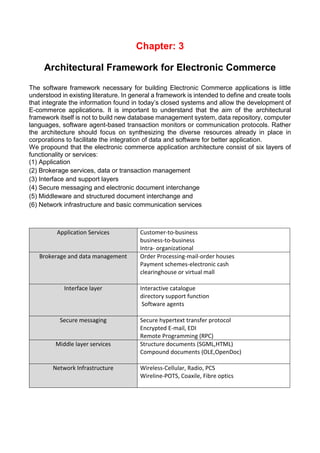
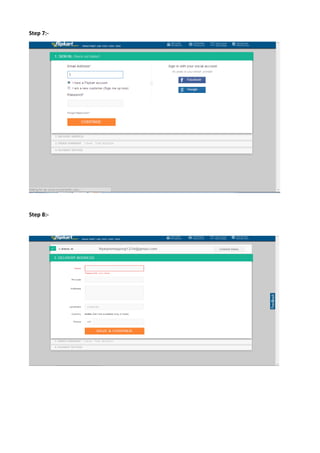
This document is a project report submitted by Divya Rajguru, a third year BCA student at Dezyne E'cole College in Ajmer, India on the topic of electronic commerce. It consists of an introduction and 8 chapters that discuss topics like the definition of e-commerce, the role of the world wide web, architectural frameworks for e-commerce, underlying technologies, network security, e-commerce companies, and a pictorial representation of the e-buying methodology. The student thanks their college and project guide for their assistance in completing this report.