3 - Islamic Banking Products and Services.pptx

Chapter 3 - Islamic Banking Products and Services.pptx
1.4 modern child centered education - mahatma gandhi-2.pptx

1.4 modern child centered education - mahatma gandhi-2.pptx
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...
Digital Artifact 2 - Investigating Pavilion Designs

Digital Artifact 2 - Investigating Pavilion Designs
DPP
- 7. Solution to Dining Philosophers
- 8. Solution to Dining Philosophers
